This month’s Patch Tuesday provides a bit one thing for everybody, together with safety updates for a zero-day flaw in Microsoft Home windows that’s below energetic assault, and one other Home windows weak point specialists say might be used to energy a fast-spreading laptop worm. Additionally, Apple has additionally quashed a pair of zero-day bugs affecting sure macOS and iOS customers, and launched iOS 16, which provides a brand new privateness and safety characteristic referred to as “Lockdown Mode.” And Adobe axed 63 vulnerabilities in a variety of merchandise.
Microsoft in the present day launched software program patches to plug a minimum of 64 safety holes in Home windows and associated merchandise. Worst when it comes to outright scariness is CVE-2022-37969, which is a “privilege escalation” weak point within the Home windows Frequent Log File System Driver that enables attackers to realize SYSTEM-level privileges on a weak host. Microsoft says this flaw is already being exploited within the wild.
Kevin Breen, director of cyber menace analysis at Immersive Labs, mentioned any vulnerability that’s actively focused by attackers within the wild have to be put to the highest of any patching record.
“To not be fooled by its comparatively low CVSS rating of seven.8, privilege escalation vulnerabilities are sometimes extremely wanted by cyber attackers,” Breen mentioned. “As soon as an attacker has managed to realize a foothold on a sufferer’s system, one in all their first actions can be to realize a better degree of permissions, permitting the attacker to disable safety functions and any machine monitoring. There isn’t a identified workaround to this point, so patching is the one efficient mitigation.”
Satnam Narang at Tenable mentioned CVE-2022-24521 — an identical vulnerability in the identical Home windows log file part — was patched earlier this yr as a part of Microsoft’s April Patch Tuesday launch and was additionally exploited within the wild.
“CVE-2022-37969 was disclosed by a number of teams, although it’s unclear if CVE-2022-37969 is a patch-bypass for CVE-2022-24521 at this level,” Narang mentioned.
One other vulnerability Microsoft patched this month — CVE-2022-35803 — additionally appears to be associated to the identical Home windows log file part. Whereas there aren’t any indications CVE-2022-35803 is being actively exploited, Microsoft means that exploitation of this flaw is extra probably than not.
Development Micro’s Dustin Childs referred to as consideration to CVE-2022-34718, a distant code execution flaw within the Home windows TCP/IP service that might permit an unauthenticated attacker to execute code with elevated privileges on affected techniques with out consumer interplay.
“That formally places it into the ‘wormable’ class and earns it a CVSS ranking of 9.8,” Childs mentioned. “Nonetheless, solely techniques with IPv6 enabled and IPSec configured are weak. Whereas excellent news for some, when you’re utilizing IPv6 (as many are), you’re most likely operating IPSec as properly. Positively check and deploy this replace shortly.”
Cisco Talos warns about 4 vital vulnerabilities fastened this month — CVE-2022-34721 and CVE-2022-34722 — which have severity scores of 9.8, although they’re “much less probably” to be exploited, in response to Microsoft.
“These are distant code execution vulnerabilities within the Home windows Web Key Alternate protocol that might be triggered if an attacker sends a specifically crafted IP packet,” wrote Jon Munshaw and Asheer Malhotra. “Two different vital vulnerabilities, CVE-2022-35805 and CVE-2022-34700 exist in on-premises cases of Microsoft Dynamics 365. An authenticated attacker may exploit these vulnerabilities to run a specifically crafted trusted resolution package deal and execute arbitrary SQL instructions. The attacker may escalate their privileges additional and execute instructions because the database proprietor.”
 To not be outdone, Apple fastened a minimum of two zero-day vulnerabilities when it launched updates for iOS, iPadOS, macOS and Safari. CVE-2022-32984 is an issue within the deepest recesses of the working system (the kernel). Apple pushed an emergency replace for a associated zero-day final month in CVE-2022-32983, which might be used to foist malware on iPhones, iPads and Macs that visited a booby-trapped web site.
To not be outdone, Apple fastened a minimum of two zero-day vulnerabilities when it launched updates for iOS, iPadOS, macOS and Safari. CVE-2022-32984 is an issue within the deepest recesses of the working system (the kernel). Apple pushed an emergency replace for a associated zero-day final month in CVE-2022-32983, which might be used to foist malware on iPhones, iPads and Macs that visited a booby-trapped web site.
Additionally listed below energetic assault is CVE-2022-32817, which has been fastened on macOS 12.6 (Monterey), macOS 11.7 (Large Sur), iOS 15.7 and iPadOS 15.7, and iOS 16. The identical vulnerability was fastened in Apple Watch in July 2022, and credit Xinru Chi of Japanese cybersecurity agency Pangu Lab.
“Curiously, this CVE can also be listed within the advisory for iOS 16, however it isn’t referred to as out as being below energetic exploit for that taste of the OS,” Development Micro’s Childs famous. “Apple does state in its iOS 16 advisory that ‘Extra CVE entries to be added quickly.’ It’s doable different bugs may additionally impression this model of the OS. Both manner, it’s time to replace your Apple gadgets.”
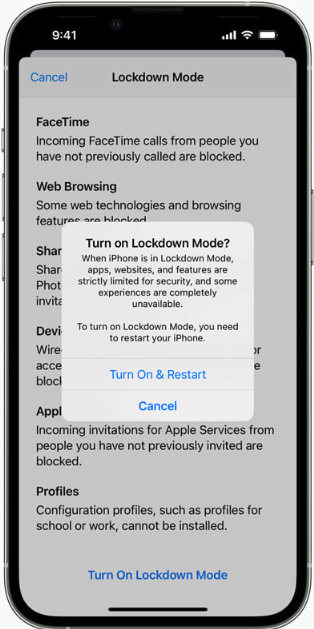
Apple’s iOS 16 contains two new safety and privateness options — Lockdown Mode and Security Test. Wired.com describes Security Test as a characteristic for customers who’re in danger for, or at the moment experiencing, home abuse.
“The device centralizes a lot of controls in a single place to make it simpler for customers to handle and revoke entry to their location information and reset privacy-related permissions,” wrote Lily Hay Newman.
“Lockdown Mode, however, is supposed for customers who probably face focused spy ware assaults and aggressive state-backed hacking. The characteristic comprehensively restricts any nonessential iOS options so there are as few potential factors of entry to a tool as doable. As extra governments and repressive entities world wide have begun buying highly effective commodity spy ware to focus on people of specific significance or curiosity, iOS’s normal safety defenses haven’t been capable of hold tempo with these specialised threats.”
To activate Lockdown Mode in iOS 16, go to Settings, then Privateness and Safety, then Lockdown Mode. Security Test is positioned in the identical space.
Lastly, Adobe launched seven patches addressing 63 safety holes in Adobe Expertise Supervisor, Bridge, InDesign, Photoshop, InCopy, Animate, and Illustrator. Extra on these updates is right here.
Don’t overlook to again up your information and/or system earlier than making use of any safety updates. For those who expertise glitches or issues putting in any of those patches this month, please think about leaving a remark about it under; there’s a good likelihood different readers have skilled the identical and should chime in right here with helpful ideas.

