We not too long ago revealed a blogpost about Telekopye, a Telegram bot that helps cybercriminals rip-off folks in on-line marketplaces. Telekopye can craft phishing web sites, emails, SMS messages, and extra.
Within the first half, we wrote about technical particulars of Telekopye and hinted at hierarchical construction of its operational teams. On this second half, we deal with what we had been capable of find out about Neanderthals, the scammers who function Telekopye, their inner onboarding course of, completely different tips of commerce that Neanderthals use, and extra.
Key factors of this blogpost:
- How aspiring Neanderthals be a part of Telekopye teams.
- Detailed view of the entire scamming operation from the Neanderthals’ perspective.
- Evaluation of the rip-off situations and what every Neanderthal has to do as a way to achieve success.
- The instruments utilized by senior Neanderthals.
- Insights into tips that Neanderthals use to lure their victims.
- Highlights from an interview with one of many Telekopye directors.
Overview
Just lately, we revealed an evaluation of Telekopye; on this follow-up blogpost, we deal with the Neanderthals’ techniques and modus operandi. Our info comes from three principal sources:
- supply code of the bot itself,
- evaluation of Neanderthals’ conversations from scamming teams we’ve infiltrated, and
- our evaluation of Neanderthals’ inner documentation – a set of paperwork, graphs, photos, and extra – that they use as their very own private data base. Such info is supplied to newcomers to assist them with onboarding.
We might additionally prefer to thank Flare, who helped us in our analysis.
Becoming a member of a gaggle
Telekopye teams recruit new Neanderthals through ads in many various channels, together with underground boards. These ads clearly state the aim: to rip-off on-line market customers, as seen in Determine 1.
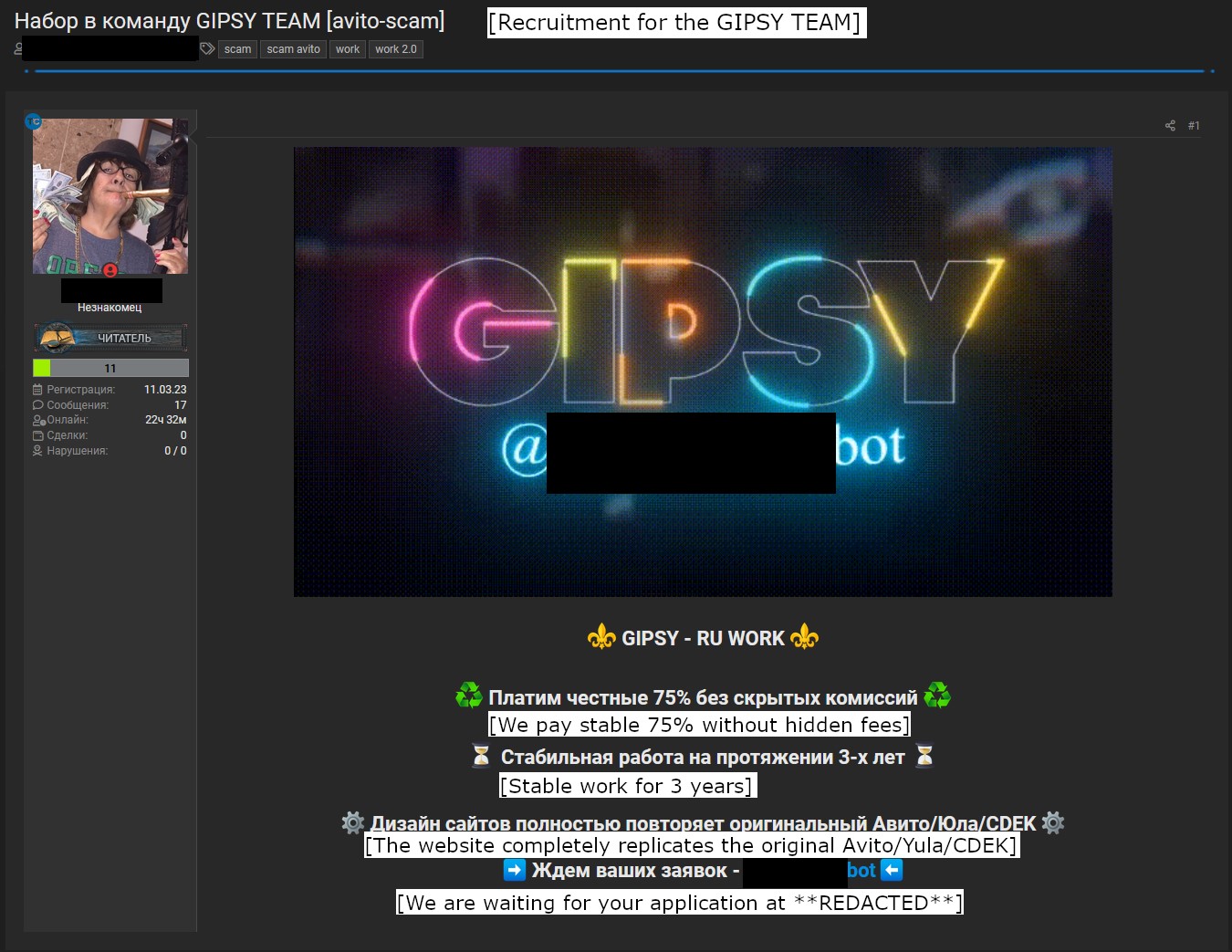
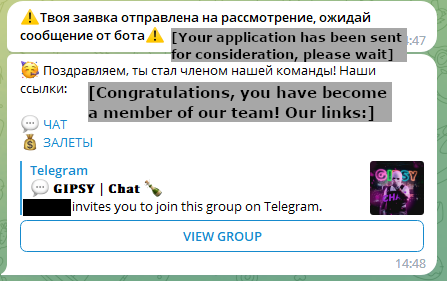
Aspiring Neanderthals are required to fill out an software, answering fundamental questions like the place they discovered in regards to the group and what expertise they’ve on this line of “work”. If authorised by current group members with sufficiently excessive function, the brand new Neanderthals can begin utilizing Telekopye to its full extent. Moreover, each Neanderthal is required to hitch two channels: a gaggle chat the place Neanderthals talk and the place guidelines and manuals are stored, and a separate channel the place transaction logs are stored. The method is demonstrated in Determine 2.
