
A brand new examine Networks discovered that, on common, organizations depend on over 30 instruments for general safety, and that diploma of complexity is making for much less safety, no more.
Over 60% of organizations have been working in a cloud surroundings for 3 or extra years, however technical complexities and sustaining complete safety nonetheless hamper their cloud migration efforts, in response to the 2023 State of Cloud-Native Safety Report.
SEE: CrowdStrike: Attackers specializing in cloud exploits, information theft (TechRepublic)
Three quarters of respondents to Palo Alto Networks’ survey reported the variety of cloud safety instruments they use creates blind spots that have an effect on their means to prioritize danger and forestall threats. Over three quarters mentioned they wrestle to establish what safety instruments are obligatory to attain their goals.
90% of C-Suites respondents mentioned they may not detect, comprise and resolve cyberthreats inside an hour, and about half conceded {that a} majority of their workforce doesn’t perceive their safety obligations.
Bounce to:
High challenges to offering complete safety, prime to backside, left to proper
Respondents to the Palo Alto Networks’ survey named the highest challenges to offering complete safety, which embody the next:
Managing safety holistically throughout groups
It isn’t sufficient to undertake a duty mannequin between cloud service suppliers and customers; firms have to look inward, and remove silos insofar as they stop safety processes that work for growth, operations and safety.
Embedding safety throughout the cloud-native growth lifecycle
Embedding the appropriate cloud safety options at each stage of the applying growth course of from code to runtime is important.
Coaching IT, growth and safety workers to make use of safety instruments
Cloud-native software growth requires securing “exponentially extra cloud belongings throughout code, workloads, identities, information, and so on., and throughout a number of execution environments, comparable to containers, serverless, and platforms,” famous the agency.
Lack of visibility into safety vulnerabilities throughout cloud assets
Palo Alto Networks calls vulnerability administration the “holy grail of software safety.” However attaining this implies with the ability to mirror the dimensions, pace and agility of the cloud, in response to the corporate. Efficiently performed, it may possibly reward firms with close to real-time detection of threats and vulnerabilities.
Utilizing the appropriate instruments
Within the report, the perfect cloud safety answer is scalable and capable of deal with fast safety wants and extra use circumstances as the corporate expands cloud functions and makes use of.
C-Suites executives not sure about safe cloud deployment
The report is predicated on a survey of two,500 C-level executives worldwide in November and December 2022 that tracked enterprises’ shift from on-premise software program and providers to the cloud and located a usually weak safety posture. A typical theme amongst executives surveyed was that their organizations want to enhance visibility into a number of clouds in addition to incident response and investigation.
“With three out of 4 organizations deploying new or up to date code to manufacturing weekly, and nearly 40% committing new code each day, nobody can afford to miss the safety of cloud workloads,” mentioned Ankur Shah, senior vice chairman, Prisma Cloud, Palo Alto Networks.
“As cloud adoption and growth continues, organizations have to undertake a platform strategy that secures functions from code to cloud throughout multicloud environments.”
5 keys to best-in-class safety capabilities and ease of use
Based on the survey, the highest components firms contemplate when selecting safety options for his or her cloud functions have been:
- Ease of use.
- Finest-in-class capabilities.
- Potential affect on enterprise efficiency.
- Familiarity with vendor or software.
- Aggressive pricing and/or value.
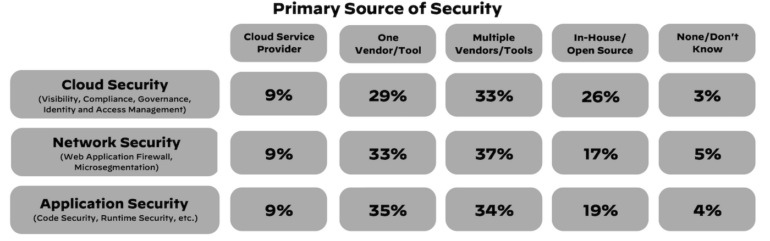
The survey discovered that enterprises are cut up between a single safety vendor/software strategy and a a number of safety vendor/software strategy for every of their safety wants.
