A surprising variety of organizations — together with banks and healthcare suppliers — are leaking non-public and delicate data from their public Salesforce Group web sites, KrebsOnSecurity has discovered. The info exposures all stem from a misconfiguration in Salesforce Group that permits an unauthenticated consumer to entry information that ought to solely be accessible after logging in.
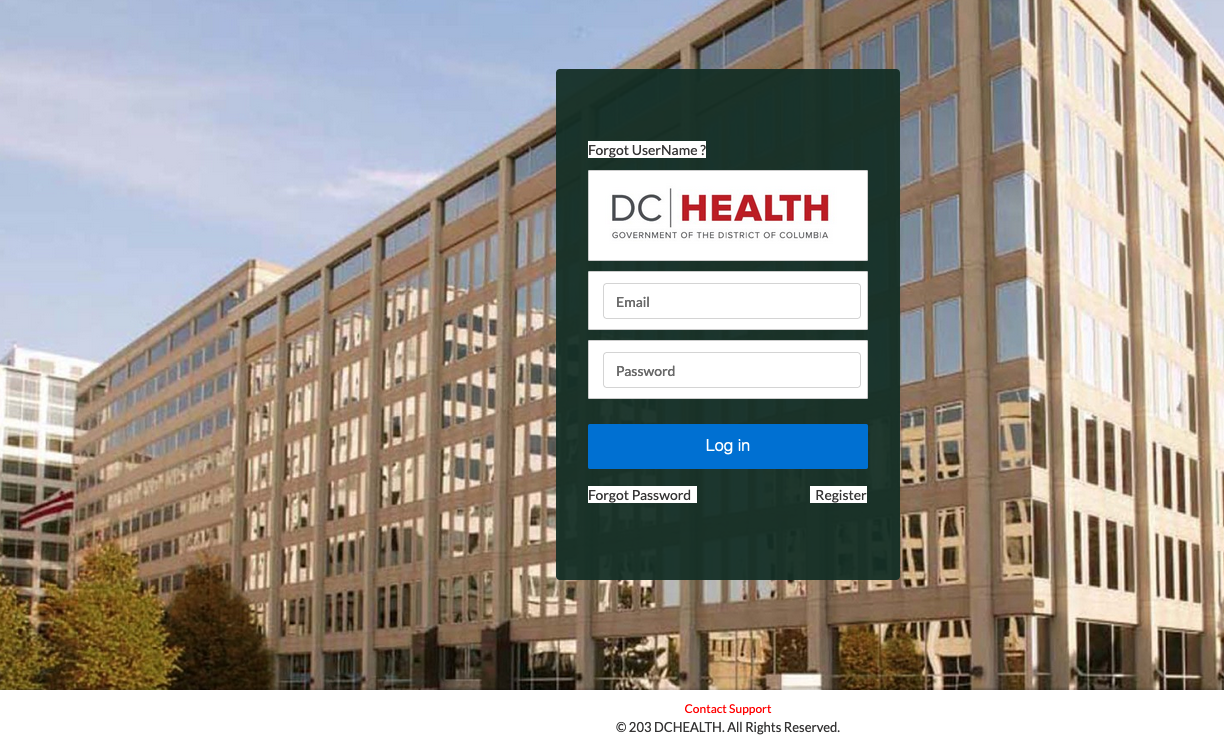
A researcher discovered DC Well being had 5 Salesforce Group websites exposing knowledge.
Salesforce Group is a widely-used cloud-based software program product that makes it straightforward for organizations to rapidly create web sites. Clients can entry a Salesforce Group web site in two methods: Authenticated entry (requiring login), and visitor consumer entry (no login required). The visitor entry function permits unauthenticated customers to view particular content material and sources with no need to log in.
Nonetheless, typically Salesforce directors mistakenly grant visitor customers entry to inside sources, which may trigger unauthorized customers to entry a corporation’s non-public data and result in potential knowledge leaks.
Till being contacted by this reporter on Monday, the state of Vermont had not less than 5 separate Salesforce Group websites that allowed visitor entry to delicate knowledge, together with a Pandemic Unemployment Help program that uncovered the applicant’s full title, Social Safety quantity, deal with, cellphone quantity, electronic mail, and checking account quantity.
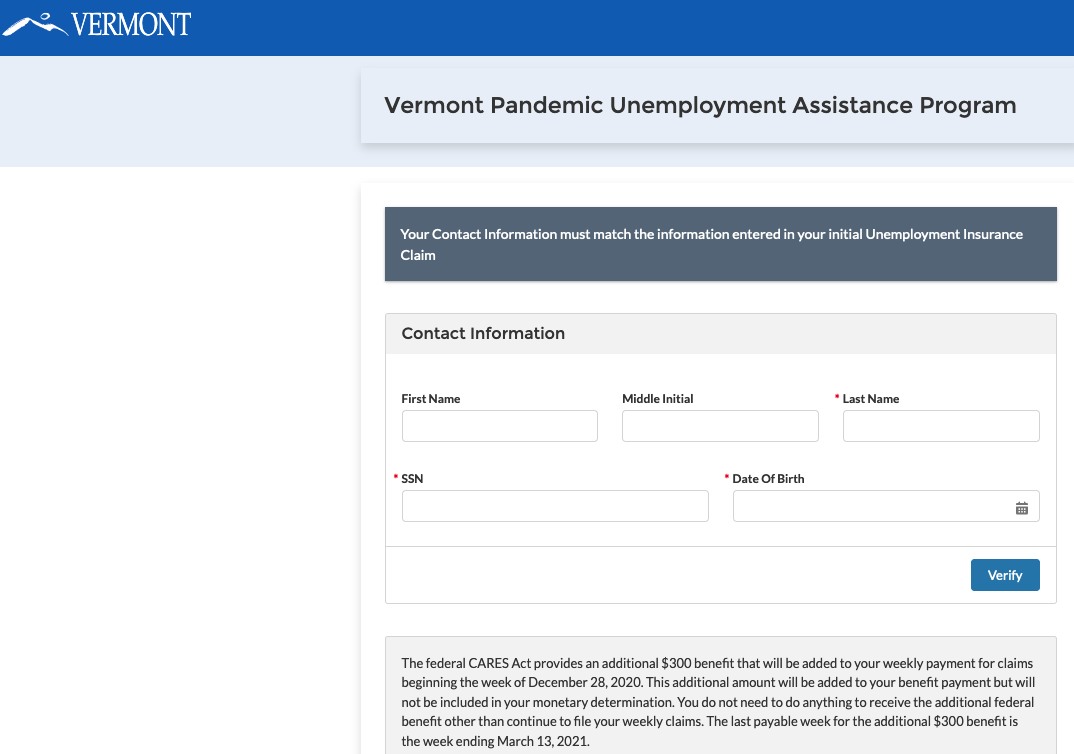
This misconfigured Salesforce Group website from the state of Vermont was leaking pandemic help mortgage utility knowledge, together with names, SSNs, electronic mail deal with and checking account data.
Vermont’s Chief Data Safety Officer Scott Carbee mentioned his safety groups have been conducting a full assessment of their Salesforce Group websites, and already discovered one further Salesforce website operated by the state that was additionally misconfigured to permit visitor entry to delicate data.
“My group is annoyed by the permissive nature of the platform,” Carbee mentioned.
Carbee mentioned the susceptible websites had been all created quickly in response to the Coronavirus pandemic, and weren’t subjected to their regular safety assessment course of.
“Throughout the pandemic, we had been largely standing up tons of functions, and let’s simply say lots of them didn’t have the complete advantage of our dev/ops course of,” Carbee mentioned. “In our case, we didn’t have any native Salesforce builders after we needed to all of a sudden get up all these websites.”
Earlier this week, KrebsOnSecurity notified Columbus, Ohio-based Huntington Financial institution that its lately acquired TCF Financial institution had a Salesforce Group web site that was leaking paperwork associated to industrial loans. The info fields in these mortgage functions included title, deal with, full Social Safety quantity, title, federal ID, IP deal with, common month-to-month payroll, and mortgage quantity.
