Throughout structure evaluations, we usually determine technical-debt points inside a single system or challenge. Nonetheless, the affect of technical debt typically reaches past the scope of a single system or challenge. In our work, we check with this type of technical debt as enterprise technical debt. Like all technical debt, enterprise technical debt consists of decisions expedient within the brief time period, however typically problematic over the long run. Ignoring enterprise technical debt can have important penalties, so architects must be alert for it, and they need to not let it get missed or ignored after they come throughout it. On this publish, I present examples of enterprise technical debt (and the chance it represents) taken from real-world initiatives.
As structure evaluators, we now have the distinctive alternative to view architectural dangers from extra of an enterprise perspective (versus project-level), notably if we’re taking part in evaluations for a portfolio of initiatives. Over the previous a number of years, the SEI has leveraged SEI technical-debt analysis to institutionalize technical-debt practices at a company with a big portfolio of methods valued at over $100 million. This group has a portfolio of greater than two dozen enterprise functions and follows a decentralized IT governance mannequin. The examples on this publish got here from our work as structure evaluators on these initiatives.
To make enterprise technical debt extra concrete to readers, I present three examples of enterprise technical debt gadgets and penalties. In a future publish, I’ll go into larger element about documenting and remediating enterprise technical debt.
Instance 1: A Brittle System-Integration Answer
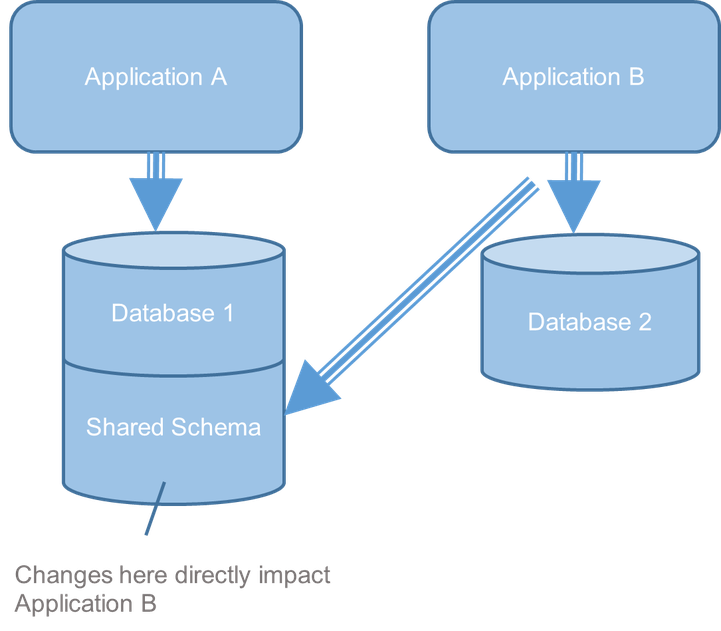
On this instance (Determine 1), challenge necessities referred to as for exchanging knowledge between Functions A and B. The challenge groups made an architectural choice to make use of a shared database schema because the data-exchange mechanism. This method was interesting to the groups on the time because it was simple to implement, however later it grew to become evident that this resolution was brittle. Particularly, when Group A made an impartial change to shared schema with out coordinating with Group B, Software B needed to additionally make adjustments to accommodate and vice versa.
Determine 1: A Brittle System-Integration Answer
The groups got here up with a workaround that made issues worse. The builders copied knowledge of their native environments to keep away from altering the schema. The groups created extract, remodel, load (ETL) jobs to maintain knowledge synchronized that have been unreliable. When an ETL job failed, knowledge was left in an inconsistent state. For instance, after failures, customers would get completely different historic question responses from Software A and Software B. Undertaking characteristic supply additionally slowed as a result of schema adjustments required time-consuming evaluation.
Each groups have been glad with the shared schema—not less than within the brief time period. Nonetheless, from our structure analysis, which provides us an exterior and enterprise-level perspective, we may see that the destructive penalties of this resolution have been more likely to improve over time as performance grew. Because of this, we advisable changing the brittle shared-schema resolution with an utility programming interface (API) for utility knowledge change.
The groups readily accepted the proposed technical resolution, however the group didn’t act to repair the problem initially for a number of causes. First, on this decentralized governance setting, neither crew felt answerable for the refactoring work. Second, fixing a brittle integration resolution was not seen as a precedence to the enterprise. Due to this fact, the product house owners wouldn’t allocate challenge funds to the redesign effort. Though no motion can be taken within the close to time period, we created a technical debt merchandise—a written description of the problem and consequence. Documenting the problem as a technical debt merchandise allowed the group to make it seen and work on a longer-range technique to remodel the answer. I’ll present examples of those technical debt gadgets we created in a future weblog publish.
Instance 2: Heterogeneous Entry and Authentication-Management Options
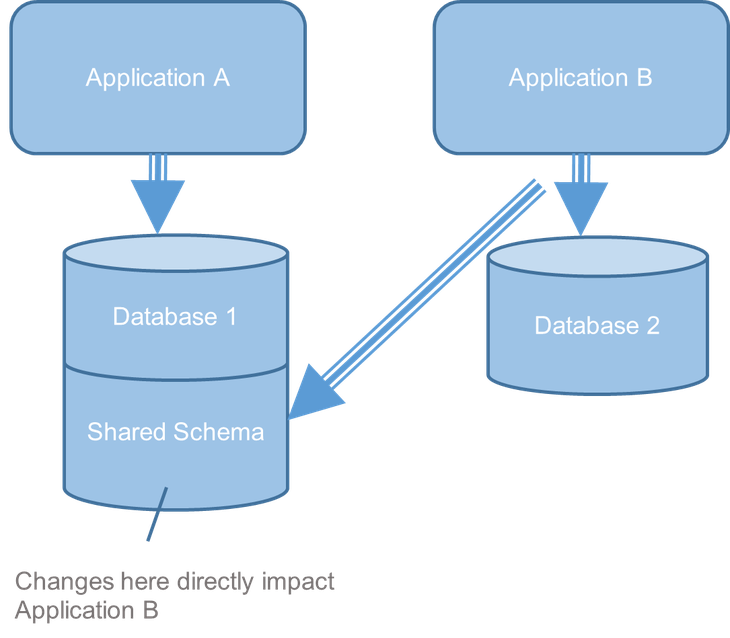
As structure evaluators for this group, we reviewed a number of challenge architectures wherein the groups have been implementing duplicative authentication and access-control functionality. Duplicative capabilities included
- skill to retailer function and permission data
- administrative functionality so as to add, change, and delete person permissions
- safe token technology
- skill to set and implement access-control insurance policies for software program companies (API calls)
A typical entry and authentication functionality was not supplied, so the person groups carried out this functionality in a heterogeneous method. Determine 2 depicts three completely different implementation kinds we noticed.
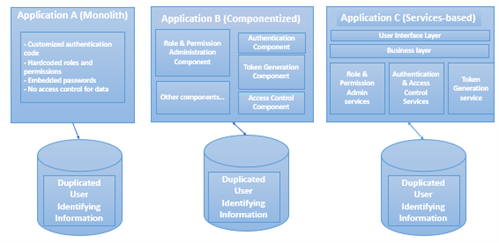
Determine 2: Heterogeneous Entry and Authentication-Management Options
- Software A is a legacy utility developed as a monolith, which is outdated and has a number of drawbacks. For instance, the groups wrote customized authentication code as an alternative of utilizing safe, verified vendor parts. We additionally discovered that roles and permission data have been hard-coded, and fewer safe password credentials have been used as an alternative of tokens for certification. Lastly, there was no application-level safety verify on the data-access layer.
- Software B was a extra fashionable implementation with a component-based architectural type. On this implementation, there was separation of authentication and access-control functionality into parts (e.g., roles and permissions administration, authentication, token technology, entry management). These parts have been shareable by a number of customers.
- Software C had a service-oriented structure. Companies used have been function and permission administration, authentication, token technology, and entry management.
These heterogeneous authentication and access-control options finally resulted in elevated safety and upkeep danger. For instance, and not using a widespread administration module, person accounts have been deactivated (moderately than deleted), leaving the group open to impersonation assaults. As well as, altering person permissions concerned operating error-prone guide database scripts to replace a number of databases. As an alternative of storing user-identifying knowledge in a single safe, authoritative knowledge supply, that knowledge was saved haphazardly in varied operational challenge databases.
Once more, the challenge groups noticed no issues with this example. When seen from the enterprise perspective, nevertheless, the safety and upkeep dangers have been clear. To make this debt seen, we created a technical debt merchandise and labored with the group to get it prioritized. I’ll share the technical debt merchandise we created for this instance within the subsequent publish.
Instance 3: Information-Warehouse Refresh Concern
Years in the past, the group invested in constructing an intensive knowledge warehouse. Throughout structure evaluations, we discovered that a number of groups weren’t utilizing the data-warehouse reporting. Quite, they have been operating many advanced nightly database jobs to repeat historic knowledge to their native databases. We discovered that the basis trigger for this method was a 48-hour lag in updating knowledge to the information warehouse. Customers weren’t glad with viewing stale knowledge, which left the information warehouse underutilized and added pointless complexity to the ecosystem.
As soon as once more, this example was positive with the challenge groups. When analyzed from the enterprise perspective, nevertheless, the enterprise and upkeep/price dangers grew to become clear. For instance, the information copying triggered an explosion in data-storage utilization. Complying to records-management necessities grew to become a nightmare after in depth copying made authoritative knowledge sources unclear. Operations and upkeep workers complained about spending time monitoring and updating the advanced net of ETL synchronization jobs. In consequence, we created a technical debt merchandise documenting the issue and advisable a redesign to scale back data-warehouse lag time.
Wanting Forward
On this publish, I described three examples of enterprise technical debt. We illustrated, by means of instance, the elusive nature of enterprise technical debt and the potential affect unchecked enterprise technical debt can have on a company. In our examples the affect of ETD gadgets wasn’t felt on the technical stage. Nonetheless, ignoring it resulted in multi-project or organization-wide dangers. These in flip elevated price, effectivity, or safety dangers for the group. I additionally mentioned the architect’s function in making use of technical debt practices to trace and remediate technical debt. In my subsequent publish, I’ll describe how we remediated these examples and the way we guided groups to use technical debt and governance practices to inspire motion.