Methods whose failure is insupportable, typically termed vital programs, have to be designed rigorously, no matter whether or not they’re safety-, security-, mission-, or life-critical—or some mixture of the 4. A variety of improvement methodologies and applied sciences exists to help this cautious design, however one of many extra well-studied and promising is model-based engineering (MBE) the place fashions of a system, subsystem, or a set of parts are constructed and analyzed. As a result of sophistication of those fashions and the intricacies of their analyses, nevertheless, software program tooling is nearly required for all however the easiest duties. On this put up, I describe a brand new extension to the Open Supply AADL Software Setting (typically abbreviated as OSATE), SEI’s software program toolset for MBE. This extension, known as the OSATE Slicer, adapts an idea known as slicing to architectural fashions of embedded, vital programs. It does this by calculating of varied notions of reachability that can be utilized to help each guide and automatic analyses of system fashions.
Earlier than diving into the small print, let me take a step again and focus on the method of model-based engineering in a bit extra depth. Typically, fashions are constructed and analyzed previous to the ultimate development of the part or system itself, resulting in the early discovery of system integration points. Whereas engineering fashions are helpful by themselves (e.g., speaking between stakeholders and figuring out gaps in necessities) they will also be analyzed for varied purposeful or non-functional system properties. What’s extra, if the mannequin is constructed utilizing a sufficiently rigorous language, these analyses may be automated. Fashions are, by definition, abstractions of the entities they signify, and people abstractions emphasize a specific perspective. However one factor that analyses—each guide and automatic—can wrestle with is deciphering a mannequin constructed to showcase one perspective (e.g., a purposeful mannequin of a system’s structure) from a special perspective (e.g., the circulation of knowledge or management sequences via these purposeful components).
This explicit shift in perspective is commonly essential, although, and it underlies lots of the guide and automatic analyses we’ve created right here on the MBE workforce on the SEI. Whether or not it’s a security evaluation that should think about the circulation of faulty sensor readings via a system, a safety evaluation that should assure confidential information can not leak out unencrypted ports, or a efficiency evaluation that calculates end-to-end latency, the necessity to extract the paths that information or management messages take via a system is properly established.
The OSATE Slicer
Current work achieved by the MBE workforce goals to assist calculate these paths via fashions of a system’s structure. We’ve got created a software program implementation that generates a graph-based illustration of the paths via a system, after which makes use of that graph to reply reachability queries. This concept could sound acquainted to some readers: it underlies the idea of program or mannequin slicing, which may be very carefully associated to our work, therefore the software program software’s title: The OSATE Slicer (or, the place context makes it clear, simply the slicer). The essential concept of slicing is to take a program or mannequin and a few enter known as a slicing criterion, after which discard every little thing that doesn’t should do with the slicing criterion to provide a decreased model of this system or mannequin. Whereas our work doesn’t but help this full imaginative and prescient of mannequin discount, the reachability graph and question help we’ve carried out are a essential first step, and—as we focus on on this put up—helpful in their very own proper.
Like loads of the work achieved by the SEI MBE workforce, this venture was enabled by two key SEI applied sciences. First, the Architectural Evaluation and Design Language (AADL) is an structure modeling language for vital programs. It has well-specified semantics that make it significantly amenable to automated analyses, and has been used for many years by the U.S. Division of Protection (DoD), business, and researchers for a wide range of functions. The second key know-how is OSATE, which is an built-in improvement setting for AADL. Many analyses that function on AADL fashions are carried out as plug-ins to OSATE, and the slicer is as properly.
In case you’re not acquainted with AADL, there are a variety of sources out there to elucidate the ins and outs of the language (the AADL web site specifically is a superb place to begin). On this put up, although, I’ll use a easy mannequin as an instance a number of the particulars of the OSATE Slicer. This mannequin, proven under, known as the BasicErrorFlow instance. It contains each core AADL, which specifies the fundamental structure of a system, and annotations from AADL’s EMV2 Language Annex, which extends the core language in order that error habits will also be modeled.
The black bins and contours within the mannequin under are legitimate AADL (which has each a graphical and a textual syntax) that present three speaking summary (i.e., undefined and meant for later refinement) components. These components talk over options, named “i” for enter or “o” for output, and numbered 1-3. Superimposed on prime of this (in pink) in a notional syntax is an instance error circulation from factor a, via factor b, into factor c. You may think factor a as some sort of sensor that’s liable to a specific failure, b as an automatic controller which interprets that sensor information and points instructions based mostly upon them, and c as some form of actuator which effectuates the instructions.
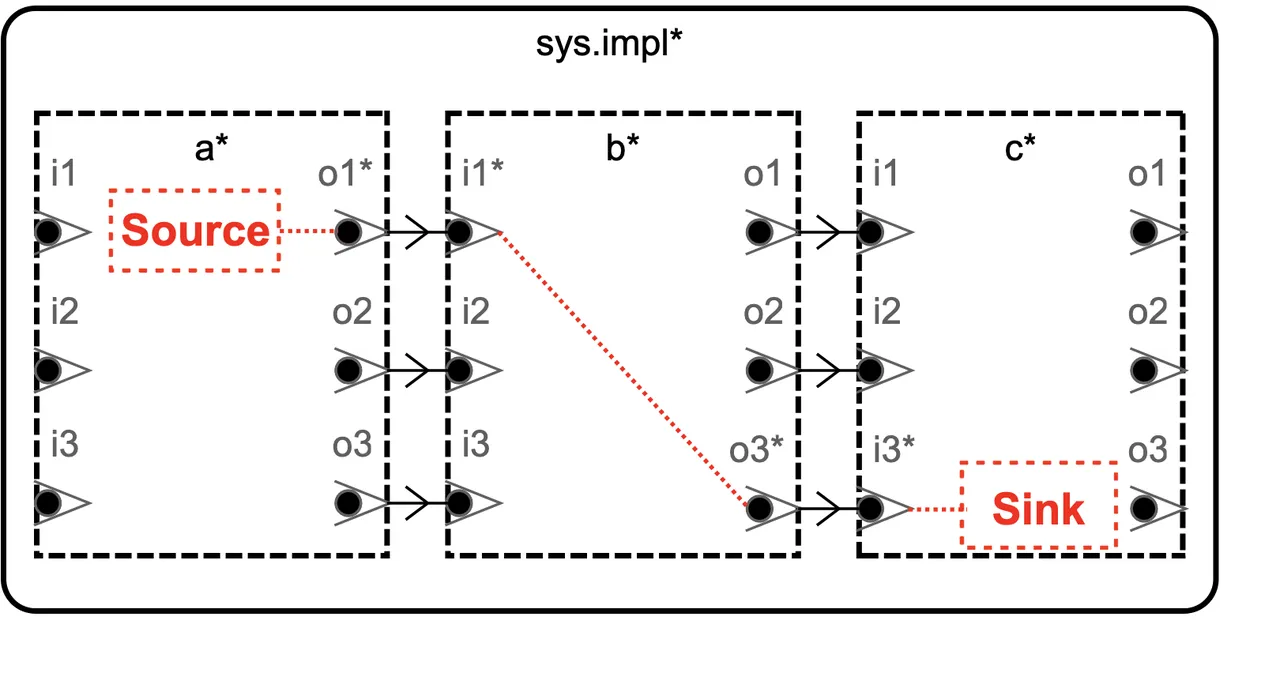
Determine 1: A snippet of graphical AADL, exhibiting the BasicErrorFlow mannequin
“Underneath the Hood” of Architectural Mannequin Evaluation
Let’s dive a bit deeper into how these evaluation plug-ins usually work. Like many instruments that course of inputs laid out in some form of programming or modelling language, OSATE supplies plug-in builders entry to AADL mannequin components utilizing a way known as the customer sample. Primarily, this sample ensures that each factor will likely be “visited” and when it’s, the developer of an evaluation plug-in can specify some motion to take (e.g., recording an related property worth or storing a reference to the factor for later use). Considerably, although, the order through which these components are visited has little to no bearing on the order through which they could create or entry information or management messages when the system is operational. As a substitute, they’re visited in keeping with their place within the mannequin’s summary syntax tree.
Earlier work achieved as a part of the Awas venture by Hariharan Thiagarajan and colleagues at Kansas State College’s SAnToS Lab in collaboration with the SEI demonstrated the worth of extracting and querying a reachability graph from AADL fashions. That work was subsequently constructed on by initiatives each right here on the SEI and externally. See, for instance, its use in DARPA’s Cyber Assured Methods Engineering (CASE) program. We have been satisfied of the worth of this strategy, however needed to see if we may create our personal implementation which—whereas less complicated and fewer feature-rich than Awas—might be extra properly aligned with OSATE’s implementation and design rules, and in doing so, might be extra maintainable and performant.
Maintainability and Efficiency through Cautious Design
Graph Definition and Implementation
Earlier within the put up, I discussed how the OSATE Slicer generates and queries one thing known as a reachability graph. The time period graph is used right here to imply not a chart evaluating completely different values of some variable, however fairly a mathematical or information construction the place vertices are linked collectively by edges, (i.e., “a set of vertices and and edges that be part of pairs of vertices”). The reachability a part of the time period refers back to the which means of the graph: vertices signify explicit components of the system structure, and if two vertices are linked by an edge, that signifies that information or management messages can circulation from the mannequin factor related to the supply vertex to the factor related to the vacation spot vertex. The best graph definition is simply G=(V,→), and that is the definition we use: V is the set of architectural components, and → is a operate connecting a few of these components to another components. The satan is within the particulars, after all; on this case these particulars are which components are included in V and which relationships are included in →. These particulars are specified and defined in a paper printed earlier this yr on the work.
