Increasingly individuals these days want to purchase items on-line. And why not? It’s handy, items shall be delivered to the doorstep, and if you happen to select certainly one of many on-line marketplaces, it’s even attainable to avoid wasting cash. Sadly, scammers abuse this, concentrating on these providers and their clients for the scammer’s profit. They’ll create an inventory for items they don’t personal or don’t intend to promote. As soon as the sufferer pays, they seemingly disappear into the ether.
Not too long ago we discovered the supply code of a toolkit that helps scammers a lot of their endeavors that they don’t have to be notably well-versed in IT, however solely want a silver tongue to influence their victims. This toolkit is applied as a Telegram bot that, when activated, gives a number of easy-to-navigate menus within the type of clickable buttons that may accommodate many scammers directly. On this blogpost we are going to give attention to toolkit evaluation and options, and on the construction of the group(s) that use itWe now have named this toolkit Telekopye.
This weblog put up is the primary of a two-part sequence the place we take a more in-depth have a look at Telekopye and present among the key options which are very useful to scammers. Within the second half, we are going to focus extra on group operations.
Key factors of this blogpost
- Telekopye is a toolkit that operates as a Telegram bot and helps scammers rip-off their victims.
- Telekopye is designed to focus on on-line marketplaces; primarily (however not solely) these in style in Russia.
- Telekopye creates phishing internet pages from predefined templates, and generates and sends phishing emails and SMS messages.
- Customers and operators of Telekopye are organized in a transparent hierarchy.
Overview
We devised the title Telekopye as a portmanteau of Telegram and kopye (копье), the Russian phrase for spear, as a result of using extremely focused (aka spear-) phishing. Victims of this rip-off operation are referred to as Mammoths by the scammers (see Determine 1) and a number of other leads level to Russia because the nation of origin of the toolkit’s authors and customers. For the sake of readability, and following the identical logic, we are going to discuss with the scammers utilizing Telekopye as Neanderthals.

Determine 1. One of many memes (Mammoth misplaced) from a bunch dialog posted by Neanderthals
Telekopye was uploaded to VirusTotal a number of occasions, primarily from Russia, Ukraine, and Uzbekistan, from the place Neanderthals normally function primarily based on the language utilized in feedback within the code (we now have added machine translations to English in brackets in varied pictures on this blogpost) and the vast majority of focused markets. Regardless that the principle targets of Neanderthals are on-line markets in style in Russia, like OLX and YULA, we noticed that their targets are additionally on-line markets that aren’t native to Russia, like BlaBlaCar or eBay, and even others that don’t have anything in frequent with Russia, like JOFOGAS and Sbazar. Simply for instance how large a few of these marketplaces are, the OLX platform had, in accordance with Fortune, 11 billion web page views and eight.5 million transactions monthly in 2014.
We had been capable of accumulate a number of variations of Telekopye, suggesting steady improvement. All of those variations are used to create phishing internet pages, and ship phishing e-mail and SMS messages. As well as, some variations of Telekopye can retailer sufferer information (normally card particulars or e-mail addresses) on disk the place the bot is run. Telekopye could be very versatile however doesn’t include any chatbot AI performance. Therefore, it doesn’t really carry out the scams; it solely eases the era of content material utilized in such scams. In July 2023, we detected new domains that match the modus operandi of Telekopye operators, so they’re nonetheless lively. The most recent model of Telekopye we now have been capable of collect was from April eleventh, 2022. We assess that Telekopye has been in use since no less than 2015 and, primarily based on snippets of dialog between Neanderthals, that totally different scammer teams are utilizing it.
Telekopye rip-off situation
Because of human nature, scamming in on-line marketplaces appears to be very straightforward. It normally comes right down to a number of key components of the rip-off, as seen in Determine 2, that Neanderthals comply with. First, Neanderthals discover their victims (Mammoths). Then they attempt to earn their belief and persuade them that they’re legit (why that is wanted we are going to talk about partially 2). When Neanderthals assume {that a} Mammoth sufficiently trusts them, they use Telekopye to create a phishing internet web page from a premade template and ship the URL to the Mammoth (the URL may also be despatched through SMS or e-mail). After the mammoth submits card particulars through this web page, the Neanderthals use these card particulars to steal cash from the Mammoth’s credit score/debit card, whereas hiding the cash utilizing a number of totally different strategies equivalent to laundering it via cryptocurrency. Primarily based on a number of dialog snippets, we assess that some crypto mixers are concerned. There’s a lacking hyperlink between when cash is scammed from the Mammoth and the payout to the Neanderthals, which is normally in cryptocurrency.
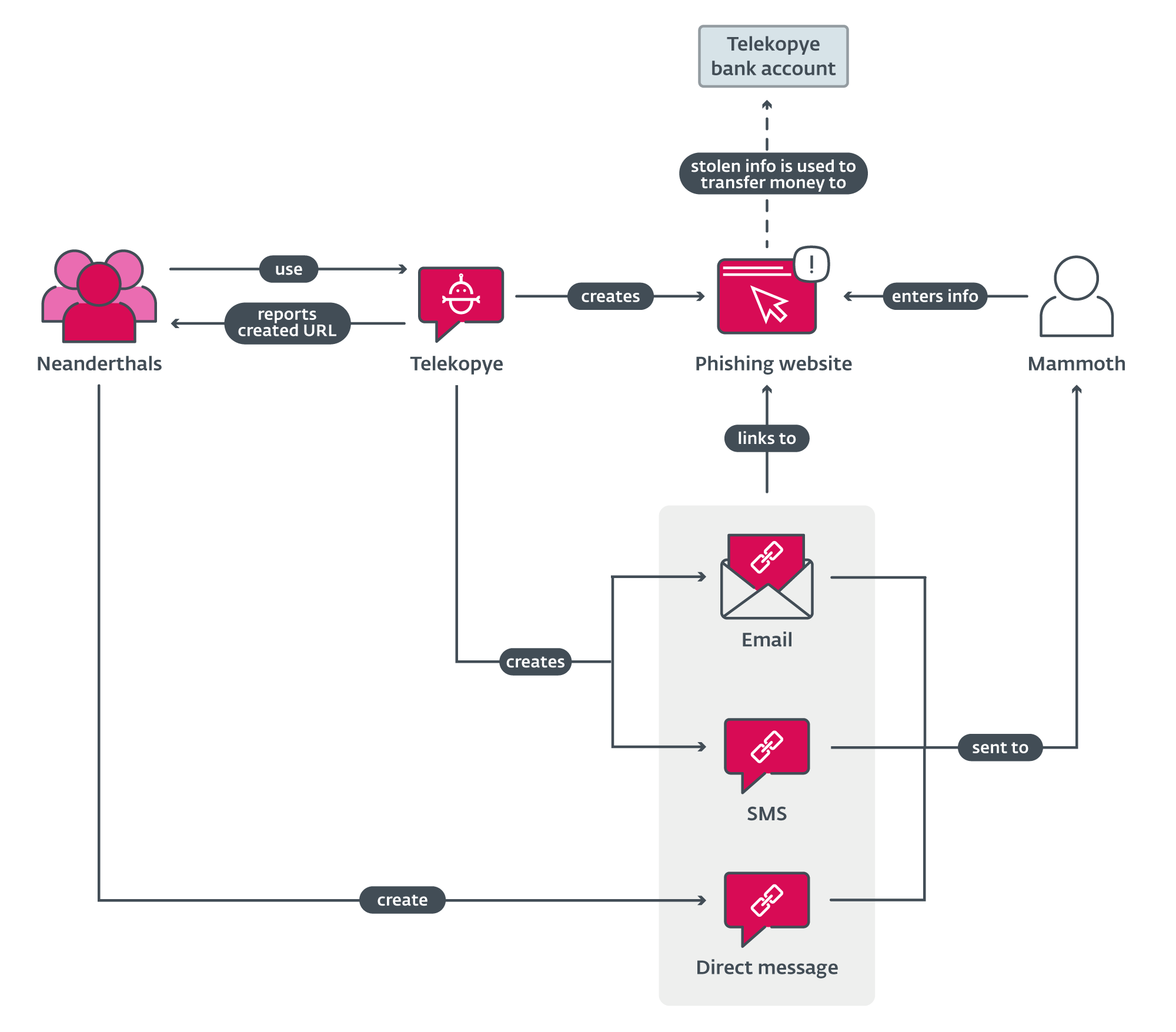
Determine 2. Overview of the Neanderthals’ rip-off
Telekopye performance
Telekopye has a number of totally different functionalities that Neanderthals can use to their full extent. These functionalities embody sending phishing emails, producing phishing internet pages, sending SMS messages, creating QR codes, and creating phishing screenshots. Within the following sections, we are going to give attention to probably the most helpful components of Telekopye for the typical Neanderthal.
