The SEI SBOM Framework helps organizations use a software program invoice of supplies (SBOM) for third-party software program administration. We created it, partially, in response to Government Order (EO) 14028, Enhancing the Nation’s Cybersecurity. Launched within the wake of the SolarWinds and Apache Log4j provide chain assaults, EO 14028 requires U.S. authorities companies to boost software program provide chain safety, transparency, and integrity by using SBOMs.
In case your group produces or provides software program for the U.S. authorities, maybe you might have already executed your due diligence and complied with EO 14028. You have got analyzed your code, extracted the related knowledge, composed your SBOM, and made it obtainable. You would declare victory and depart it at that. However think about all the info you might have assembled and should preserve—why not make good use of it?
On this SEI Weblog put up, I’ll study methods you may leverage your SBOM knowledge, utilizing the SEI SBOM Framework, to enhance your software program safety and inform your provide chain threat administration.
The SBOM Is a Knowledge-Wealthy Useful resource
An SBOM is a proper document containing the small print and provide chain relationships of assorted parts utilized in constructing software program. Consider it as an annotated checklist of components in your software program. Thus far, so good. However when you think about that software program consists of many libraries and modules and different (typically open supply) parts, most of which have been produced by third events who, in flip, might incorporate parts from different third events additional upstream, a lot of which could have their very own SBOMs, you start to grasp that an SBOM can rapidly develop into a really huge knowledge repository.
To assist baseline SBOM knowledge, in July 2021 the Division of Commerce specified the minimal parts for an SBOM:
- provider title: the title of an entity that creates, defines, and identifies parts
- part title: the designation assigned to a unit of software program outlined by the unique provider
- model of the part identifier: the identifier utilized by the provider to specify a change in software program from a beforehand recognized model
- different distinctive identifiers: different identifiers which might be used to determine a part, or function a look-up key for related databases
- dependency relationship: a characterization of the connection that an upstream part X is included in software program Y
- creator of SBOM knowledge: the title of the entity that creates the SBOM knowledge for this part
- timestamp document: the date and time of the SBOM knowledge meeting
As you may see, manually assembling an SBOM for all of the parts that compose a typical software program product would signify an enormous endeavor, even when you solely collected the minimal data required by the Division of Commerce. Nonetheless, most SBOMs are produced utilizing software program composition evaluation (SCA) instruments, which scan code to determine and catalog open supply software program (OSS) parts. To facilitate automation, the next machine- and human-readable knowledge codecs can be found for producing and consuming SBOMs:
Even with automation, creating SBOMs is a weighty, sophisticated activity. The SEI SBOM Framework compiles a set of main practices for constructing and utilizing an SBOM to assist cyber threat discount. This tailor-made model of our Acquisition Safety Framework (ASF) offers a roadmap for integrating SBOM utilization into the acquisition and improvement efforts of a corporation to arrange for managing vulnerabilities and dangers in third-party software program, together with commercial-of-the-shelf (COTS) software program, government-of-the-shelf (GOTS) software program, and open supply software program (OSS).
The next sections recommend methods organizations can apply the SEI SBOM Framework to handle third-party software program and improve the safety of their software program improvement pipelines and merchandise.