Varieties of scams
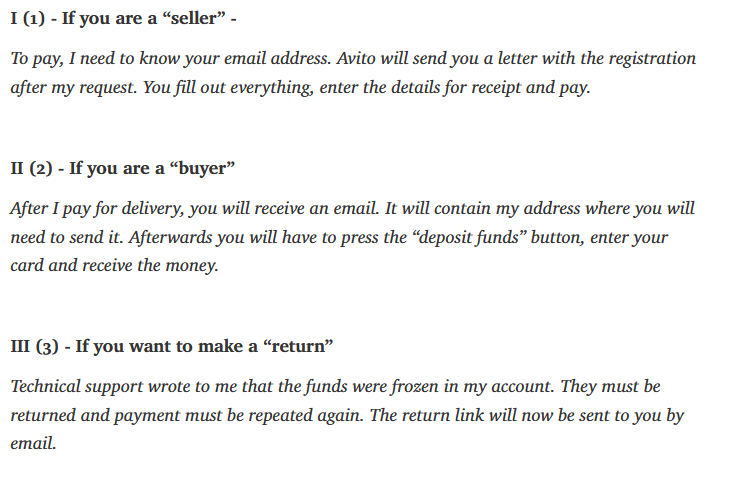
There are three principal rip-off situations:
1. Vendor, internally known as 1.0.
2. Purchaser, internally known as 2.0.
3. Refund.
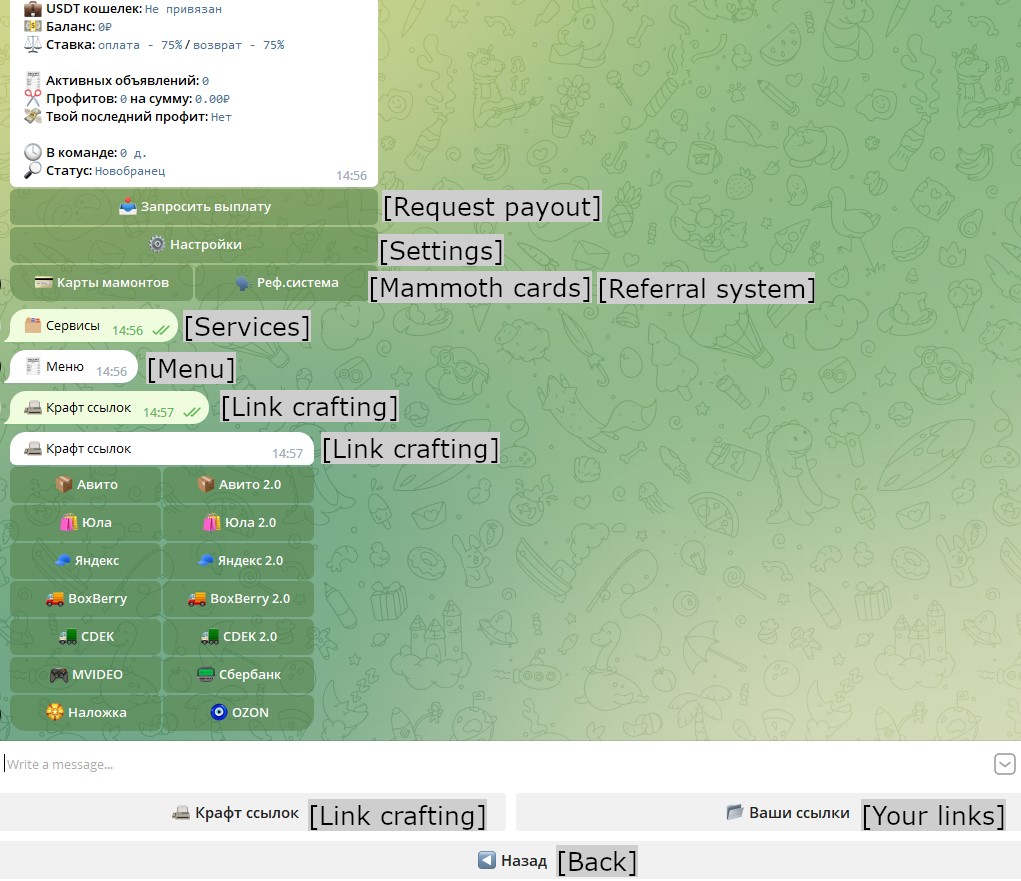
Determine 3 is the creation menu for the primary two rip-off situations, the place column 1 on the backside represents Vendor scams (1.0). The Refund rip-off state of affairs is then tied to every rip-off state of affairs individually. These rip-off sorts are described within the following subsections.
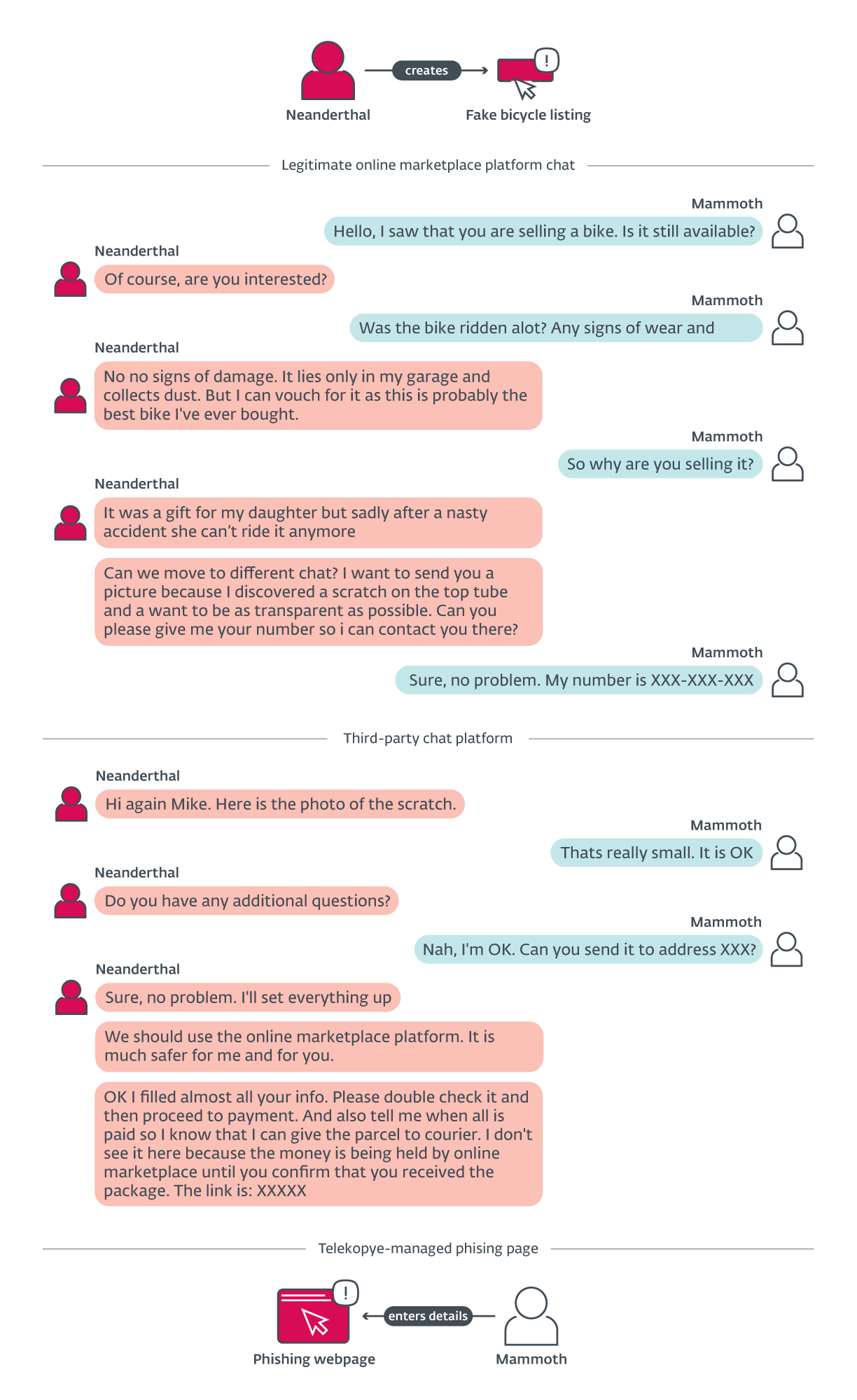
Vendor rip-off
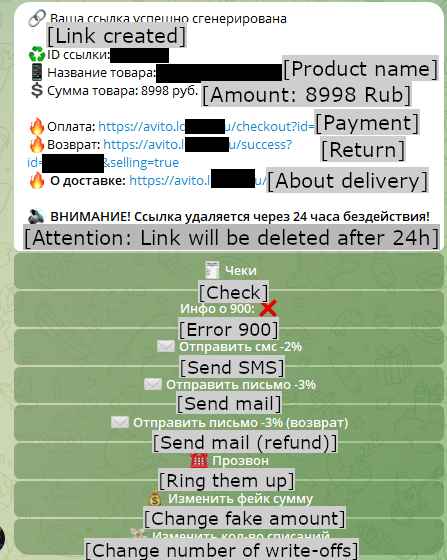
On this state of affairs, Neanderthals pose as sellers and attempt to lure unsuspecting Mammoths into shopping for some non-existent merchandise. When a Mammoth exhibits curiosity within the merchandise, the Neanderthal persuades the Mammoth to pay on-line reasonably than in individual. If the Mammoth agrees, the Neanderthal gives a hyperlink to a phishing web site supplied by Telekopye and punctiliously crafted to resemble the cost web page of the professional on-line market itemizing the reputed merchandise. Not like the professional internet web page although, this web page asks for a web-based banking login, bank card particulars (generally together with steadiness), or different delicate info. If the Mammoth enters this information, the phishing web site robotically steals it. Curiously, this information doesn’t