The United Parcel Service (UPS) says fraudsters have been harvesting cellphone numbers and different info from its on-line cargo monitoring software in Canada to ship extremely focused SMS phishing (a.okay.a. “smishing”) messages that spoofed UPS and different high manufacturers. The missives addressed recipients by title, included particulars about current orders, and warned that these orders wouldn’t be shipped until the client paid an added supply price.
In a snail mail letter despatched this month to Canadian clients, UPS Canada Ltd. stated it’s conscious that some package deal recipients have acquired fraudulent textual content messages demanding cost earlier than a package deal will be delivered, and that it has been working with companions in its supply chain to attempt to perceive how the fraud was occurring.
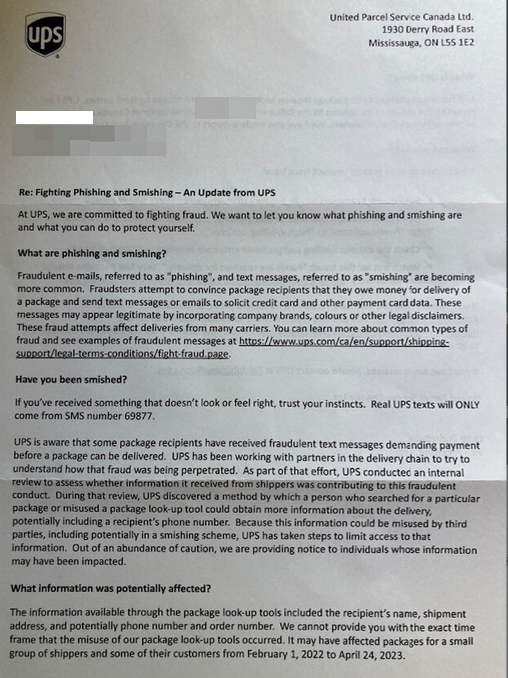
The current letter from UPS about SMS phishers harvesting cargo particulars and cellphone numbers from its web site.
“Throughout that evaluation, UPS found a way by which an individual who looked for a selected package deal or misused a package deal look-up software may receive extra details about the supply, doubtlessly together with a recipient’s cellphone quantity,” the letter reads. “As a result of this info might be misused by third events, together with doubtlessly in a smishing scheme, UPS has taken steps to restrict entry to that info.”
The written discover goes on to say UPS believes the information publicity “affected packages for a small group of shippers and a few of their clients from February 1, 2022 to April 24, 2023.”
As early as April 2022, KrebsOnSecurity started receiving ideas from Canadian readers who have been puzzling over why they’d simply acquired certainly one of these SMS phishing messages that referenced info from a current order they’d legitimately positioned at a web-based retailer.
In March, 2023, a reader named Dylan from British Columbia wrote in to say he’d acquired certainly one of these transport price rip-off messages not lengthy after putting an order to purchase gobs of constructing blocks instantly from Lego.com. The message included his full title, cellphone quantity, and postal code, and urged him to click on a hyperlink to mydeliveryfee-ups[.]information and pay a $1.55 supply price that was supposedly required to ship his Legos.
“From looking out the textual content of this phishing message, I can see that lots of people have skilled this rip-off, which is extra convincing due to the knowledge the phishing textual content incorporates,” Dylan wrote. “It appears more likely to me that UPS is leaking info by some means about upcoming deliveries.”
Josh is a reader who works for a corporation that ships merchandise to Canada, and in early January 2023 he inquired whether or not there was any details about a breach at UPS Canada.
“We’ve seen a lot of our clients focused with a fraudulent UPS textual content message scheme after putting an order,” Josh stated. “A hyperlink is supplied (usually solely after the client responds to the textual content) which takes you to a captcha web page, adopted by a fraudulent cost assortment web page.”
Pivoting on the area within the smishing message despatched to Dylan reveals the phishing area shared an Web host in Russia [91.215.85-166] with almost two dozen different smishing associated domains, together with upsdelivery[.]information, legodelivery[.]information, adidascanadaltd[.]com, crocscanadafee[.]information, refw0234apple[.]information, vista-printcanada[.]information and telus-ca[.]information.
The inclusion of big-name manufacturers within the domains of those UPS smishing campaigns suggests the perpetrators had the flexibility to focus their lookups on UPS clients who had not too long ago ordered gadgets from particular firms.
Makes an attempt to go to these domains with an internet browser failed, however loading them in a cellular system (or in my case, emulating a cellular system utilizing a digital machine and Developer Instruments in Firefox) revealed the primary stage of this smishing assault. As Josh talked about, what first popped up was a CAPTCHA; after the customer solved the CAPTCHA, they have been taken by means of a number of extra pages that requested the consumer’s full title, date of start, bank card quantity, deal with, e-mail and cellphone quantity.
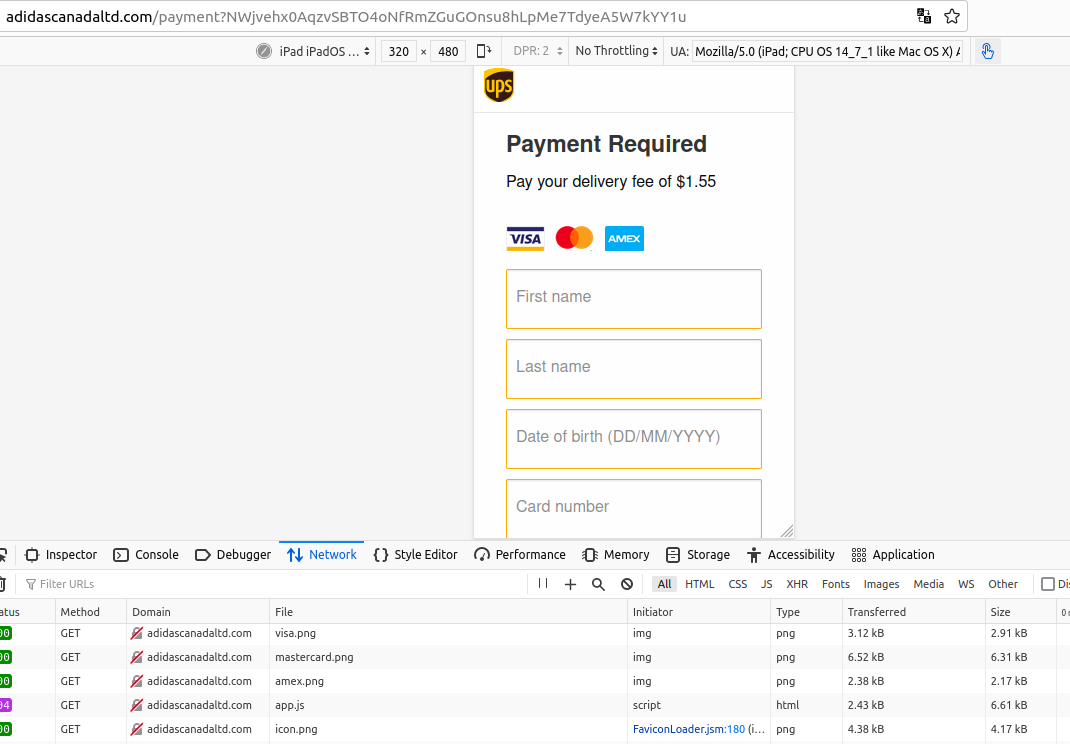
A smishing web site focusing on Canadians who not too long ago bought from Adidas on-line. The positioning would solely load in a cellular browser.
In April 2022, KrebsOnSecurity heard from Alex, the CEO of a know-how firm in Canada who requested to depart his final title out of this story. Alex reached out when he started receiving the smishing messages virtually instantly after ordering two units of Airpods instantly from Apple’s web site.
What puzzled Alex most was that he’d instructed Apple to ship the Airpods as a present to 2 completely different individuals, and fewer than 24 hours later the cellphone quantity he makes use of for his Apple account acquired two of the phishing messages, each of which contained salutations that included the names of the individuals for whom he’d purchased Airpods.
“I’d put the recipient as completely different individuals on my workforce, however as a result of it was my cellphone quantity on each orders I used to be the one getting the texts,” Alex defined. “That very same day, I obtained textual content messages referring to me as two completely different individuals, neither of whom have been me.”
Alex stated he believes UPS Canada both doesn’t absolutely perceive what occurred but, or it’s being coy about what it is aware of. He stated the wording of UPS’s response misleadingly suggests the smishing assaults have been by some means the results of hackers randomly wanting up package deal info through the corporate’s monitoring web site.
Alex stated it’s seemingly that whoever is accountable found out tips on how to question the UPS Canada web site for less than pending orders from particular manufacturers, maybe by exploiting some kind of utility programming interface (API) that UPS Canada makes or made out there to its greatest retail companions.
“It wasn’t like I put the order by means of [on Apple.ca] and a few days or perhaps weeks later I obtained a focused smishing assault,” he stated. “It was kind of the identical day. And it was as if [the phishers] have been being notified the order existed.”
The letter to UPS Canada clients doesn’t point out whether or not every other clients in North America have been affected, and it stays unclear whether or not any UPS clients exterior of Canada might have been focused.
In a press release supplied to KrebsOnSecurity, Sandy Springs, Ga. primarily based UPS [NYSE:UPS] stated the corporate has been working with companions within the supply chain to know how that fraud was being perpetrated, in addition to with legislation enforcement and third-party specialists to determine the reason for this scheme and to place a cease to it.
“Legislation enforcement has indicated that there was a rise in smishing impacting numerous shippers and many various industries,” reads an e-mail from Brian Hughes, director of monetary and technique communications at UPS.
“Out of an abundance of warning, UPS is sending privateness incident notification letters to people in Canada whose info might have been impacted,” Hughes stated. “We encourage our clients and basic customers to study in regards to the methods they’ll keep protected towards makes an attempt like this by visiting the UPS Struggle Fraud web site.”

