The SEI conducts impartial technical assessments (ITAs) periodically for any applications that request them, taking a look at each technical and programmatic points. Such requests usually come from both applications which might be experiencing challenges with delivering their methods or from exterior stakeholders to verify on the progress that’s being made. In the middle of performing such an evaluation, the ITA staff might interview as many as 50 to 100 folks from the program administration workplace (PMO) workers, contractor workers, customers, and different exterior stakeholder organizations, all underneath assurance of anonymity. Interviewees usually give very open and candid responses, giving the staff perception into what is definitely taking place on a program and the flexibility to achieve a deep understanding of the pressures and incentives underneath which individuals are working.
One notable facet of such assessments is that comparable issues come up throughout separate and dissimilar applications. The important thing questions that come up when conducting assessments of many alternative applications are “Why do a few of these hostile behaviors maintain taking place throughout fully completely different applications?” and “Is there a option to cease them?” On this weblog put up, I talk about the recurring downside in software program acquisition and growth of what I name clinging to the previous methods. I describe the habits within the context of a real-world state of affairs and supply suggestions on recovering from and stopping future occurrences of this downside. Future posts on this sequence will discover different recurring issues.
About Acquisition Archetypes
The SEI’s work on some of these recurring patterns of habits relies on our experiences doing assessments of huge authorities applications, and employs ideas from methods considering to research dynamics which were noticed in software program growth and acquisition observe.
The Acquisition Archetypes, as we name them, are primarily based partially on the thought of the extra common methods archetypes. Acquisition Archetypes describe recurring patterns of failure noticed in acquisition applications with the intent of constructing folks conscious of them and their results and supply folks with approaches to mitigate or keep away from them. (See among the earlier SEI work in Acquisition Archetypes.)
Within the majority of instances, the incentives at work in acquisition applications don’t change a lot from program to program, and so are inclined to drive comparable behaviors throughout a variety of acquisition applications. Taken collectively, these incentives are analogous to the legal guidelines of physics for nature in that they drive the behaviors of all organizations.
The archetype I current on this put up is expounded to the introduction of a brand new know-how and methodology. I illustrate it within the context of utilizing DevSecOps as a result of it’s a newer portfolio of applied sciences that’s being utilized to key DoD acquisition applications. Nevertheless, this archetype would apply equally nicely to many different new, disruptive applied sciences—underscoring the purpose that regardless of the numerous modifications in know-how and the substantial variations throughout applications, the concepts underlying this archetype nonetheless apply.
Clinging to the Previous Methods
Description
There’s a completely different rigidity taking place inside acquisition applications that attempt to undertake new applied sciences and strategies: the technologists and engineers are thrown into battle with useful organizations which might be unfamiliar with and unaccustomed to doing enterprise in a different way to help the brand new know-how or methodology. These useful organizations usually resist the modifications that will enhance velocity and safety. There could also be some official causes for this resistance. For instance, the present interpretation of the laws underneath which they function might prohibit sure selections or actions.
A tradition of doing issues the same old or conventional manner as a substitute of embracing newer approaches and applied sciences can create schisms inside the program. These schisms usually are not shocking because it’s a serious tradition change to considerably evolve the strategies and insurance policies of any group. Modifications are being pushed by quite a few completely different new strategies and applied sciences—not simply DevSecOps, but in addition model-based methods engineering (MBSE), digital engineering, synthetic intelligence/machine studying, and others. I deal with DevSecOps on this put up as a result of it has demonstrated unprecedented enhancements in DoD fielding occasions and safety, but in addition introduces extra engineering complexity and requires extra coordination and ability.
Some engineers might anticipate everybody to leap onboard with the brand new know-how and are shocked after they don’t and gained’t. Some might imagine the functionals (the finance, authorized, safety, and contracting consultants) are old-fashioned and caught of their methods, or among the functionals might imagine the brand new know-how or methodology is a passing fad that has little to do with the best way they carry out their function. These opposing factors of view characterize a cultural battle that stems from the know-how. The extra the engineers attempt to drive change on the functionals, the more durable these elements of the group are more likely to push again towards these modifications.
An vital facet of this battle is that there are two chains of command for functionals: one which goes to this system they’re working for, and one which goes again to the bigger group they’re part of (e.g., finance, acquisition, and so forth.). The extra revolutionary the technological change, the better the affect on the functionals who must help its enterprise points. For instance, within the context of cybersecurity, as a substitute of the safety functionals adapting the safety strategy to the brand new applied sciences, the technologists are sometimes compelled to make use of the older applied sciences that the safety individuals are extra accustomed to. This aversion to newer applied sciences additionally has to do with the standard approaches of a long time in the past versus the approaches being utilized by engineers at present. The stress manifests in varied methods, similar to within the shift from waterfall to Agile/DevSecOps, or from conventional safety approaches to extra streamlined automated strategies, from monolithic certification on the finish of growth to steady certification, and so forth.
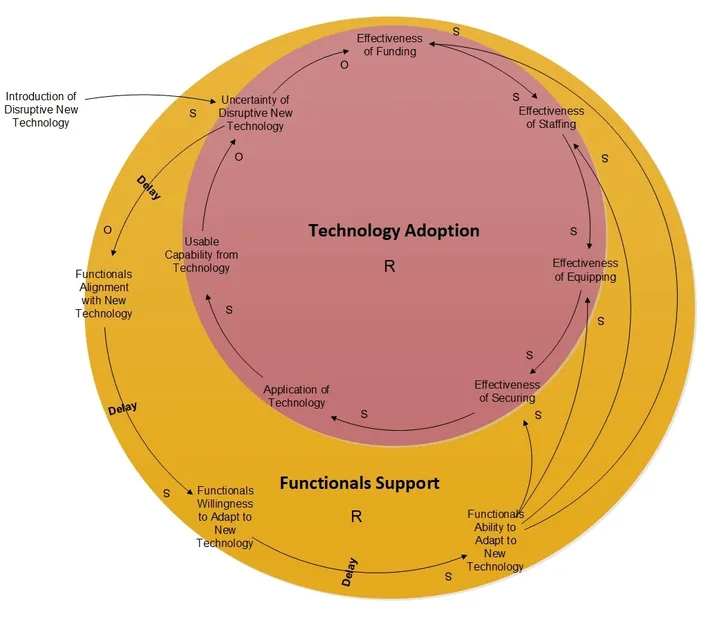
This battle is finally resolved in one in all two methods: Both a point of change is ultimately effected to get functionals’ buy-in and help for adapting the prevailing processes to the brand new know-how, or the know-how adoption is deemed unsuccessful and could also be discarded (Determine 1).
Stories from the Subject
One program that was adopting DevSecOps bumped into quite a lot of points in supporting that strategy with the useful help of acquisition, personnel, buying, and finance. As one official put it, “A part of the frustration on the acquisition facet is the shortage of DevSecOps understanding.”
Equally, one other workers member stated, “Some folks haven’t any expertise with DevSecOps earlier than, in order that they battle. The way in which they strategy applications, they’re functionally aligned, and matrixed to them, so there’s a battle typically to translate their work of finance and contracts to the technical folks.”
One other went as far as to say, “The predominant threat within the DoD house is individuals who don’t perceive DevSecOps and DevSecOps contracting, saying that this manner of constructing software program is illegal—and I’ve been on calls with three authorities attorneys about that, the place they had been arguing that it was unlawful to construct software program that manner. There’s a DoD publication for constructing software program, and the way DoD buys software program. It’s all about waterfall—however nobody builds software program like that anymore. New memos have come out that make DevSecOps buying approaches lawful now, however there’s nonetheless quite a lot of concern on the market, and it’s arduous to persuade people who it’s OK.”
One officer identified that, “We now have Federal Acquisition Regulation (FAR) insurance policies that haven’t modified in years, and acquisition has native insurance policies as nicely, and other people turn into annoyed.” One other stated “In acquisition it’s so troublesome to make one thing occur, you turn into pleased with something you may get. They depart contractual stuff in place for a number of years with out evolving it—however we’d by no means try this on the technical facet. Persons are afraid to ask to do one thing in a different way.”
Whereas the speed of technical change appears to be rising, one workers member stated that lots of the functionals are “…nonetheless dwelling in a world the place individuals are extra snug with the previous manner of doing issues, and never as snug with doing issues in a brand new manner with new know-how. So, it’s the shortage of willingness to make use of digital know-how that considerations me.” As one other acquisition official summed it up, “Nobody is taking a look at how acquisition should change to help DevSecOps”—and so there’s a massive and rising hole between the technical workers and the functionals who help them.
With safety, “It comes off as a Eighties safety strategy. As a substitute of adapting the safety to the brand new applied sciences, they drive you to make use of the older applied sciences that they’re accustomed to as a substitute.” One other admitted that whereas “We would like implementations to be sturdy when it comes to safety, we’ve tried to implement safety that folks both don’t perceive, don’t care about, or each. Most PMs (program managers), most SPDs (system program administrators) don’t perceive, and neither do the SCAs (safety management assessors) or AOs (authorizing officers).”
By way of finance, there are some apparent points in supporting DevSecOps. As one useful famous, “We settle for cash from different applications, 3400 (O&M) and 3600 (RDT&E). We couldn’t combine colours of cash, however you nearly have to with DevSecOps.”
Relating to contracting for skilled DevSecOps workers, a contracting official stated “[The contractor] drives us loopy. They’re the costliest, they suppose they’re unicorns, and they also’re troublesome to barter. They comprehend it, they usually are available in excessive on their charges. As a PCO (procuring contracting officer), I have to decide if the value is truthful and cheap—and you need to justify that. Technical skill is at all times extra vital than worth. Technical folks don’t perceive having to justify the usage of a specific vendor.”
Regardless of the clear must do issues in a different way, one acquisition skilled acknowledged that “There are few acquisition people who find themselves true advocates of or champions for change. That development piece is lacking.” The bigger downside is that “Everybody simply accepts the best way issues are. How will you change your processes so to do it higher and sooner? We are able to’t be content material with what we’ve got. We now have to be considering, what’s subsequent, and what can we make higher?”
In making an attempt to reply that query, one officer admitted that “The [functional] profession area is extra about checking containers to get promoted. It can take an overhaul in expertise administration and career-field administration to do this higher. You too can assist to retrain some communities, however in all probability not all.” For one officer, a key place to begin was acknowledging that “We should provide you with a technique to help DevSecOps. Individuals want a baseline understanding of DevSecOps.” Going additional, one other officer acknowledged that an Agile-based and DevSecOps-like strategy might be utilized to the work of functionals as nicely, saying “We needs to be utilizing DevSecOps for functionals in the identical manner that we’re already utilizing it for engineers/builders, by doing extra in the best way of automation of repetitive duties, and establishing a unique tradition that’s extra modern in utilizing the mechanisms that exist already. We might be doing for acquisition what DevSecOps is doing for software program growth.”
Options and Mitigations
Because of the dual-reporting construction of functionals within the army, some modifications required to allow full help of a brand new know-how, similar to DevSecOps, should happen nicely above the extent of this system workplace making an attempt to undertake it.
A part of the issue is that every service has barely completely different takes on how they interpret the FAR and Protection Federal Acquisition Regulation (DFAR) guidelines—and people guidelines are longstanding and rigorously enforced, though they’re solely interpretations of the unique laws. Revisiting the unique laws usually reveals that they aren’t as restrictive as the following coverage interpretations had been—however years later these interpretations are nonetheless being rigidly utilized even after they not serve both the present altering atmosphere or the unique regulation they had been meant to implement.
One instance is the necessity to do appropriate budgeting 5 years upfront of each deliberate piece of labor divided throughout analysis, growth, take a look at & analysis (RDT&E) versus operations and upkeep (O&M) expenditures, which characteristic nearly paralyzing guidelines relating to which sort of funding must be used for issues similar to direct replacements versus alternative upgrades. One other instance is the buying of software program licenses, the place there’s uncertainty relating to the allowed use of RDT&E versus O&M colours of cash within the first versus subsequent years of use. The cumulative impact is to constrain applications making an attempt to maneuver to extra versatile growth fashions, similar to Agile and DevSecOps, and put their success in danger.
As alluded to earlier, contracting for skilled DevSecOps workers may be troublesome. Likewise, staffing additionally performs a task within the profitable, or unsuccessful, adoption of DevSecOps. There are comparatively few DevSecOps engineers obtainable within the DoD, and DoD is instantly competing with trade when it comes to salaries and work atmosphere when hiring that sort of expert expertise. Packages have difficulties staffing authorities billets with DevSecOps experience, missing acceptable job classes and well-defined profession paths with adequate compensation, and forcing applications to backfill with contract workers—which presents its personal challenges. When army and civilian workers are capable of be employed and educated to work in DevSecOps roles, retention turns into a difficulty as business corporations work to poach them from their authorities roles into what are sometimes extra profitable business positions. The federal government even acts towards its personal pursuits by rotating extremely expert army personnel out of DevSecOps positions to extra conventional (and sometimes much less attention-grabbing) acquisition billets requiring extra routine expertise the place their hard-won DevSecOps experience will not be relevant, and quickly declines.
To deal with the coverage restrictions imposed on acquisition, finance, and contracting functionals, these workers should be educated in the usage of key new applied sciences similar to DevSecOps even when they’re circuitously utilizing them, in order that they’re conscious of the problems, perceive them and the objectives, and are thus higher geared up to advertise and allow the usage of the know-how. Technical workers also needs to turn into extra conscious of the completely different points of acquisition. A few of this coaching content material ought to come from accumulating collectively the insights from the experiences of personnel in software program factories about finest use and leverage current insurance policies. A coaching curriculum alongside the traces of a DevSecOps for Managers needs to be the end result, specializing in
- software program lifecycle processes, acquisition methods, and the total vary of various kinds of contracting automobiles
- how current mechanisms and contractual automobiles may be utilized in modern methods to help DevSecOps
- making current coaching on DevSecOps extra related
- addressing the cultural and course of implications of DevSecOps adoption pertaining to acquisition
- involving DevSecOps consultants in modern coaching roles to show and construct new coursework
One other helpful strategy could be to institute an change program amongst acquisition, finance, and different useful workers working in numerous software program factories, in order that they might share and find out about completely different approaches which were developed and utilized by different workers to deal with comparable points and conditions.
As a extra strategic repair, DoD ought to proceed to check extra of the coverage modifications which may be wanted on precise applications, primarily based on the varieties of key points they face. An instance of such a coverage experiment already occurring is the Price range Appropriation 8 (BA-8) software program funding single appropriation pilots, through which a single new appropriation class (shade of cash) is created that can be utilized for each RDT&E and O&M appropriations. Such an appropriation would imply that applications wouldn’t must price range particular quantities of RDT&E and O&M funding years upfront, probably limiting their skill to spend funding as wanted in a DevSecOps growth, the place the event and upkeep actions are tightly intertwined and troublesome to separate.
To deal with the problems of DevSecOps staffing over the long run, as this system workforce initially grows after which begins to show over, this system should interact in a major workforce enchancment and coaching or retraining exercise, and evolve towards a tradition that may retain such a sophisticated workforce:
- Mentor army officers in DevSecOps organizations with profitable trade DevSecOps leaders to be taught new management types for high-tech groups.
- Survey the federal government and contractor workers commonly (and report back to management) on their morale and the diploma to which the specified DevSecOps tradition is being achieved, and take further steps to advertise the tradition if the metrics usually are not transferring within the course and on the velocity required.
- Actively interact with native and regional universities to create a pipeline of future software program engineers with the DevSecOps expertise to help the wants of this system throughout its lifespan.
- Institute externship applications or rotations between authorities and protection or business trade companions to commonly advance the ability units of key software program growth workers.
- Advocate for brand new compensation charges which might be extra acceptable for hiring and retaining extremely expert DevSecOps positions (comparable to what’s performed for physicians, surgeons, pilot flight pay, and so forth.).
- Advocate for devoted DevSecOps officer and civilian profession tracks past the standard software program profession fields.
- Calm down or get hold of waivers for army rotations for expert DevSecOps officers and enlisted personnel to enhance continuity in groups.
Lastly, a extra controversial strategy is perhaps to align further monetary or efficiency incentives to functionals who efficiently area their applications inside time/price range/high quality objectives, incentivizing general program efficiency in addition to coverage compliance.
The Outlook for DevSecOps Adoption
On this put up, I’ve seemed into one recurring program habits associated to the introduction of DevSecOps into the context of acquisition applications: a battle between builders and their supporting useful areas that aren’t accustomed to supporting this new manner of creating software program.
Whereas it has many substantial advantages, DevSecOps has been—and for the foreseeable future will proceed to be—a strong however disruptive know-how with cooperation issues which might be pervasive all through acquisition. A few of these issues can’t be handled on the particular person program stage and should require some vital coverage modifications throughout the DoD enterprise. The significance of DevSecOps to DoD software program growth signifies that making the modifications to coverage to have the ability to absolutely help it should be a precedence.
In my subsequent weblog put up on this sequence, I’ll talk about intimately one other recurring archetypal downside associated to DevSecOps adoption: vendor lock-in and the excessive value of switching distributors.