Our core mission within the NOC is community resilience. We additionally present built-in safety, visibility and automation, a SOC contained in the NOC.
In half one, we coated:
- Designing the Black Hat Community, by Evan Basta
- AP Placement Planning, by Sandro Fasser
- Wi-Fi Air Marshal, by Jérémy Couture, Head of SOC, Paris 2024 Olympic Video games
- Meraki Dashboards, by Rossi Rosario Burgos
- Meraki Methods Supervisor, by Paul Fidler
- A Higher Solution to Design Coaching SSIDs/VLANs, by Paul Fidler
Partly two, we’re going deep with safety:
- Integrating Safety
- First Time at Black Hat, by Jérémy Couture, Head of SOC, Paris 2024 Olympic Video games
- Trojan on an Attendee Laptop computer, by Ryan MacLennan
- Automated Account Provisioning, by Adi Sankar
- Integrating Meraki Scanning Information with Umbrella Safety Occasions, by Christian Clasen
- Area Title Service Statistics, by Adi Sankar
Integrating Safety
Because the wants of Black Hat advanced, so did the Cisco Safe Applied sciences within the NOC:
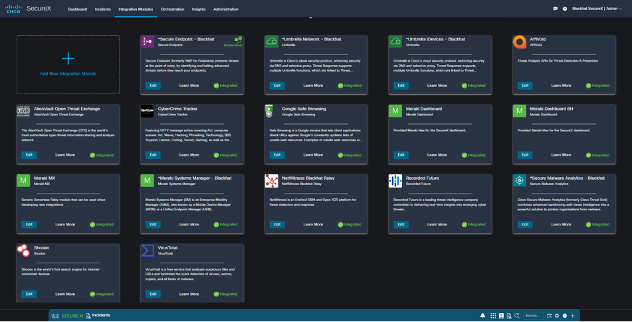
The SecureX dashboard made it straightforward to see the standing of every of the related Cisco Safe applied sciences.

Since becoming a member of the Black Hat NOC in 2016, my purpose stays integration and automation. As a NOC crew comprised of many applied sciences and firms, we’re happy that this Black Hat NOC was probably the most built-in thus far, to supply an total SOC cybersecurity structure answer.

Now we have concepts for much more integrations for Black Hat Asia and Black Hat USA 2023. Thanks, Piotr Jarzynka, for designing the mixing diagram.
Beneath are the SecureX menace response integrations for Black Hat Europe, empowering analysts to research Indicators of Compromise in a short time, with one search.
The unique Black Hat NOC integration for Cisco was NetWitness sending suspicious recordsdata to Menace Grid (know Safe Malware Analytics). We expanded that in 2022 with Palo Alto Networks Cortex XSOAR and used it in London, for investigation of malicious payload assault.
NetWitness noticed a focused assault towards the Black Hat community. The assault was meant to compromise the community.
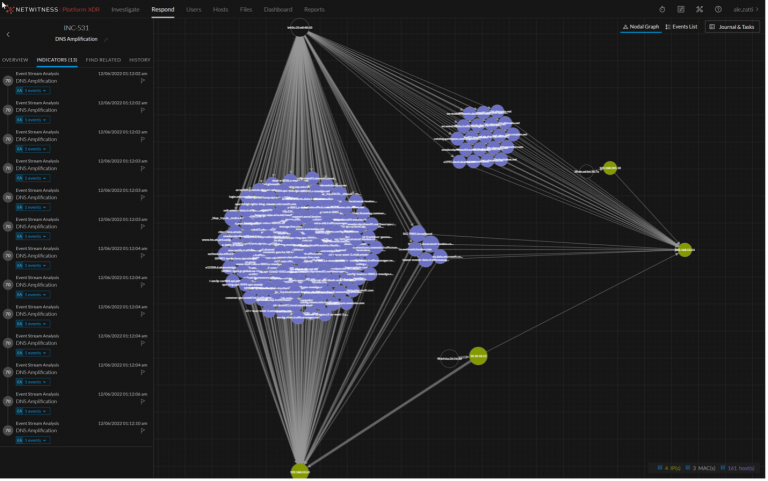
NetWitness extracted the payload and despatched it to Safe Malware Analytics for detonation.
Reviewing the evaluation report, we had been capable of rapidly decide it was the MyDoom worm, which might have been very damaging.
The assault was blocked on the perimeter and the analysts had been capable of monitor and enrich the incident in XSOAR.
First Time at Black Hat, by Jérémy Couture, Head of SOC, Paris 2024 Olympic Video games
My first time at Black Hat turned out to be an unimaginable journey!
Due to the cybersecurity partnership between Paris 2024 and Cisco, I used to be capable of combine into the Cisco Crew, to function the NOC/SOC as a Menace Hunter on probably the most harmful community on the planet for this European Version of Black Hat.
My first day, I helped with deploying the community by putting in the wi-fi Meraki APs on the venue, understanding how they had been configured and the way they may assist analysts to establish and find any shopper related to the community that might have a foul habits in the course of the occasion, the thought being to guard the attendees if an assault was to spray on the community.