Interface
Each Telegram group utilizing Telekopye consists of a number of Neanderthals that function concurrently and independently. Performance is obtainable via buttons, more likely to make scamming simpler for Neanderthals.
Determine 3 exhibits one of many menus of Telekopye in a working Telegram group. Significantly noteworthy are the buttons “My advertisements”, exhibiting all opened listings (ongoing rip-off ads) every Neanderthal has, and “My profile”, permitting Neanderthals to see their profile info on this platform, such because the variety of scams pulled off, sum of money prepared for subsequent payout, and many others.
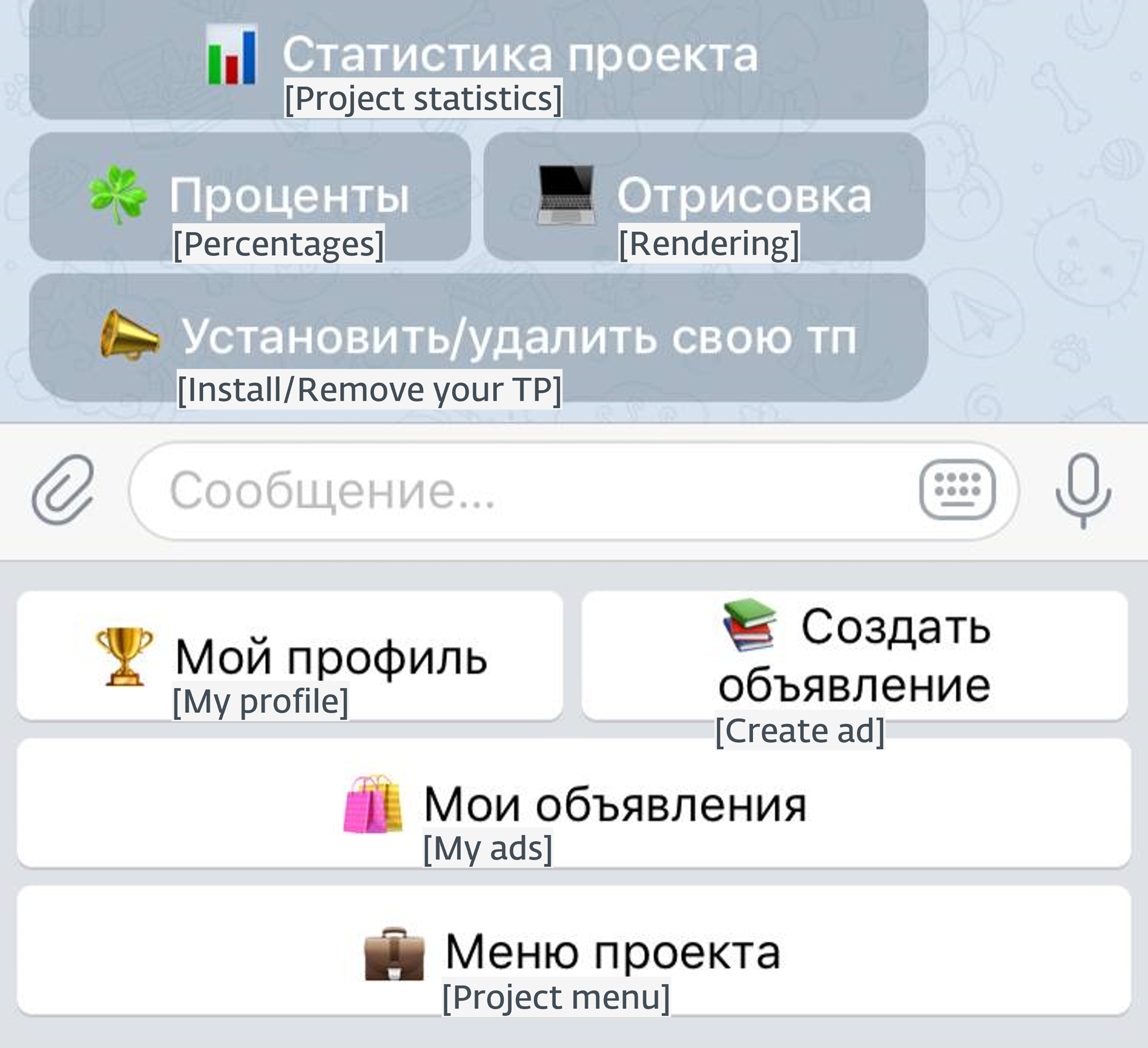
Determine 3. Instance of Telekopye operator interface in a Telegram group
Phishing web page era
The core function of Telekopye is that it creates phishing internet pages from predefined HTML templates on demand. A Neanderthal must specify the sum of money, product title and, primarily based on the template, extra info like location to which the product shall be despatched, image, weight, and purchaser’s title. Then Telekopye takes all this info and creates a phishing internet web page. These phishing internet pages are designed to imitate totally different fee/financial institution login websites, credit score/debit card fee gateways, or just fee pages of various web sites.
To make the phishing web site creation course of simpler, these web site templates are organized by international locations they aim. Determine 4 exhibits a easy creation menu the place some templates are sorted in accordance with totally different international locations. The one outlier is BlaBlaCar for country-independent car-sharing providers.

Determine 4. Creation menu for various phishing pages. Discover the Swedish flag is incorrectly related to Switzerland within the prime, proper nook.
Determine 5 exhibits one such phishing internet web page, seemingly not absolutely perfected but.