turn out to be out there to the Neanderthal providing the merchandise on the market, however is processed by different Neanderthals. Determine 4 exhibits the Telekopye menu with already created phishing hyperlinks and Determine 5 demonstrates the communication throughout this rip-off state of affairs.
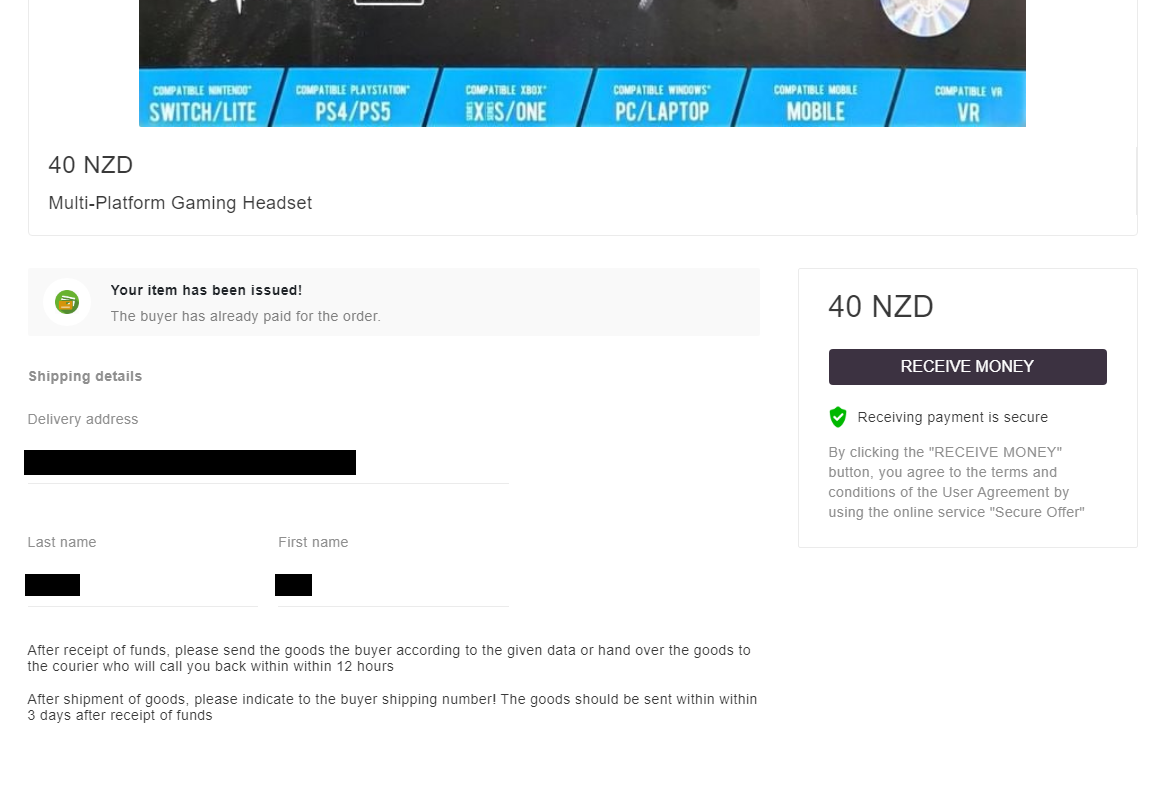
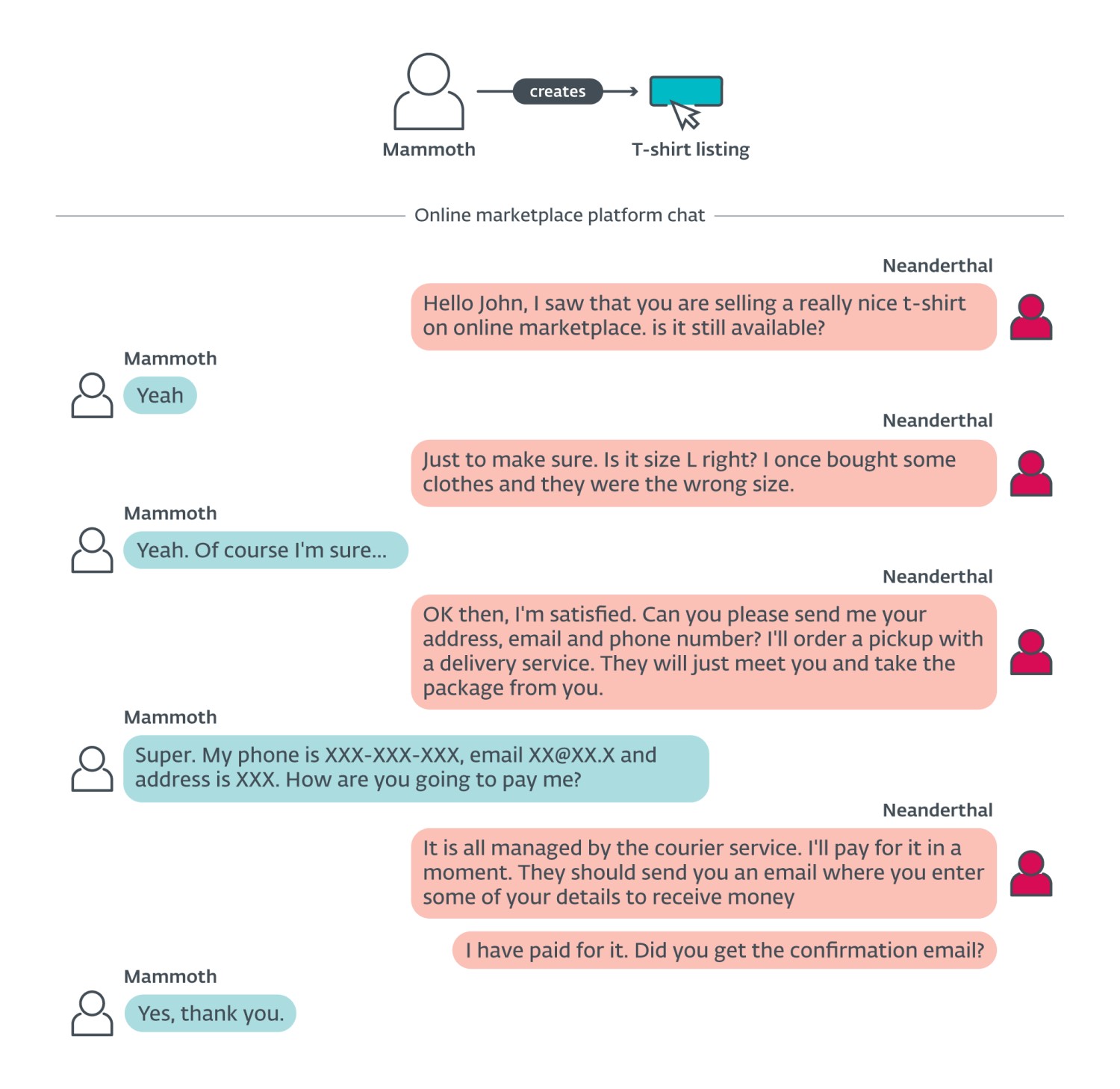
Purchaser rip-off
On this state of affairs, Neanderthals pose as consumers and so they analysis a Mammoth to focus on. They present curiosity within the merchandise a Mammoth is promoting and declare they already paid through the offering platform. The Neanderthals proceed to ship the Mammoths e-mail or SMS messages (created through Telekopye) with a hyperlink to a rigorously crafted phishing web site (additionally created through Telekopye; see Determine 6), claiming the Mammoth must click on this hyperlink as a way to obtain their cash from the platform. The remainder of the state of affairs is similar to the Vendor rip-off with slight variations throughout dialog (depicted in Determine 7).
Refund rip-off
On this state of affairs, Neanderthals create a state of affairs the place the Mammoth is anticipating a refund after which sends them a phishing e-mail with a hyperlink to the phishing web site, as soon as extra serving the identical function. Neanderthals both ship such emails to Mammoths they didn’t contact earlier, relying on them getting grasping