Following this “bodily” deployment, I’ve been capable of entry the entire Cisco Safe setting together with Meraki, Safe Malware Analytics, Umbrella, SecureX and the opposite Black Hat NOC companions software program instruments.
SecureX was undoubtedly the product on which I needed to step up. By having so implausible professionals round me, we had been capable of dig within the product, figuring out potential use circumstances to deploy within the orchestration module and anticipated integrations for Paris 2024.

Time was flying and so had been the attendees to the convention, a community with out person is enjoyable however will be fairly boring as nothing occurs, having so many cybersecurity skilled on the identical place testing totally different safety malwares, assaults and so forth led us to very attention-grabbing investigations. A paradox on the Black Hat, we don’t need to block malicious content material because it might be a part of workout routines or coaching lessons, fairly a unique mindset as what we, safety defenders, are used to! Utilizing the totally different elements, we had been capable of finding some observables/IOCs that we examine by way of SecureX, SecureX being related to all the opposite elements helped us to counterpoint the observables (IPs, urls, domains…), understanding the criticality of what we recognized (akin to malware payloads) and even led us to poke the oldsters within the coaching lessons to allow them to know that one thing actually flawed was occurring on their gadgets.

Being a part of the Black Hat NOC was an unimaginable expertise, I used to be capable of meet implausible professionals, totally dedicated on making the occasion a hit for all attendees and exhibitors. It additionally helped me to raised perceive how merchandise, that we use or will use inside Paris 2024, might be leveraged to our wants and which indicators might be added to our numerous Dashboards, serving to us to establish, instantaneously, that one thing is going on.
Trojan on an Attendee Laptop computer, by Ryan MacLennan
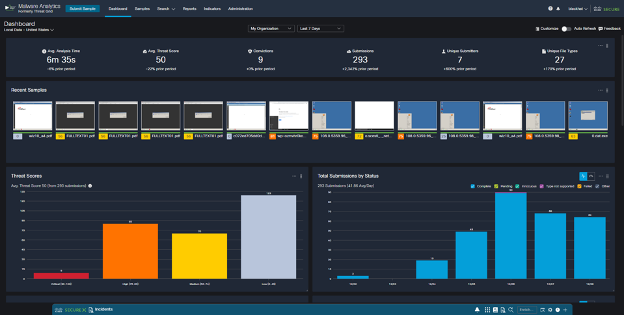
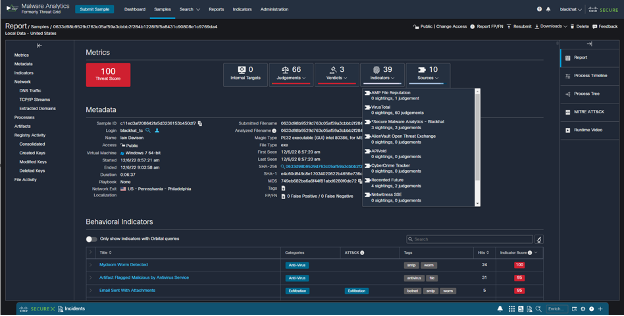
Over the last day of Black Hat Europe, our NOC companion, NetWitness noticed some recordsdata being downloaded on the community. The combination once more robotically carved out the file and submitted the Cisco Safe Malware Analytics (SMA) platform. A kind of recordsdata got here again as a trojan, after SMA detonated the file in a sandbox setting. The precise hash is the beneath SHA-256:
938635a0ceed453dc8ff60eab20c5d168a882bdd41792e5c5056cc960ebef575
The screenshot beneath exhibits among the behaviors that influenced the choice:

The results of seeing these behaviors induced SMA to provide it the very best judgement rating obtainable to a detonated file:

After this judgement was made, we related with the Palo Alto Networks crew, and so they discovered the IP handle related to the file obtain.
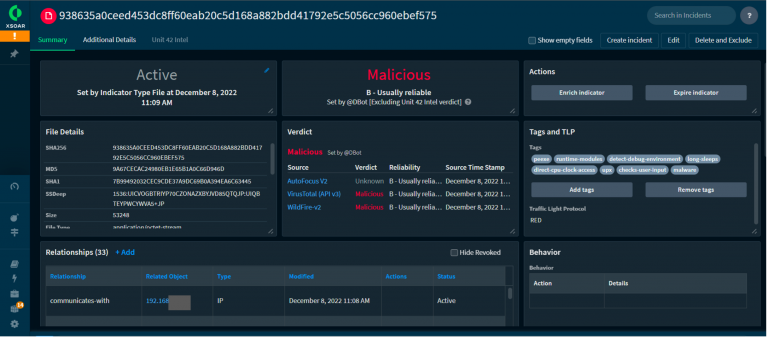
As soon as we had this info, we went to the Meraki dashboard and did a seek for the IP handle. The search returned just one shopper that has been related to the handle for the complete Black Hat convention.

Realizing that there has solely been one shopper related to the handle made discovering the attendee simpler. We then wanted to know the place they had been and Meraki had this discovered. After opening the shopper’s profile, we noticed what SSID and entry level (AP) they had been related to utilizing the Meraki location map.