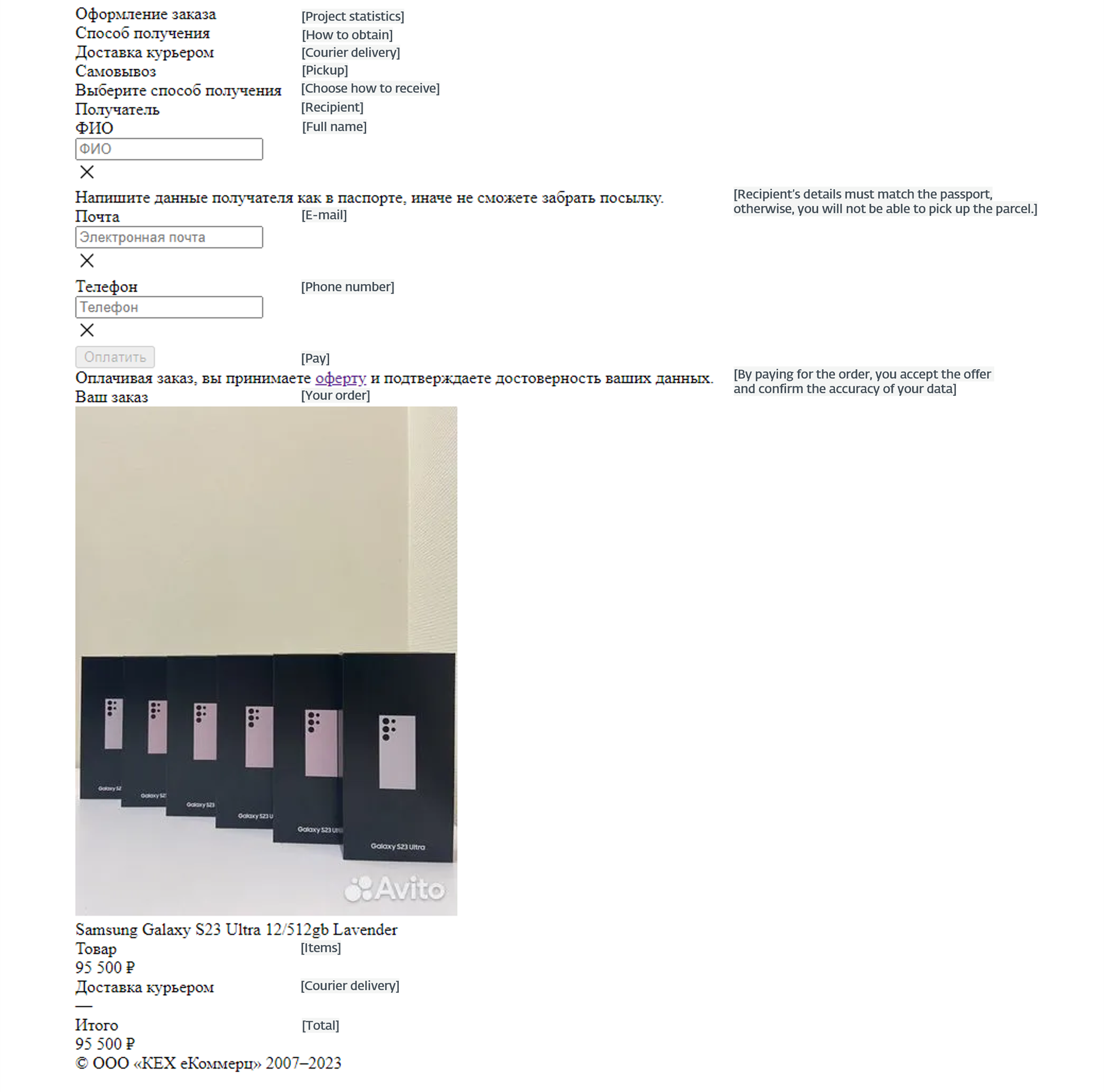
Determine 5. Crammed in uncompleted phishing web site template (machine translations in brackets)
The completed product is seen in Determine 6, an eBay internet web page look-alike that’s virtually unrecognizable from the unique (or no less than appears to be like like one thing one would count on from the legit web site). By clicking the Obtain %amount2% EUR button, a Mammoth is proven a faux credit score/debit card gateway.
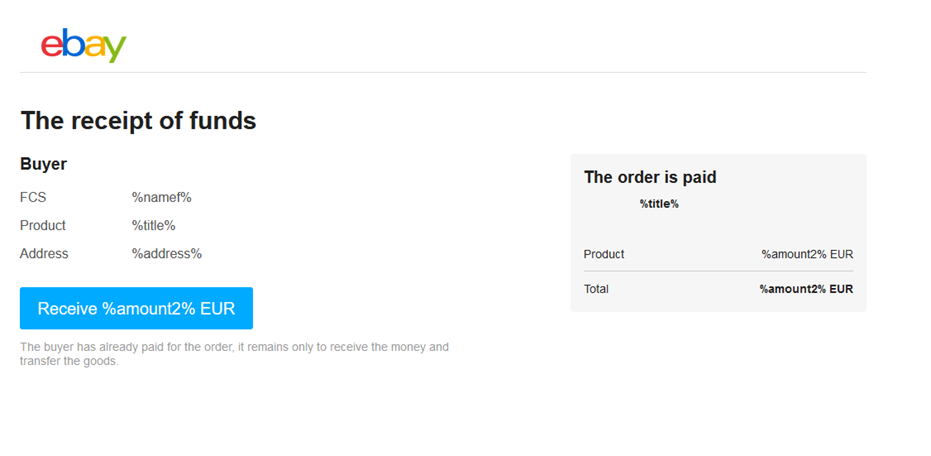
Determine 6. Completed template for phishing internet web page impersonating eBay
These phishing domains aren’t straightforward to identify. Often, Neanderthals register a website after which create subdomains for every focused market in such a manner that the ultimate URL begins with the anticipated model title. In Desk 1 discover that just one area – olx.id7423[.]ru – is used to focus on the favored market OLX. An instance of a legit area for the OLX market is olx.ua. Briefly, they normally use .ru as their top-level domains and transfer second-level domains to the third-level area’s place.
Desk 1. Examples of a number of domains used for phishing
|
Service title (RU) |
Service title |
Phishing area |
Reliable area |
|
Авито |
Avito |
avito.id7423[.]ru |
avito.ru |
|
Юла |
Youla |
youla.id7423[.]ru |
youla.ru |
|
Боксберри |
Boxberry |
boxberry.id7423[.]ru |
boxberry.ru |
|
Сдек |
Cdek |
cdek.id7423[.]ru |
cdek.ru |
|
Авито Аренда |
Avito-rent |
avito-rent.id7423[.]ru |
avito.ru |
|
OLX KZ |
OLX |
olx.id7423[.]ru |
olx.kz |
|
Куфар |
Kufar |
kufar.id7423[.]ru |
kufar.by |
|
OLX UZ |
OLX UZ |
olx.id7423[.]ru |
olx.uz |
|
OLX RO |
OLX RO |
olx.id7423[.]ru |
olx.ro |
|
OLX PL |
OLX PL |
olx.id7423[.]ru |
olx.pl |
|
OLX UA |
OLX UA |
olx.id7423[.]ru |
olx.ua |
|
СБАЗАР |
Sbazar |
sbazar.id7423[.]ru |
sbazar.cz |
|
IZI ua |
IZI ua |
izi.id7423[.]ru |
izi.ru |
|
OLX BG |
OLX BG |
olx.id7423[.]ru |
olx.bg |
Transactions and payout
Neanderthals don’t switch cash stolen from Mammoths to their very own accounts. As a substitute, all of the Neanderthals use a shared Telekopye account managed by the Telekopye administrator. Telekopye retains monitor of how profitable every Neanderthal is by logging related contributions to that shared account – both in a easy textual content file or a SQL database.
