Uber, in an replace, stated there’s “no proof” that customers’ non-public info was compromised in a breach of its inner pc programs that was found late Thursday.
“We’ve no proof that the incident concerned entry to delicate person information (like journey historical past),” the corporate stated. “All of our companies together with Uber, Uber Eats, Uber Freight, and the Uber Driver app are operational.”
The ride-hailing firm additionally stated it is introduced again on-line all the interior software program instruments it took down beforehand as a precaution, reiterating it is notified regulation enforcement of the matter.
It isn’t instantly clear if the incident resulted within the theft of some other info or how lengthy the intruder was inside Uber’s community.
Uber has not offered extra specifics of how the incident performed out past saying its investigation and response efforts are ongoing. However impartial safety researcher Invoice Demirkapi characterised Uber’s “no proof” stance as “sketchy.”
“‘No proof’ might imply the attacker did have entry, Uber simply hasn’t discovered proof that the attacker *used* that entry for ‘delicate’ person information,” Demirkapi stated. “Explicitly saying “delicate” person information moderately than person information general can also be bizarre.”
The breach allegedly concerned a lone hacker, an 18-year-old teenager, tricking an Uber worker into offering account entry by social engineering the sufferer into accepting a multi-factor authentication (MFA) immediate that allowed the attacker to register their very own system.
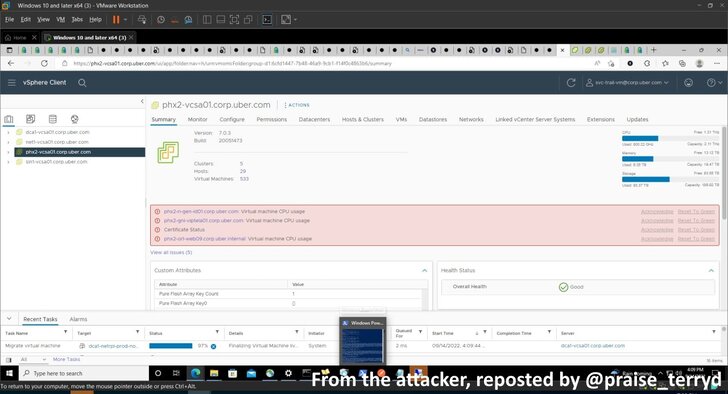
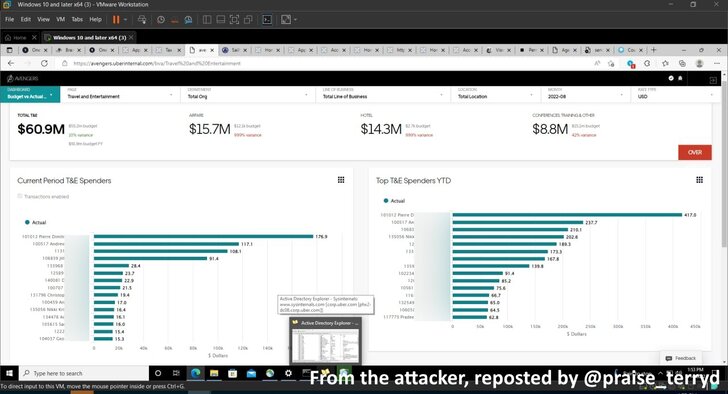
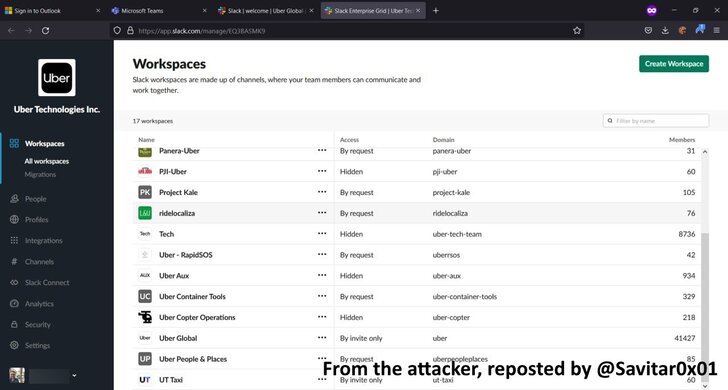
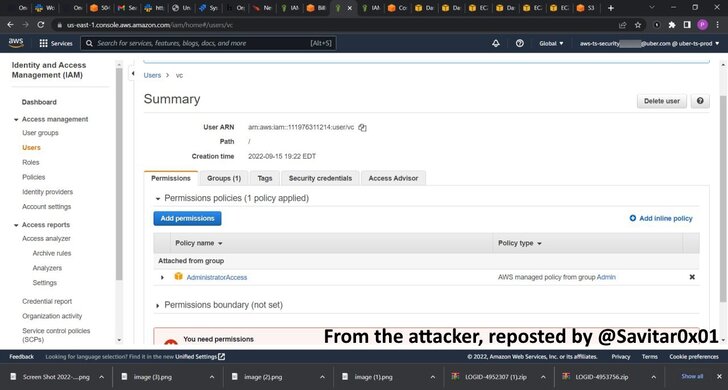
Upon gaining an preliminary foothold, the attacker discovered an inner community share that contained PowerShell scripts with privileged admin credentials, granting carte blanche entry to different crucial programs, together with AWS, Google Cloud Platform, OneLogin, SentinelOne incident response portal, and Slack.
Worryingly, as revealed by safety researcher Sam Curry, the teenager hacker can also be stated to have gotten maintain of privately disclosed vulnerability studies submitted through HackerOne as a part of Uber’s bug bounty program.
HackerOne has since moved to disable Uber’s account, however the unauthorized entry to unpatched safety flaws within the platform might pose an enormous safety threat to the San Francisco-based agency ought to the hacker decide to promote the knowledge to different risk actors for a fast revenue.
Thus far, the attacker’s motivations behind the breach are unclear, though a message posted by the hacker asserting the breach on Slack included a name for larger pay for Uber’s drivers.
A separate report from The Washington Publish famous that the attacker broke into the corporate’s networks for enjoyable and may leak the corporate’s supply code in a matter of months, whereas describing Uber’s safety as “terrible.”
“Many occasions we solely speak about APTs, like nation states, and we neglect about different risk actors together with disgruntled staff, insiders, and like on this case, hacktivists,” Ismael Valenzuela Espejo, vp of risk analysis and intelligence at BlackBerry, stated.
“Organizations ought to embody these as a part of their risk modeling workouts to find out who could have a motivation to assault the corporate, their talent stage and capabilities, and what the affect may very well be in response to that evaluation.”
The assault concentrating on Uber, in addition to the current string of incidents towards Twilio, Cloudflare, Cisco, and LastPass, illustrates how social engineering continues to be a persistent thorn within the flesh for organizations.
It additionally reveals that each one it takes for a breach to happen is an worker to share their login credentials, proving that password-based authentication is a weak hyperlink in account safety.
“As soon as once more, we see that an organization’s safety is just nearly as good as their most weak staff,” Masha Sedova, co-founder and president of Elevate Safety, stated in a press release.
“We have to assume past generic coaching, as a substitute let’s pair our riskiest staff with extra particular protecting controls. So long as we proceed to deal with cybersecurity as solely a technical problem, we are going to proceed to lose this battle,” Sedova added.
Incidents like these are additionally proof that Time-based One Time Password (TOTP) codes – usually generated through authenticator apps or despatched as SMS messages – are insufficient at securing 2FA roadblocks.
One approach to counter such threats is using phishing-resistant FIDO2-compliant bodily safety keys, which drops passwords in favor of an exterior {hardware} system that handles the authentication.
“MFA suppliers ought to *by default* mechanically lock accounts out quickly when too many prompts are despatched in a brief time frame,” Demirkapi stated, urging organizations to restrict privileged entry.