We then discovered the attendee and allow them to know to have their IT examine their laptop computer to verify it’s clear.
Other than the technical challenges of working a brief community for N thousand folks, the Black Hat occasion reminded us that success doesn’t occur with out teamwork; that management isn’t nearly conserving the mission on monitor. It is usually about taking care of the crew and that small particulars in planning, construct up and tear down will be simply as necessary, as having all the appropriate instruments and beautifully expert People utilizing them in the course of the occasion itself.
Automated Account Provisioning, by Adi Sankar
Within the Cisco Safe know-how stack, inside the Black Hat NOC, we use SecureX Single Signal-on. This reduces the confusion of managing a number of accounts and passwords. It additionally streamlines the integrations between the Cisco merchandise and our fellow NOC companions. Now we have an open ecosystem strategy to integrations and entry within the NOC, so we are going to provision Cisco Safe accounts for any workers member of the NOC. Logging into every particular person console and creating an account is time consuming and might usually result in confusion on which instruments to provision and which permission ranges are wanted.
To automate this course of, I developed two workflows: one to create non-admin customers for NOC companions and one to create administrator accounts in all of the instruments for Cisco workers. The workflows create accounts in SecureX, Safe Malware Analytics (Menace Grid), Umbrella DNS and Meraki dashboard, all utilizing SecureX Single Signal-On.
Here’s what the workflow appears like for creating non-admin customers.
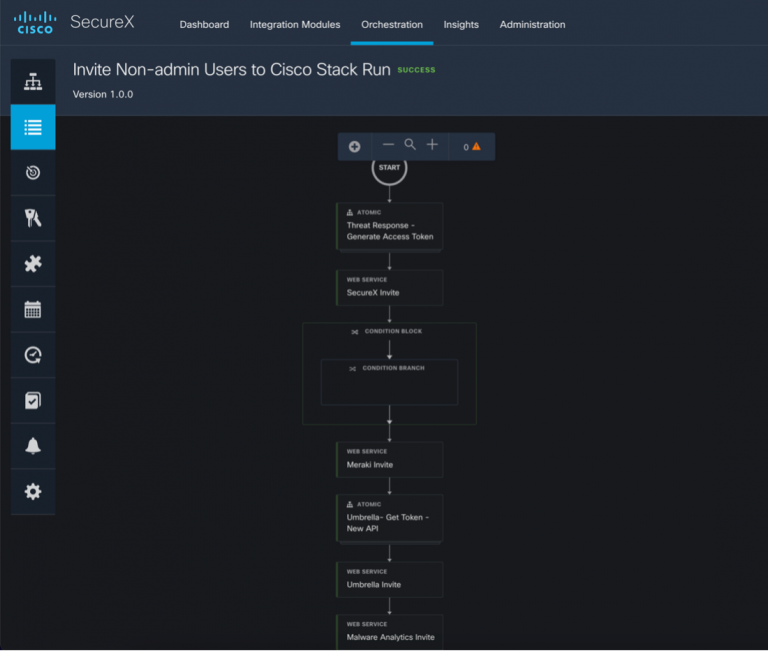
The workflow requires three inputs: first identify, final identify, and e mail. Click on Run.

The sequence of API calls is as follows:
- Generate a SecureX token to entry the SecureX API together with the “admin/invite:write, invite:write” scopes.
- Invite the Consumer to SecureX utilizing the invite API (https://visibility.amp.cisco.com/iroh/invite/index.html#/). Within the physique of this POST the position is ready to “person”. Within the Administrator workflow this may be set to “admin” permitting full entry to SecureX.
- If the invite fails resulting from a reproduction invite, print an error message in Webex groups.
- Invite the person to the Meraki dashboard utilizing the “admins” API (https://api.meraki.com/api/v1/organizations/{organizationId}/admins). Within the physique of this name, the group entry is ready to none, and entry to 2 networks (Wi-fi community and Methods Supervisor) are set to “read-only” to make sure the person can not make any modifications to have an effect on the community. Within the Administrator model org entry remains to be set to none however “full” permissions are supplied to the 2 networks, one thing we are not looking for all customers to have.
- Generate a token to the brand new Umbrella API utilizing https://api.umbrella.com/auth/v2/token with the next scopes (learn admin customers, write admin customers, learn admin roles). This single endpoint for producing a token primarily based on scopes has made utilizing the Umbrella API considerably simpler.
- Then invite the person to Umbrella utilizing the “admins” API at (https://api.umbrella.com/admin/v2/customers) and within the physique of this POST the “position ID” is ready to 2 to make sure read-only permissions are provisioned for Umbrella.
- Create a person in Safe Malware analytics utilizing the API at (https://panacea.threatgrid.com/api/v3/organizations/<ORG_ID>/customers). The physique of this request merely creates a Malware Analytics login utilizing the customers final identify and appending “_blackhat”
- The final name is to ship a password reset e mail for the Malware Analytics person. (https://panacea.threatgrid.com/api/v3/customers/<LOGIN>/password-email) They will set their password through the e-mail, login to the Malware Analytics console after which hyperlink their SecureX sign-on account, which implies they are going to now not want to make use of their Malware Analytics credentials.

As soon as the workflow has accomplished efficiently, the person will obtain 4 emails to create a SecureX Signal-On account and settle for the invites to the varied merchandise. These workflows actually improved our responsiveness to account provisioning requests and makes it a lot simpler to collaborate with different NOC companions.
Integrating Meraki Scanning Information with Umbrella Safety Occasions, by Christian Clasen
Over the earlier Black Hat occasions, we’ve been using Meraki scanning information to get location information for particular person purchasers, as they roamed convention. Within the preliminary weblog submit (Black Hat Asia 2022), we created a Docker container to just accept the info from the Meraki Scanning API and reserve it for future evaluation. At Black Hat USA 2022, we wrote about the right way to use Python Folium to make use of the flat textual content recordsdata to generate chronological heatmaps that illustrated the density of purchasers all through the convention.
This time round, we’ve stepped it up once more by integrating Umbrella DNS Safety occasions and including the power to trace purchasers throughout the heatmap utilizing their native IP handle.

To enhance the portability of our information and the effectivity of our code, we started by shifting from flat JSON recordsdata to a correct database. We selected SQLite this time round, although going ahead we are going to seemingly use Mongo.
Each will be queried instantly into Python Pandas dataframes which is what’s going to give us the optimum efficiency we’re on the lookout for. Now we have a devoted Docker container (Meraki-Receiver) that can validate the incoming information stream from the Meraki dashboard and insert the values into the database.
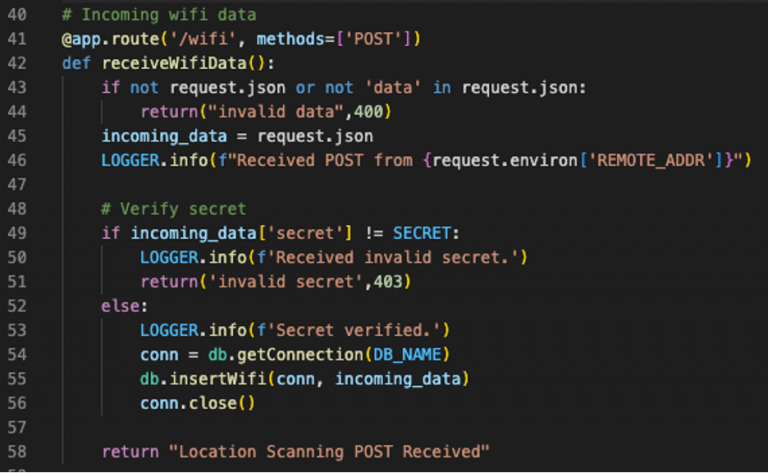
The database is saved on a Docker quantity that may be mounted by our second container, the Meraki-Mapper. Although this container’s major objective is constructing the heatmaps, it additionally performs the duty of retrieving and correlating Umbrella DNS safety occasions. That’s, any DNS question from the Black Hat community that matches certainly one of a number of predefined safety classes. Umbrella’s APIs had been not too long ago improved so as to add OAuth and simplify the URI scheme for every endpoint. After retrieving a token, we will get all safety occasions in the time-frame of the present heatmap with one name.
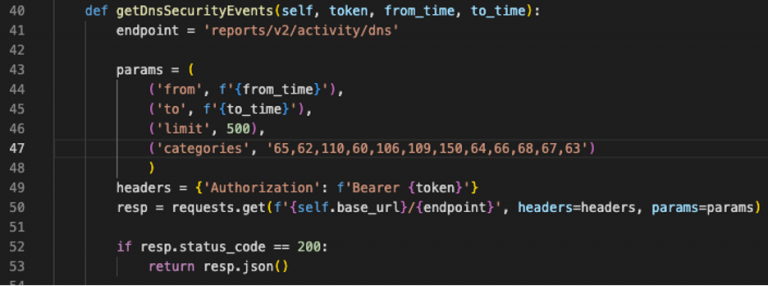
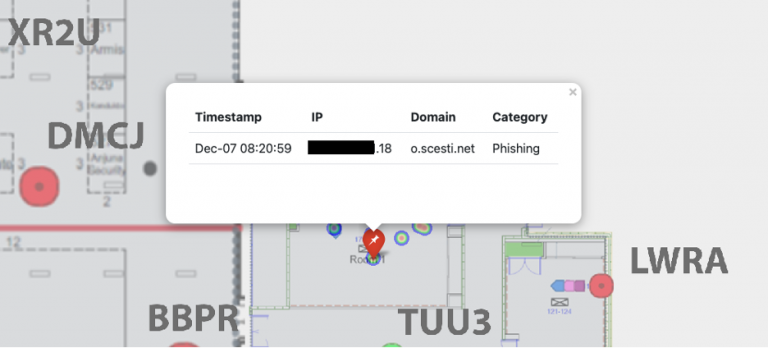
What we need to do with these occasions is to create Folium Markers. These are static “pins” that can sit on the map to point the place the DNS question originated from. Clicking on a marker will popup extra details about the question and the shopper who despatched it.
Due to the Umbrella Digital Home equipment within the Black Hat community, we’ve the interior IP handle of the shopper who despatched the DNS question. We even have the interior IP handle within the Meraki scanning information, together with the latitude and longitude. After changing the database question right into a Pandas dataframe, our logic takes the IP handle from the DNS question and finds all cases within the database of location information for that IP inside a 5-minute window (the decision of our heatmap).