As a consequence, Neanderthals receives a commission by the Telekopye administrator. Cost is break up into three components:
1. Fee to the Telekopye administrator.
2. Fee to recommender (suggestion system is mentioned later within the weblog put up).
3. Precise payout.
The fee to the Telekopye administrator is 5–40%, relying on the Telekopye model and Neanderthal position (roles are additionally mentioned later within the weblog put up).
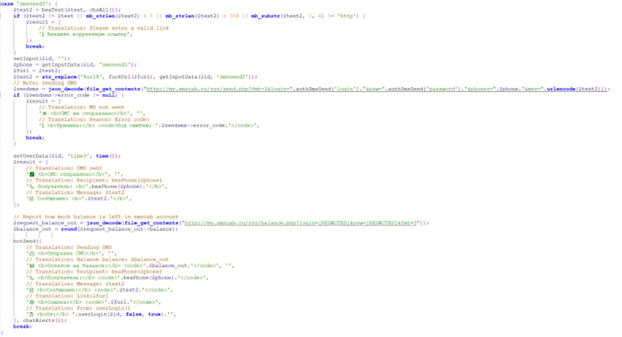
As soon as a Neanderthal turns into eligible for a payout, he asks Telekopye for one. Telekopye checks the Neanderthal’s steadiness, remaining request is accepted by the Telekopye administrator and, lastly, funds are transferred to the Neanderthal’s cryptocurrency pockets. In some Telekopye implementations, step one, asking for a payout, is automated and the negotiation is initiated each time a Neanderthal reaches a sure threshold of stolen cash from efficiently pulled off scams (e.g., 500 RUB). The method of the handbook payout request is illustrated in Determine 7 and the related a part of the Telekopye supply code in Determine 8.
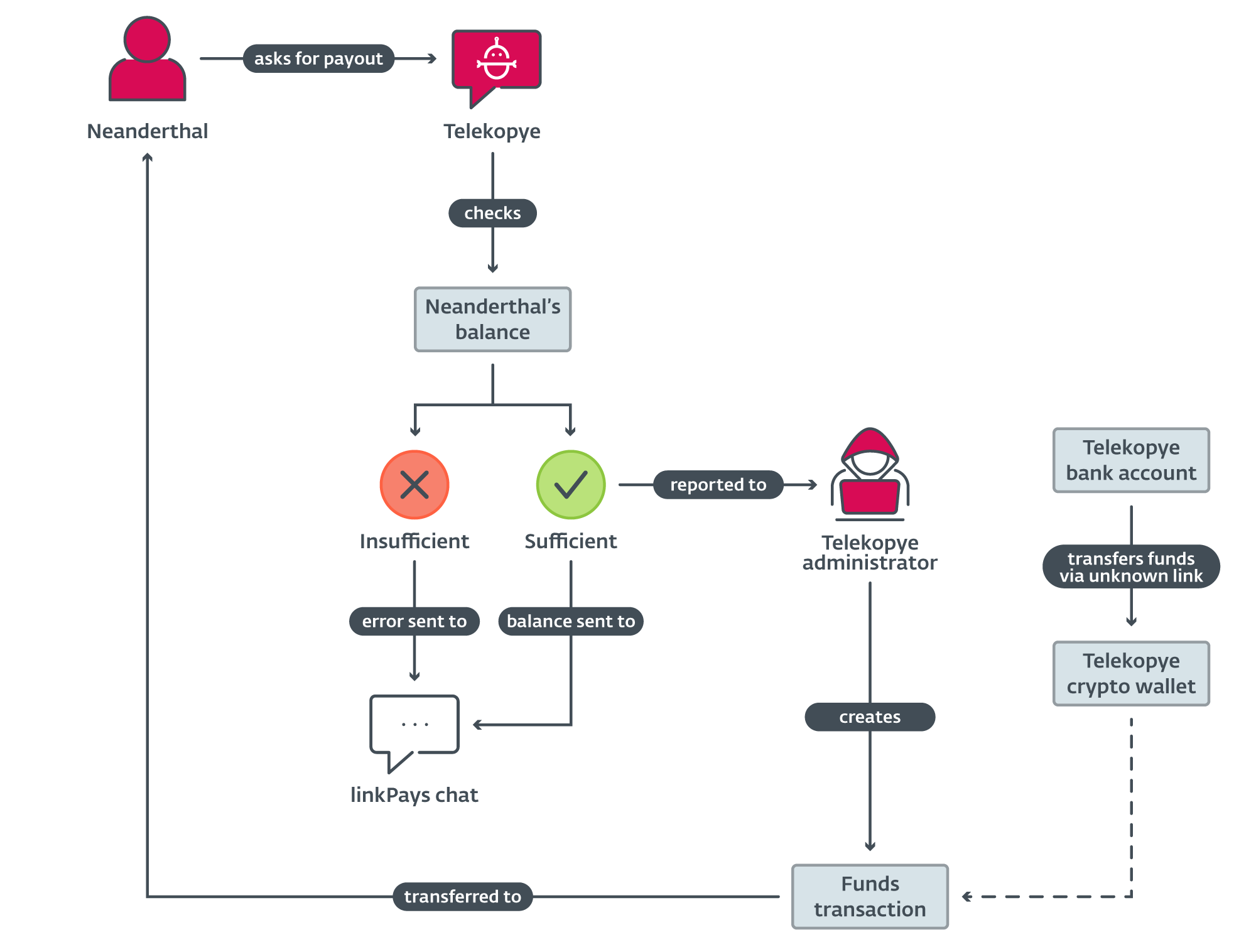
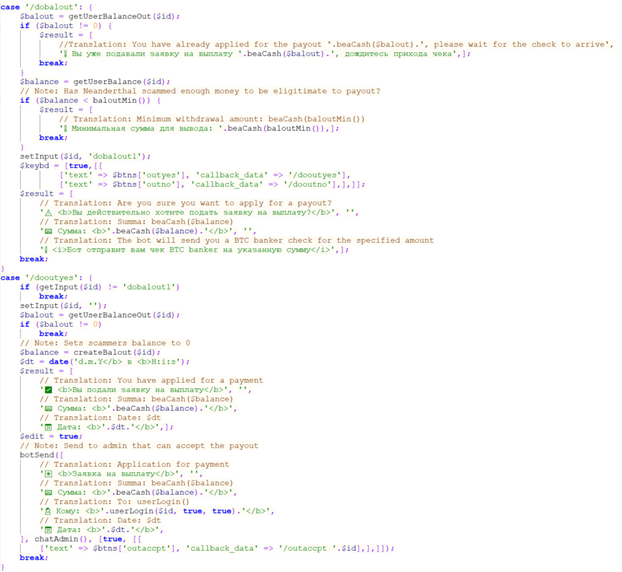
Determine 8. Code that’s executed each time a Neanderthal desires to withdraw funds
Telekopye retains logs of processed payouts in a separate Telegram channel. A Neanderthal who’s paid additionally receives a hyperlink to this channel, in all probability to have the ability to confirm that the transaction is logged. Determine 9 exhibits an instance of such a logs channel.