Huntington Financial institution has disabled the leaky TCF Financial institution Salesforce web site. Matthew Jennings, deputy chief data safety officer at Huntington, mentioned the corporate was nonetheless investigating how the misconfiguration occurred, how lengthy it lasted, and what number of information could have been uncovered.
KrebsOnSecurity discovered of the leaks from safety researcher Charan Akiri, who mentioned he wrote a program that recognized a whole lot of different organizations operating misconfigured Salesforce pages. However Akiri mentioned he’s been cautious of probing too far, and has had issue getting responses from a lot of the organizations he has notified so far.
“In January and February 2023, I contacted authorities organizations and a number of other firms, however I didn’t obtain any response from these organizations,” Akiri mentioned. “To handle the difficulty additional, I reached out to a number of CISOs on LinkedIn and Twitter. In consequence, 5 firms finally mounted the issue. Sadly, I didn’t obtain any responses from authorities organizations.”
The issue Akiri has been making an attempt to lift consciousness about got here to the fore in August 2021, when safety researcher Aaron Costello printed a weblog publish explaining how misconfigurations in Salesforce Group websites may very well be exploited to disclose delicate knowledge (Costello subsequently printed a follow-up publish detailing how you can lock down Salesforce Group websites).
On Monday, KrebsOnSecurity used Akiri’s findings to inform Washington D.C. metropolis directors that not less than 5 completely different public DC Well being web sites had been leaking delicate data. One DC Well being Salesforce Group web site designed for well being professionals searching for to resume licenses with the town leaked paperwork that included the applicant’s full title, deal with, Social Safety quantity, date of start, license quantity and expiration, and extra.
Akiri mentioned he notified the Washington D.C. authorities in February about his findings, however acquired no response. Reached by KrebsOnSecurity, interim Chief Data Safety Officer Mike Rupert initially mentioned the District had employed a 3rd social gathering to analyze, and that the third social gathering confirmed the District’s IT techniques had been not susceptible to knowledge loss from the reported Salesforce configuration subject.
However after being offered with a doc together with the Social Safety variety of a well being skilled in D.C. that was downloaded in real-time from the DC Well being public Salesforce web site, Rupert acknowledged his group had neglected some configuration settings.
Washington, D.C. well being directors are nonetheless smarting from an information breach earlier this yr on the medical health insurance alternate DC Well being Hyperlink, which uncovered private data for greater than 56,000 customers, together with many members of Congress.
That knowledge later wound up on the market on a prime cybercrime discussion board. The Related Press experiences that the DC Well being Hyperlink breach was likewise the results of human error, and mentioned an investigation revealed the trigger was a DC Well being Hyperlink server that was “misconfigured to permit entry to the experiences on the server with out correct authentication.”
Salesforce says the information exposures usually are not the results of a vulnerability inherent to the Salesforce platform, however they’ll happen when prospects’ entry management permissions are misconfigured.
“As beforehand communicated to all Expertise Website and Websites prospects, we advocate using the Visitor Consumer Entry Report Package deal to help in reviewing entry management permissions for unauthenticated customers,” reads a Salesforce advisory from Sept. 2022. “Moreover, we advise reviewing the next Assist article, Greatest Practices and Concerns When Configuring the Visitor Consumer Profile.”
In a written assertion, Salesforce mentioned it’s actively centered on knowledge safety for organizations with visitor customers, and that it continues to launch “sturdy instruments and steering for our prospects,” together with:
Management Which Customers Expertise Cloud Website Customers Can See
Greatest Practices and Concerns When Configuring the Visitor Consumer Profile
“We’ve additionally continued to replace our Visitor Consumer safety insurance policies, starting with our Spring ‘21 launch with extra to come back in Summer time ‘23,” the assertion reads. “Lastly, we proceed to proactively talk with prospects to assist them perceive the capabilities accessible to them, and the way they’ll finest safe their occasion of Salesforce to satisfy their safety, contractual, and regulatory obligations.”

