Safety is important when transmitting info over any untrusted medium, notably with the web. Cryptography is usually used to guard info over a public channel between two entities. Nevertheless, there’s an imminent menace to present cryptography with the arrival of quantum computer systems. In line with the Nationwide Institute of Requirements and Expertise (NIST), “When quantum computer systems are a actuality, our present public key cryptography received’t work anymore… So, we have to begin designing now what these replacements can be.”
Quantum computing menace
A quantum pc works with qubits, which might exist in a number of states concurrently, based mostly on the quantum mechanical precept of superposition. Thus, a quantum pc may discover many potential permutations and combos for a computational activity, concurrently and swiftly, transcending the boundaries of classical computing.
Whereas a sufficiently giant and commercially possible quantum pc has but to be constructed, there have been large investments in quantum computing from many companies, governments, and universities. Quantum computer systems will empower compelling improvements in areas reminiscent of AI/ML and monetary and local weather modeling. Quantum computer systems, nevertheless, may even give dangerous actors the power to interrupt present cryptography.
Public-key cryptography is ubiquitous in trendy info safety purposes reminiscent of IPsec, MACsec, and digital signatures. The present public-key cryptography algorithms are based mostly on mathematical issues, such because the factorization of huge numbers, that are daunting for classical computer systems to resolve. Shor’s algorithm offers a means for quantum computer systems to resolve these mathematical issues a lot quicker than classical computer systems. As soon as a sufficiently giant quantum pc is constructed, present public-key cryptography (reminiscent of RSA, Diffie-Hellman, ECC, and others) will now not be safe, which is able to render most present makes use of of cryptography weak to assaults.
Retailer now, break later
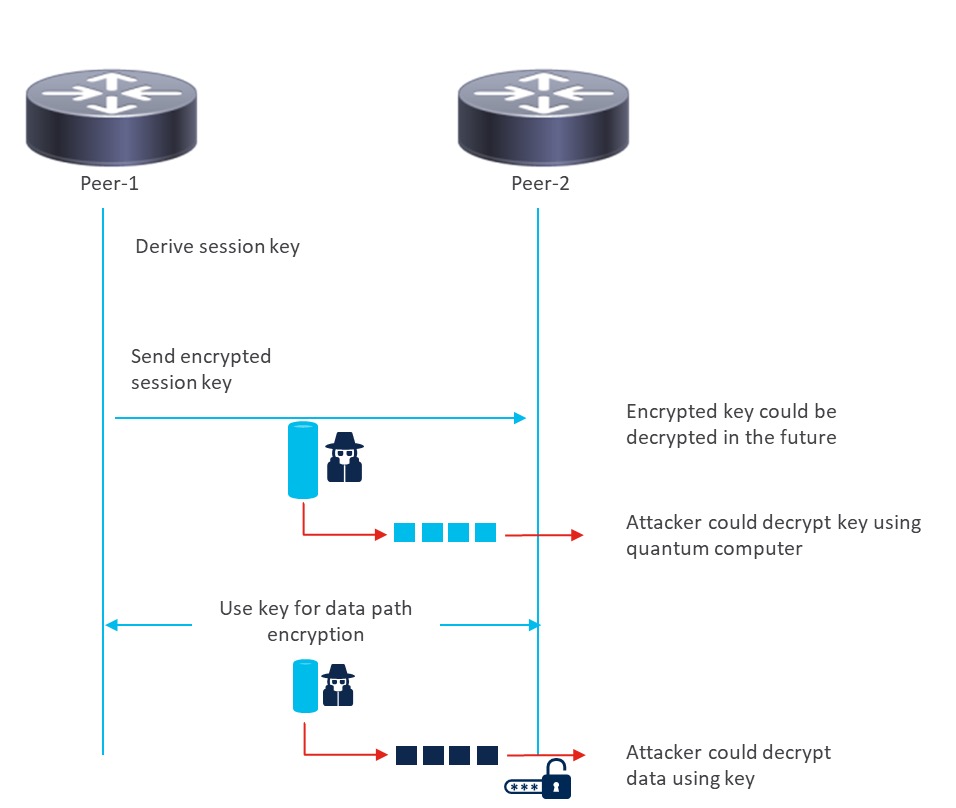
Why fear now? Many of the transport safety protocols like IPsec and MACsec use public-key cryptography through the authentication/key institution section to derive the session key. This shared session key’s then used for symmetric encryption and decryption of the particular visitors.
Unhealthy actors can use the “harvest now, decrypt later” strategy to seize encrypted knowledge proper now and decrypt it later, when a succesful quantum pc materializes. It’s an unacceptable threat to depart delicate encrypted knowledge prone to impending quantum threats. Specifically, if there’s a want to take care of ahead secrecy of the communication past a decade, we should act now to make these transport safety protocols quantum-safe.
The long-term answer is to undertake post-quantum cryptography (PQC) algorithms to exchange the present algorithms which are prone to quantum computer systems. NIST has recognized some candidate algorithms for standardization. As soon as the algorithms are finalized, they should be applied by the distributors to begin the migration. Whereas actively working to offer PQC-based options, Cisco already has quantum-safe cryptography options that may be deployed now to safeguard the transport safety protocols.
Cisco’s answer
Cisco has launched the Cisco session key import protocol (SKIP), which allows a Cisco router to securely import a post-quantum pre-shared key (PPK) from an exterior key supply reminiscent of a quantum key distribution (QKD) system or different supply of key materials.