Leveraging Your SBOM Knowledge: 2 SEI SBOM Framework Use Instances
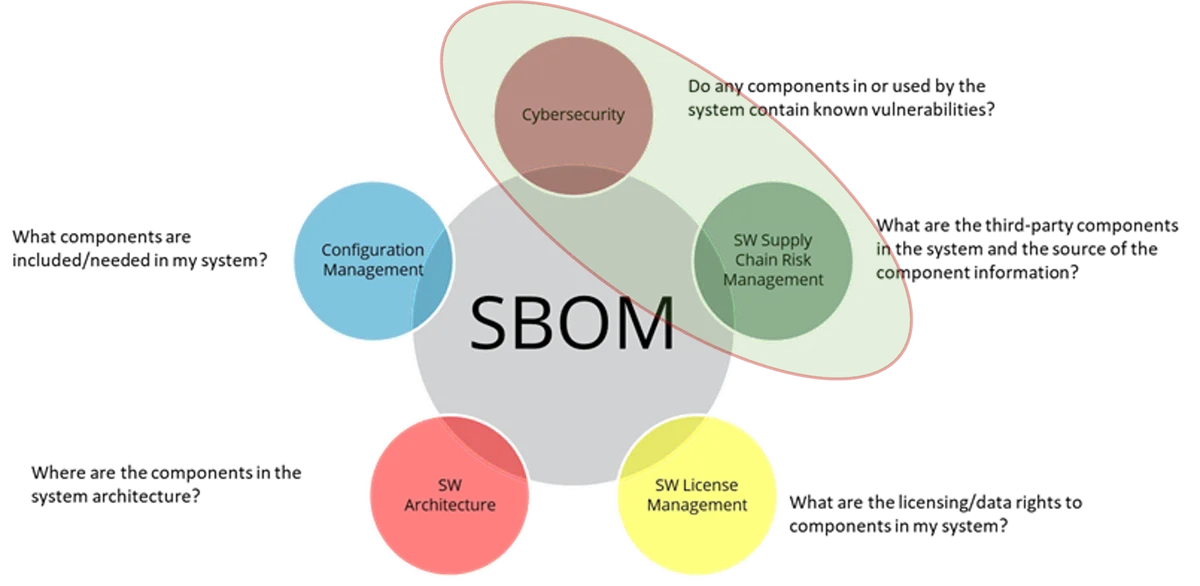
In our SEI Weblog put up introducing the SEI SBOM Framework, we famous 5 observe areas through which you should use the framework to enhance third-party software program administration (Determine 1). On this put up, I’ll sketch use instances for 2 of those areas: cybersecurity and software program provide chain threat administration.
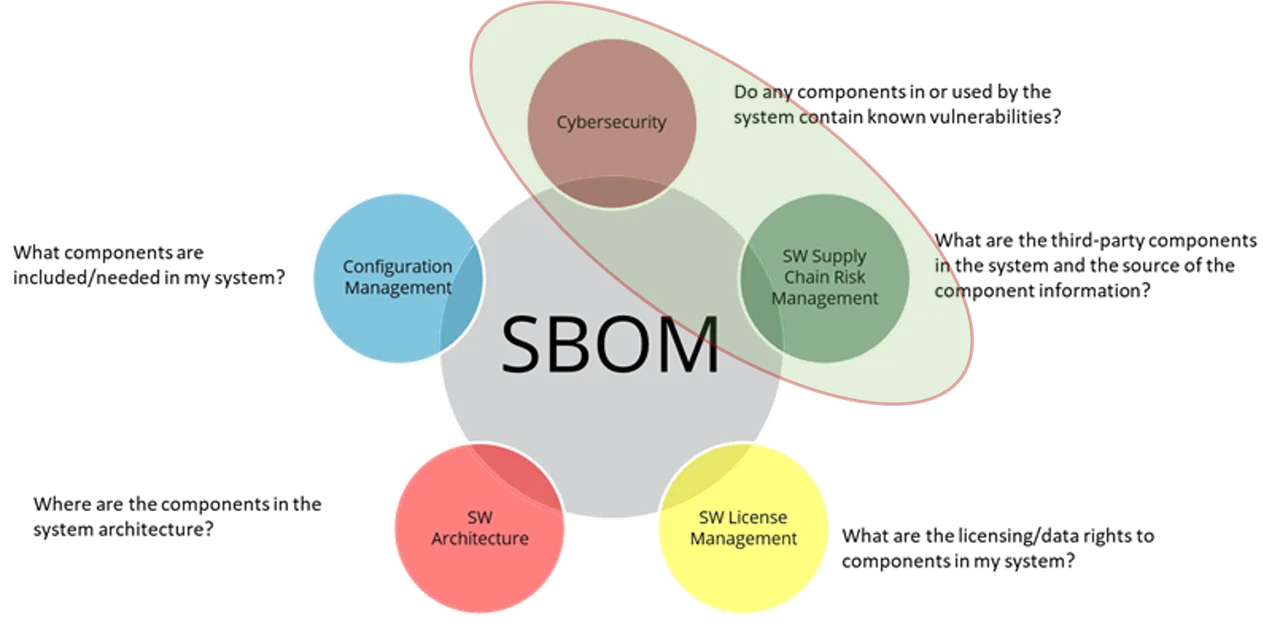
Determine 1: SBOM Framework Use Instances Examined in This SEI Weblog Submit
These two areas figured prominently within the motivation for the EO 14028 SBOM mandate within the wake of the SolarWinds assault, through which attackers injected malware into SolarWinds merchandise that unfold the malware by software program updates, and the exploitation of a vulnerability in Apache’s Log4j software program library, a software program part utilized by many different downstream functions. Most just lately, a vulnerability in MOVEit, a broadly used file-transfer part integrated in lots of software program packages, enabled attackers to steal data from all kinds of firms and organizations, together with the U.S. Division of Vitality.