Whereas our graph definition is easy, which ought to assist obtain our objective of creating it quick and easy to generate and question, it’s nonetheless solely a mathematical abstraction. We have to signify the graph in software program, and for that we turned to the wonderful and well-established graph principle library JGraphT. Encoding our graph in JGraphT was easy: we may affiliate OSATE’s illustration of AADL components with JGraphT vertex objects, which lets analyses simply use each the graph and its related system mannequin. Virtually, which means that analyses can run operations on the reachability graph, which can yield graph objects, akin to subgraphs or particular person vertices, after which translate these objects to AADL mannequin components that will likely be significant to customers.
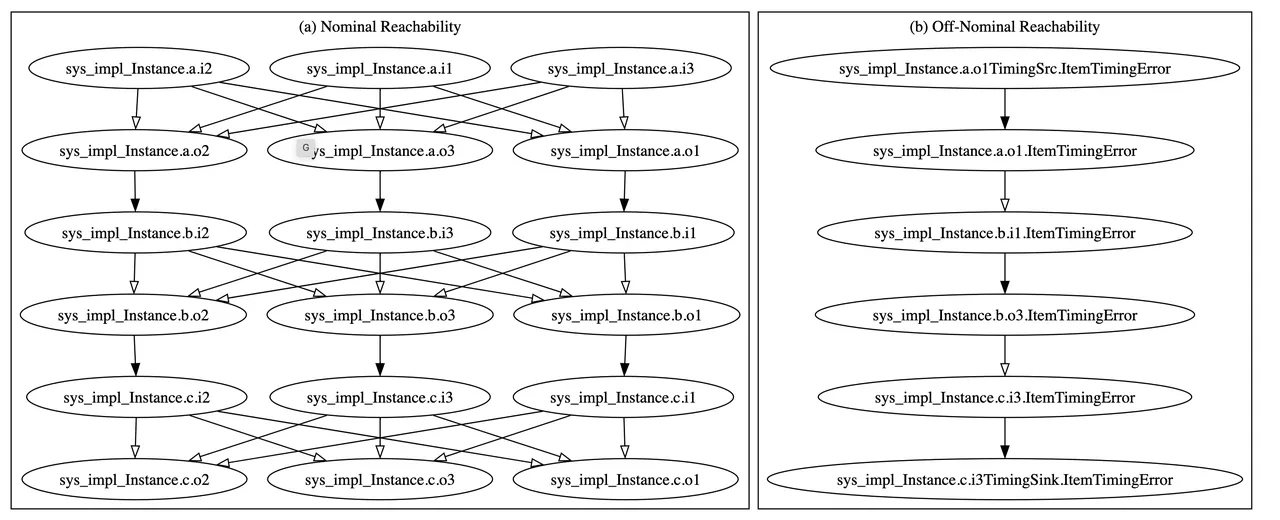
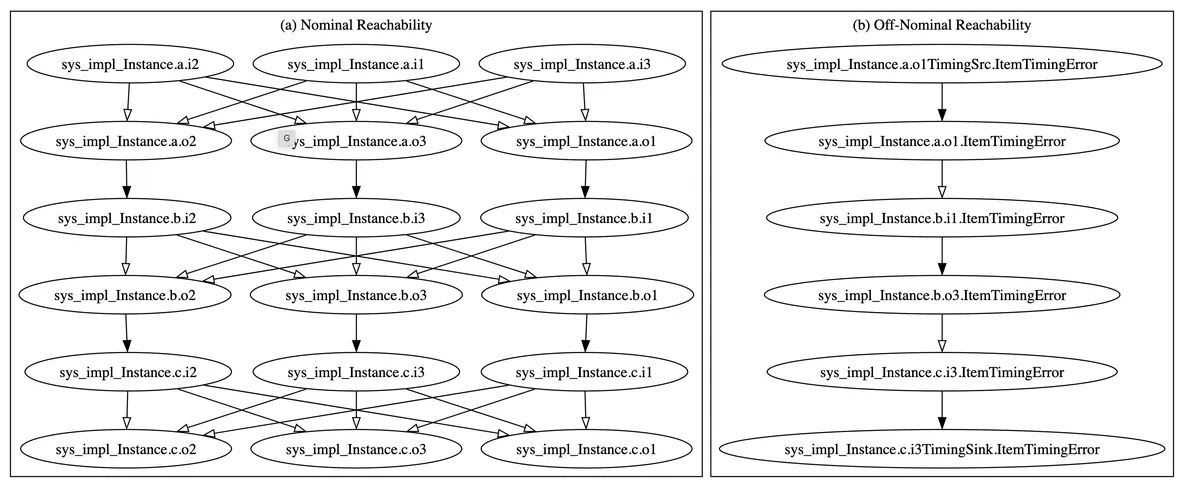
Determine 2: The reachability graph for the BasicErrorFlow mannequin
The reachability graph for the BasicErrorFlow mannequin launched earlier is proven in Determine 2. There are a pair notable issues concerning the graph: First, it’s really two graphs, the one on the left is the nominal graph, constructed utilizing solely core AADL, which is the bottom language. The (far less complicated) graph on the best is the off-nominal graph, constructed utilizing each core AADL and its error-modeling extension referred to as EMV2. For the exact meanings of the graphs, I’ll once more refer readers to the paper. For this put up, I’ve included them to provide an intuitive feeling of the form of information constructions we’re working with. The essential concept, although, is {that a} extra detailed mannequin produces a much less ambiguous reachability graph; so the off-nominal graph (which may make the most of the error circulation info current within the mannequin) is way less complicated and extra exact.
Querying the Reachability Graph
To get any worth out of the reachability graph, we’ve to have the ability to question it, pose questions on relationships between varied vertices. There are 4 foundational queries: attain ahead, attain backward, attain from, and attain via.
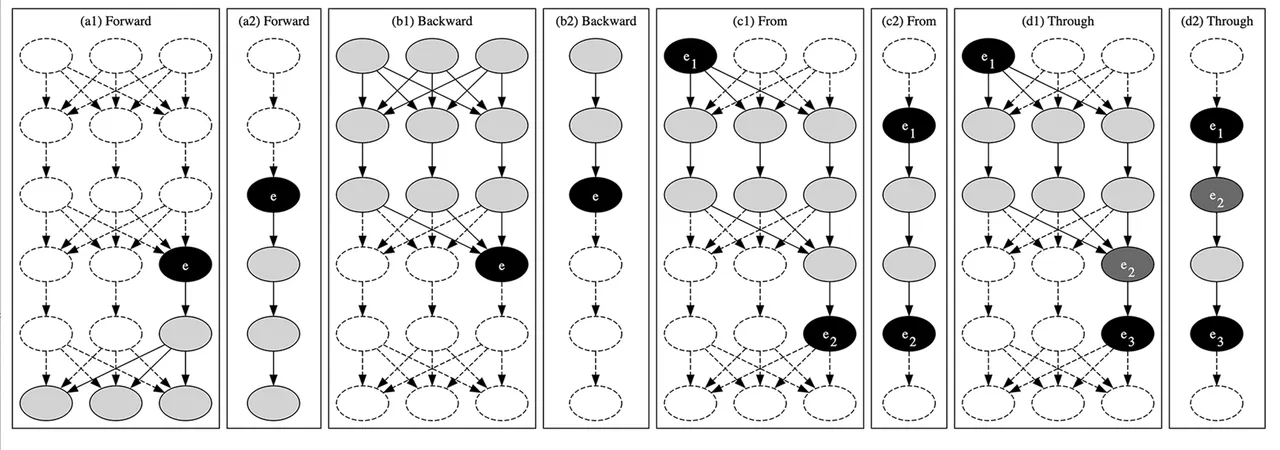
Determine 3: Queries of the reachability graph for the BasicErrorFlow mannequin
Attain Ahead and Backward
The primary two queries are pretty easy. Attain ahead queries ask, What mannequin components can this mannequin factor have an effect on? That’s, if we return to our conceptualization of the BasicErrorFlow mannequin as a sensor linked to a controller linked to an actuator, we would ask, The place can information readings produced by the sensor, or any instructions derived from them, go? Attain backward queries are related, however they as a substitute pose the query, What mannequin components can have an effect on this mannequin factor? Utilized to a real-world system, these queries may ask, What sensors and controllers produce info used to control this explicit actuator?
Determine 3 reveals graphically, in (a1) and (a2), instance ahead reachability queries on the reachability graphs: nominal in (a1), off-nominal in (a2). Equally, (b1) and (b2) present instance backward reachability queries. The factor used because the slicing criterion, i.e., the question origin, is proven in black and labeled with an e. The outcomes of the question are all shaded components—together with the question origin. Notably, the results of executing this question is a decreased portion of a system’s related reachability graph (particularly an induced subgraph). Not like a number of the different queries that return a easy sure/no-style outcome, these subgraphs aren’t more likely to be very helpful by themselves in automated analyses, and so they don’t lend themselves to, for instance, DevOps-style automated analysis. They’re more likely to be helpful, although, for both producing visible outcomes that may then be interpreted by a human, or as the primary stage in additional complicated, multi-stage queries.
Attain From
The third question sort is a kind of multi-stage queries, although it’s not terribly complicated. In attain from queries, we merely ask, Can this mannequin factor attain that one? We do that by first executing a ahead attain question from the primary factor (e1 in (c1) and (c2) in Determine 3) after which seeing if the second factor (e2) is contained within the ensuing subgraph. Figuring out whether or not info from a sensor, or instructions from a controller, can have an effect on a specific actuator is helpful, however this question actually shines when executed on the off-nominal reachability graph. Recall that it’s constructed utilizing a system’s structure (laid out in AADL) and details about what occurs when the system encounters errors (specified within the error-modeling extension to AADL known as EMV2). This design implies that attain from queries let modelers or automated analyses ask, Can an error from this system attain that one, or is it by some means stopped?
Attain By
The fourth and ultimate foundational question sort solutions questions of the shape, Do all paths from this mannequin factor which attain that one undergo some explicit intermediate factor?
The utility of this question will not be instantly apparent, however think about two eventualities. The primary, from the security area, entails (a) a sensor that’s identified to sometimes produce jittery values, (b) a “checker” mannequin factor that may detect and discard these jittery readings, and (c) an actuator, which actuates in response to the sensor readings. We could need to verify that each one paths from the sensor (i.e., the origin, or e1 in (d1) and (d2) in Determine 3) to the actuator (e3) undergo the checker (e2)—hardly a easy process in a system the place there could also be a number of makes use of of the sensor’s information by a variety of completely different intermediate controllersor different system components.
In a second state of affairs from the area of data safety, some secret info have to be despatched throughout an untrusted community. To keep up secrecy, we should always encrypt the information earlier than broadcasting it. However how can we decide that there aren’t any “leaks,” i.e., that no system components processing or manipulating the key info can ship it straight or not directly to the broadcasting factor with out its first passing via the encryption module? We will use the attain via question, with the supply of the key info being the origin, the encryption module being the intermediate factor, and the broadcasting factor the goal.
Different Queries
From these 4 foundational queries, builders constructing automated analyses in OSATE can create extra complicated queries that finally can reply deep questions on a system. The utility of this strategy is one thing we explored in our analysis of the OSATE Slicer.
How Effectively Did We Do?
After creating the OSATE Slicer, we needed to guage each how helpful it’s and the way properly it performs. Generally, we have been happy with the outcomes of our work, although as at all times, there’s extra to be achieved.
How Helpful is the OSATE Slicer?
The primary place we used the slicer was within the Structure Supported Audit Processor (ASAP), an experimental automated security evaluation. ASAP had initially been created utilizing Awas, however sustaining that dependency proved difficult. We have been capable of exchange Awas with the Slicer in our implementation of ASAP. Doing so was comparatively easy; whereas most of our current implementation transferred seamlessly, we did have to write down one customized question (described additional in the paper).
The second place we used the OSATE Slicer is in an as but unpublished re-implementation of OSATE’s current Fault Impression Evaluation (described in, e.g., this paper by Larson et al.), which considers the place a specific factor’s fault or error can go (i.e., be propagated to) in a fully-specified system. This was trivial to reimplement utilizing the ahead slice question, after which—as a part of an ongoing analysis effort—we have been capable of take issues a step additional with a handful of customized queries to validate foundational assumptions a few system mannequin that have to be true for the evaluation’s outcomes to be legitimate.
Trying ahead, we’ve recognized two potential safety analyses that we’re occupied with updating to make use of the OSATE Slicer: an attack-tree calculator and a verifier that checks if a system meets the Bell-LaPadula safety coverage. Past that, there are different analyses that, at their core, discover properties of paths via a system. These can probably profit from the OSATE Slicer, although some are fairly complicated and should require extra options to be added to the Slicer.
How Quick is the OSATE Slicer?
Of their publication on Awas, Thiagarajan et al. analyzed a corpus of 11 system fashions written in AADL. We got down to run the OSATE Slicer on this identical corpus in order that we may evaluate the efficiency of the 2 instruments. Sadly, whereas lots of the fashions have been open-source, model info and different key specifics essential for reproducibility are usually not current of their publication. We have been capable of work straight with them (we owe them thanks for that) as a part of this effort to get entry to most of these fashions and specifics, although, and have made an archive of the corpus out there publicly as a part of this effort.

Determine 4: The efficiency of the OSATE Slicer relative to Awas, not the Y Axis is logarithmic
General, we discovered the efficiency of the Slicer to be fairly passable: we noticed a 10-100x speedup over Awas on the era and querying of practically all of the fashions within the corpus (see Determine 4). What’s extra, some attain via queries wouldn’t execute beneath Awas on two of the bigger fashions (denoted with ★ symbols within the determine), however we have been capable of run them with out problem utilizing our software.
Subsequent Steps: We’re In search of Collaborators!
We’re excited concerning the functions of the OSATE Slicer, each those we’ve recognized on this put up and people who we haven’t even considered but. To assist us out with these, we’re at all times on the lookout for individuals to collaborate with—do you’ve got system fashions that you just’d like to investigate extra simply or shortly? If that’s the case, please attain out. Since their inception, AADL and OSATE have been knowledgeable by the wants of DoD and industrial customers. The Slicer isn’t any completely different on this regard, and we welcome person ideas, suggestions, concepts, and collaborations to enhance the work.