and attempting to get this “refund” or they mix it with the Vendor rip-off state of affairs – when Mammoths complain that they didn’t obtain their items, Neanderthals ship them refund phishing emails in an try and rip-off them for a second time.
Modus operandi
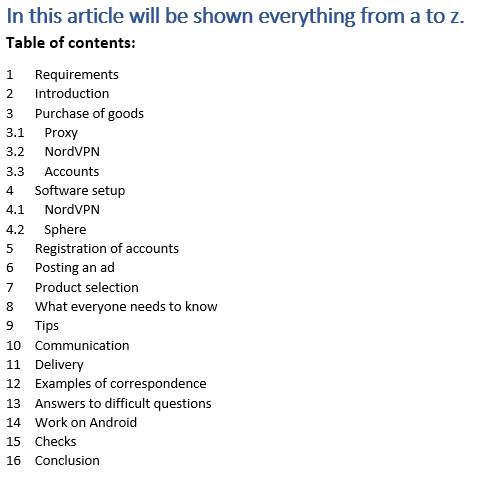
Now that we’ve got described the completely different rip-off situations, let’s take a look at what data the Neanderthals have gathered all through the years of their operation. Their inner documentation consists of photos, graphs, brief guides, and even complicated paperwork – the desk of contents of 1 such doc is illustrated in Determine 8.
We additionally found that there are two sorts of Neanderthals. The primary variety writes to each doable Mammoth and the opposite one is far pickier relating to on the lookout for a possible Mammoth. There’s a little bit of rivalry between them because the extra cautious variety argues that the “reckless” conduct of the much less cautious scammers may carry a bit extra revenue, however it creates far more public consciousness.
Preparation
Making ready for a rip-off differs based mostly on the chosen state of affairs. For the Vendor rip-off state of affairs, Neanderthals are suggested to organize extra images of the merchandise to be prepared if Mammoths ask for added particulars. If Neanderthals are utilizing photos they downloaded on-line, they’re imagined to edit them to make picture search tougher.
