Menace actors related to the Roaming Mantis assault marketing campaign have been noticed delivering an up to date variant of their patent cellular malware often called Wroba to infiltrate Wi-Fi routers and undertake Area Title System (DNS) hijacking.
Kaspersky, which carried out an evaluation of the malicious artifact, mentioned the characteristic is designed to focus on particular Wi-Fi routers positioned in South Korea.
Roaming Mantis, also referred to as Shaoye, is a long-running financially motivated operation that singles out Android smartphone customers with malware able to stealing checking account credentials in addition to harvesting other forms of delicate data.
Though primarily concentrating on the Asian area since 2018, the hacking crew was detected increasing its sufferer vary to incorporate France and Germany for the primary time in early 2022 by camouflaging the malware because the Google Chrome internet browser utility.
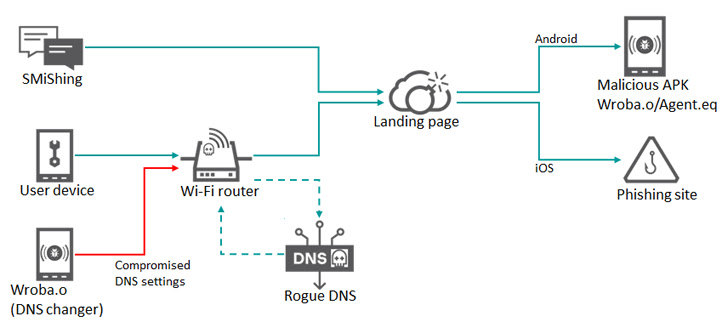
The assaults leverage smishing messages because the preliminary intrusion vector of option to ship a booby-trapped URL that both gives a malicious APK or redirects the sufferer to phishing pages based mostly on the working system put in within the cellular gadgets.
Alternatively, some compromises have additionally leveraged Wi-Fi routers as a way to take unsuspecting customers to a faux touchdown web page through the use of a method referred to as DNS hijacking, wherein DNS queries are manipulated to be able to redirect targets to bogus websites.
Whatever the methodology used, the intrusions pave the way in which for the deployment of a malware dubbed Wroba (aka MoqHao and XLoader) that is geared up to hold out a slew of nefarious actions.
The newest replace to Wroba, per the Russian cybersecurity firm, includes a DNS changer operate that is engineered to detect sure routers based mostly on their mannequin numbers and poison their DNS settings.
“The brand new DNS changer performance can handle all machine communications utilizing the compromised Wi-Fi router, resembling redirecting to malicious hosts and disabling updates of safety merchandise,” Kaspersky researcher Suguru Ishimaru mentioned.
The underlying thought is to trigger gadgets related to the breached Wi-Fi router to be redirected to internet pages managed by the menace actor for additional exploitation. On condition that a few of these pages ship the Wroba malware, the assault chain successfully creates a gradual stream of “bots” that may be weaponized to interrupt into wholesome Wi-Fi routers.
It is notable that the DNS changer program is solely utilized in South Korea. Nevertheless, the Wroba malware in itself has been noticed concentrating on victims in Austria, France, Germany, India, Japan, Malaysia, Taiwan, Turkey, and the U.S. through smishing.
Wroba is way from the one cellular malware within the wild with DNS hijacking options. In 2016, Kaspersky unmasked one other Android trojan codenamed Switcher that assaults the wi-fi router whose community the contaminated machine is related to and performs a brute-force assault with the purpose of tampering with the DNS configurations.
“Customers with contaminated Android gadgets that hook up with free or public Wi-Fi networks could unfold the malware to different gadgets on the community if the Wi-Fi community they’re related to is weak,” the researcher mentioned.