The U.S. authorities at present introduced a coordinated crackdown in opposition to QakBot, a posh malware household utilized by a number of cybercrime teams to put the groundwork for ransomware infections. The worldwide legislation enforcement operation concerned seizing management over the botnet’s on-line infrastructure, and quietly eradicating the Qakbot malware from tens of hundreds of contaminated Microsoft Home windows computer systems.
Dutch authorities inside an information middle with servers tied to the botnet. Picture: Dutch Nationwide Police.
In a world operation introduced at present dubbed “Duck Hunt,” the U.S. Division of Justice (DOJ) and Federal Bureau of Investigation (FBI) mentioned they obtained court docket orders to take away Qakbot from contaminated units, and to grab servers used to regulate the botnet.
“That is essentially the most vital technological and monetary operation ever led by the Division of Justice in opposition to a botnet,” mentioned Martin Estrada, the U.S. legal professional for the Southern District of California, at a press convention this morning in Los Angeles.
Estrada mentioned Qakbot has been implicated in 40 completely different ransomware assaults over the previous 18 months, intrusions that collectively value victims greater than $58 million in losses.
Rising in 2007 as a banking trojan, QakBot (a.okay.a. Qbot and Pinkslipbot) has morphed into a complicated malware pressure now utilized by a number of cybercriminal teams to arrange newly compromised networks for ransomware infestations. QakBot is mostly delivered by way of e mail phishing lures disguised as one thing reputable and time-sensitive, equivalent to invoices or work orders.
Don Alway, assistant director accountable for the FBI’s Los Angeles subject workplace, mentioned federal investigators gained entry to an internet panel that allowed cybercrooks to observe and management the actions of the botnet. From there, investigators obtained court-ordered approval to instruct all contaminated programs to uninstall Qakbot and to disconnect themselves from the botnet, Alway mentioned.
The DOJ says their entry to the botnet’s management panel revealed that Qakbot had been used to contaminate greater than 700,000 machines previously 12 months alone, together with 200,000 programs in america.
Working with legislation enforcement companions in France, Germany, Latvia, the Netherlands, Romania and the UK, the DOJ mentioned it was in a position to seize greater than 50 Web servers tied to the malware community, and practically $9 million in ill-gotten cryptocurrency from QakBot’s cybercriminal overlords. The DOJ declined to say whether or not any suspects have been questioned or arrested in reference to Qakbot, citing an ongoing investigation.
In keeping with latest figures from the managed safety agency Reliaquest, QakBot is by far essentially the most prevalent malware “loader” — malicious software program used to safe entry to a hacked community and assist drop further malware payloads. Reliaquest says QakBot infections accounted for practically one-third of all loaders noticed within the wild in the course of the first six months of this 12 months.
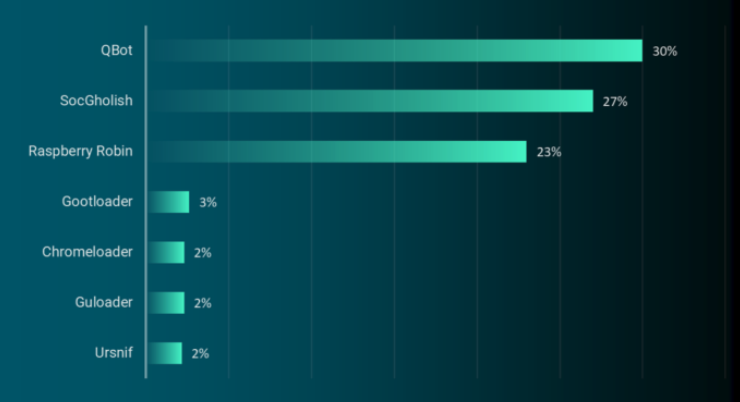
Qakbot/Qbot was as soon as once more the highest malware loader noticed within the wild within the first six months of 2023. Supply: Reliaquest.com.
Researchers at AT&T Alien Labs say the crooks chargeable for sustaining the QakBot botnet have rented their creation to numerous cybercrime teams over time. Extra not too long ago, nonetheless, QakBot has been intently related to ransomware assaults from Black Basta, a prolific Russian-language legal group that was thought to have spun off from the Conti ransomware gang in early 2022.
At the moment’s operation will not be the primary time the U.S. authorities has used court docket orders to remotely disinfect programs compromised with malware. In April 2022, the DOJ quietly eliminated malware from computer systems all over the world contaminated by the “Snake” malware, a good older malware household that has been tied to the GRU, an intelligence arm of the Russian army.
Paperwork printed by the DOJ in assist of at present’s takedown state that starting on Aug. 25, 2023, legislation enforcement gained entry to the Qakbot botnet, redirected botnet site visitors to and thru servers managed by legislation enforcement, and instructed Qakbot-infected computer systems to obtain a Qakbot Uninstall file that uninstalled Qakbot malware from the contaminated laptop.
“The Qakbot Uninstall file didn’t remediate different malware that was already put in on contaminated computer systems,” the federal government defined. “As a substitute, it was designed to forestall further Qakbot malware from being put in on the contaminated laptop by untethering the sufferer laptop from the Qakbot botnet.”
The DOJ mentioned it additionally recovered greater than 6.5 million stolen passwords and different credentials, and that it has shared this info with two web sites that permit customers examine to see if their credentials have been uncovered: Have I Been Pwned, and a “Test Your Hack” web site erected by the Dutch Nationwide Police.
Additional studying:
–The DOJ’s software for a search warrant software tied to Qakbot uninstall file (PDF)
–The search warrant software related to QakBot server infrastructure in america (PDF)
–The federal government’s software for a warrant to grab digital foreign money from the QakBot operators (PDF)
–A technical breakdown from SecureWorks