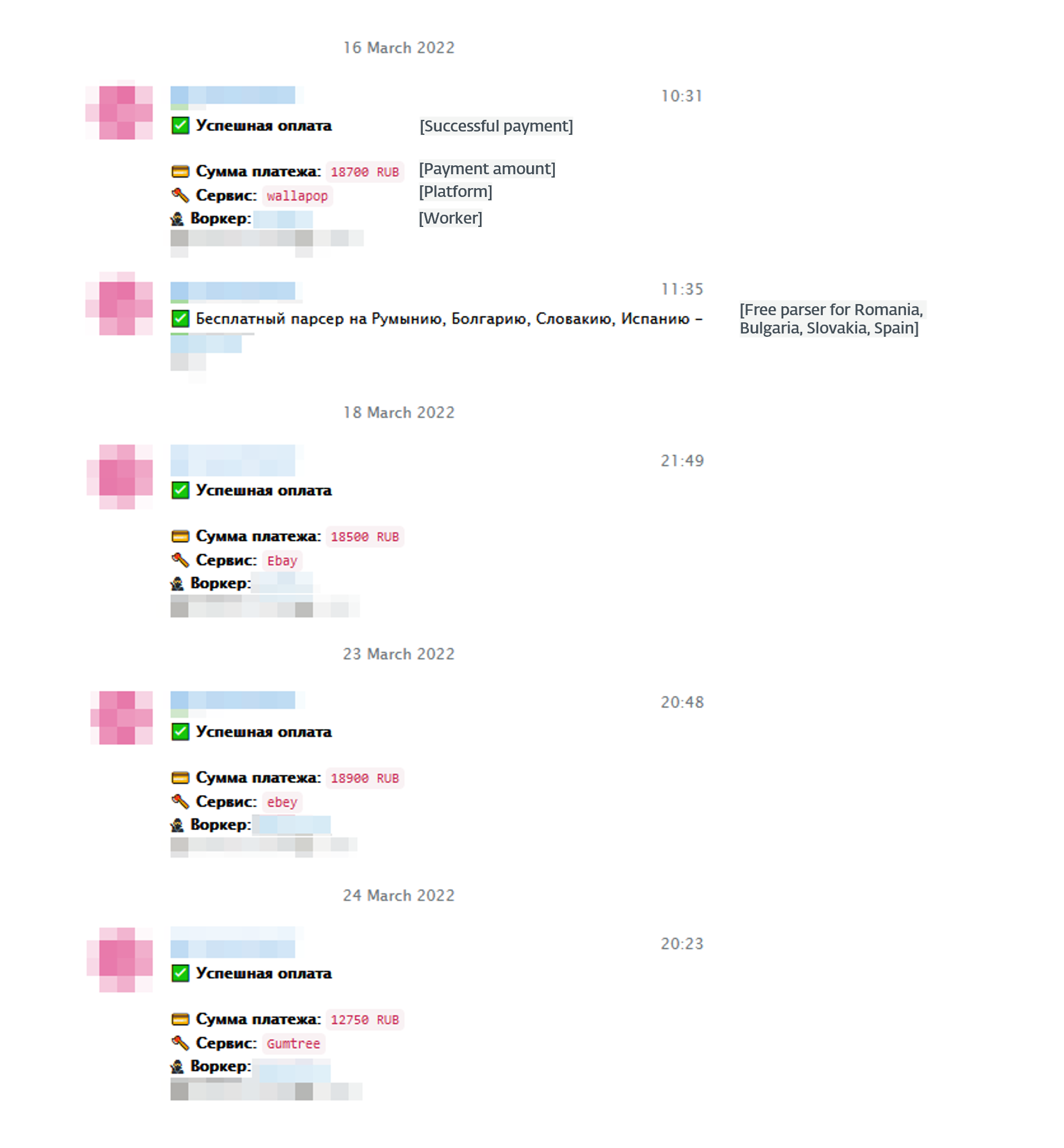
Determine 9. Instance of payout logs in a Telegram channel
The Telekopye administrator doesn’t switch the cash via Telekopye itself. As a substitute, the admin makes use of both a instrument referred to as “BTC Change bot”, seemingly an unbiased Telegram bot, or transfers the cash manually. Nonetheless, we now have noticed growing integration of payout-related options into Telekopye, so this may increasingly change sooner or later.
Sending phishing e-mail
Neanderthals can instruct Telekopye to create and ship e-mail messages. The sender is a predefined e-mail account shared between all of the Neanderthals. These e-mail accounts are usually related to the phishing domains arrange by Neanderthals. Determine 10 exhibits the code to spoof the e-mail headers From and Reply-To in order that the e-mail messages seem extra legit.
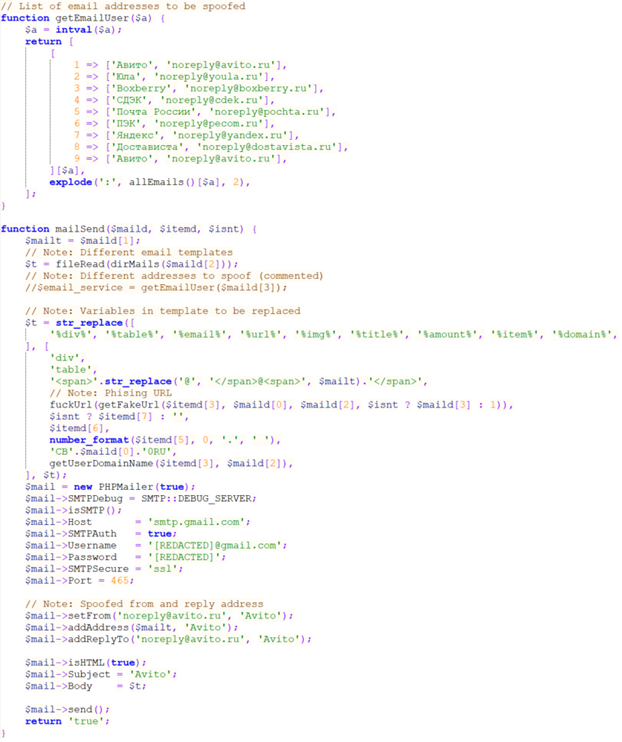
Determine 10. Code to craft phishing emails with a faux URL and spoofed sender handle
Determine 11 exhibits certainly one of many templates used to create phishing e-mail our bodies. No extra info has been given, so default values are proven, as a substitute of user-defined textual content, for %title% and %quantity%. A malicious URL is hidden behind the “Go to fee” button.
