
Pretend extortionists are piggybacking on knowledge breaches and ransomware incidents, threatening U.S. corporations with publishing or promoting allegedly stolen knowledge until they receives a commission.
Typically the actors add the menace of a distributed denial-of-service (DDoS) assault if the message recipient doesn’t adjust to the directions within the message.
Dangerous actors
The attackers behind this exercise use the identify Midnight and began concentrating on corporations within the U.S. since not less than March 16.
They’ve additionally impersonated some ransomware and knowledge extortion gangs in emails and claimed to be the authors of the intrusion, stealing lots of of gigabytes of vital knowledge.
In a single e mail to the worker of a holding firm within the trade of petroleum components, the menace actor claimed to be the Silent Ransom Group (SRG) – a splinter of the Conti syndicate targeted on stealing knowledge and extorting the sufferer, often known as Luna Moth.
The identical message, nonetheless, used within the topic line the identify of one other menace actor, the Surtr ransomware group, first seen to encrypt firm networks in December 2021.

supply: BleepingComputer
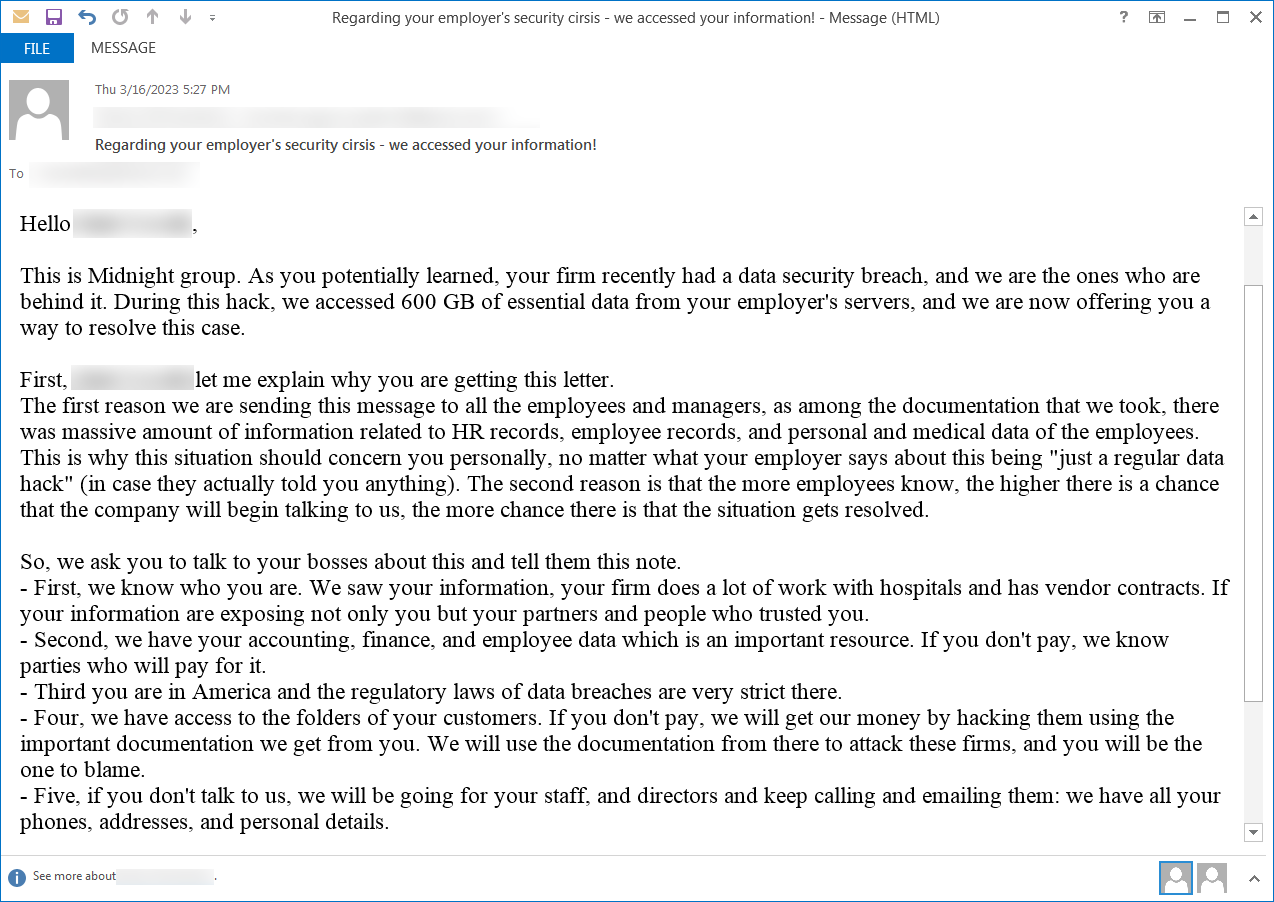
BleepingComputer discovered one other e mail from Midnight Group, professing that they have been the authors of the information breach and that they stole 600GB of “important knowledge” from the servers.
The messages have been despatched to the handle of a senior monetary planner that had left the goal firm greater than half a yr earlier than.
supply: BleepingComputer
Pending DDoS menace
A report in late March from the managed detection and response division on the Kroll company investigation and threat consulting agency notes that some senders of comparable emails additionally threatened with DDoS assaults.
Kroll investigators say that beginning March 23 organizations began submitting an elevated variety of studies for emails obtained below the Silent Ransom Group identify.
It’s “a brand new wave of faux extorsion makes an attempt,” Kroll responders say within the report, including that the authors use the names of better-known cybercriminals in an try to intimidate and provides legitimacy to the menace.
“This methodology is affordable and simply carried out by low-skilled attackers. Very like 419 wirefraud scams, the rip-off depends on social engineering to extort victims by inserting strain on the sufferer to pay earlier than a deadline. We count on this pattern to proceed indefinitely as a consequence of its value effectiveness and skill to proceed to generate income for cybercriminals” – Kroll
Kroll has seen such incidents since 2021, though such exercise began in early November 2019, when non-paying victims additionally skilled DDoS assaults.
However, the assaults have been low-level DDoS and got here with the specter of bigger ones until the extortionists acquired paid.
Such incidents echo the exercise of an extortion group that in 2017 despatched DDoS threats to 1000’s of corporations below the names of notorious hacker teams on the time (e.g. New World Hackers, Lizard Squad, LulzSec, Fancy Bear, and Nameless).
Focusing on ransomware assault victims
One other report from incident response firm Arete confirms Kroll’s observations about Midnight Group’s fraudulent emails impersonating Surtr and SRG and the bigger variety of messages delivered within the weeks earlier than March 24.
Based mostly on their visibility, although, the incident responders noticed that Midnight focused organizations that had beforehand been victims of a ransomware assault.
Based on Arete’s analysts, among the many preliminary attackers are QuantumLocker (presently rebranded as DagonLocker), Black Basta, and Luna Moth.
Arete says that not less than 15 of their present and former shoppers obtained pretend threats from the Midnight Group, which supported their knowledge theft claims with obscure particulars.
It’s unclear how victims are chosen however one risk is from publicly out there sources, such because the preliminary attacker’s knowledge leak website, social media, information studies, or firm disclosures.
Nonetheless, Arete notes that the pretend attacker recognized some ransomware victims even when the data was not publicly out there, presumably indicating collaboration with the preliminary intruders.
Ransomware actors usually promote the information they steal from victims even once they receives a commission. If Midnight Group has entry to the markets and boards the place this knowledge is traded or bought they might find out about ransomware victims which have but to reveal the cyberattack.
Empty threats since 2019
Midnight Group’s extortion rip-off isn’t new. The tactic has been noticed in 2019 by ransomware incident response firm Coveware who calls it Phantom Incident Extortion.
Coveware explains that the menace actor tries to provide credibility to the menace through the use of knowledge that’s distinctive to the recipient goal, provides the strain of a expensive end result, and calls for fee that’s far lower than the injury of public publicity.
All these three parts are the mainstays of a phantom incident extortion (PIE) and a transparent indication of an empty menace.
Coveware initially offered 4 examples of PIE scams and up to date the report solely just lately with a pattern e mail from the Midnight Group.
All three corporations assess that Midnight Group’s threats are a part of a fraud marketing campaign. Arete’s try to have interaction with the actor resulted in no response or proof of stolen knowledge from the actor.
The advice is to fastidiously analyze such emails to acknowledge the parts of a phantom incident extortion message and dismiss them as an empty menace.

