What Time Is It?
It’s been a minute since my final replace on our community safety technique, however now we have been busy constructing some superior capabilities to allow true new-normal firewalling. As we launch Safe Firewall 4200 Sequence home equipment and Menace Protection 7.4 software program, let me carry you on top of things on how Cisco Safe elevates to guard your customers, networks, and purposes like by no means earlier than.
Safe Firewall leverages inference-based site visitors classification and cooperation throughout the broader Cisco portfoliowhich continues to resonate with cybersecurity practitioners. The truth of hybrid work stays a problem to the insertion of conventional community safety controls between roaming customers and multi-cloud purposes. The shortage of visibility and blocking from a 95% encrypted site visitors profileis a painful downside that hits increasingly organizations; a number of fortunate ones get in entrance of it earlier than the harm is completed. Each community and cybersecurity operations groups look to consolidate a number of level merchandise, scale back noise, and do extra with much less; Cisco Safe Firewall and Workload portfolio masterfully navigates all points of community insertion and menace visibility.
Safety Begins with Connectivity
Even the best and environment friendly safety answer is ineffective until it may be simply inserted into an present infrastructure. No group would undergo the difficulty of redesigning a community simply to insert a firewall at a crucial site visitors intersection. Safety gadgets ought to natively communicate the community’s language, together with encapsulation strategies and path resiliency. With hybrid work driving way more distributed networks, our Safe Firewall Menace Protection software program adopted by increasing the prevailing dynamic routing capabilities with application- and hyperlink quality-based path choice.
Utility-based coverage routing has been a problem for the firewall {industry} for fairly a while. Whereas some distributors use their present software identification mechanisms for this objective, these require a number of packets in a stream to cross via the system earlier than the classification may be made. Since most edge deployments use some type of NAT, switching an present stateful connection to a special interface with a special NAT pool is unimaginable after the primary packet. I at all times get a chuckle when studying these configuration guides that first inform you the right way to allow application-based routing after which promptly warning you towards it as a result of NAT getting used the place NAT is often used.
Our Menace Protection software program takes a special strategy, permitting frequent SaaS software site visitors to be directed or load-balanced throughout particular interfaces even when NAT is used. Within the spirit of leveraging the facility of the broader Cisco Safe portfolio, we ported over a thousand cloud software identifiers from Umbrella,that are tracked by IP addresses and Absolutely Certified Area Identify (FQDN) labels so the application-based routing determination may be made on the primary packet. Steady updates and inspection of transit Area Identify System (DNS) site visitors ensures that the appliance identification stays correct and related in any geography.
This application-based routing performance may be mixed with different highly effective hyperlink choice capabilities to construct extremely versatile and resilient Software program-Outlined Broad Space Community (SD-WAN) infrastructures. Safe Firewall now helps routing choices based mostly on hyperlink jitter, round-trip time, packet loss, and even voice high quality scores towards a specific monitored distant software. It additionally allows site visitors load-balancing with as much as 8 equal-cost interfaces and administratively outlined hyperlink succession order on failure to optimize prices. This permits a department firewall to prioritize trusted WebEx software site visitors on to the Web over a set of interfaces with the bottom packet loss. One other low-cost hyperlink can be utilized for social media purposes, and inner software site visitors is directed to the non-public knowledge heart over an encrypted Digital Tunnel Interface (VTI) overlay. All these interconnections may be monitored in real-time with the brand new WAN Dashboard in Firewall Administration Heart.
Divide by Zero Belief
The compulsory inclusion of Zero Belief Community Entry (ZTNA) into each vendor’s advertising and marketing collateral has change into a pandemic of its personal in the previous few years. Some safety distributors acquired so misplaced of their implementation that they’d so as to add an inner model management system. When you peel away the colourful wrapping paper, ZTNA is little greater than per-application Digital Non-public Community (VPN) tunnel with an aspiration for a less complicated consumer expertise. With hybrid work driving customers and purposes all over, a safe distant session to an inner payroll portal must be so simple as opening the browser – whether or not on or off the enterprise community. Usually sufficient, the hazard of carelessly carried out simplicity lies in compromising the safety.
