The sufferer shaming web site operated by the cybercriminals behind 8Base — at the moment one of many extra lively ransomware teams — was till earlier at the moment leaking fairly a bit of knowledge that the crime group most likely didn’t intend to be made public. The leaked information means that at the least a few of web site’s code was written by a 36-year-old programmer residing within the capital metropolis of Moldova.
The 8Base ransomware group’s sufferer shaming web site on the darknet.
8Base maintains a darknet web site that’s solely reachable by way of Tor, a freely out there world anonymity community. The positioning lists a whole lot of sufferer organizations and corporations — all allegedly hacking victims that refused to pay a ransom to maintain their stolen information from being printed.
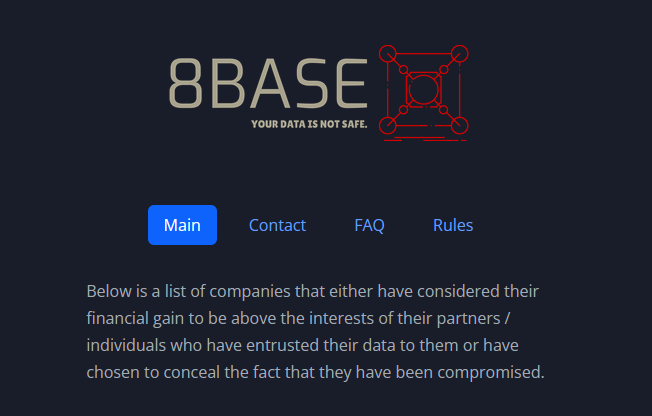
The 8Base darknet website additionally has a built-in chat function, presumably in order that 8Base victims can talk and negotiate with their extortionists. This chat function, which runs on the Laravel net utility framework, works positive so long as you might be *sending* data to the location (i.e., by making a “POST” request).
Nevertheless, if one had been to attempt to fetch information from the identical chat service (i.e., by making a “GET” request), the web site till fairly lately generated a particularly verbose error message:
The verbose error message when one tries to tug information from 8Base’s darknet website. Discover the hyperlink on the backside of this picture, which is generated when one hovers over the “View commit” message beneath the “Git” heading.
That error web page revealed the true Web deal with of the Tor hidden service that homes the 8Base web site: 95.216.51[.]74, which in accordance with DomainTools.com is a server in Finland that’s tied to the Germany-based internet hosting large Hetzner.
However that’s not the attention-grabbing half: Scrolling down the prolonged error message, we are able to see a hyperlink to a personal Gitlab server referred to as Jcube-group: gitlab[.]com/jcube-group/purchasers/apex/8base-v2. Digging additional into this Gitlab account, we are able to discover some curious information factors out there within the JCube Group’s public code repository.
For instance, this “standing.php” web page, which was dedicated to JCube Group’s Gitlab repository roughly one month in the past, consists of code that makes a number of mentions of the time period “KYC” (e.g. KYC_UNVERIFIED, KYC_VERIFIED, and KYC_PENDING).
That is curious as a result of a FAQ on the 8Base darknet website features a part on “particular provides for journalists and reporters,” which says the crime group is open to interviews however that journalists might want to show their id earlier than any interview can happen. The 8base FAQ refers to this vetting course of as “KYC,” which generally stands for “Know Your Buyer.”
“We extremely respect the work of journalists and take into account data to be our precedence,” the 8Base FAQ reads. “We’ve a particular program for journalists which incorporates sharing data a number of hours and even days earlier than it’s formally printed on our information web site and Telegram channel: you would want to undergo a KYC process to use. Journalists and reporters can contact us by way of our PR Telegram channel with any questions.”
