Over the previous decade, the cyber risk panorama has undergone a major transformation, escalating from remoted assaults by lone wolves to classy, coordinated breaches by state-sponsored entities and arranged crime teams. Throughout this era of change, cybersecurity has usually been a secondary thought for enterprises, steadily addressed via reactive measures inadequate to counteract such superior threats. Nevertheless, we’re witnessing a pivotal shift, predominantly pushed by regulatory our bodies, towards establishing harmonized pointers that may maintain tempo with the dynamic nature of cyber threats.
The Digital Operational Resilience Act (DORA) represents one such proactive stride on this path. Focused on the European Union (EU) monetary sector and constructed round 5 core pillars, DORA advocates for a risk-based framework that enhances the sector’s capabilities to stop, reply to, and get well from cyber incidents.

How will you leverage Safe Workload to organize for DORA?
Whereas DORA doesn’t dictate exact technical necessities, it gives the groundwork for a risk-based shift in cybersecurity. Safe Workload serves as a pivotal device on this transition, enabling organizations to grasp danger, stop and mitigate danger, and report dangers related to their software workloads.
1. Understanding Threat
To grasp danger, you have to have visibility to know what is going on in your atmosphere. Safe Workload delivers in-depth insights into how your workloads talk and behave, together with figuring out any weak packages put in. You may rapidly reply questions resembling:
- “Are my workloads using authorized enterprise companies for frequent companies resembling DNS or NTP?”
- “Am I weak to a particular vulnerability?
- “What’s the danger of that vulnerability” Is it simply exploitable?
- “Are my workloads utilizing insecure or out of date transport session protocols and ciphers?”
- “Are my monetary software workloads speaking to non-production environments?
- “How is my monetary software speaking to exterior dependencies?”
- “Is it speaking to malicious networks?”


2. Stopping and Mitigating Threat
As soon as the chance is known, it’s time to act. This motion can take the type of proactive controls and compensating controls.
- Proactive Controls: Safe Workload microsegmentation insurance policies permit you to create fine-grained allow-list insurance policies for purposes by discovering their dependencies. Moreover, guardrail insurance policies may be established to limit communications from risk-prone environments to your manufacturing workloads, resembling non-production can’t discuss to manufacturing workloads, or the PCI Cardholder Setting can’t discuss to PCI Out-of-Scope or maybe OT community can’t talk with the info heart, permitting to include lateral motion and cut back the blast radius.

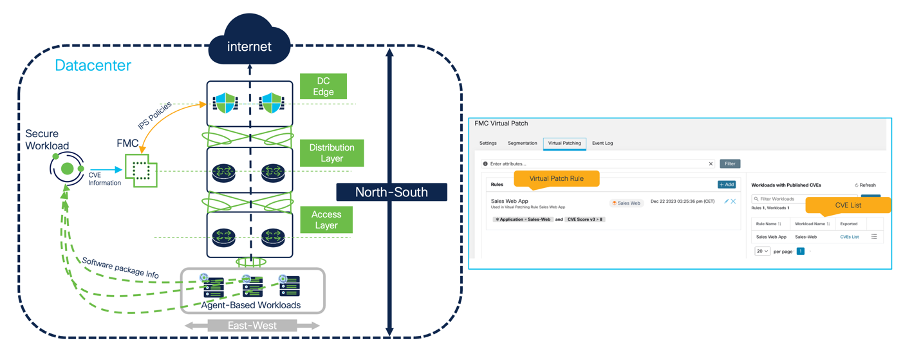
- Compensating Controls: Even within the worst-case state of affairs, the place a brand new zero-day vulnerability is disclosed or ransomware hits the group, Safe Workload can quickly act on this and limit For instance, you may quarantine a workload communication based mostly on a number of attributes, resembling CVE data, CVE Rating, and even the entry vectors entry vectotr assestment.You can too select to leverage Digital Patch via the Safe Firewall integration to guard your workloads in opposition to exploits whereas the patch is utilized. Even within the state of affairs {that a} workload modifications its habits (e.g., from trusted to untrusted on account of an intrusion occasion or malware occasion) you may leverage Safe Firewall intelligence via FMC (Firewall Administration Heart) to quarantine workloads.

3. Reporting Threat
DORA mandates to report main ICT-related incidents to related competent authorities. Due to this, reporting turns into a paramount course of throughout the group. Safe Workload gives a number of choices for reporting, starting from close to real-time visualization dashboard and reviews to detailed point-in-time retrospectives of incidents.
- Safety Dashboard: Supplies a high-level overview of the safety posture and hygiene of the atmosphere.
- Vulnerability Dashboard: Shows present CVEs throughout the atmosphere together with an in depth evaluation of their potential impression on confidentiality, integrity, and availability. Extra metrics resembling danger rating, exploitability, and complexity are additionally included.
- Reporting Dashboard: Presents an in depth view tailor-made to particular roles like SecOps and NetOps. An essential functionality to say right here is how the safety abstract maps to a contemporary risk-based strategy to detect adversaries MITRE ATT&CK framework. Safe Workload has a number of forensic guidelines mapped to the MITRE ATT&CK TTPs (Approach, Ways, and Procedures) permitting one to establish an adversary and observe each single step taken to compromise, exploit, and exfiltrate knowledge.


Key Takeaways
Whereas navigating the necessities of DORA could seem daunting, the proper instruments can revolutionize your group’s strategy to Cyber Resilience with a risk-centric focus. Safe Workload may be instrumental in facilitating this transformation, enabling your group to attain:
- Strategic Cyber Resilience: Safe Workload could be a strategic enabler for aligning with DORA’s imaginative and prescient. Transitioning from a reactive cybersecurity stance to a proactive, risk-based strategy, prepares your group to anticipate and counteract the evolving cyber risk panorama
- Complete Threat Insights: With granular visibility into software workload communications, dependencies, and vulnerabilities, coupled with the implementation of sturdy microsegmentation and compensating controls, Safe Workload equips you with the capabilities to not solely perceive but additionally to successfully mitigate dangers earlier than they materialize into breaches.
Study extra about Cisco Safe Workload
We’d love to listen to what you assume. Ask a Query, Remark Beneath, and Keep Linked with Cisco Safety on social!
Cisco Safety Social Channels
Share:


