A number of domains tied to Genesis Market, a bustling cybercrime retailer that offered entry to passwords and different information stolen from hundreds of thousands of computer systems contaminated with malicious software program, have been seized by the Federal Bureau of Investigation (FBI) at this time. The area seizures coincided with greater than 100 arrests in america and overseas focusing on those that allegedly operated the service, in addition to suppliers who constantly fed Genesis Market with freshly-stolen information.

A number of web sites tied to the cybercrime retailer Genesis Market had their homepages modified at this time to this seizure discover.
Lively since 2018, Genesis Market’s slogan was, “Our retailer sells bots with logs, cookies, and their actual fingerprints.” Prospects might seek for contaminated methods with quite a lot of choices, together with by Web handle or by particular domains related to stolen credentials.
However earlier at this time, a number of domains related to Genesis had their homepages changed with a seizure discover from the FBI, which mentioned the domains have been seized pursuant to a warrant issued by the U.S. District Court docket for the Japanese District of Wisconsin.
The U.S. Legal professional’s Workplace for the Japanese District of Wisconsin didn’t reply to requests for remark. The FBI declined to remark.
Replace, April 5, 11:40 a.m. ET: The U.S. Division of Justice simply launched an announcement on its investigation into Genesis Market. In a press briefing this morning, FBI and DOJ officers mentioned the worldwide regulation enforcement investigation concerned 14 international locations and resulted in 400 regulation enforcement actions, together with 119 arrests and 208 searches and interviews worldwide. The FBI confirmed that some American suspects are amongst these arrested, though officers declined to share extra particulars on the arrests.
The DOJ mentioned investigators have been in a position to entry the person database for Genesis Market, and located the invite-only service had greater than 59,000 registered customers. The database contained the acquisition and exercise historical past on all customers, which the feds say helped them uncover the true identities of many customers.
Unique story: However sources near the investigation inform KrebsOnSecurity that regulation enforcement companies in america, Canada and throughout Europe are at present serving arrest warrants on dozens of people thought to assist Genesis, both by sustaining the positioning or promoting the service bot logs from contaminated methods.
The seizure discover consists of the seals of regulation enforcement entities from a number of international locations, together with Australia, Canada, Denmark, Germany, the Netherlands, Spain, Sweden and the UK.
When Genesis clients buy a bot, they’re buying the flexibility to have the entire sufferer’s authentication cookies loaded into their browser, in order that on-line accounts belonging to that sufferer will be accessed with out the necessity of a password, and in some circumstances with out multi-factor authentication.
“You should purchase a bot with an actual fingerprint, entry to e-mail, social networks, financial institution accounts, fee methods!,” a cybercrime discussion board advert for Genesis enthused. “You additionally get all earlier digital life (historical past) of the bot – most companies received’t even ask for login and password and determine you as their returning buyer. Buying a bot package with the fingerprint, cookies and accesses, you turn into the distinctive person of all his or her companies and different web-sites. The opposite use of our package of actual fingerprints is to cover-up the traces of your actual web exercise.”
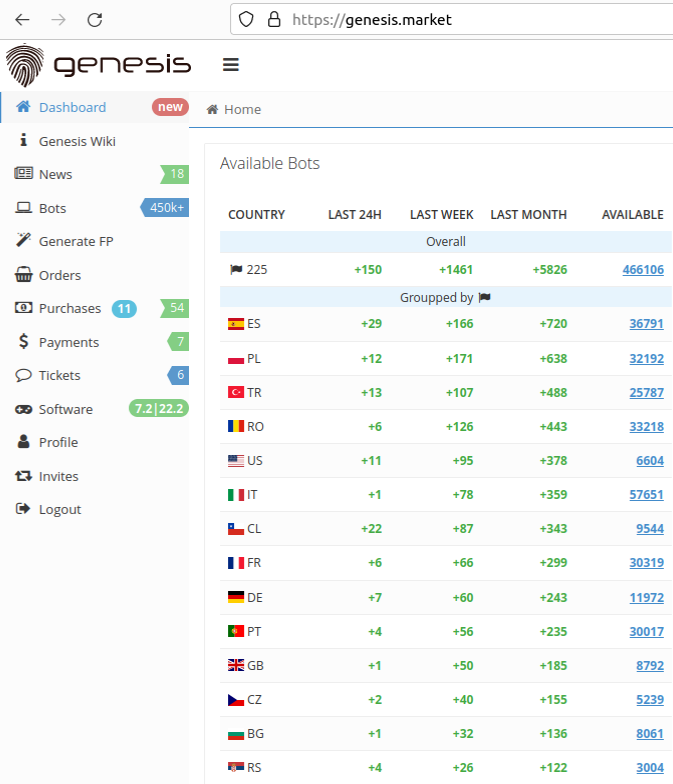
The Genesis Retailer had greater than 450,000 bots on the market as of Mar. 21, 2023. Picture: KrebsOnSecurity.
The pricing for Genesis bots ranged fairly a bit, however usually bots with massive quantities of passwords and authentication cookies — or these with entry to particular monetary web sites akin to PayPal and Coinbase — tended to fetch far increased costs.
New York based mostly cyber intelligence agency Flashpoint says that along with containing a lot of sources, the most costly bots overwhelmingly appear to have entry to accounts which are straightforward to monetize.
“The excessive incidence of Google and Fb is predicted, as they’re such broadly used platforms,” Flashpoint famous in an evaluation of Genesis Market, observing that every one ten of the ten costliest bots on the time included Coinbase credentials.
Genesis Market has launched plenty of cybercriminal improvements all through its existence. Most likely the most effective instance is Genesis Safety, a customized Net browser plugin which might load a Genesis bot profile in order that the browser mimics just about each vital facet of the sufferer’s machine, from display dimension and refresh fee to the distinctive person agent string tied to the sufferer’s net browser.
Flashpoint mentioned the directors of Genesis Market declare they’re a staff of specialists with “intensive expertise within the area of methods metrics.” They are saying they developed the Genesis Safety software program by analyzing the highest forty-seven browser fingerprinting and monitoring methods, in addition to these utilized by 283 completely different banking and fee methods.
Cybersecurity consultants say Genesis and a handful of different bot outlets are additionally in style amongst cybercriminals who work to determine and buy bots inside company networks, after which flip round and resell that entry to ransomware gangs.
Michael Debolt, chief intelligence officer for Intel 471, mentioned so-called “community entry brokers” will scour automated bot outlets for top worth targets, after which resell them for an even bigger revenue.
“From ‘used’ or ‘processed’ logs — it’s really fairly widespread for a similar log for use by a number of completely different actors who’re all utilizing it for various functions – for example, some actors are solely focused on crypto pockets or banking credentials in order that they bypass credentials that community entry brokers are focused on,” Debolt mentioned. “These community entry brokers purchase these ‘used’ logs for very low cost (or generally free of charge) and seek for large fish targets from there.”
In June 2021, hackers who broke into and stole a wealth of supply code and sport information from the pc gaming big EA informed Motherboard they gained entry by buying a $10 bot from Genesis Market that permit them log into an organization Slack account.
One function of Genesis that units it other than different bot outlets is that clients can retain entry to contaminated methods in real-time, in order that if the rightful proprietor of an contaminated system creates a brand new account on-line, these new credentials will get stolen and displayed within the web-based panel of the Genesis buyer who bought that bot.
“Whereas some infostealers are designed to take away themselves after execution, others create persistent entry,” reads a March 2023 report from cybersecurity agency SpyCloud. “Which means unhealthy actors have entry to the present information for so long as the machine stays contaminated, even when the person modifications passwords.”
SpyCloud says Genesis even advertises its dedication to maintain the stolen information and the compromised methods’ fingerprints updated.
“In response to our analysis, Genesis Market had greater than 430,000 stolen identities on the market as of early final yr – and there are various different marketplaces like this one,” the SpyCloud report concludes.
It seems this week’s motion focused solely the clear net variations of Genesis Market, and that the shop remains to be working on a darkish net handle that’s solely reachable by the Tor community. In at this time’s press briefing, DOJ officers mentioned their investigation is ongoing, and that actions taken have already got allowed them to disrupt Genesis in a manner that might not be readily obvious.
In a weblog put up at this time, safety agency Trellix mentioned it was approached by the Dutch Police, who have been searching for help with the evaluation and detection of the malicious information linked to Genesis Market.
“The first purpose was to render the market’s scripts and binaries ineffective,” Trellix researchers wrote.
As described within the Trellix weblog, a serious a part of this effort towards Genesis Market entails focusing on its suppliers, or cybercriminals who’re continuously feeding the market with freshly-stolen bot information. The corporate says Genesis partnered with a number of cybercriminals liable for promoting, distributing and sustaining completely different strains of infostealer malware, together with malware households akin to Raccoon Stealer.
“Through the years, Genesis Market has labored with a big number of malware households to contaminate victims, the place their data stealing scripts have been used to steal data, which was used to populate the Genesis Market retailer,” the Trellix researchers continued. “It comes as no shock that the malware households linked to Genesis Market belong to the standard suspects of widespread info-stealers, like AZORult, Raccoon, Redline and DanaBot. In February 2023, Genesis Market began to actively recruit sellers. We consider with a average stage of confidence that this was completed to maintain up with the rising demand of their customers.”
How does one’s pc turn into a bot in certainly one of these fraud networks? Infostealers are constantly mass-deployed through a number of strategies, together with malicious attachments in e mail; manipulating search engine outcomes for in style software program titles; and malware that’s secretly connected to respectable software program made accessible for obtain through software program crack web sites and file-sharing networks.
John Fokker, head of risk intelligence at Trellix, informed KrebsOnSecurity that the Dutch Police tracked down a number of folks whose information was on the market on Genesis Market, and found that the victims had put in infostealer malware that was bundled with pirated software program.
The Dutch Police have stood up an internet site that lets guests examine whether or not their data was a part of the stolen information on the market on Genesis. Troy Hunt‘s Have I Been Pwned web site can also be providing a lookup service based mostly on information seized by the FBI.
Ruben van Properly, staff chief of the Dutch police cybercrime unit in Rotterdam, mentioned greater than 800,000 guests have already checked their web site, and that greater than 2,000 of these guests have been alerted to energetic infostealer malware infections.
Van Properly mentioned Dutch authorities executed at the very least 17 arrests in reference to the investigation thus far. He added that whereas the cybercriminals operating Genesis Market promised their clients that person account safety was a excessive precedence, the service saved all of its information in plain textual content.
“If customers would say are you able to please delete my account, they’d do it, however we will nonetheless see within the logs that they requested for that,” van Properly mentioned. “Genesis Market was not excellent at defending the safety of its customers, which made a large number for them but it surely’s been nice for regulation enforcement.”
In response to the Dutch Police, Microsoft this morning shipped an replace to supported Home windows computer systems that may take away infections from infostealer malware households related to Genesis Market.
The Dutch pc safety agency Computest labored with Trellix and the Dutch Police to research the Genesis Market malware. Their extremely technical deep-dive is offered right here.
It is a creating story. Any updates will likely be added with discover and timestamp right here.
Apr. 5, 11:00 am ET: Added assertion from Justice Division, and background from a press briefing this morning.
Apr. 5, 12:24 pm ET: Added perspective from Trellix, and context from DOJ officers.
Apr. 5, 1:27 pm ET: Added hyperlinks to lookup companies by the Dutch Police and Troy Hunt.

