In line with a 2023 Ponemon examine, the variety of reported insider danger incidents and the prices related to them continues to rise. With greater than 7,000 reported instances in 2023, the typical insider danger incident value organizations over $600,000. To assist organizations assess their insider danger packages and determine potential vulnerabilities that would end in insider threats, the SEI CERT Division has launched two instruments obtainable for obtain on its web site. Beforehand obtainable solely to licensed companions, the Insider Risk Vulnerability Evaluation (ITVA) and Insider Risk Program Analysis (ITPE) toolkits present sensible strategies to evaluate your group’s skill to handle insider danger. This publish describes the aim and use of the toolkits, with a concentrate on the workbook elements of the toolkits which can be the first strategies of program evaluation.
The ITVA and ITPE Toolkits
The lITVA and ITPE toolkits are supposed to evaluate distinct areas of an insider danger program. The ITVA toolkit helps packages assess their capability to forestall, detect, and reply to threats to a corporation’s vital belongings and processes, and is derived from vulnerabilities coded within the CERT insider menace case corpus. The ITPE toolkit evaluates the elements of an insider danger program at an enterprise stage. It benchmarks them towards Nationwide Insider Risk Process Pressure (NITTF) requirements together with CERT finest practices. Every toolkit consists of a number of workbooks and a wide range of helpful content material to assist facilitate insider danger program assessments, together with interview and logistics steerage, pre-assessment data assortment worksheets, and participant briefing templates.
The Workbooks
The workbooks included with every toolkit are the first strategies of evaluation. The workbooks are organized by the practical space that they assess, and make the most of the Targets, Questions, Indicators, and Measures (GQIM) framework to measure effectiveness. The tables under present the names of the workbooks for the ITVA and ITPE (in daring), in addition to their respective functionality areas:
Insider Risk Program Analysis (ITPE) Workbooks
As proven in Determine 1 under, ITPE is organized by three practical space workbooks: Program Administration, Personnel and Coaching, and Information Assortment and Evaluation. Every workbook is damaged down into particular person functionality areas.
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
Determine 1: The Insider Risk Program Analysis (ITPE) is organized by three practical space workbooks: Program Administration, Personnel and Coaching, and Information Assortment and Evaluation.
Insider Risk Vulnerability Evaluation (ITVA) Workbooks
Just like the ITPE workbooks, the ITVA workbooks are named after seven practical areas: Information House owners, Human Assets, Data Know-how, Authorized, Bodily Safety, Software program Engineering, and Trusted Enterprise Companions (Determine 2). Every workbook is damaged down into particular person functionality areas.
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
||
|
|
|
|
|
|
||
|
|
|
Determine 2: The Insider Risk Vulnerability Evaluation (ITVA) is organized by seven practical space workbooks: Information House owners, Human Assets, Data Know-how, Authorized, Bodily Safety, Software program Engineering, and Trusted Enterprise Companions.
Workbook Scoring Methodology
As talked about above, every workbook within the ITVA and ITPE toolkits is descomposed into practical areas and their particular person capabilities. These capabilities are outlined as a delegated exercise, course of, coverage, or duty thought-about good apply or a requirement for an insider menace program. As an example, the Data Know-how workbook has seven capabilities that can be assessed: Entry Management, Modification of Information or Disruption of Companies or Methods, Unauthorized Entry, Obtain, or Switch of Property, Detection and Identification, Incident Response, and Termination
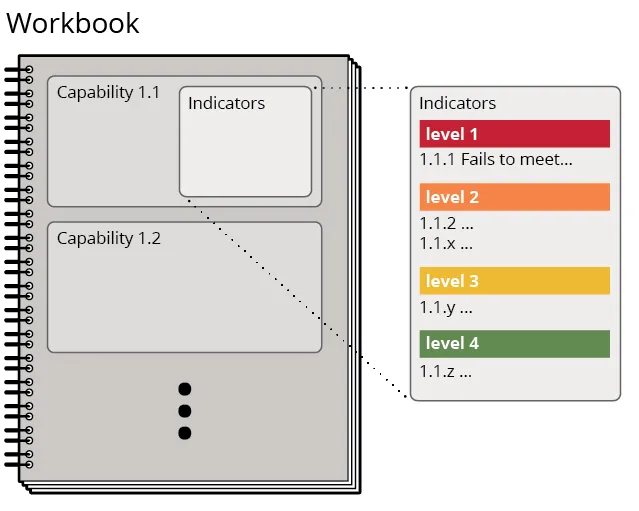
Every functionality makes use of a number of indicators to find out whether or not the related actions are carried out. Indicators are particular person questions associated to controls, practices, processes, or different actions that should be answered and substantiated (by way of interviews, observations, or doc overview) to find out functionality scoring ranges. A functionality is scored based mostly on the indicator stage achieved. Determine 3 exhibits the connection between workbooks, capabilities, and indicators/indicator scoring ranges.
Determine 3: The connection between workbooks, capabilities, and indicators/indicator scoring ranges
Determine 4 under describes the scoring stage definitions utilized by the ITVA and ITPE.
|
ITVA |
ITPE |
||
|
Stage |
Definition |
Stage |
Definition |
|
1: Not Carried out |
There’s a failure in a corporation’s skill to fulfill the functionality. The group shouldn’t be ready to carry out this functionality. |
1: Not Carried out |
There’s a failure of the group to completely carry out this functionality. A number of of the Stage 2: Core indicators are not being carried out. |
|
2: Core |
The group has minimal controls and processes in place. The group is ready to Detect however has points Stopping or Responding to the problem of concern. |
2: Core |
The group performs all of the minimal set of practices as required by the NITTF. All of the Stage 2 Core indicators are carried out. A number of indicators (however not all) at ranges 3 and 4 might also be carried out. |
|
3: Enhanced |
The group has sufficient controls and processes in place. The group is ready to Detect and Reply however has points Stopping the problem of concern. |
3: Enhanced |
The group has extra practices past what’s required by NITTF to handle insider threats to enhance effectivity and performance. All the indications at ranges 2 and three are carried out. Some (however not all) of the indications at stage 4: Strong might also be carried out. |
|
4: Strong |
The group has distinctive controls and insurance policies in place. The group is ready to Stop/Detect/Reply to the problem of concern. |
4: Strong |
The group has in depth practices for the efficient, environment friendly, and sustained administration of insider threats. All the indications at ranges 2, 3, and 4 are carried out. |
Determine 4: Scoring stage definitions utilized by the ITVA and ITPE.
Scoring Instance
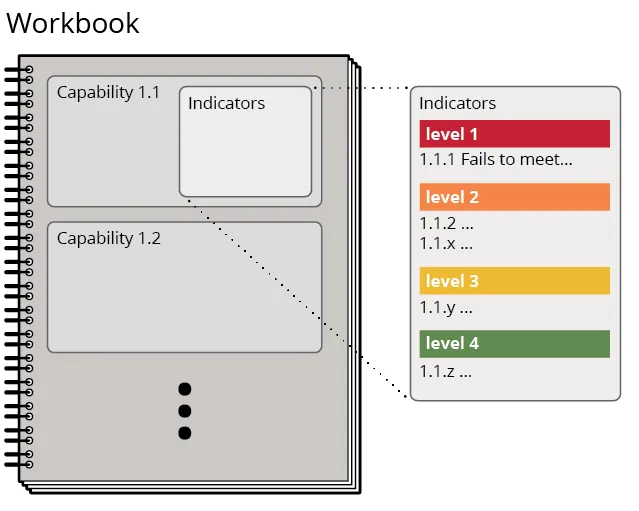
Functionality scores are attained by evaluating the indications at every stage. Stage scores can then be compiled to offer general scoring for the workbook. The next are instance indicators from the Entry Management/Expired Accounts functionality within the Data Know-how workbook. Observe the totally different indicators and substantiation necessities for every of the 4 ranges.

Determine 5: Instance indicators from the Entry Management/Expired Accounts functionality within the Data Know-how workbook.