For the Purchaser rip-off state of affairs, the important thing a part of a Neanderthal’s preparation is how they select the Mammoth. Over time, Neanderthals have created pointers to observe when selecting their targets – they think about gender, age, expertise in on-line marketplaces, ranking, evaluations, variety of accomplished trades, and plenty of extra indicators.
Market analysis
In virtually each group of Neanderthals, we are able to discover references to manuals with on-line market analysis from which Neanderthals draw their methods and conclusions. The supply of this analysis is normally a research from 2017 by Avito and Knowledge Perception company. Determine 9 illustrates the outcomes of 1 such analysis, depicting graphs of gender, age, expertise, and revenue distribution on a selected on-line market.
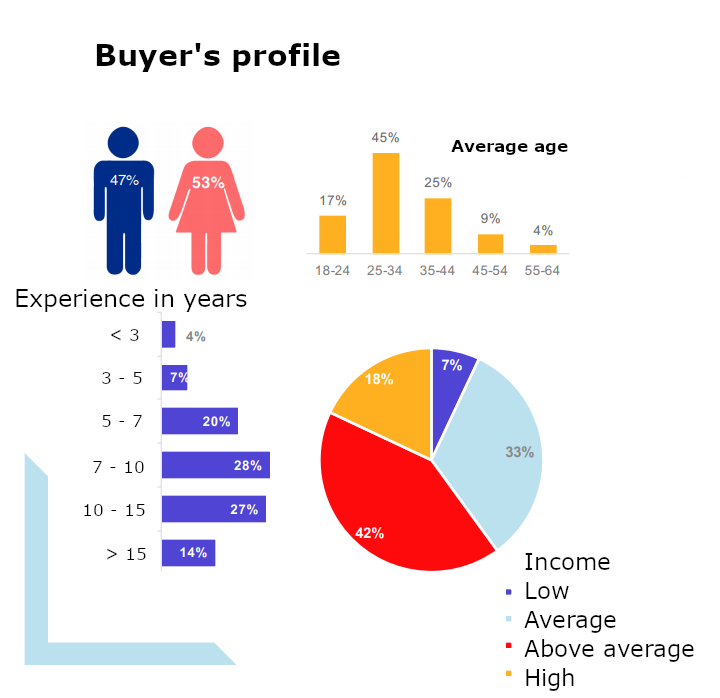
In the course of the Purchaser rip-off state of affairs, Neanderthals select their targets based mostly on the kind of gadgets they’re promoting. For example, some teams keep away from electronics fully. However, cellular units are a valued class for different teams. The worth of the merchandise can also be vital – if too excessive, then Neanderthals is not going to goal such Mammoths, as they consider that the Mammoths’ vigilance will probably be a lot larger by default. Manuals advocate that Neanderthals, within the Purchaser rip-off state of affairs, decide gadgets with a worth between 1,000 to 30,000 rubles (€9.50 to €290 as of 20th October, 2023).
The placement of the Mammoth can also be vital. Neanderthals focus extra on richer cities the place they anticipate extra listings and other people not preserving such a detailed eye on their very own funds.
Lastly, the scammers take the day of the month into consideration too. They purpose at days proper after folks obtain their paychecks, as they naturally anticipate they will have more cash of their financial institution accounts.
Internet scraping
Neanderthals make the most of internet scrapers to rapidly go although many on-line market listings and decide an ideal Mammoth who will fall for the rip-off; that is, as we’ve got already written, a vital preliminary a part of the Purchaser rip-off state of affairs.
We aren’t conscious of customized internet scrapers applied by Neanderthals, however their documentation mentions just a few supplied as professional companies. Neanderthals scrape the focused market for listings, particulars of things, and consumer info, which leads to a CSV or XML file. Neanderthals then use the outcomes to rapidly discover the fitting targets. We offer an instance of such a file in Determine 10.
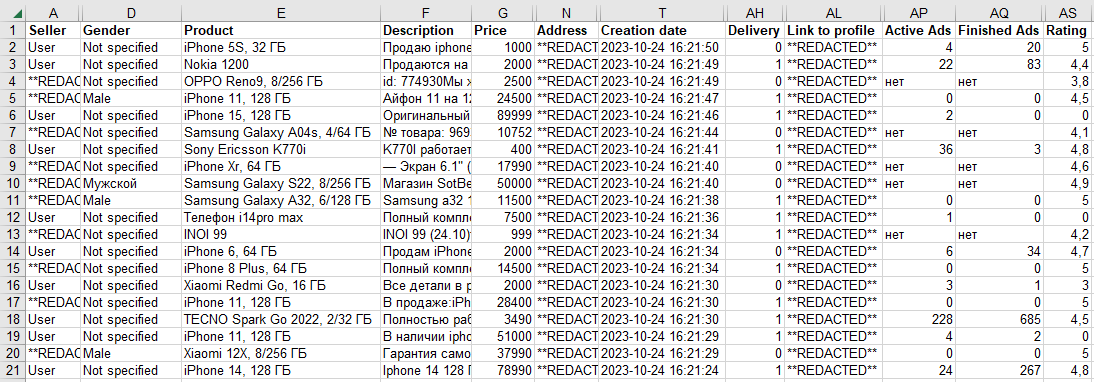
Person rankings and expertise are of explicit curiosity to Neanderthals, as they use this info to keep away from targets that they deem prone to spot the rip-off.
Avoiding in-person supply
For security causes, many Mammoths favor each in-person cost and in-person supply for bought items. That poses a difficulty for Neanderthals as they should persuade Mammoths to agree to make use of a supply service and on-line cost, in order that they’ll direct them to the phishing web site. Normally, they declare they’re too far-off or that they’re leaving town for a enterprise journey for just a few days. On the identical time, they attempt to look very within the merchandise to extend the possibilities that the Mammoth will conform to their suggestion.
Phishing internet web page hyperlink supply
Many professional on-line marketplaces have an built-in chat function and, alongside, moderation in place. Sending somebody a hyperlink via such a chat is normally a crimson flag and will very nicely end in a ban. Neanderthals attempt to overcome this impediment by persuading Mammoths to proceed their dialog on a unique chat platform that has much less monitoring.
Their arguments are similar to these towards in-person supply. They declare that they should depart their dwelling and can’t entry the chat from their cell phone, however are capable of proceed their discuss on one of many chat apps.
By their very own statistics, Neanderthals declare that about 50% of Mammoths will conform to a platform change and 20% of these will fall for the rip-off. This ends in a ten% success charge general.