An SBOM Framework purpose defines the result or goal towards which a program’s effort is directed. Every SBOM purpose is supported by a gaggle of practices. Practices describe discrete actions that have to be carried out to attain a purpose. Practices are framed as questions.
The SEI SBOM Framework construction (Determine 2) is tailored from the SEI Acquisition Safety Framework construction, which is designed to assist a program coordinate managing engineering and supply-chain dangers throughout system parts, together with {hardware}, community interfaces, software program interfaces, and mission. A company can use the SBOM Framework to determine gaps in the way it makes use of SBOM knowledge and to research what interventions would supply the best worth for the group. Underneath this multilayered framework, a number of observe areas comprise a number of domains, which in flip comprise a number of objectives, which in flip comprise a number of practices.
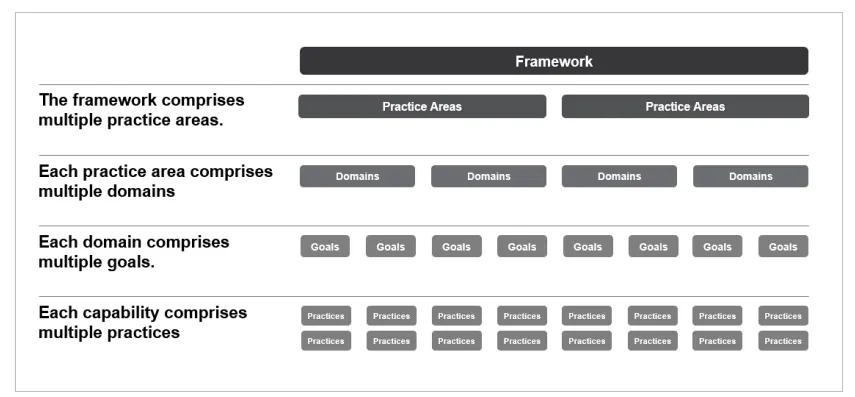
Determine 2: SEI SBOM Framework Construction
From our evaluation of SBOM use instances, we assembled a set of related practices, which we then mapped to the acquisition and improvement lifecycle to determine related domains as follows: necessities, planning, construct/assemble, deploy/use, handle/assist, and infrastructure. A website is concentrated on a given technical or administration subject, reminiscent of program planning, threat administration, or necessities, and inside every area there are a number of objectives supporting it.
USE CASE: Utilizing the SEI SBOM Framework to Enhance Cybersecurity by Managing Identified Vulnerabilities
On this use case, one vital purpose related to cybersecurity is vulnerability administration. For every purpose, the SBOM Framework focuses particular practices which might be framed as inquiries to encourage a corporation to discover how properly they’re addressing this observe. The next observe questions had been recognized in vulnerability administration related to SBOMs, and the linkage between SBOM knowledge and vulnerability knowledge offers perception as as to whether a weak software program part is in use on the group and poses a cybersecurity threat:
- Are identified vulnerabilities and obtainable updates monitored for software program parts recognized within the system’s SBOM? Retaining monitor of identified vulnerabilities and software program updates is an important exercise for efficient vulnerability administration. A well-designed SBOM will comprise details about your software program or system, all of the parts it contains, and the suppliers of these parts. Nonetheless, the present steering mainly says you could monitor to the primary degree of part use (e.g., you understand what you used, however not essentially under that degree). The secondary and decrease dependencies are unknown dangers until an SBOM provider signifies there aren’t any additional dependencies. This data might be paired with vulnerability data, reminiscent of that communicated by the Widespread Vulnerabilities and Exposures (CVE) checklist maintained by MITRE, to assist warn you to any parts with identified vulnerabilities. Notice that the vulnerability data is saved outdoors of the SBOM (not a part of it). Understanding what you might have, when it’s been uncovered, and really useful mitigations can significantly facilitate your vulnerability administration efforts.
- Are vulnerabilities in SBOM parts recognized? Right here we transfer from the system degree to the part degree. Scanning supply code and binaries to determine potential vulnerabilities is an choice open to every group. Whereas not all organizations have this experience available, impartial service suppliers can help. Organizations ought to mechanically scan and mitigate vulnerabilities within the supply code they’re creating. The proprietor of the software program might want to deal with the chance mitigation for third-party parts.
- Is the mission threat of every SBOM part assessed? Not all parts are equal. A vulnerability in a single part may result in catastrophic penalties if exploited, whereas a vulnerability in one other part would possibly stay unaddressed for months with out consequence. From a system perspective, understanding the place within the software program and system structure the affected parts are positioned is critical to guage the chance to the system. The software program and system structure data (e.g., implementation) isn’t a part of the SBOM data and can take some subject material experience (multidisciplinary strategy) to map these data sources. Mission threads, which hint the stream of essential mission actions by the expertise layers, can help in figuring out the parts of excessive significance. On this manner, you may focus your vulnerability administration efforts on parts most important to mission success.
- Are software program updates prioritized primarily based on their potential affect to mission threat? For software program or programs comprising many third-party parts, managing updates for all these parts presents a frightening activity. Having recognized the parts most important to mission success, you must prioritize these parts and allocate sources to updating the highest-priority parts first. In an ideal world, you’ll keep 100% updated on all part releases, however in the actual world of restricted organizational sources and a gradual stream of updates for a whole bunch of parts, it’s essential to allocate sources properly. Utilizing SBOM knowledge to determine and rank parts most important to mission success, you may care for essential parts first and fewer essential parts as time and sources enable.
- Are software program part evaluations/updates performed primarily based on their mission-risk priorities? Simply as you prioritized software program updates primarily based on the extent of mission threat every part poses to your software program or system, so too do you have to prioritize part evaluations. As soon as once more, the main focus right here is on utilizing the data you’ve collected within the SBOM to determine parts most important to mission success and/or those who current the best mission threat ought to they be compromised. Doing so lets you slim your focus within the face of an awesome quantity of information and apply your sources successfully and effectively.
- Are vulnerability administration standing, dangers, and priorities tracked for every software program part? Your SBOM knowledge offers you details about all of the parts in your system. Evaluating that knowledge with knowledge from a vulnerability checklist service like CVE lets you know when one in every of your parts is in danger. Instruments can be wanted to do that successfully. When you’ve assessed and prioritized your parts primarily based on mission threat, will you understand whenever you final up to date a part? Are you able to simply decide the place a given part ranks when it comes to mission threat? What if a change to your software program or system has elevated the precedence of a part you as soon as thought of low threat? To make the simplest use of your SBOM knowledge for ongoing vulnerability administration, it’s essential to spend money on knowledge administration programs and practices.
The duties on this vulnerability administration use case, and in threat administration extra typically, assist you to determine and prioritize your most dear belongings. On this case, you’re making selections primarily based on mission threat. These selections contain tradeoffs. Right here, the tradeoff is defending your most dear parts, and subsequently your software program and/or system, from severe hurt ensuing from vulnerabilities whereas permitting for the potential of an exploit of a vulnerability in a part with low mission threat. Such a tradeoff is inevitable for software program and/or programs with a whole bunch or 1000’s of parts.
USE CASE: Utilizing the SEI SBOM Framework to Enhance Provide Chain Danger Administration
The shortage of integration amongst a system’s expertise groups, together with suppliers, is one other supply of threat the place SBOM data may also help cut back threat and enhance effectivity. {Hardware} has acquired a lot of the consideration previously with issues for counterfeits, however the rising affect of software program dealing with performance requires a deal with each. However groups typically work in stovepipes, and the groups who use provider software program and expertise companies/merchandise might also neglect to have interaction or oversee these suppliers. Improvement and assist groups typically work independently with various aims and priorities pushed by price and schedule calls for that don’t absolutely think about current or potential threat.
One other consideration vital to the federal government is overseas possession, management, or affect (FOC) of organizations supplying the {hardware} and software program. That is additionally tracked outdoors of an SBOM however may very well be built-in utilizing a free-form subject.
On this use case, the next observe questions (which, bear in mind, are framed as evaluation questions) apply to the purpose of Handle/Assist. The aim of this purpose is to make sure that correct, full, and well timed SBOM knowledge is obtainable for system parts to successfully handle threat. Connecting the SBOM knowledge with different provider data obtainable to the group strengthens the flexibility to handle provide chain threat administration. The particular observe questions are as follows:
- Are the suppliers for system parts recognized? This data can come from the SBOM. Understanding the suppliers may also help you handle bug fixes, integration points, and different issues extra effectively. Some suppliers could also be unknown, reminiscent of for open-source parts, and this offers an indicator of potential threat.