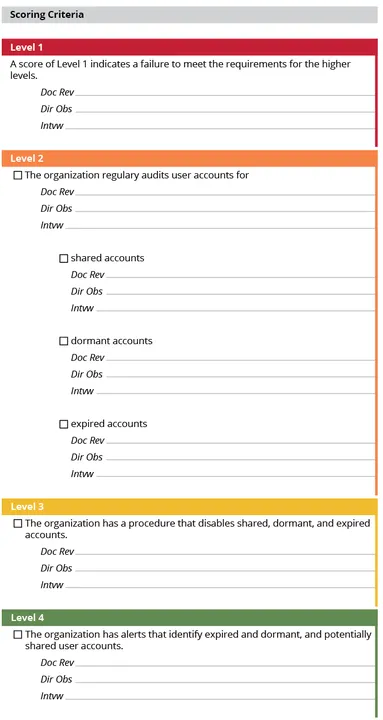
In spite of everything capabilities are scored, cumulative workbook scoring might be produced. The circle graph in Determine 6 under is an instance visualization of functionality scoring from the Data Know-how workbook within the ITVA. The Data Know-how workbook comprises 50 capabilities and greater than 300 indicators. The scoring ranges are represented by shade, together with the variety of capabilities at every scoring stage. Whereas twenty-six of the capabilities are scored as Stage 4 “sturdy,” three operate at an “enhanced” Stage 3, 9 are at a “core” Stage 2, and two capabilities are Stage 1 “not carried out.” Detailed workbook functionality scoring permits organizations to drill right down to particular indicators and distinctly determine strengths and weaknesses of their program, reveal potential gaps in processes and procedures, and supplies a baseline for future assessments.
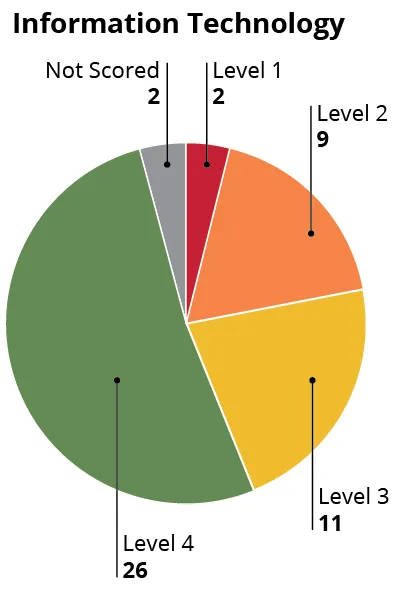
Determine 6: Pattern workbook functionality scoring. The Data Know-how workbook comprises 50 capabilities and greater than 300 indicators.
Extra Workbook Content material
The ITVA and ITPE workbooks additionally embrace extra sections to assist evaluation groups perceive capabilities and help with evaluation actions:
- Clarification/Intent supplies easy-to-understand explanations of the workbook capabilities and their supposed objective.
- Evaluation Staff Steering provides detailed route from CERT to assist evaluation groups consider the workbook capabilities.
- Group Response, Proof Sought, Extra Data outlines extra workbook fields utilized by the evaluation workforce to doc the varied evaluation knowledge collected.
Insider Threat-Measures of Effectiveness (IRM-MOE)
For organizations on the lookout for detailed steerage on the usage of the ITVA and ITPE toolkits, CERT’s new IRM-MOE course provides instruction and help with other ways to evaluate your insider danger program. This three-day course covers utilizing the ITVA and ITPE toolkits, and in addition opinions CISA’s Insider Threat Mitigation Program Analysis (IRMPE) instrument. The IRMPE is a light-weight software with built-in reporting used to assist consider your insider danger program. The software is straightforward to make use of, and might sometimes be accomplished in beneath 4 hours. As well as, the IRM-MOE course supplies instruction for metric growth utilizing the Objective-Query-Indicator-Measure (GQIM) framework. This framework allows insider danger packages to create customized metrics based mostly on their group’s standards.
Toolkits Add Worth to Your Insider Threat Program
The ITVA and ITPE toolkits might be priceless belongings to your insider danger program. The accompanying ITVA and ITPE workbooks assist organizations assess their insider danger packages and determine potential vulnerabilities related to insider danger habits. Utilizing the toolkits as a part of your program’s routine evaluation procedures will help align your program with finest practices and NITTF requirements, determine potential vulnerabilities, and produce scoring to benchmark your program’s progress.