LUCR-3 overlaps with teams corresponding to Scattered Spider, Oktapus, UNC3944, and STORM-0875 and is a financially motivated attacker that leverages the Identification Supplier (IDP) as preliminary entry into an setting with the objective of stealing Mental Property (IP) for extortion. LUCR-3 targets Fortune 2000 firms throughout varied sectors, together with however not restricted to Software program, Retail, Hospitality, Manufacturing, and Telecoms.
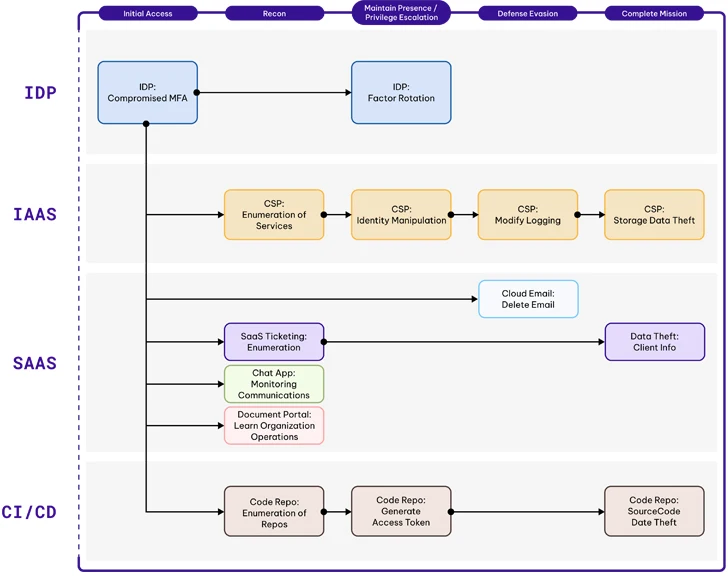
LUCR-3 doesn’t rely closely on malware and even scripts; as an alternative, LUCR-3 expertly makes use of victims’ personal instruments, purposes, and sources to realize their targets. At a excessive stage, Preliminary Entry is gained by means of compromising present identities within the IDP (Okta: Identification Cloud, Azure AD / Entra, Ping Identification: PingOne). LUCR-3 makes use of SaaS purposes corresponding to doc portals, ticketing programs, and chat purposes to learn the way the sufferer group operates and learn how to entry delicate data. Utilizing the information they gained from reconnaissance inside the SaaS purposes, they then perform their mission of information theft. Knowledge theft is often centered on IP, Code Signing Certificates, and buyer knowledge.
Attacker Attributes
Highlights
- LUCR-3 attribution is troublesome. Many people within the Cyber Intelligence neighborhood have even begun to trace the person personas individually. Additional complicated attribution, some LUCR-3 personas seem like associates of ALPHV with entry to deploy BlackCat ransomware.
- Very similar to LUCR-1 (GUI-Vil), LUCR-3 tooling, particularly in Cloud, SaaS, and CI/CD, largely makes use of net browsers and a few GUI utilities corresponding to S3 Browser. Leveraging the native options of purposes, identical to any worker would do, to hold out their objective.
- LUCR-3 closely targets the IDPs for Preliminary Entry. Shopping for creds from frequent marketplaces and bypassing MFA through SIM swapping, social engineering, and push fatigue.
- LUCR-3 does its homework on its preliminary entry victims, selecting identities that may have elevated privileges and even guaranteeing they supply from related geolocation as their sufferer identities to keep away from not possible journey (geo disparity) alerts.
- LUCR-3 will make the most of the sufferer organizations software program deployment options, corresponding to SCCM, to deploy specified software program to focus on programs.
Mission
LUCR-3 is a financially motivated menace actor that makes use of knowledge theft of delicate knowledge (IP, Buyer knowledge, Code Signing Certificates) to try extortion. Whereas extortion calls for do fluctuate, they’re usually within the tens of thousands and thousands of {dollars}. Some personas inside LUCR-3 will usually collaborate with ALPHV to hold out the extortion part of the assault.
Tooling
LUCR-3 makes use of largely Home windows 10 programs working GUI utilities to hold out their mission within the cloud. Utilizing the native options of SaaS purposes corresponding to search, LUCR-3 is ready to navigate by means of a company with out elevating any alarms. In AWS, the menace actor routinely leverages the S3 Browser (model 10.9.9) and the AWS administration console (through an online browser). LUCR-3 makes use of AWS Cloudshell inside the AWS administration console to hold out any exercise that requires direct interplay with the AWS API.
Victimology
LUCR-3 usually targets massive (Fortune 2000) organizations which have Mental Property (IP) that’s precious sufficient that sufferer organizations are prone to pay an extortion charge. Software program firms are a typical goal as they intention to extort a charge associated to the theft of supply code in addition to code signing certificates. LUCR-3 will usually goal organizations that may be leveraged in a provide chain assault towards others. Identification Suppliers and their outsourced companies firms are often focused as a singular compromise of certainly one of these entities will permit for entry into a number of different organizations. In current months, LUCR-3 has expanded its focusing on into sectors they have not beforehand centered as a lot on, corresponding to hospitality, gaming, and retail.
LUCR-3 (SCATTERED SPIDER) THREAT BRIEFING
Learn the way LUCR-3 (aka Scattered Spider) is compromising IDPs and increasing assaults towards laaS, SaaS and CI/CD pipelines.
Attacker Lifecycle
 |
| AWS Attacker Lifecycle |
Preliminary Recon
LUCR-3 does their homework when deciding on their goal sufferer identities. They guarantee they’re focusing on customers that may have the entry they should perform their mission. This contains however isn’t restricted to Identification Admins, Builders, Engineers, and the Safety workforce.
They’ve been identified to leverage credentials that have been obtainable in frequent deep net marketplaces.
Preliminary Entry (IA)
LUCR-3’s preliminary entry into an setting is gained by means of compromised credentials. They don’t seem to be performing noisy actions like password spraying to search out passwords. Once they join, they have already got a official password to make use of. The everyday strategy for them is:
1. Establish credentials for the supposed sufferer identification
- Purchase credentials from frequent deepweb marketplaces
- Smishing victims to gather their credentials
- Social engineering assist desk personnel to achieve entry to the credentials
2. Bypass Multi-factor Authentication (MFA)
- SIM Swapping (when SMS OTP is enabled)
- Push Fatigue (when SMS OTP isn’t enabled)
- Phishing assaults with redirects to official websites the place OTP codes are captured and replayed
- Purchase or social engineer entry from an insider (final resort)
3. Modify MFA settings
- Register a brand new machine
- Add various MFA choices
When LUCR-3 modifies MFA settings, they usually register their very own cellular machine and add secondary MFA choices corresponding to emails. Indicators to observe for listed below are:
- When a person registers a tool that’s in a distinct ecosystem than their earlier machine (Android to Apple for example)
- When a person registers a brand new machine that’s an older mannequin than their earlier machine
- When a single telephone (machine ID) is assigned to a number of identities
- When an exterior e mail is added as a multi-factor possibility
Recon (R)
R-SaaS
With a purpose to perform their objective of information theft, ransom, and extortion, LUCR-3 should perceive the place the essential knowledge is and learn how to get to it. They carry out these duties very like any worker would. Looking out by means of and viewing paperwork in varied SaaS purposes like SharePoint, OneDrive, data purposes, ticketing options, and chat purposes permits LUCR-3 to find out about an setting utilizing native purposes with out setting off alarm bells. LUCR-3 makes use of search phrases focused at discovering credentials, studying in regards to the software program deployment environments, code signing course of, and delicate knowledge.
R-AWS
In AWS, LUCR-3 performs recon in a number of methods. They may merely navigate across the AWS Administration Console into companies like Billing, to grasp what varieties of companies are being leveraged, after which navigate every of these companies within the console. Moreover, LUCR-3 needs to know what packages are working on the compute programs (EC2 cases) in a company. Leveraging Techniques Supervisor (SSM), LUCR-3 will run the native AWS-GatherSoftwareInventory job towards all EC2 cases, returning the software program working on the EC2 cases. Lastly, LUCR-3 will leverage the GUI utility S3 Browser together with a long-lived entry key to view obtainable S3 buckets.
Privilege Escalation (PE)
LUCR-3 usually chooses preliminary victims who’ve the kind of entry vital to hold out their mission. They don’t at all times must make the most of privilege escalation strategies, however we’ve got noticed them achieve this once in a while in AWS environments.
PE-AWS
LUCR-3 has utilized three (3) essential strategies for privilege escalation in AWS:
- Coverage manipulation: LUCR-3 has been seen modifying the coverage of present roles assigned to EC2 cases ( ReplaceIamInstanceProfileAssociation ) in addition to creating new ones with a full open coverage.
- UpdateLoginProfile: LUCR-3 will replace the login profile and, once in a while, create one if it does not exist to assign a password to an identification to allow them to leverage it for AWS Administration Console logons.
- SecretsManager Harvesting: Many organizations retailer credentials in SecretsManger or Terraform Vault for programmatic entry from their cloud infrastructure. LUCR-3 will leverage AWS CloudShell to scrape all credentials which might be obtainable in SecretsManager and related options.
Set up Persistence/ Keep Presence (EP)
LUCR-3, like most attackers, needs to make sure that they’ve a number of methods to enter an setting within the occasion that their preliminary compromised identities are found. In a contemporary cloud world, there are various methods to realize this objective, and LUCR-3 employs a myriad to take care of its presence.
EP-AzureAD/Okta
After having access to an identification within the IDP (AzureAD, Okta, and so forth.), LUCR-3 needs to make sure they’ll simply proceed to entry the identification. So as to take action, they are going to usually carry out the next actions:
- Reset/Register Issue: LUCR-3 will register their very own machine to ease their potential for continued entry. As talked about beforehand, look ahead to ecosystem switches for customers in addition to single gadgets which might be registered to a number of customers.
- Alternate MFA: Many IDPs permit for alternate MFA choices. LUCR-3 will make the most of these options to register exterior emails as an element. They’re sensible about selecting a reputation that aligns with the sufferer’s identification.
- Robust Authentication Kind: In environments the place the default setting is to not permit for SMS as an element, LUCR-3 will modify this setting if they’re able to. In AzureAD, you’ll be able to monitor for this by searching for the StrongAuthenticationMethod altering from a 6 (PhoneAppOTP) to a 7 (OneWaySMS)
EP-AWS
To take care of persistence in AWS, LUCR-3 has been noticed performing the next:
- CreateUser: LUCR-3 will try to create IAM Customers when obtainable. They select names that align with the sufferer identification they’re utilizing for preliminary entry into the setting.
- CreateAccessKey: LUCR-3 will try to create entry keys for newly created IAM Customers in addition to present IAM Customers that they’ll then use programmatically. Like GUI-Vil (LUCR-1), the entry keys which might be created are sometimes inputted into the S3 Browser to work together with S3 buckets.
- CreateLoginProfile / UpdateLoginProfile: LUCR-3, when attempting to be extra stealthy or when they don’t have entry to create new IAM customers, will try to create or replace login profiles for present customers. Login profiles are what assign a password to an IAM Person and permit for console entry. This method additionally lets the attacker achieve the privileges of the sufferer’s identification.
- Credential Harvesting: As talked about beforehand, LUCR-3 finds nice worth in harvesting credentials from credential vaults corresponding to AWS SecretsManager and Terraform Vault. These usually retailer credentials not only for the sufferer organizations but in addition credentials that will permit entry to enterprise companions, expertise integrations, and even shoppers of the sufferer group.
- Useful resource Creation: Lastly, LUCR-3 will create or take over present sources, corresponding to EC2 cases that may be leveraged for entry again into the setting in addition to a staging space for instruments and knowledge theft as wanted.
EP-SaaS
LUCR-3 will use all of the purposes obtainable to them to additional their objective. In ticketing programs, chat packages, doc shops, and data purposes, they are going to usually carry out searches searching for credentials that may be leveraged throughout their assault.
Moreover, many of those purposes permit the creation of entry tokens that can be utilized to work together with the SaaS purposes API.
EP-CI/CD
LUCR-3 will even generate entry tokens for interacting with the APIs of your code repositories, corresponding to GitHub and GitLab.
Protection Evasion (DE)
Now we have noticed that LUCR-3 considerably focuses on protection evasion ways in varied environments. That is clearly to keep away from detection so long as doable till they’re positive they’ve achieved their mission goals and are able to carry out ransom and extortion actions. They accomplish this by means of a number of means relying on the kind of setting they’re in.
DE-AWS
LUCR-3 employs largely frequent protection evasion strategies in AWS, with a few distinctive flares.
- Disable GuardDuty: LUCR-3 will carry out the everyday deletion of GuardDuty detectors but in addition tries to make it tougher so as to add again to the org stage by deleting invites. That is completed by means of the next three instructions: DisassociateFromMasterAccount, DeleteInvitations, DeleteDetector
- Cease Logging: LUCR-3 additionally makes an attempt to evade AWS detections by performing DeleteTrail and StopLogging actions.
- Serial Console Entry: This can be giving LUCR-3 an excessive amount of credit score, however we’ve got noticed them EnableSerialConsoleAccess for AWS accounts they’ve compromised after which try to make use of EC2 Occasion Hook up with SendSerialConsoleSSHPublicKey which is able to try to determine a serial connection to a specified EC2 occasion. This may be leveraged to keep away from community monitoring, as serial connections are hardware-based.
DE-AzureAD/Okta
LUCR-3 clearly understands that one of many extra frequent detections in place for IDPs is to observe and alert on not possible journey. To keep away from these not possible journey detections, LUCR-3 will be certain that they supply from an analogous geolocation as their sufferer identification. This appears to be largely completed through the usage of residential VPNs.
DE-M365/Google Workspace
A few of LUCR-3’s actions in an setting, corresponding to producing tokens and opening up assist desk tickets, trigger emails to be despatched to the victims’ mailboxes. LUCR-3, already sitting in these mailboxes, will delete the emails to keep away from detection. Whereas e mail deletion by itself is a really weak sign, searching for e mail deletions through the online model of Outlook with delicate phrases like OAuth, entry token, and MFA may deliver to gentle greater constancy indicators to comply with.
Full Mission (CM)
LUCR-3 has one objective: monetary achieve. They do that largely by means of extortion of delicate knowledge that they’ve collected through the native instruments of the sufferer organizations’ SaaS and CI/CD purposes. In AWS, that is completed by knowledge theft in S3 and in database purposes corresponding to Dynamo and RDS.
Whereas within the SaaS world, they full their mission by looking out and downloading paperwork and net pages through a standard net browser.
On the CI/CD aspect, LUCR-3 will use the clone, archive, and think about uncooked options of Github and Gitlab to view and obtain supply knowledge.
Indicators
Detections
Permiso shoppers are protected by the next detections: