The North Korean risk actor referred to as Kimsuky has been noticed focusing on analysis institutes in South Korea as a part of a spear-phishing marketing campaign with the last word purpose of distributing backdoors on compromised programs.
“The risk actor in the end makes use of a backdoor to steal data and execute instructions,” the AhnLab Safety Emergency Response Middle (ASEC) stated in an evaluation posted final week.
The assault chains start with an import declaration lure that is truly a malicious JSE file containing an obfuscated PowerShell script, a Base64-encoded payload, and a decoy PDF doc.
The subsequent stage entails opening the PDF file as a diversionary tactic, whereas the PowerShell script is executed within the background to launch the backdoor.
The malware, for its half, is configured to gather community data and different related information (i.e., host title, consumer title, and working system model) and transmit the encoded particulars to a distant server.
It is also able to working instructions, executing extra payloads, and terminating itself, turning it right into a backdoor for distant entry to the contaminated host.
Cracking the Code: Study How Cyber Attackers Exploit Human Psychology
Ever puzzled why social engineering is so efficient? Dive deep into the psychology of cyber attackers in our upcoming webinar.
Kimsuky, energetic since at the very least 2012, began off focusing on South Korean authorities entities, assume tanks, and people recognized as consultants in numerous fields, earlier than increasing its victimology footprint to embody Europe, Russia, and the U.S.
Earlier this month, the U.S. Treasury Division sanctioned Kimsuky for gathering intelligence to assist North Korea’s strategic goals, together with geopolitical occasions, overseas coverage, and diplomatic efforts.
“Kimsuky has centered its intelligence assortment actions on overseas coverage and nationwide safety points associated to the Korean peninsula, nuclear coverage, and sanctions,” cybersecurity agency ThreatMon famous in a current report.
The state-sponsored group has additionally been noticed leveraging booby-trapped URLs that, when clicked, obtain a bogus ZIP archive masquerading as an replace for the Chrome browser to deploy a malicious VBScript from Google Drive that employs the cloud storage as a conduit for information exfiltration and command-and-control (C2).
Lazarus Group Goes Phishing on Telegram
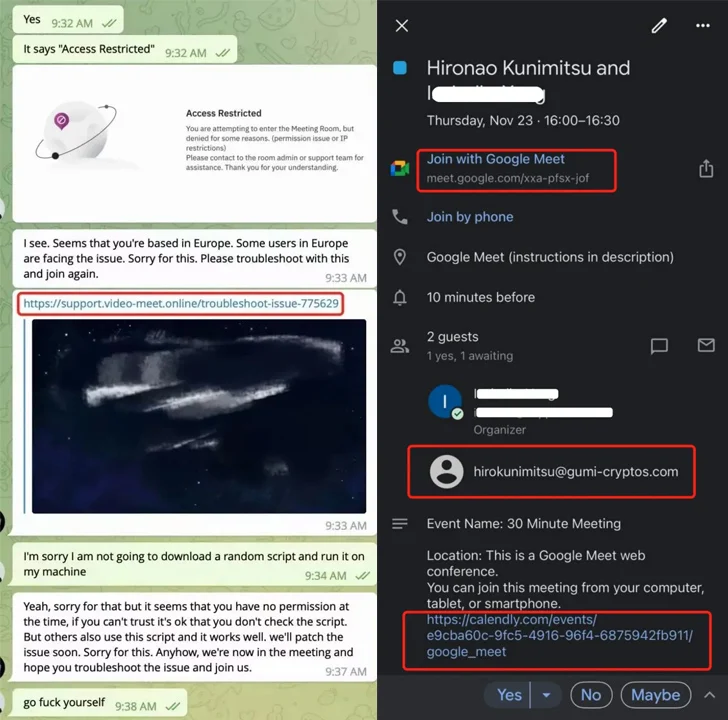
The event comes as blockchain safety firm SlowMist implicated the infamous North Korea-backed outfit known as the Lazarus Group in a widespread phishing marketing campaign on Telegram focusing on the cryptocurrency sector.
“Extra just lately, these hackers have escalated their ways by posing as respected funding establishments to execute phishing scams in opposition to numerous cryptocurrency challenge groups,” the Singapore-based agency stated.
After establishing rapport, the targets are deceived into downloading a malicious script below the guise of sharing an internet assembly hyperlink that facilitates crypto theft.
It additionally follows a report from the Seoul Metropolitan Police Company (SMPA) that accused the Lazarus sub-cluster codenamed Andariel of stealing technical details about anti-aircraft weapon programs from home protection corporations and laundering ransomware proceeds again to North Korea.
It’s estimated that greater than 250 information amounting to 1.2 terabytes have been stolen within the assaults. To cowl up the tracks, the adversary is alleged to have used servers from an area firm that “rents servers to subscribers with unclear identities” as an entry level.
As well as, the group extorted 470 million gained ($356,000) value of bitcoin from three South Korean corporations in ransomware assaults and laundered them by way of digital asset exchanges reminiscent of Bithumb and Binance. It is value noting that Andariel has been linked to the deployment of Maui ransomware up to now.