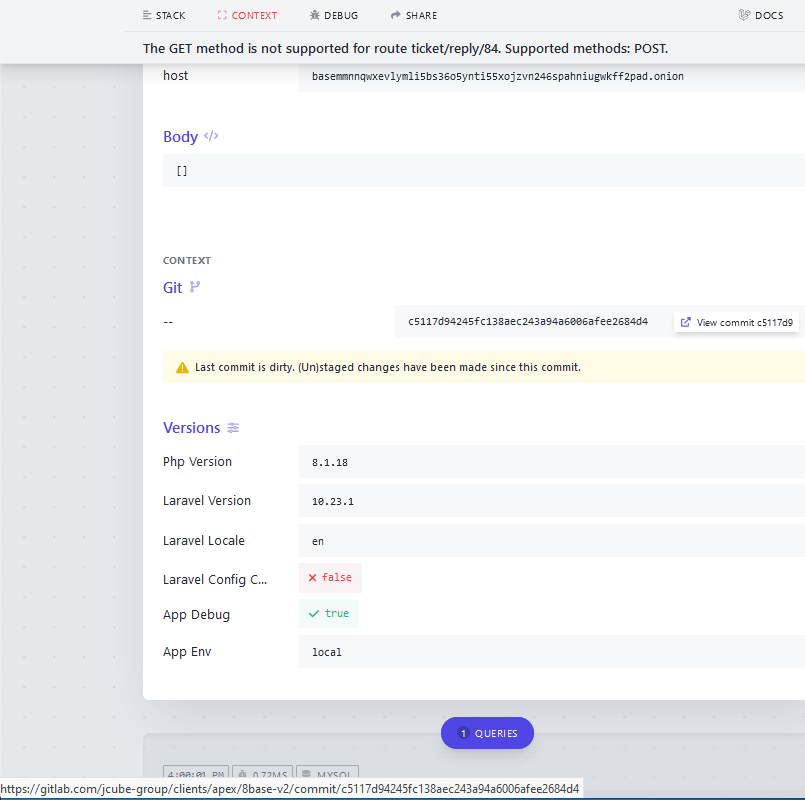
The 8Base darknet website additionally has a publicly accessible “admin” login web page, which options a picture of a business passenger airplane parked at what seems to be an airport. Subsequent to the airplane picture is a message that reads, “Welcome to 8Base. Admin Login to 8Base dashboard.”
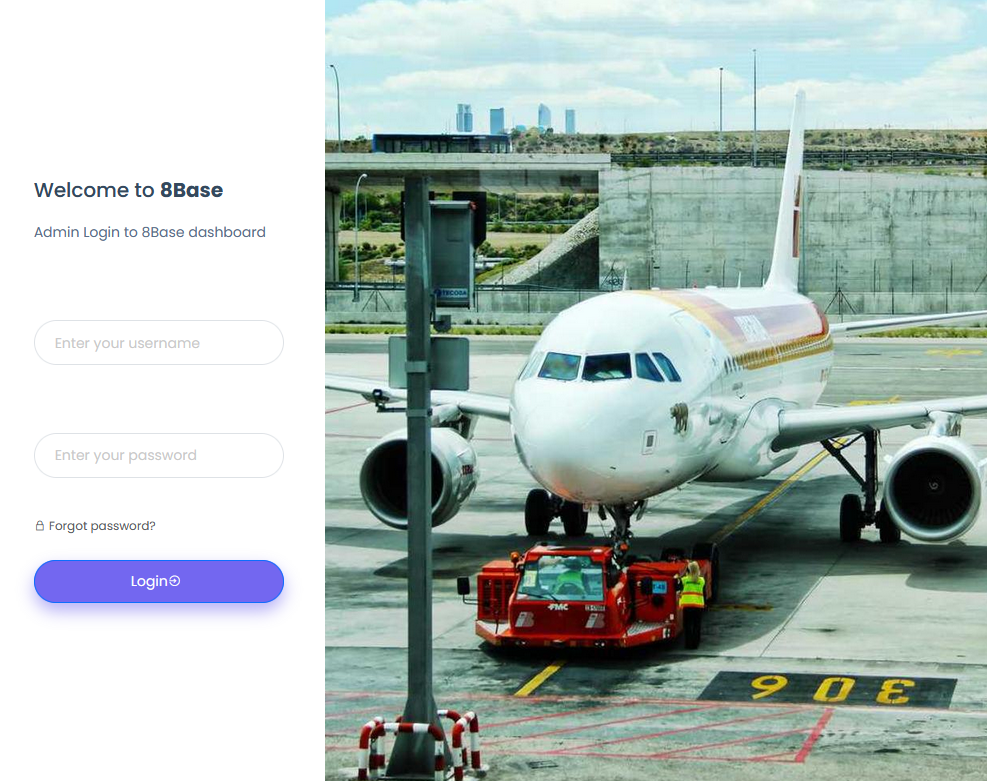
The login web page on the 8Base ransomware group’s darknet web site.