One other favored technique of supply is utilizing e-mail or SMS. Telekopye is ready to rapidly generate convincing phishing messages. Neanderthals use tips (a few of them illustrated in Determine 11) to be taught Mammoths’ e-mail addresses or telephone numbers as a way to ship them such messages. The benefit of this method is that asking for a telephone quantity or e-mail deal with will probably not set off any crimson flags for neither Mammoth nor chatting platform and the Neanderthal doesn’t want to steer the Mammoth to switch to a unique chat platform.
Communication
No AI is utilized by Telekopye. This can be shocking, however Neanderthals consider that their method is superior and fewer prone to be noticed by monitoring mechanisms. Consequently, the huge portion of their inner documentation is targeted on communication methods to realize the very best outcomes.
Incomes the Mammoth’s belief is essential to the success of a rip-off. Neanderthals typically deliberately don’t instantly reply to each message however wait (generally even just a few hours) to create the phantasm that they’re busy with common on a regular basis life. Talking of time: they attempt to adapt to the Mammoth’s time zone so as to not increase suspicion.
They typically interact in chitchat first; they could even share a faux private story. The entire function is to search for crimson flags – indicators that may inform the Neanderthal that the Mammoth is just too suspicious or skilled. Since Neanderthals are targeted on revenue, they don’t need to spend time on Mammoths who find yourself recognizing the entice.
One other nice instance is that when Neanderthals make the most of the Purchaser rip-off state of affairs, they guarantee Mammoths that they’ve already paid for the merchandise. This, mixed with the design of the phishing e-mail that guarantees fast cash retrieval, ends in Mammoths being much less vigilant.
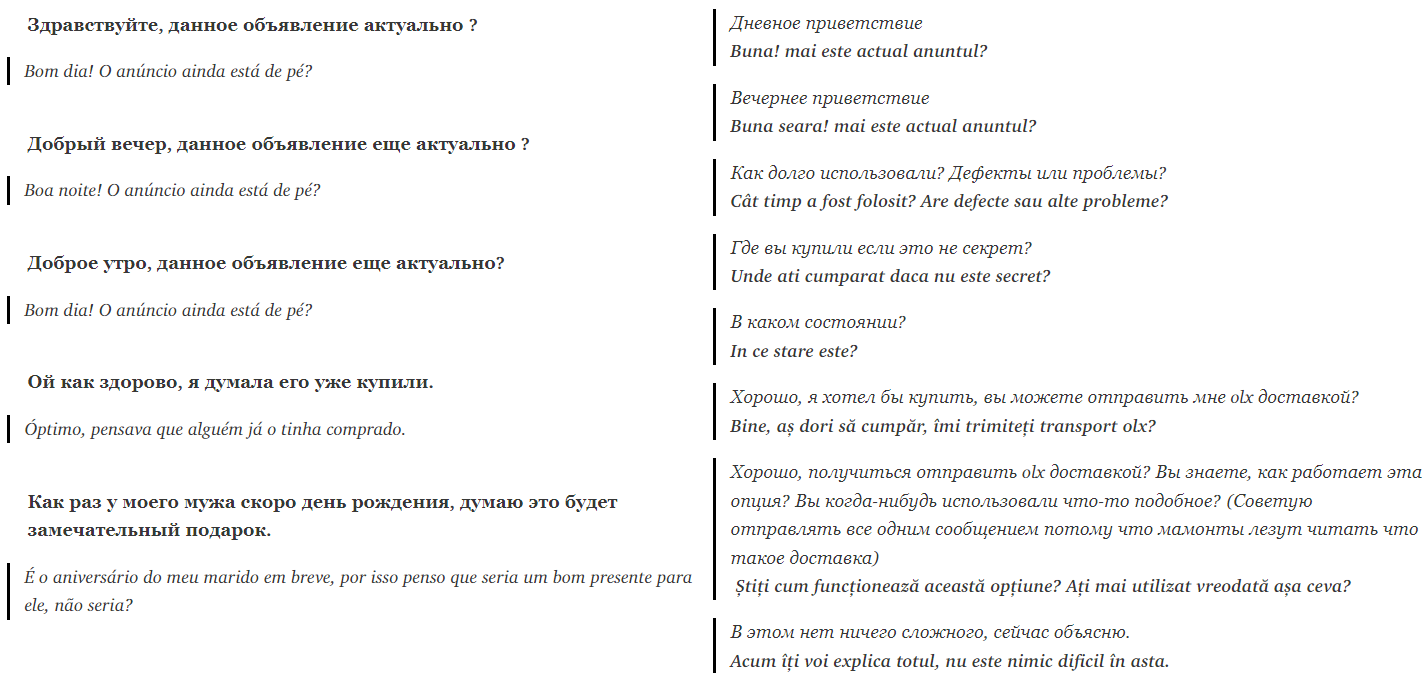
Skilled Neanderthals present newcomers with full conversations to take inspiration in; one such instance is supplied in Determine 12.
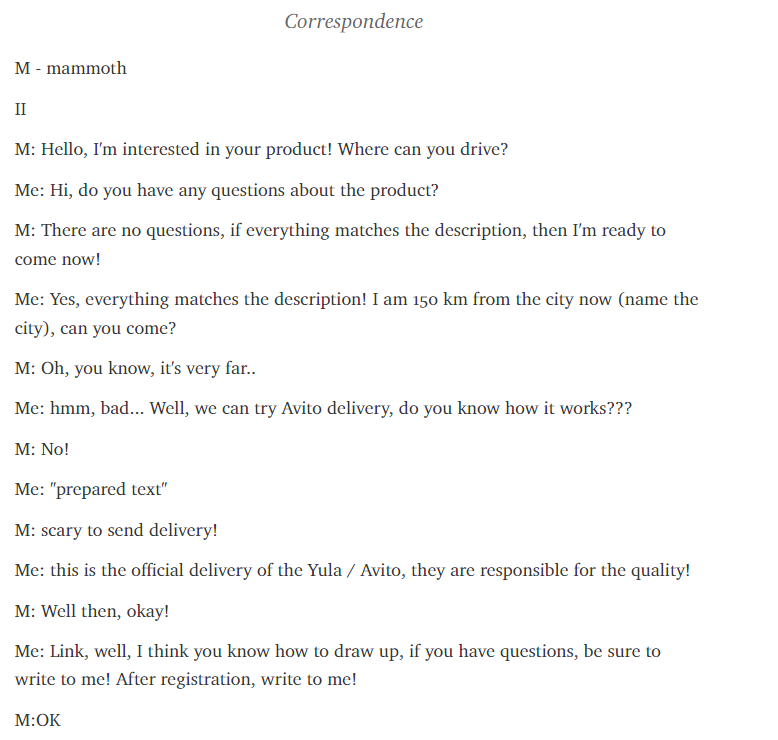
Neanderthals solely tolerate a sure stage of resistance from Mammoths – in the event that they deem the rip-off will not be prone to succeed, they transfer to a unique goal. Nonetheless, in the event that they really feel like they’ve virtually received, they’re very persuasive. An ideal instance is their documented method to conditions the place they efficiently harvest the Mammoth’s delicate information, however both the financial institution blocks the transaction or there are inadequate funds. In that case, Neanderthals could go so far as asking the Mammoth to make use of a member of the family’s card and even name their financial institution and authorize the switch themselves.
