At the moment, we announce the discharge of a second model of the risk matrix for storage providers, a structured software that assists in figuring out and analyzing potential safety threats on knowledge saved in cloud storage providers. The matrix, first launched in April 2021 as detailed within the weblog submit Risk matrix for storage providers, lays out a wealthy set of assault strategies mapped to a well known set of techniques described by MITRE’s ATT&CK® framework and complete data base, permitting defenders to extra effectively and successfully adapt and reply to new strategies.
Cybercriminals goal cloud storage accounts and providers for quite a few functions, similar to accessing and exfiltrating delicate knowledge, gaining community footholds for lateral motion, enabling entry to extra sources, and deploying malware or participating in extortion schemes. To fight such threats, the up to date risk matrix offers higher protection of the assault floor by detailing a number of new preliminary entry strategies. The matrix additional offers visibility into the risk panorama by detailing a number of novel assaults distinctive to cloud environments, together with some not but noticed in actual assaults. The brand new model of the matrix is out there at: https://aka.ms/StorageServicesThreatMatrix
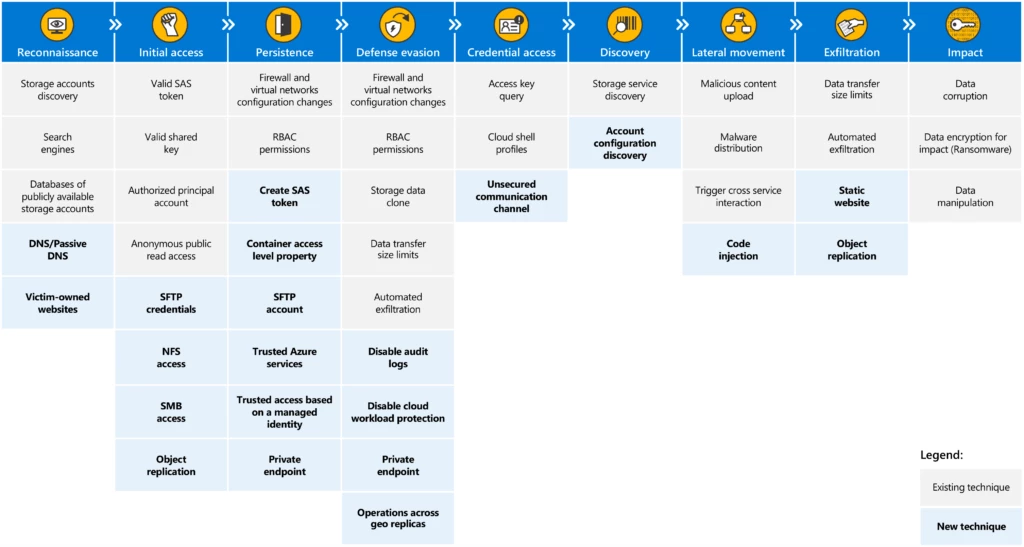
Of the brand new strategies detailed on this weblog, a number of noteworthy examples embrace:
- Object replication – Permits attackers to maliciously misuse the thing replication characteristic in each instructions by both utilizing outbound replication to exfiltrate knowledge from a goal storage account or utilizing inbound replication to ship malware to the goal account.
- Operations throughout geo replicas – Helps attackers evade defenses by distributing operations throughout geographical copies of storage accounts. Safety options could solely have visibility into components of the assault and will not detect sufficient exercise in a single area to set off an alert.
- Static web site – Permits attackers to exfiltrate knowledge utilizing the “static web site” characteristic, a characteristic offered by main storage cloud suppliers that may usually be ignored by much less skilled customers.
On this weblog submit, we’ll introduce new assault strategies which have emerged since our final evaluation and canopy the varied levels of a possible assault on cloud storage accounts.
New strategies within the matrix
1. Reconnaissance
Reconnaissance consists of strategies that contain attackers actively or passively gathering data that can be utilized to assist focusing on.
DNS/Passive DNS – Attackers could seek for DNS knowledge for legitimate storage account names that may turn into potential targets. Risk actors can question nameservers utilizing brute-force strategies to enumerate current storage accounts within the wild, or search by means of centralized repositories of logged DNS question responses (often known as passive DNS).
Sufferer-owned web sites – Attackers could search for storage accounts of a sufferer enterprise by looking its web sites. Sufferer-owned web site pages could also be saved on a storage account or comprise hyperlinks to retrieve knowledge saved in a storage account. The hyperlinks comprise the URL of the storage and supply an entry level into the account.
2. Preliminary entry
Preliminary entry consists of strategies that use numerous entry vectors to realize their preliminary foothold on a storage account. As soon as achieved, preliminary entry could enable for continued entry, knowledge exfiltration, or lateral motion by means of a malicious payload that’s distributed to different sources.
SFTP credentials – Attackers could get hold of and abuse credentials of an SFTP (Safe File Switch Protocol) account as a method of gaining preliminary entry. SFTP is a prevalent file switch protocol between a consumer and a distant service. As soon as the consumer connects to the cloud storage service, the consumer can add and obtain blobs and carry out different operations which can be supported by the protocol. SFTP connections require SFTP accounts, that are managed domestically within the storage service occasion, together with credentials within the type of passwords or key-pairs.
NFS entry – Attackers could carry out preliminary entry to a storage account utilizing the NFS protocol the place enabled. Whereas entry is restricted to an inventory of allowed digital networks which can be configured on the storage account firewall, connection through NFS protocol doesn’t require authentication and could be carried out by any supply on the desired networks.
SMB entry – Attackers could carry out preliminary entry to a storage account file shares utilizing the Server Message Block (SMB) protocol.
Object replication – Attackers could set a replication coverage between supply and vacation spot containers that asynchronously copies objects from supply to vacation spot. This characteristic could be maliciously misused in each instructions. Outbound replication can function an exfiltration channel of buyer knowledge from the sufferer’s container to the adversary’s container. Inbound replication can be utilized to ship malware from an adversary’s container to a sufferer’s container. After the coverage is about, the attacker can function on their container with out accessing the sufferer container.
3. Persistence
Persistence consists of strategies that attackers use to maintain entry to the storage account resulting from modified credentials and different interruptions that might reduce off their entry. Methods used for persistence embrace any entry, motion, or configuration modifications that permit them preserve their foothold on techniques.
Create SAS Token – Attackers could create a high-privileged SAS token with lengthy expiry to protect legitimate credentials for an extended interval. The tokens aren’t monitored by storage accounts, thus they can’t be revoked (besides Service SAS) and it’s not simple to find out whether or not there are legitimate tokens within the wild till they’re used.
Container entry stage property – Attackers could regulate the container entry stage property on the granularity of a blob or container to allow nameless learn entry to knowledge within the storage account. This configuration secures a channel to exfiltrate knowledge even when the preliminary entry approach is not legitimate.
SFTP account – Attackers could create an SFTP account to keep up entry to a goal storage account. The SFTP account is native on the storage occasion and isn’t topic to Azure RBAC permissions. The account can also be unaffected in case of storage account entry keys rotation.
Trusted Azure providers – Attackers could configure the storage account firewall to permit entry by trusted Azure providers. Azure Storage offers a predefined checklist of trusted providers. Any useful resource from that checklist that belongs to the identical subscription because the storage account is allowed by the firewall even when there isn’t a firewall rule that explicitly permits the supply deal with of the useful resource.
Trusted entry primarily based on a managed identification – Attackers could configure the storage account firewall to permit entry by particular useful resource cases primarily based on their system-assigned managed identification, no matter their supply deal with. The useful resource sort could be chosen from a predefined checklist offered by Azure Storage, and the useful resource occasion have to be in the identical tenant because the storage account. The RBAC permissions of the useful resource occasion decide the kinds of operations {that a} useful resource occasion can carry out on storage account knowledge.
Personal endpoint – Attackers could set personal endpoints for a storage account to determine a separate communication channel from a goal digital community. The brand new endpoint is assigned with a non-public IP deal with throughout the digital community’s deal with vary. All of the requests despatched to the personal endpoint bypass the storage account firewall by design.
4. Protection evasion
The protection evasion tactic consists of strategies which can be utilized by attackers to keep away from detection and conceal their malicious exercise.
Disable audit logs – Attackers could disable storage account audit logs to stop occasion monitoring and keep away from detection. Audit logs present an in depth report of operations carried out on a goal storage account and could also be used to detect malicious actions. Thus, disabling these logs can go away a useful resource weak to assaults with out being detected.
Disable cloud workload safety – Attackers could disable the cloud workload safety service which raises safety alerts upon detection of malicious actions in cloud storage providers.
Personal endpoint – Attackers could set personal endpoints for a storage account to determine a separate communication channel from a goal digital community. The brand new endpoint is assigned with a non-public IP deal with throughout the digital community’s deal with vary. All of the requests despatched to the personal endpoint bypass the storage account firewall by design.
Operations throughout geo replicas – Attackers could break up their requests throughout geo replicas to scale back the footprint in every area and keep away from being detected by numerous guidelines and heuristics.
5. Credential entry
Credential entry consists of strategies for stealing credentials like account names and passwords. Utilizing respectable credentials can provide adversaries entry to different sources, make them tougher to detect, and supply the chance to assist obtain their objectives.
Unsecured communication channel – Attackers could sniff community visitors and seize credentials despatched over an insecure protocol. When a storage account is configured to assist unencrypted protocol similar to HTTP, credentials are handed over the wire unprotected and are vulnerable to leakage. The attacker can use the compromised credentials to realize preliminary entry to the storage account.
6. Discovery
Discovery consists of strategies attackers could use to realize data in regards to the service. These strategies assist attackers observe the setting and orient themselves earlier than deciding easy methods to act.
Account configuration discovery – Attackers could leverage management airplane entry permission to retrieve the storage account configuration. The configuration accommodates numerous technical particulars which will help the attacker in implementing a wide range of techniques. For instance, firewall configuration offers community entry data. Different parameters could reveal whether or not entry operations are logged. The configuration may additionally comprise the backup coverage which will help the attacker in performing knowledge destruction.
7. Exfiltration
Exfiltration consists of strategies that attackers could use to extract knowledge from storage accounts. These could embrace transferring knowledge to a different cloud storage exterior of the sufferer account and may additionally embrace placing measurement limits on the transmission.
Static web site – Attackers could use the “static web site” characteristic to exfiltrate collected knowledge exterior of the storage account. Static web site is a cloud storage supplier internet hosting functionality that permits serving static internet content material instantly from the storage account. The web site could be reached through another internet endpoint which is perhaps ignored when proscribing entry to the storage account.
Object replication – Attackers could set a replication coverage between supply and vacation spot containers that asynchronously copies objects from supply to vacation spot. Outbound replication can function an exfiltration channel of buyer knowledge from a sufferer’s container to an adversary’s container.
Conclusion
As the quantity of information saved within the cloud continues to develop, so does the necessity for sturdy safety measures to guard it. Microsoft Defender for Cloud may also help detect and mitigate threats in your storage accounts. Defender for Storage is powered by Microsoft Risk Intelligence and habits modeling to detect anomalous actions similar to delicate knowledge exfiltration, suspicious entry, and malware uploads. With agentless at-scale enablement, safety groups are empowered to remediate threats with contextual safety alerts, remediation suggestions, and configurable automations. Study extra about Microsoft Defender for Cloud assist for storage safety.
Evgeny Bogokovsky
Microsoft Risk Intelligence
References
Additional studying
For the most recent safety analysis from the Microsoft Risk Intelligence neighborhood, take a look at the Microsoft Risk Intelligence Weblog: https://aka.ms/threatintelblog.
To get notified about new publications and to hitch discussions on social media, observe us on Twitter at https://twitter.com/MsftSecIntel.