Proper-clicking on the 8Base admin web page and deciding on “View Supply” produces the web page’s HTML code. That code is just about equivalent to a “login.blade.php” web page that was authored and dedicated to JCube Group’s Gitlab repository roughly three weeks in the past.
It seems the individual accountable for the JCube Group’s code is a 36-year-old developer from Chisinau, Moldova named Andrei Kolev. Mr. Kolev’s LinkedIn web page says he’s a full-stack developer at JCube Group, and that he’s at the moment on the lookout for work. The homepage for Jcubegroup[.]com lists an deal with and telephone quantity that Moldovan enterprise information affirm is tied to Mr. Kolev.
The posts on the Twitter account for Mr. Kolev (@andrewkolev) are all written in Russian, and reference a number of now-defunct on-line companies, together with pluginspro[.]ru.
Reached for remark by way of LinkedIn, Mr. Kolev mentioned he had no concept why the 8Base darknet website was pulling code from the “purchasers” listing of his non-public JCube Group Gitlab repository, or how the 8Base identify was even included.
“I [don’t have] a clue, I don’t have that mission in my repo,” Kolev defined. “They [aren’t] my purchasers. Really we at the moment have simply our personal tasks.”
Mr. Kolev shared a screenshot of his present tasks, however in a short time after that deleted it. Nevertheless, KrebsOnSecurity captured a replica of the picture earlier than it was eliminated:
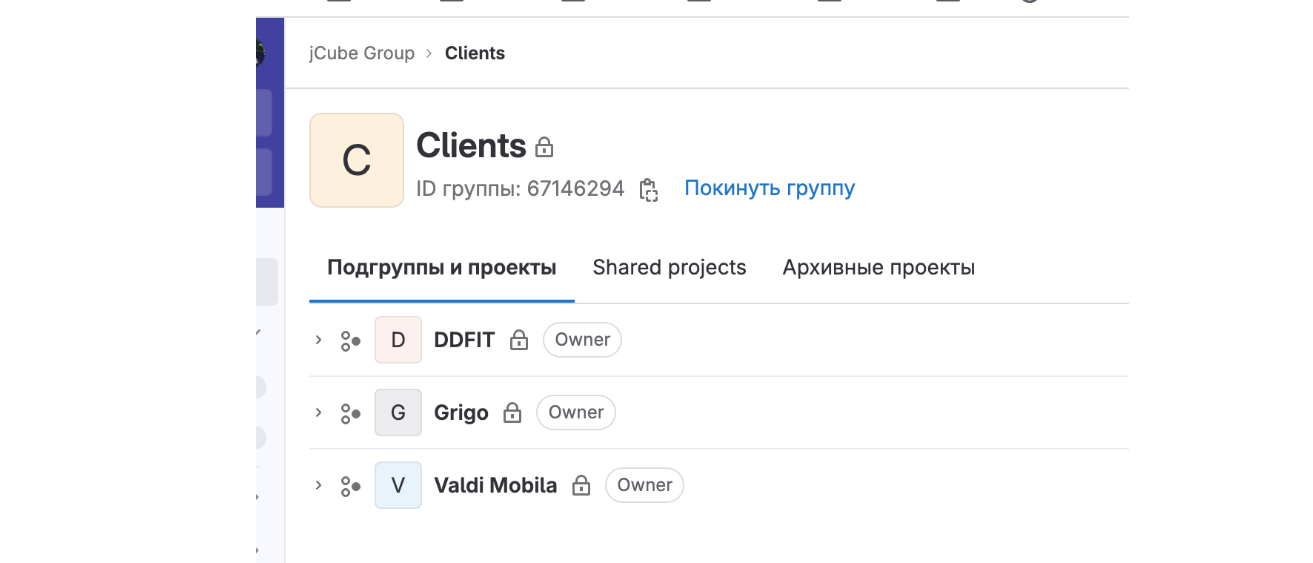
A screenshot of Mr. Kolev’s present tasks that he rapidly deleted.