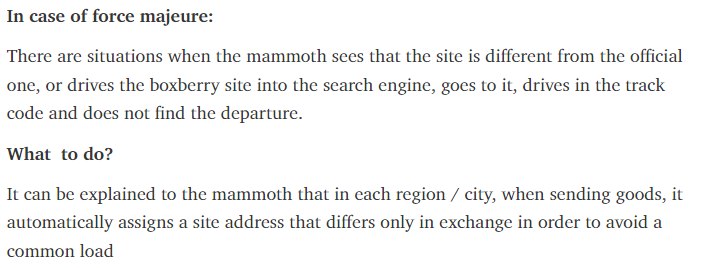
Neanderthals are able to reply many surprising questions relating to the legitimacy of their requests (see Determine 13).
Translation
As this operation targets Mammoths internationally, Neanderthals have to create the phantasm that they communicate the Mammoth’s language nicely sufficient. It’s fairly widespread to come across Russian-speaking Neanderthals who can write in English. Curiously, we had been capable of cross-reference the Telegram nicknames of many Neanderthals with language-learning platform profiles. These accounts normally said that the proprietor speaks Russian and English. Clearly, the connection may be coincidental.
For a few years Neanderthals used Google Translate. Since not less than 2021, Neanderthals moved in direction of different translators, reminiscent of DeepL, as (of their opinion) it understands context higher.
Moreover utilizing translators, they’ve created many translation tables over time, with verified translations of widespread phrases into a number of languages. These translations are mostly from Russian to European languages (see Determine 14). Neanderthals simply copy and paste these translated sentences into the chat with the Mammoth.
Group particular options
We must also point out that completely different teams have completely different quality-of-life enhancements to Telekopye. For instance, when producing a phishing hyperlink (a outcome might be seen in Determine 15), Neanderthals from one among these teams are requested a number of questions that allow them to have sure diploma of customization of every phishing web site. Probably the most fascinating is the query about guide/automated phishing web site technology. Within the case of guide technology, the Neanderthal should specify all info wanted to create the phishing web site. For Neanderthals posing as consumers, this takes from 10 to fifteen questions (Determine 16).
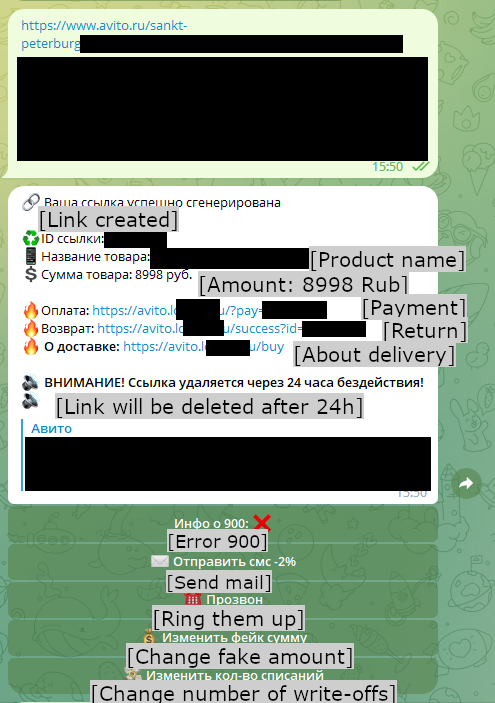
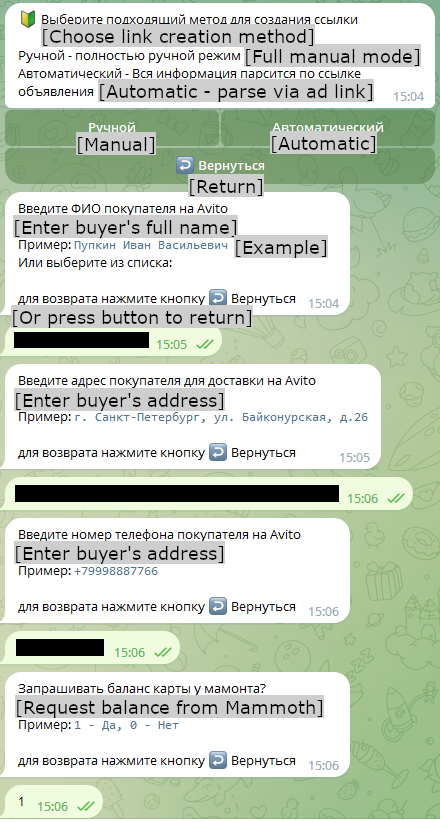
Within the case of automated web page technology, the Neanderthal solely must specify the URL of the merchandise to “purchase” and to reply 5 questions (like what the client’s title and telephone quantity are). Telekopye then scrapes all info from the web site and creates the phishing web site.
Anonymity and evasion
Neanderthals consider their teams are stuffed with “rats” (for instance, legislation enforcement or researchers). So, they religiously keep on with the principles, primarily no probing for info that might determine different members of the group. Breaking such guidelines could very nicely end in being banned. The golden rule is “work extra discuss much less”. As well as, they’re inspired to make use of VPNs, proxies, and TOR to remain protected. Neanderthals present newcomers with intensive guides and even interact in heated discussions over what packages or companies to make use of and why, together with browser preferences. Some Neanderthals even make the most of Orbot, a TOR variant for Android.
Cash
Neanderthals want to cover not solely their identities and site, but in addition their cash. Naturally, cryptocurrencies are the reply to that. We weren’t in a position to attract any conclusions relating to cryptocurrency desire.
Lastly, Neanderthals favor companies for which they’ll register utilizing solely a cell phone quantity. They think about this the very best method, since it’s comparatively simple to purchase a SIM card whereas not disclosing their id.