Firms maintain too many safety arrows of their quivers
Three quarters of the leaders Palo Alto surveyed mentioned they struggled to establish which safety instruments have been obligatory to attain their goals, which led to deploying quite a few single level safety options — of the 30-plus safety instruments on common that organizations are utilizing, six to 10 are devoted to cloud safety.
SEE: Open supply code for industrial software program functions is ubiquitous, however so is the danger (TechRepublic)
1 / 4 of respondents reported utilizing each in-house and open supply instruments, with many of the firms polled saying they deploy a number of distributors to safe their clouds, networks and functions (Determine A).
Determine A
Safety gaps persist regardless of efforts
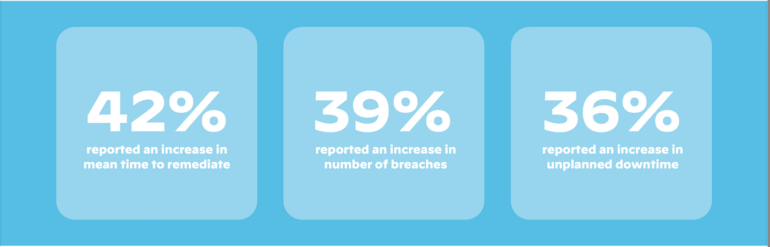
Palo Alto Networks’ examine reported that solely about 10% of respondents couldn’t detect, comprise and resolve threats in lower than an hour. As well as, 68% of organizations have been unable to even detect a safety incident in lower than an hour, and amongst people who did, 69% couldn’t reply in underneath an hour (Determine B).
Determine B
The right way to keep away from blind spots and poor overview of safety danger
Suggestions from the examine’s authors embody shortly figuring out anomalous or suspicious behaviors that point out a compromise, and specializing in the means of accelerating near-constant visibility of cloud belongings, partly by eliminating blind spots brought on by the shortage of a holistic strategy to safety software deployment. The authors additionally recommended:
Incorporate safety in any respect levels
Safety groups ought to have a complete understanding of how their firm goes from growth to manufacturing within the cloud to search out the least disruptive insertion factors for safety instruments.
“Beginning by elevating visibility and fix-recommendations for software program with identified vulnerabilities and container picture scanning is a superb first step in direction of getting early buy-in from DevOps or platform groups,” the report mentioned.
Undertake risk prevention strategies
Deployment ways can actively block zero-day assaults and comprise lateral motion within the occasion of a breach. Additionally, calculate net-effective permissions throughout cloud assets to make sure finest practices for least-privilege entry.
“On the very least, organizations ought to contemplate making use of prevention options to their mission-critical functions,” mentioned Palo Alto.
Align cyber ways with cloud presence
Don’t find yourself with dozens of instruments siloed for particular safety use circumstances within the cloud, resulting in what Palo Alto Networks calls a “sprawl” of instruments that lavatory down cloud safety groups and go away visibility gaps. The corporate suggests reviewing cloud adoption objectives over a two to 5 12 months span.
Consolidate instruments the place potential
Unify information and safety controls right into a platform strategy to acquire a complete view of danger, versus the granular views supplied by a number of siloed instruments.
“By consolidating instruments, safety groups can automate correlation and deal with an important safety points throughout the applying lifecycle,” famous the agency.
Appearing quick when an incident happens depends upon a robust coverage
Safety incidents on computer systems and different gadgets, networks, functions and cloud providers platforms requires a quick response. The earlier one reviews to IT and related safety groups the higher when receiving suspicious messages, noticing uncommon adjustments to system or gadget efficiency, discovering a misdirecting hyperlink or some other suspected assault or infiltration. Obtain TechRepublic Premium’s Safety Incident Response Coverage to be taught finest practices for incident response.