Inside minutes of explaining why I used to be reaching out to Mr. Kolev and strolling him by means of the method of discovering this connection, the 8Base web site was modified, and the error message that linked to the JCube Group non-public Gitlab repository not appeared. As a substitute, attempting the identical “GET” methodology described above induced the 8Base web site to return a “405 Methodology Not Allowed” error web page:
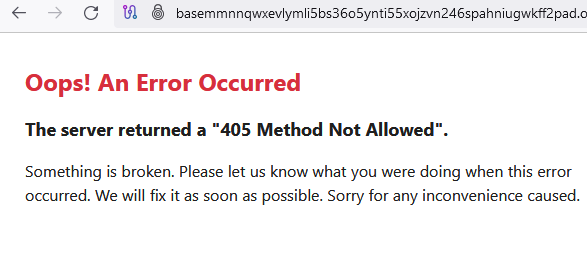
Mr. Kolev claimed he didn’t know something concerning the now-removed error web page on 8Base’s website that referenced his non-public Gitlab repo, and mentioned he deleted the screenshot from our LinkedIn chat as a result of it contained non-public data.
Ransomware teams are identified to remotely rent builders for particular tasks with out disclosing precisely who they’re or how the brand new rent’s code is meant for use, and it’s doable that one among Mr. Kolev’s purchasers is merely a entrance for 8Base. However regardless of 8Base’s assertion that they’re joyful to correspond with journalists, KrebsOnSecurity continues to be ready for a reply from the group by way of their Telegram channel.
The tip concerning the leaky 8Base web site was offered by a reader who requested to stay nameless. That reader, a reputable safety skilled and researcher who goes by the deal with @htmalgae on Twitter, mentioned it’s probably that whoever developed the 8Base web site inadvertently left it in “growth mode,” which is what induced the location to be so verbose with its error messages.
“If 8Base was working the app in manufacturing mode as a substitute of growth mode, this Tor de-anonymization would have by no means been doable,” @htmalgae mentioned.
A latest weblog put up from VMware/Carbon Black referred to as the 8Base ransomware group “a heavy hitter” that has remained comparatively unknown regardless of the huge spike in exercise in Summer time of 2023.
“8Base is a Ransomware group that has been lively since March 2022 with a big spike in exercise in June of 2023,” Carbon Black researchers wrote. “Describing themselves as ‘easy pen testers,’ their leak website offered sufferer particulars by means of Steadily Requested Questions and Guidelines sections in addition to a number of methods to contact them. ”
In response to VMware, what’s significantly attention-grabbing about 8Base’s communication fashion is using verbiage that’s strikingly acquainted to a different identified cybercriminal group: RansomHouse.
“The group makes use of encryption paired with ‘name-and-shame’ strategies to compel their victims to pay their ransoms,” VMware researchers wrote. “8Base has an opportunistic sample of compromise with latest victims spanning throughout diverse industries. Regardless of the excessive quantity of compromises, the knowledge concerning identities, methodology, and underlying motivation behind these incidents nonetheless stays a thriller.”
Replace, Sept. 21, 10:43 a.m. ET: The writer of Databreaches.internet was lurking within the 8Base Telegram channel once I popped in to ask the crime group a query, and stories that 8Base did ultimately reply: ““hello for the time being we r not doing interviews. we’ve nothing to say. we r a little bit busy.”