Just a few distributors lengthen ZTNA solely to the preliminary software connection institution section. As soon as a consumer is multi-factor authenticated and licensed with their endpoint’s posture validated, full unimpeded entry to the protected software is granted. This strategy usually leads to shamingly profitable breaches the place legitimate consumer credentials are obtained to entry a susceptible software, pop it, after which laterally unfold throughout the remainder of the no-longer-secure infrastructure. Sufficiently motivated dangerous actors can go so far as acquiring a managed endpoint that goes together with these “borrowed” credentials. It’s not fully unusual for a disgruntled worker to make use of their respectable entry privileges for lower than noble causes. The straightforward conclusion right here is that the “authorize and neglect” strategy is mutually unique with the very notion of Zero Belief framework.
Safe Firewall Menace Protection 7.4 software program introduces a local clientless ZTNA functionality that topics distant software periods to the identical steady menace inspection as every other site visitors. In spite of everything, that is what Zero Belief is all about. A granular Zero Belief Utility Entry (ZTAA – see what we did there?) coverage defines particular person or grouped purposes and permits every one to make use of its personal Intrusion Prevention System (IPS) and File insurance policies. The inline consumer authentication and authorization functionality interoperates with each internet software and Safety Assertion Markup Language (SAML) succesful Id Supplier (IdP). As soon as a consumer is authenticated and licensed upon accessing a public FQDN for the protected inner software, the Menace Protection occasion acts as a reverse proxy with full TLS decryption, stateful firewall, IPS, and malware inspection of the stream. On prime of the safety advantages, it eliminates the necessity to decrypt the site visitors twice as one would when separating all variations of legacy ZTNA and inline inspection features. This vastly improves the general stream efficiency and the ensuing consumer expertise.
Let’s Decrypt
Talking of site visitors decryption, it’s usually seen as a vital evil so as to function any DPI features on the community layer – from IPS to Information Loss Prevention (DLP) to file evaluation. With practically all community site visitors being encrypted, even probably the most environment friendly IPS answer will simply waste processing cycles by wanting on the outer TLS payload. Having acknowledged this straightforward truth, many organizations nonetheless select to keep away from decryption for 2 primary causes: worry of extreme efficiency impression and potential for inadvertently breaking some crucial communication. With some safety distributors nonetheless not together with TLS inspected throughput on their firewall knowledge sheets, it’s laborious responsible these community operations groups who’re cautious round enabling decryption.
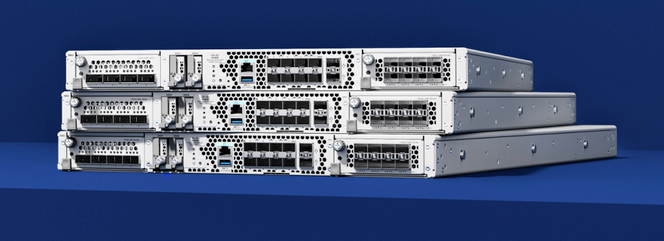
Constructing on the architectural innovation of Safe Firewall 3100 Sequence home equipment, the newly launched Safe Firewall 4200 Sequence firewalls kick the efficiency recreation up a notch. Similar to their smaller cousins, the 4200 Sequence home equipment make use of custom-built inline Discipline Programmable Gateway Array (FPGA) parts to speed up crucial stateful inspection and cryptography features straight inside the knowledge aircraft. This industry-first inline crypto acceleration design eliminates the necessity for pricey packet traversal throughout the system bus and frees up the principle CPU complicated for extra refined menace inspection duties. These new home equipment maintain the compact single Rack Unit (RU) type issue and scale to over 1.5Tbps of menace inspected throughput with clustering. They will even present as much as 34 hardware-level remoted and totally practical FTD cases for crucial multi-tenant environments.
These community safety directors who search for an intuitive approach of enabling TLS decryption will benefit from the utterly redesigned TLS Decryption Coverage configuration stream in Firewall Administration Heart. It separates the configuration course of for inbound (an exterior consumer to a personal software) and outbound (an inner consumer to a public software) decryption and guides the administrator via the required steps for every kind. Superior customers will retain entry to the complete set of TLS connection controls, together with non-compliant protocol model filtering and selective certificates blocklisting.