- Is provider knowledge reviewed periodically and up to date as wanted? Constructing an SBOM will not be a “one-and-done” exercise. Over time, data might change. For example, the corporate who equipped one in every of your parts previously fiscal 12 months might have been acquired by a bigger firm within the present fiscal 12 months. Deal with the SBOM as a part of the info that must be configuration managed and managed. To make sure your knowledge is beneficial, it’s essential to set up schedules and processes for holding provider knowledge present.
- Are SBOMs for system parts recognized, analyzed, and tracked? Third-party organizations producing system parts ought to be producing their very own SBOMs for these parts. Understanding what’s in these parts, what upstream dependencies would possibly exist, what model has been used, and different related knowledge is crucial whenever you’re working to resolve points launched by third-party part software program. Consequently, you must institute practices for figuring out SBOMs revealed for the third-party parts utilized in your software program. You must also decide what SBOM data is most related to your wants and study this data to guage what, if any, penalties incorporating the part may need in your system’s performance and safety. Bear in mind that software program might have exterior dependencies (e.g., Dynamic Hyperlink Libraries in Home windows), which is not going to be within the SBOM as it’s at the moment outlined, since they’re runtime dependencies.
- Are SBOMs managed to make sure they’re present? Suppliers and merchandise are repeatedly altering. Efficient provider administration requires information of dependencies in order that single factors of failure and dangers for provider loss might be proactively managed. The extra your knowledge is outdated, the much less useful it turns into. For example, in case your SBOM knowledge tells you you’re utilizing model 2.0 of part X, however you’ve just lately up to date your system to model 2.4, you would possibly miss a vulnerability alert associated to model 2.4, inflicting ache in your customers or prospects and risking the fame of your group. Counting on the distributors to offer this data also can depart you in danger. You’ll want to develop and implement schedules and practices for holding your SBOMs updated that will require individuals from throughout the group (i.e., acquisition, engineering, and operations).
- Are the dangers associated to incomplete or lacking SBOM knowledge recognized and mitigated? There are typically plenty of high quality points with SBOMs which might be slowly being labored out (e.g., lacking or incomplete knowledge, non-compliance with the minimal parts steering, and so on.). The SBOMs must be validated earlier than being accepted to be used (or revealed). For example, lacking model data, or lacking details about an upstream subcomponent of the part you’ve integrated into your system, can delay or impede efforts to resolve threat in a well timed method. Within the case of lacking upstream dependency knowledge, you may not even pay attention to a provider downside till it’s too late. You’ll want to guarantee you might have a system or observe for figuring out incomplete or lacking knowledge in your SBOMs, gathering that data, and updating your SBOMs. This would possibly imply working along with your suppliers to make sure their SBOMs are full and updated.
- Are dangers and limitations associated to managing and redistributing SBOM data recognized and managed? The requirement to make SBOM knowledge obtainable requires consideration of how broadly that knowledge can be shared. Many have expressed concern that it might pose issues associated to the disclosure of delicate or categorized data. Nonetheless, the SBOM is simply a listing of the components and never the detailed description of how they’re assembled. If protections are wanted, since there can be consolidation of a variety of details about suppliers, making certain the data is obtainable to people who want it throughout the group and downstream within the provide chain have to be a major consideration.
- Is the provenance of SBOM knowledge established and maintained? The usefulness of SBOM knowledge rests on the diploma to which you’ll be able to belief the info is correct and derives from reputable sources. You’ll want to analyze which knowledge is most vital to the safety of your system and develop processes to make sure the integrity of the info and the flexibility to hint the possession of that knowledge to a verifiable supply. These processes should be capable of accommodate provider consolidation, shifts in provider sources, and different regular acquisition enterprise processes.
Provider administration is a posh however more and more vital space of consideration for each group as our dependencies by expertise improve. Leveraging obtainable SBOM data can set up a focus for gathering and sustaining this data in a sharable format, however timeliness and integrity of the info is essential.
The SEI SBOM Framework: Making Software program Administration Extra Manageable
The mandate for SBOMs articulated in Government Order 14028 imposed a heavy elevate for many who develop and handle software program offered to the DoD and U.S. authorities. One results of all of the work that goes into creating an SBOM is much more knowledge to course of and handle. The excellent news is you could put that knowledge to work to enhance your efforts in cybersecurity, provide chain administration, software program license administration, software program structure, and configuration administration. The SEI SBOM Framework may also help you alongside your path to organizing, prioritizing, and managing this knowledge that can assist you goal your efforts in these areas and make them extra environment friendly and efficient. Actually, this may contain additional work within the quick time period, however this work can pay nice long-term dividends.