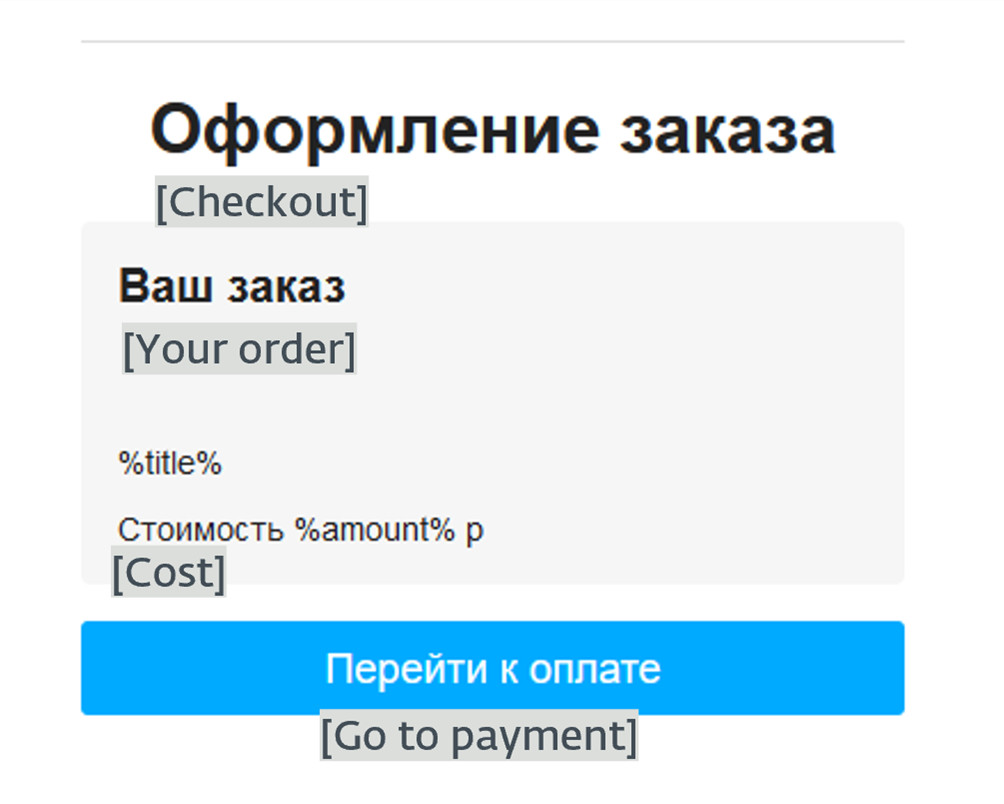
Determine 11. E-mail template that imitates a easy checkout e-mail
SMS help
Apart from phishing emails, Telekopye permits Neanderthals to create and ship SMS messages in an identical method. Determine 12 illustrates the piece of code accountable for creating and sending such messages.
Determine 12. A part of the code to create SMS messages utilizing the net service [legitimate] smscab.ru
Some implementations of Telekopye even have predefined SMS texts in several languages. All SMS templates say roughly the identical factor, for instance, “Your merchandise has been paid for. To obtain funds, fill out the shape: <malicious_link>”. Examples of a number of SMS templates are proven in Determine 13, the place unique Russian templates are proven.How this SMS appears to be like when a Mammoth receives it may be seen in Determine 14.
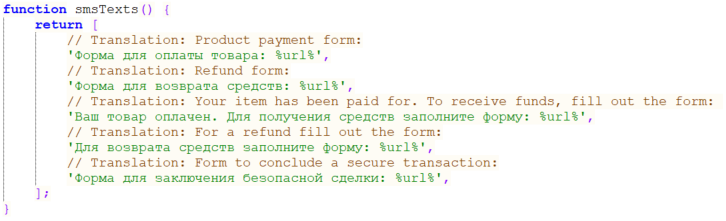
Determine 13. Telekopye SMS template texts in Russian
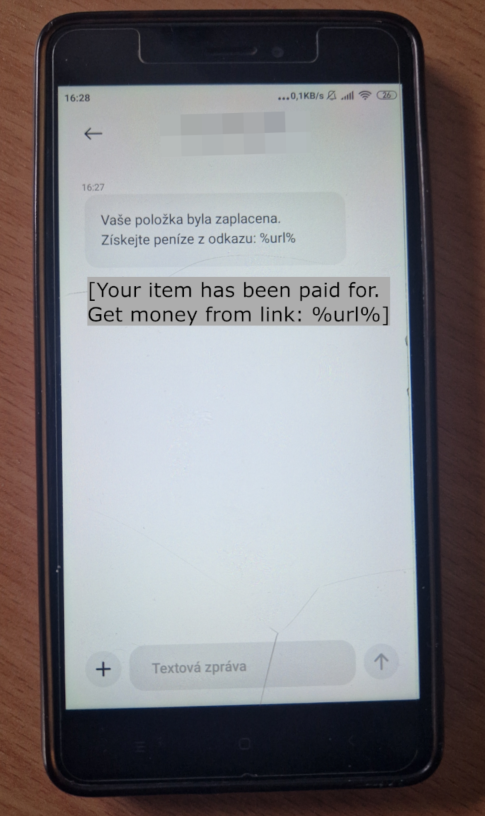
Determine 14. Instance of an SMS created with a template textual content in Czech and acquired with out a malicious hyperlink
Telekopye depends closely on on-line providers equivalent to smscab.ru or smshub.org to ship SMS messages. We now have analyzed an older variant, the place Telekopye used one hardcoded telephone quantity shared amongst all Neanderthals. Nonetheless, seemingly as a result of blocking one telephone quantity would end in blocking all Neanderthals’ messages, this function was discontinued.
Picture manipulation
On this part, we describe how easy it’s for Neanderthals utilizing Telekopye to create convincing pictures and screenshots. Some variations of Telekopye have a part referred to as Render bot. Though Render bot may very well be categorized as a standalone bot, we are going to deal with it as a part of Telekopye.
When Render bot is added to a Telegram chat, we’re greeted with the preliminary message seen in Determine 15.
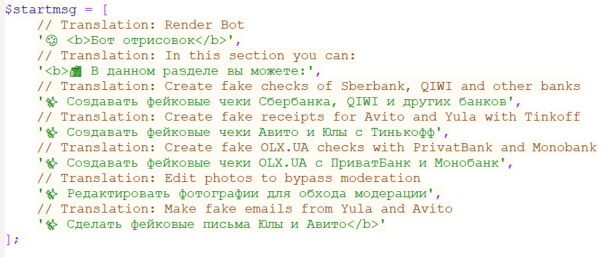
Determine 15. The preliminary message from Render bot
This offers us good perception into how this a part of Telekopye works. We will classify the makes use of of Render bot into two classes. First, it may be used to mangle pictures in order that they don’t seem to be straightforward to cross-reference. Second, it will possibly create faux pictures that are supposed to seem like legit screenshots. On this part, we are going to focus first on the creation of those faux screenshots, a function much like creating phishing web sites.
Not like faux internet pages which are generated from HTML templates, the bottom for faux screenshots is a JPG picture with some key components eliminated. These components embody the supposed paid value, debit/bank card quantity, title, title, and many others. This transformation is proven in Determine 16, the place there’s a side-by-side comparability of a plain template and a stuffed template. As a result of these are pictures, there aren’t any interactive buttons, not like the e-mail and phishing internet web page counterparts.