Not-so-Random Further Screening
Making use of decryption and DPI at scale is all enjoyable and video games, particularly with {hardware} home equipment which can be purpose-built for encrypted site visitors dealing with, however it’s not at all times sensible. The vast majority of SaaS purposes use public key pinning or bi-directional certificates authentication to stop man-in-the-middle decryption even by probably the most highly effective of firewalls. Irrespective of how briskly the inline decryption engine could also be, there’s nonetheless a pronounced efficiency degradation from indiscriminately unwrapping all TLS site visitors. With each operational prices and complexity in thoughts, most safety practitioners would favor to direct these valuable processing assets towards flows that current probably the most danger.
Fortunate for many who wish to optimize safety inspection, our industry-leading Snort 3 menace prevention engine consists of the power to detect purposes and doubtlessly malicious flows with out having to decrypt any packets. The integral Encrypted Visibility Engine (EVE) is the primary within the {industry} implementation of Machine Studying (ML) pushed stream inference for real-time safety inside the knowledge aircraft itself. We constantly prepare it with petabytes of actual software site visitors and tens of 1000’s of day by day malware samples from our Safe Malware Analytics cloud. It produces distinctive software and malware fingerprints that Menace Protection software program makes use of to categorise flows by inspecting just some outer fields of the TLS protocol handshake. EVE works particularly effectively for figuring out evasive purposes reminiscent of anonymizer proxies; in lots of instances, we discover it simpler than the standard pattern-based software identification strategies. With Safe Firewall Menace Protection 7.4 software program, EVE provides the power to mechanically block connections that classify excessive on the malware confidence scale. In a future launch, we are going to mix these capabilities to allow selective decryption and DPI of these high-risk flows for actually risk-based menace inspection.
The opposite trick for making our Snort 3 engine extra exact lies in cooperation throughout the remainder of the Cisco Safe portfolio. Only a few cybersecurity practitioners on the market prefer to manually sift via tens of 1000’s of IPS signatures to tailor an efficient coverage with out blowing out the efficiency envelope. Cisco Suggestions from Talos has historically made this process a lot simpler by enabling particular signatures based mostly on really noticed host working programs and purposes in a specific setting. Sadly, there’s solely a lot {that a} community safety system can uncover by both passively listening to site visitors and even actively poking these endpoints. Safe Workload 3.8 launch supercharges this capability by constantly feeding precise vulnerability info for particular protected purposes into Firewall Administration Heart. This permits Cisco Suggestions to create a way more focused record of IPS signatures in a coverage, thus avoiding guesswork, bettering efficacy, and eliminating efficiency bottlenecks. Such an integration is a chief instance of what Cisco Safe can obtain by augmenting community stage visibility with software insights; this isn’t one thing that every other firewall answer can implement with DPI alone.
Gentle Implausible Forward
Safe Firewall 4200 Sequence home equipment and Menace Protection 7.4 software program are essential milestones in our strategic journey, nevertheless it in no way stops there. We proceed to actively spend money on inference-based detection methods and tighter product cooperation throughout the whole Cisco Safe portfolio to carry worth to our clients by fixing their actual community safety issues extra effectively. As you will have heard from me on the current Nvidia GTC occasion, we’re actively growing {hardware} acceleration capabilities to mix inference and DPI approaches in hybrid cloud environments with Information Processing Unit (DPU) expertise. We proceed to spend money on endpoint integration each on the appliance aspect with Safe Workload and the consumer aspect with Safe Consumer to leverage stream metadata in coverage choices and ship a very hybrid ZTNA expertise with Cisco Safe Entry. Final however not least, we’re redefining the fragmented strategy to public cloud safety with Cisco Multi-Cloud Protection.
The sunshine of community safety continues to shine shiny, and we recognize you for the chance to construct the way forward for Cisco Safe collectively.
We’d love to listen to what you suppose. Ask a Query, Remark Beneath, and Keep Related with Cisco Safe on social!
Cisco Safe Social Channels
Share: