ConnectWise, which presents a self-hosted, distant desktop software program utility that’s extensively utilized by Managed Service Suppliers (MSPs), is warning about an unusually subtle phishing assault that may let attackers take distant management over consumer methods when recipients click on the included hyperlink. The warning comes simply weeks after the corporate quietly patched a vulnerability that makes it simpler for phishers to launch these assaults.

A phishing assault concentrating on MSP clients utilizing ConnectWise.
ConnectWise Management is extraordinarily common amongst MSPs that handle, shield and repair giant numbers of computer systems remotely for consumer organizations. Their product offers a dynamic software program consumer and hosted server that connects two or extra computer systems collectively, and offers short-term or persistent distant entry to these consumer methods.
When a assist technician needs to make use of it to remotely administer a pc, the ConnectWise web site generates an executable file that’s digitally signed by ConnectWise and downloadable by the consumer by way of a hyperlink.
When the distant consumer in want of help clicks the hyperlink, their pc is then immediately related to the pc of the distant administrator, who can then management the consumer’s pc as in the event that they had been seated in entrance of it.
Whereas trendy Microsoft Home windows working methods by default will ask customers whether or not they wish to run a downloaded executable file, many methods arrange for distant administration by MSPs disable that consumer account management characteristic for this specific utility.
In October, safety researcher Ken Pyle alerted ConnectWise that their consumer executable file will get generated based mostly on client-controlled parameters. Which means, an attacker might craft a ConnectWise Management consumer obtain hyperlink that will bounce or proxy the distant connection from the MSP’s servers to a server that the attacker controls.
That is harmful as a result of many organizations that depend on MSPs to handle their computer systems typically arrange their networks in order that solely distant help connections coming from their MSP’s networks are allowed.
Utilizing a free ConnectWise trial account, Pyle confirmed the corporate how straightforward it was to create a consumer executable that’s cryptographically signed by ConnectWise and might bypass these community restrictions by bouncing the connection by an attacker’s ConnectWise Management server.
“You because the attacker have full management over the hyperlink’s parameters, and that hyperlink will get injected into an executable file that’s downloaded by the consumer by an unauthenticated Internet interface,” stated Pyle, a companion and exploit developer on the safety agency Cybir. “I can ship this hyperlink to a sufferer, they may click on this hyperlink, and their workstation will join again to my occasion by way of a hyperlink in your web site.”
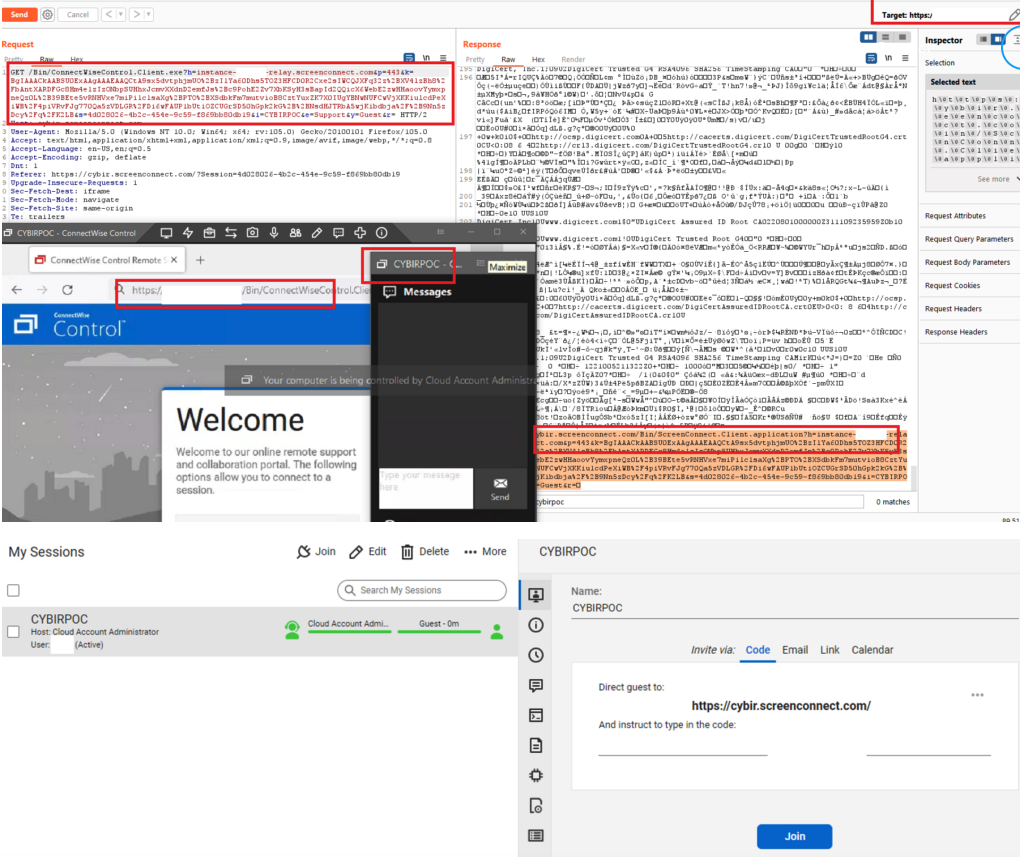
A composite of screenshots researcher Ken Pyle put collectively for instance the ScreenConnect vulnerability.
On Nov. 29, roughly the identical time Pyle revealed a weblog submit about his findings, ConnectWise issued an advisory warning customers to be on guard in opposition to a brand new spherical e-mail phishing makes an attempt that mimic reliable e-mail alerts the corporate sends when it detects uncommon exercise on a buyer account.
“We’re conscious of a phishing marketing campaign that mimics ConnectWise Management New Login Alert emails and has the potential to result in unauthorized entry to reliable Management cases,” the corporate stated.
ConnectWise stated it launched software program updates final month that included new protections in opposition to the misdirection vulnerability that Pyle reported. However the firm stated there is no such thing as a motive to imagine the phishers they warned about are exploiting any of the problems reported by Pyle.
“Our crew rapidly triaged the report and decided the danger to companions to be minimal,” stated Patrick Beggs, ConnectWise’s chief data safety officer. “Nonetheless, the mitigation was easy and offered no threat to companion expertise, so we put it into the then-stable 22.8 construct and the then-canary 22.9 construct, which had been launched as a part of our regular launch processes. As a result of low severity of the problem, we didn’t (and don’t plan to) difficulty a safety advisory or alert, since we reserve these notifications for severe safety points.”
Beggs stated the phishing assaults that sparked their advisory stemmed from an occasion that was not hosted by ConnectWise.
“So we will verify they’re unrelated,” he stated. “Sadly, phishing assaults occur far too commonly throughout quite a lot of industries and merchandise. The timing of our advisory and Mr. Pyle’s weblog had been coincidental. That stated, we’re all for elevating extra consciousness of the seriousness of phishing assaults and the overall significance of staying alert and conscious of doubtless harmful content material.”
The ConnectWise advisory warned customers that earlier than clicking any hyperlink that seems to return from their service, customers ought to validate the content material contains “domains owned by trusted sources,” and “hyperlinks to go to locations you acknowledge.”
However Pyle stated this recommendation just isn’t terribly helpful for purchasers focused in his assault situation as a result of the phishers can ship emails immediately from ConnectWise, and the quick hyperlink that will get offered to the consumer is a wildcard area that ends in ConnectWise Management’s personal area title — screenconnect.com. What’s extra, inspecting the exceedingly lengthy hyperlink generated by ConnectWise’s methods presents few insights to the common consumer.
“It’s signed by ConnectWise and comes from them, and when you join a free trial occasion, you possibly can e-mail individuals invitations immediately from them,” Pyle stated.
ConnectWise’s warnings come amid breach studies from one other main supplier of distant assist applied sciences: GoTo disclosed on Nov. 30 that it’s investigating a safety incident involving “uncommon exercise inside our growth atmosphere and third-party cloud storage companies. The third-party cloud storage service is presently shared by each GoTo and its affiliate, the password supervisor service LastPass.
In its personal advisory on the incident, LastPass stated they imagine the intruders leveraged data stolen throughout a earlier intrusion in August 2022 to realize entry to “sure parts of our clients’ data.” Nevertheless, LastPass maintains that its “buyer passwords stay safely encrypted resulting from LastPass’s Zero Information structure.”
In brief, that structure means when you lose or neglect your all-important grasp LastPass password — the one wanted to unlock entry to all your different passwords saved with them — LastPass can’t make it easier to with that, as a result of they don’t retailer it. However that very same structure theoretically implies that hackers who would possibly break into LastPass’s networks can’t entry that data both.
Replace, 7:25 p.m. ET: Included assertion from ConnectWise CISO.