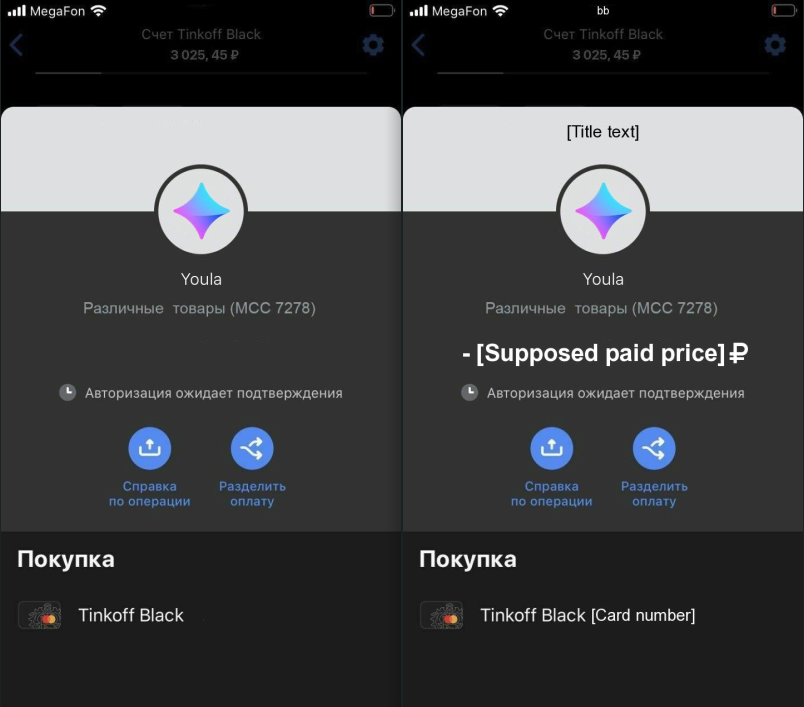
Determine 16. Generated faux screenshot (template on the left, template crammed with pattern textual content on the fitting)
There’s a excessive emphasis on making the inserted textual content match in addition to attainable, so Telekopye helps a number of totally different fonts. Simply as beforehand, all habits is hardcoded and no AI is used. We discovered 9 templates for Sberbank, Avito, Youla, Qiwi, and some different providers.
From the Neanderthals’ perspective, creating these screenshots isn’t any totally different from creating phishing internet pages. A Neanderthal solely wants to produce just a few bits of data, and Telekopye creates a faux screenshot/picture from them.
In Render bot folders additionally it is attainable to see certainly one of these templates within the strategy of creation. Determine 17 exhibits a photograph of an bill for a parcel, with numbered fields. Builders of Telekopye erase all fields with numbers subsequent to them and attempt to match their very own font fashion and font measurement in them. When they’re happy with how the ultimate product appears to be like, they add it to the bot for different Neanderthals to make use of as a brand new template.

Determine 17. Faux verify in progress of creation
One other no much less necessary performance of this a part of Telekopye is picture manipulation. From the code and its feedback, it’s attainable to assemble that it is ready to change pictures of marketed items in order that serps can not cross-reference them. We assume that if the picture was discovered on a web-based market, AI antispam safety would flag it as malicious. This transformation could be very easy and consists of a vertical flip of the picture and a small change in distinction.
Experimental options
Because of content material from Telekopye supply recordsdata, we assess that the builders try to experiment with differing types/variations of the rip-off. For instance, within the code, we see QR code era performance (Determine 18). This would possibly imply certainly one of two issues. Both it’s a part of the payout course of or they’re attempting to make it a brand new trick for scamming. A possible motive is that Mammoths don’t assume twice when paying through a QR code. So we estimate that there’s going to be a small improve in scams utilizing these sorts of methods.
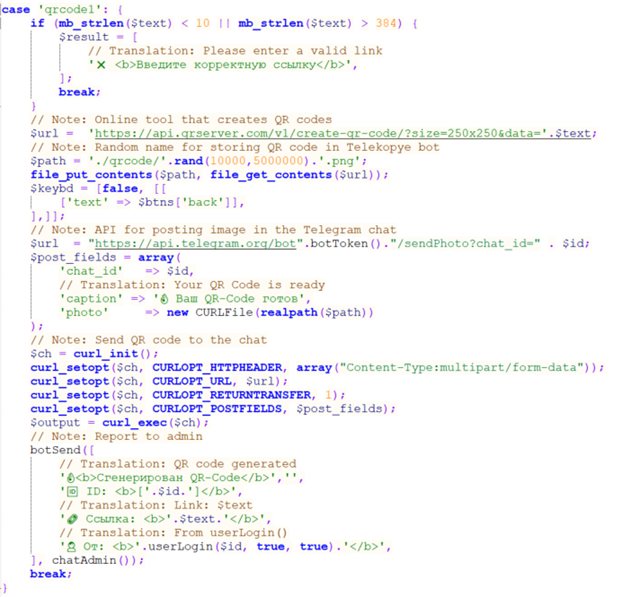
Determine 18. Code that generates QR codes
From Determine 15 it appears to be like as if Render bot can create faux checks for Sberbank. However in actuality, it will possibly solely create fee confirmations (Determine 19).

Determine 19. Cost affirmation template
Roles
Teams of scammers utilizing Telekopye are organized right into a hierarchy with least to most privileges so as as follows:
1. Directors
2. Moderators
3. Good employees / Assist bots
4. Employees
5. Blocked
We now have noticed some variants enriching this checklist with just a few additions, however these 5 roles stay the premise. We give attention to every position in additional element within the sections under.
Telekopye additionally employs a referral system. When a brand new Neanderthal desires to affix the group, he must fill in an software (how a lot “business” expertise he has, who invited him, and many others.). This software then must be accepted by Moderators or Directors to ensure that the brand new Neanderthal to affix.
Blocked
A consumer with this position will not be ready to make use of any a part of the Telekopye toolkit. Guidelines which are a part of Telekopye supply code recommend that is some kind of punishment for breaking them (Determine 20).
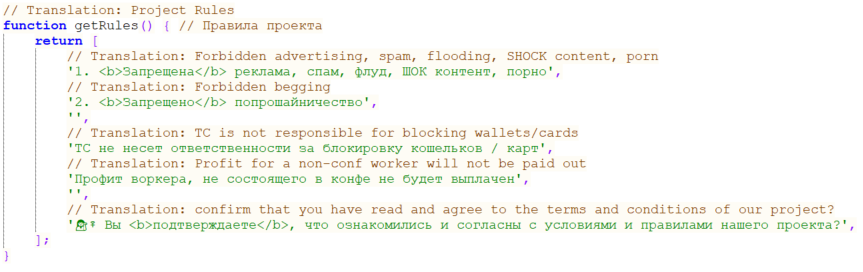
Determine 20. Guidelines of Telekopye chat group
Employees
That is the most typical position that the majority new Neanderthals begin with. With this position, Neanderthals are ready to make use of each Telekopye function, excluding moderation of the group. Throughout payout, this position has the worst fee charges, as seen in Desk 2.
Desk 2. Instance of payout charges
|
Position |
Fee to |
Fee to recommender |
Precise payout |
|
Employees |
33% |
2% |
65% |
|
Good employees/Assist bots |
23% |
2% |
75% |
Good employees/Assist bots
This position is a direct improve of the Employee position. The one distinction is that Neanderthals with this position don’t have to present such a big share of their payout to the platform proprietor.
To get this position, Neanderthals should show their usefulness – pull off quite a few scams or obtain a specific amount of stolen funds.
Generally it’s attainable to see that this position is reserved for help bots. We’re not sure what these bots are.
Moderators
Moderators can promote and demote different members and approve new members. They can not modify Telekopye settings.
Directors
Directors are the best position within the group. They’ll use Telekopye to its full extent. On prime of moderators’ capabilities, they’ll modify Telekopye settings – add phishing internet web page templates, change/add e-mail addresses that the bot makes use of, and alter payout charges, payout sort, and many others.
Find out how to keep away from being scammed
The best solution to inform whether or not you’re being focused by a Neanderthal attempting to steal your cash is by trying on the language used. It may be the language utilized in dialog, e-mail, or on the internet web page itself. Sadly, this isn’t foolproof, and it has been noticed that a few of these rip-off makes an attempt have ironed out grammar and vocabulary errors.
Insist on in-person cash and items alternate each time attainable when coping with secondhand items on on-line marketplaces. Such trades aren’t protected by well-known establishments or providers. These scams are solely attainable as a result of Neanderthals faux they already paid on-line/despatched an merchandise. Sadly, generally in-person supply will not be attainable and in that case you have to be further cautious.
Keep away from sending cash until you’re sure the place it is going to go. When you have to ship cash someplace, verify the net web page for grammatical errors and graphical disproportions. If you’re fortunate, a template can have some inaccuracies. Additionally verify the web site certificates and look intently on the URL, which will be made to seem like an actual hyperlink.
Be careful for strong-arm arguments like “I’ll ship cash via service XYZ. Are you aware the way it works?”. Ask if one other fee sort is feasible and particularly if they’re keen to simply accept fee from a service you’re acquainted with. This isn’t foolproof as a result of scammers have a number of templates, however you would possibly be capable to acknowledge a faux template extra simply while you use a fee methodology recognized to you.
Be further cautious when clicking on hyperlinks in SMS messages or emails, even when they give the impression of being as if they arrive from a good supply. Neanderthals aren’t any strangers to e-mail spoofing. A superb rule of thumb is to ask your self whether or not to procure one thing that will make respected sources ship you emails like that. If you’re uncertain, go to the supposed service’s web site immediately (not utilizing the hyperlink within the e-mail/SMS) and ask. Most of those pages have buyer help and they’re going to fortunately offer you a hand.
Conclusion
We found and analyzed Telekopye, a toolkit that helps much less technical individuals pull off on-line scams extra simply. We estimate that Telekopye was in use since no less than 2015. We targeted on one model, analyzing its most important capabilities and uncovering how Telekopye works internally. These capabilities embody creating phishing web sites, sending phishing SMS and emails, and creating faux screenshots. We additionally described the hierarchy of teams utilizing Telekopye. Because of our telemetry, we additionally came upon that this instrument continues to be in use and in lively improvement. The second Telekopye weblog put up, which shall be launched later, uncovers the interior working of the rip-off teams.
Acknowledgement
The creator wish to thank Ondřej Novotný for the preliminary discovery.
For any inquiries about our analysis revealed on WeLiveSecurity, please contact us at threatintel@eset.com.
ESET Analysis presents non-public APT intelligence studies and information feeds. For any inquiries about this service, go to the ESET Risk Intelligence web page.
IoCs
A complete checklist of Indicators of Compromise and samples can be found in our GitHub repository.
Information
|
SHA-1 |
Filename |
Detection |
Description |
|
26727D5FCEEF79DE2401CA0C9B2974CD99226DCB |
rip-off.php |
PHP/HackTool.Telekopye.A |
Telekopye rip-off toolkit |
|
285E0573EF667C6FB7AEB1608BA1AF9E2C86B452 |
tinkoff.php |
PHP/HackTool.Telekopye.A |
Telekopye rip-off toolkit |
|
8A3CA9EFA2631435016A4F38FF153E52C647146E |
600be5ab7f0513833336bec705ca9bcfd1150a2931e61a4752b8de4c0af7b03a.php |
PHP/HackTool.Telekopye.A |
Telekopye rip-off toolkit |
Community
|
IP |
Area |
Internet hosting supplier |
First seen |
Particulars |
|
N/A |
id23352352.ru |
Cloudflare |
2023-07-04 |
Area that’s used to check toolkit or rip-off sufferer. |
|
N/A |
id8092.ru |
Cloudflare |
2023-06-26 |
Area that’s used to check toolkit or rip-off sufferer. |
|
N/A |
id2770.ru |
Cloudflare |
2023-06-28 |
Area that’s used to check toolkit or rip-off sufferer. |
|
N/A |
id83792.ru |
Cloudflare |
2023-06-17 |
Area that’s used to check toolkit or rip-off sufferer. |
|
N/A |
id39103.ru |
Cloudflare |
2023-06-19 |
Area that’s used to check toolkit or rip-off sufferer. |
|
N/A |
2cdx.website |
Cloudflare |
2021-03-21 |
Area that’s used to check toolkit or rip-off sufferer. |
|
N/A |
3inf.website |
Cloudflare |
2021-03-12 |
Area that’s used to check toolkit or rip-off sufferer. |
|
N/A |
pay-sacure4ds.ru |
Jino |
2021-12-27 |
Area that’s used to check toolkit or rip-off sufferer. |
|
N/A |
id7423.ru |
Cloudflare |
2021-03-27 |
Area that’s used to check toolkit or rip-off sufferer. |
|
N/A |
id2918.website |
Jino |
2021-03-08 |
Area that’s used to check toolkit or rip-off sufferer. |
|
N/A |
formaa.ga |
Zomro |
2021-05-30 |
Area that’s used to check toolkit or rip-off sufferer. |
|
N/A |
id0391.ru |
Cloudflare |
2023-06-23 |
Area that’s used to check toolkit or rip-off sufferer. |
|
N/A |
id66410.ru |
Cloudflare |
2023-06-17 |
Area that’s used to check toolkit or rip-off sufferer. |
|
N/A |
id82567.ru |
Cloudflare |
2023-06-07 |
Area that’s used to check toolkit or rip-off sufferer. |
MITRE ATT&CK strategies
This desk was constructed utilizing model 13 of the MITRE ATT&CK framework.
|
Tactic |
ID |
Identify |
Description |
|
Reconnaissance |
Collect Sufferer Id Data |
Telekopye is used to assemble debit/bank card particulars, telephone numbers, emails, and many others. through phishing internet pages. |
|
|
Useful resource Growth |
Purchase Infrastructure: Domains |
Telekopye operators register their very own domains. |
|
|
Set up Accounts |
Telekopye operators set up accounts on on-line marketplaces. |
||
|
Set up Accounts: E-mail Accounts |
Telekopye operators arrange e-mail addresses related to the domains they register. |
||
|
Compromise Accounts: E-mail Accounts |
Telekopye operators use compromised e-mail accounts to extend their stealthiness. |
||
|
Develop Capabilities: Malware |
Telekopye is customized malware. |
||
|
Preliminary Entry |
Phishing: Spearphishing Hyperlink |
Telekopye sends hyperlinks to phishing web sites in emails or SMS messages. |
|
|
Assortment |
Enter Seize: Internet Portal Seize |
Internet pages created by Telekopye seize delicate info and report it to operators. |