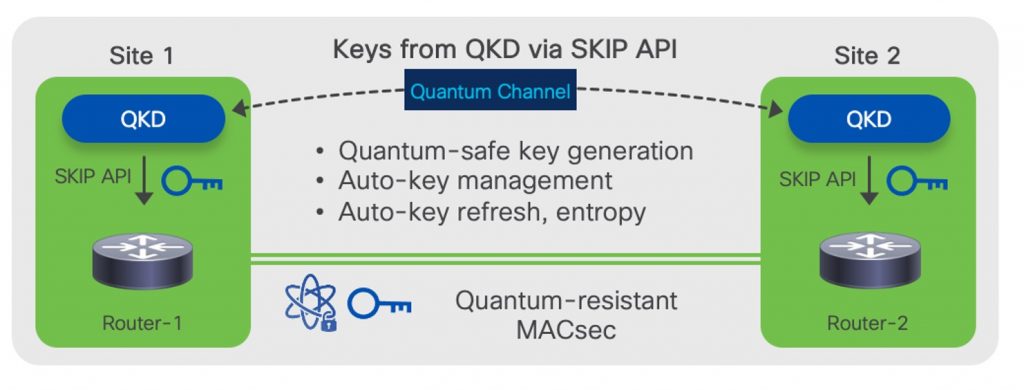
For deployments that may use an exterior hardware-based key supply, SKIP can be utilized to derive the session keys on each the routers establishing the MACsec connection (see Determine 1).
With this answer, Cisco provides many advantages to clients, together with:
- Safe, light-weight protocol that’s a part of the community working system (NOS) and doesn’t require clients to run any further purposes
- Help for “deliver your individual key” (BYOK) mannequin, enabling clients to combine their key sources with Cisco routers
- The channel between the router and key supply utilized by SKIP can also be quantum-safe, because it makes use of TLS 1.2 with DHE-PSK cipher suite
- Validated with a number of key-provider companions and finish clients
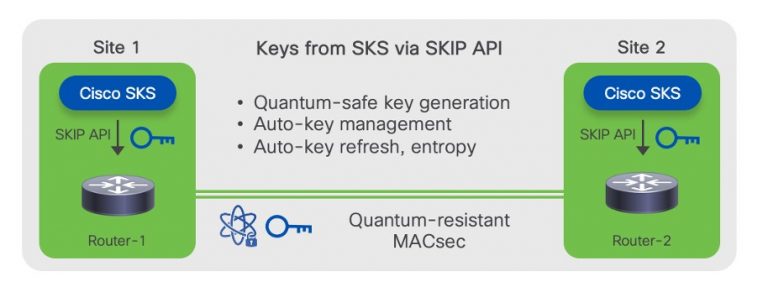
Along with SKIP, Cisco has launched the session key system (SKS), which is a singular answer that allows routers to derive session keys with out having to make use of an exterior key supply.
The SKS engine is a part of the Cisco IOS XR working system (see Determine 2). Routers establishing a safe connection like MACsec will derive the session keys straight from their respective SKS engines. The engines are seeded with a one-time, out-of-band operation to verify they derive the identical session keys.
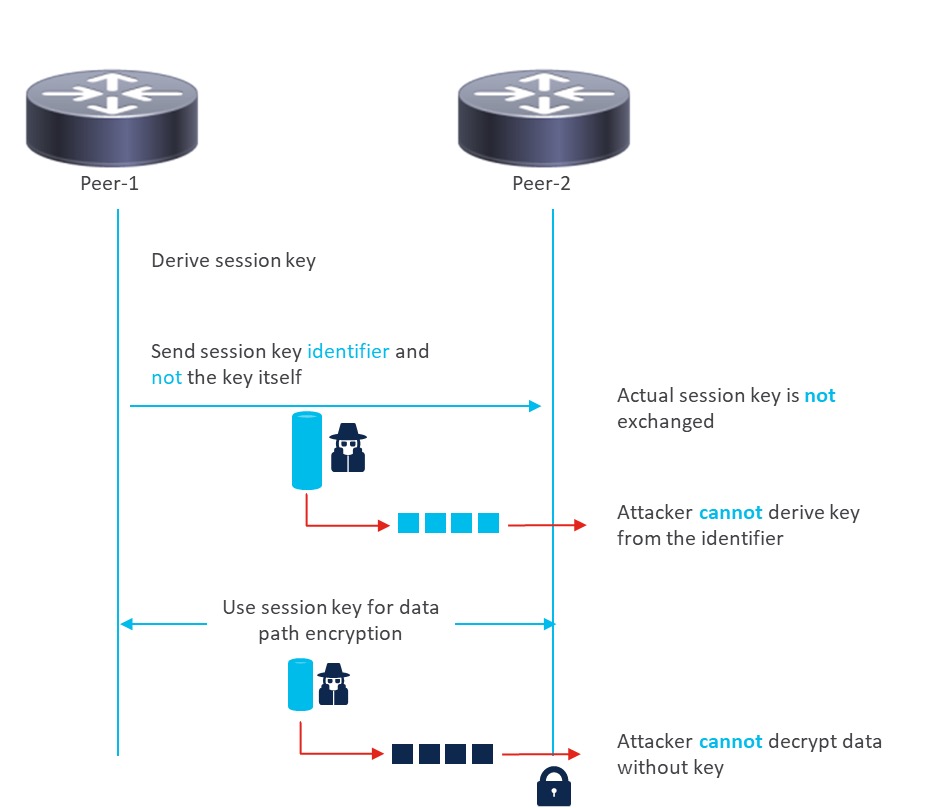
In contrast to the standard technique (see Determine 3), the place the session keys are exchanged on the wire, solely the important thing identifiers are despatched on the wire with quantum key distribution. So, any attacker tapping the hyperlinks won’t be able to derive the session keys, as having simply the important thing identifier isn’t enough (see Determine 4).
Cisco is main the best way with complete and modern quantum-safe cryptography options which are able to deploy at this time.
Watch this Cisco Data Networking (CKN) webinar
and uncover how Cisco will help shield your community.
Share:


