Microsoft’s Visible Studio Code (VS Code) code editor and growth setting incorporates a flaw that permits malicious extensions to retrieve authentication tokens saved in Home windows, Linux, and macOS credential managers.
These tokens are used for integrating with numerous third-party providers and APIs, akin to Git, GitHub, and different coding platforms, so stealing them may have important penalties for a compromised group’s knowledge safety, doubtlessly resulting in unauthorized system entry, knowledge breaches, and so forth.
The flaw was found by Cycode researchers, who reported it to Microsoft together with a working proof-of-concept (PoC) they developed. But, the tech big determined in opposition to fixing the difficulty, as extensions should not anticipated to be sandboxed from the remainder of the setting.
Stealing secrets and techniques with extensions
The safety downside found by Cycode is brought on by a scarcity of isolation of authentication tokens in VS Code’s ‘Secret Storage,’ an API that permits extensions to retailer authentication tokens within the working system.
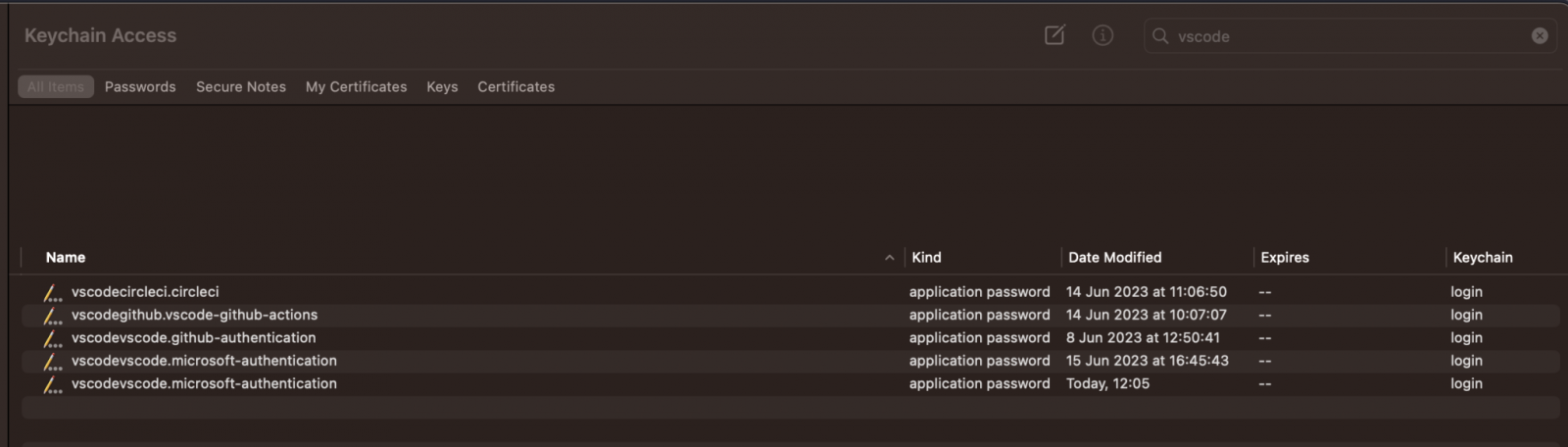
That is achieved utilizing Keytar, VS Code’s wrapper for communication with the Home windows credential supervisor (on Home windows), keychain (on macOS), or keyring (for Linux).
Which means any extension operating in VS Code, even malicious ones, can acquire entry to the Secret Storage and abuse Keytar to retrieve any saved tokens.
Cycode researcher Alex Ilgayev advised BleepingComputer that apart from the built-in GitHub and Microsoft authentication, the entire saved credentials from use of third-party extensions.
“Apart from the built-in Github/Microsoft authentication, all tokens saved in VSCode come from extensions,” Ilgayev advised BleepingComputer.
“They’re both outlined by official extensions (from Microsoft), akin to Git, Azure, Docker/Kubernetes, and so forth., or by third-party extensions, akin to CircleCI, GitLab, AWS.”
Supply: Cycode
Upon discovering the issue, Cycode’s researchers began experimenting by making a malicious extension to steal tokens for CircleCI, a preferred coding platform with VS Code extensions. They did this by modifying CircleCI’s extension to run a command that may expose its safe token and even ship it straight to the researcher’s server.
Step by step, they developed a extra versatile assault methodology to extract these secrets and techniques with out tampering with the goal extension’s code.
The important thing to this course of was discovering that any VS Code extension is allowed to entry the keychain as a result of it runs from inside the utility that the working system has already granted entry to the keychain.
“We developed a proof-of-concept malicious extension that efficiently retrieved tokens not solely from different extensions but additionally from VS Code’s built-in login and sync performance for GitHub and Microsoft accounts, presenting a “Token Stealing” assault.” – Cycode.
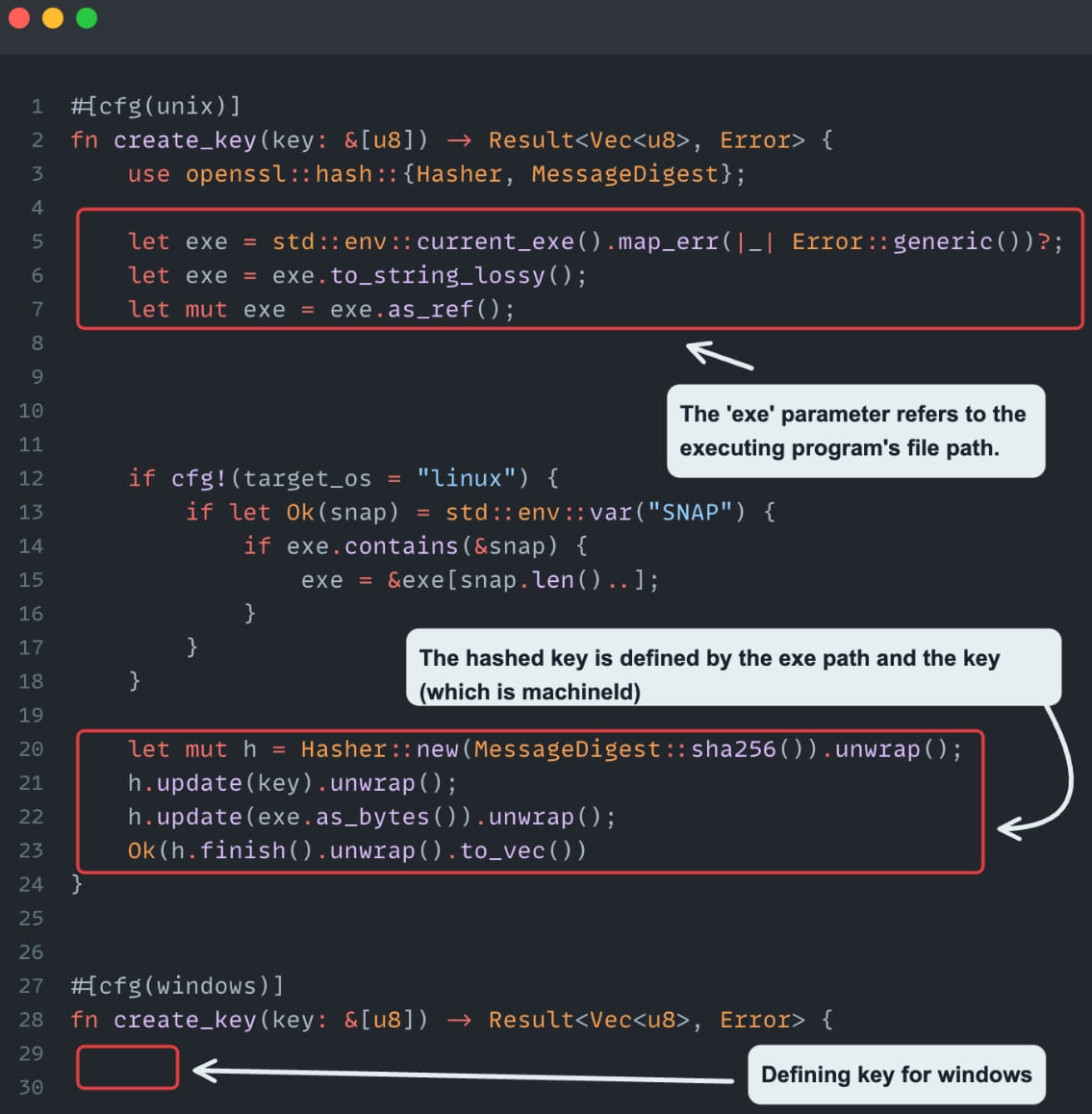
Subsequent, the retrieved tokens needed to be decrypted, and Cycode discovered that the algorithm used to encrypt tokens was AES-256-GCM, which is normally protected. Nonetheless, the important thing used to encrypt the tokens was derived from the present executable path and the machine ID, making it simple to recreate the important thing.
Supply: Cycode
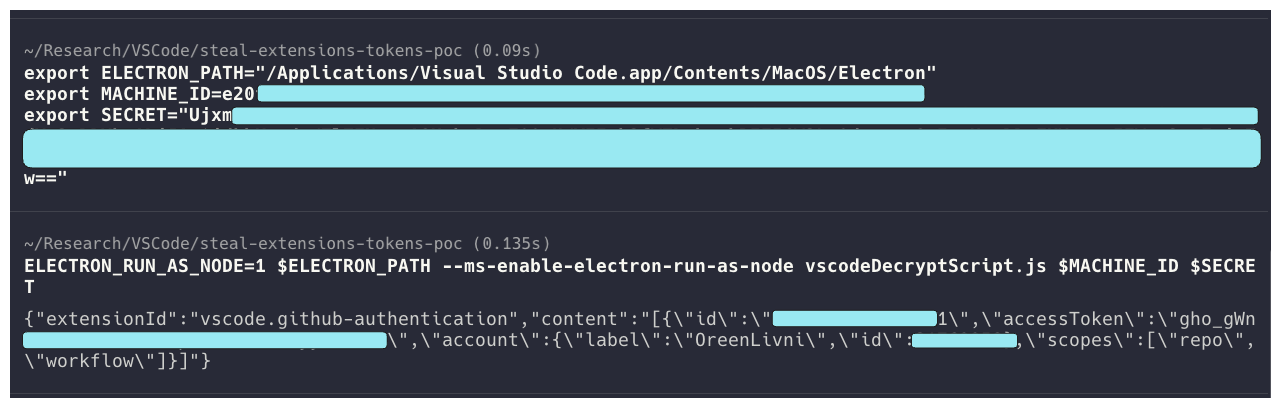
The retrieved tokens had been decrypted by a customized JS script run in VS Code’s Electron executable, deciphering and printing all passwords of regionally put in extensions.
Supply: Cycode
A second flaw found by Cycode’s researchers was that the ‘getFullKey’ operate retrieves secrets and techniques by a given ‘extensionId,’ which is derived from the extension’s title and writer.
This downside permits anybody to switch these fields and trick VS Code into granting them entry to a different extension’s safe tokens.
Cycode examined this utilizing a PoC extension that mimicked CircleCI once more; nonetheless, they famous that replicating some other extension and having access to its secrets and techniques can be trivial.
Disclosure and (not) fixing
Cycode advised BleepingComputer that they disclosed the issue to Microsoft two months in the past, even demonstrating their PoC extension and its means to steal saved extension tokens.
Regardless, Microsoft’s engineers did not see this as a safety concern and determined to take care of the prevailing design of VS Code’s secret storage administration framework.
BleepingComputer has contacted Microsoft for a touch upon the above however has not obtained a response to our questions.