Bypassing automated detection
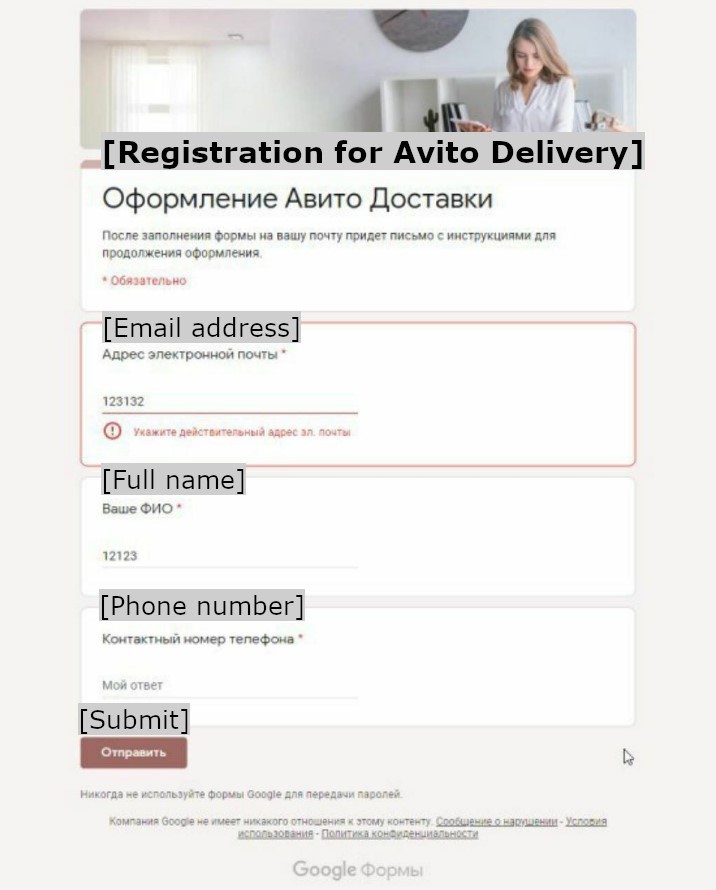
On-line market scams are nothing new. Over time, the platforms offering these companies have applied various methods to counter scammers and improve their clients’ safety. The Neanderthals are conscious of this and proceed to experiment with completely different approaches to beat the platforms’ moderation insurance policies. One early and reasonably silly try was to make the most of Google Kinds to phish private info from Mammoths (as seen in Determine 17). Contemplating the data they focused, the aim was to acquire a way to speak via a unique channel – e-mail or SMS – the place strict moderation wouldn’t happen.
These days, virtually all Neanderthals attempt to switch their Mammoths to much less policed, professional chat platforms. Neanderthals select them as a result of they consider banning accounts there takes time. Moreover, sending varied hyperlinks over chat platforms is widespread follow reasonably than suspicious conduct. As a bonus, virtually all people is conversant in such purposes, so Neanderthals don’t have to elucidate how they work.
Regardless of contemplating these platforms a lot safer, Neanderthals tread rigorously nonetheless. They keep away from sending too many messages in a brief time period and attempt to personalize messages for various Mammoths – Telekopye aids them tremendously on this effort.
Exploring new territories: Actual property rip-off
Among the Neanderthals’ teams point out a unique form of rip-off state of affairs – one which targets actual property renters. The rip-off works as follows. In the course of the preparation stage, Neanderthals write to a professional proprietor of an house, pretending to have an interest and ask for varied particulars, reminiscent of extra photos and how much neighbors the house has. The Neanderthals then take all this info and create their very own itemizing on one other web site, providing the house for lease. They reduce the anticipated market worth by about 20%. The remainder of the state of affairs is equivalent to Vendor rip-off state of affairs – the Neanderthal waits for a Mammoth to point out curiosity, and directs the Mammoth to pay a reservation price through a hyperlink that, after all, truly factors to a phishing web site.
Due to ESET’s telemetry we discovered that the phishing web sites used on this rip-off state of affairs are suspiciously much like those Telekopye creates for the Purchaser and Vendor situations. This, mixed with the rip-off being marketed by Telekopye teams, leads us to consider that there’s a connection. Nonetheless, we neither infiltrated any group specializing on this state of affairs nor obtained a Telekopye variant designed for it.
Interview
When crawling via completely different manuals, teams, and extra supplies, we discovered an interview with a Telekopye administrator that was accomplished on the finish of 2020. This helped us get a singular perception into the thoughts of a high-ranked Neanderthal. The interviewed Telekopye administrator operated a Telekopye group specializing in instructing new Neanderthals.
The administrator is at one level requested how he sees the way forward for this line of “work”. To that, he responds that “On-line market scams will at all times be current. It’s a lot tougher [to scam] than it was once because of banning insurance policies on completely different websites. However it’s simply not doable to cease all phishing on these websites”. He additionally says that he doesn’t rip-off anymore. He simply obtained uninterested in it and now works solely as administrator/tutor and that’s the reason why his group is so distinctive. “I don’t worry Mammoths. Each different Mammoth will threaten you once they understand they’ve been scammed. Apparently, everybody as of late is a spouse or a buddy of a minister of inner affairs”, says the administrator.
When requested whether or not he is considering creating a brand new rip-off undertaking, he says that he doesn’t have time for that. He moderates two channels, has an lively life-style, does loads of coaching, and he has solely 4 hours a day at dwelling.
He additionally confesses that he’s absolutely conscious that this sort of a job isn’t trustworthy however finds a typical excuse for himself. “… some folks will continually pay for hyperlinks, and somebody will continually throw them. Whoever tries arduous in life will succeed.”. On prime of that he says that if he feels sorry for Mammoth, he asks himself: “Why am I scamming them within the first place? Nicely… I solely steal from the wealthy (analysis be aware: Mammoths that in all probability have not less than €200 of their account) and if my conscience had been that fragile, I might go work as a supply man”.
Conclusion
On this second installment devoted to Telekopye, we’ve got targeted on what we discovered about Neanderthals. Due to gaining access to each their inner communication and their data base, we’ve got supplied not solely descriptions of various rip-off situations, however primarily a singular perception into their modus operandi and mindset.
Now we have demonstrated how the admission course of for newcomers seems to be like and the way Telekopye aids Neanderthals of their each day work. As well as, we’ve got proven that they in all probability are experimenting with actual property scams as nicely.
On-line market scams are probably not going away. As we demonstrated in the primary installment, we had been capable of uncover dozens of teams working Telekopye. That stated, by having our distinctive perception into the scammers’ operation, we consider loads might be discovered as a way to shield customers of such platforms from hurt.
IoCs and a MITRE ATT&CK methods desk had been supplied within the first a part of this evaluation, and are unchanged, so please seek advice from that article for these.
For any inquiries about our analysis revealed on WeLiveSecurity, please contact us at threatintel@eset.com.
ESET Analysis affords personal APT intelligence studies and information feeds. For any inquiries about this service, go to the ESET Menace Intelligence web page.