What we find yourself with is an inventory of dictionaries representing the markers we need to add to the map. Utilizing Bootstrap, we will format the popup for every occasion to make it look a bit extra polished. Folium’s Popup plugin permits for an iFrame for every marker popup.

The result’s a shifting heatmap protecting a whole day on a given convention flooring, full with markers indicating safety occasions (the purple pushpin icon).
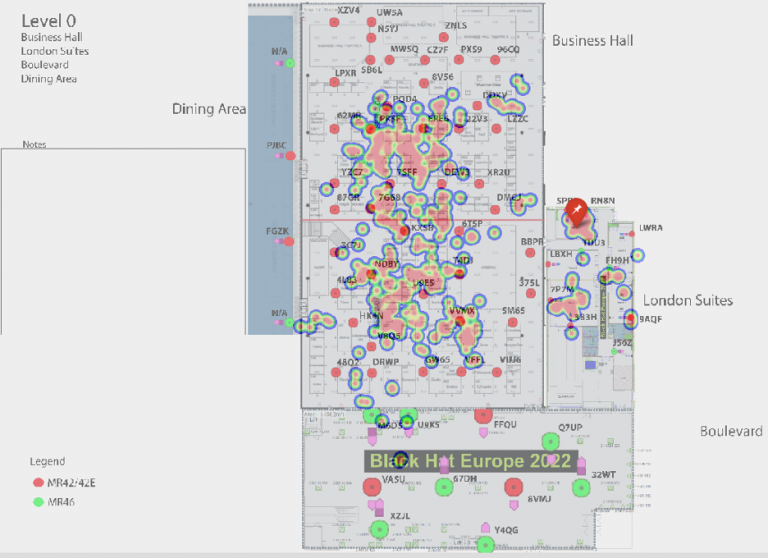
Clicking on the pushpin exhibits the small print of the question, permitting us within the NOC to see the precise location of the shopper once they despatched it.
To additional enhance this service in the course of the subsequent convention, we plan to implement an internet web page the place NOC workers can submit an IP handle and instantly get map monitoring that shopper by way of the convention flooring. This could give us an much more environment friendly method to discover and notify of us who’re both behaving maliciously or seem like contaminated.
Area Title Service Statistics, by Adi Sankar
For years we’ve been monitoring the DNS stats on the Blackhat conferences. The post-pandemic 2022 numbers seem like we by no means skipped a beat after the dip in DNS queries from 2021, seen within the bar graph beneath. This yr’s attendance noticed properly over 11 million complete DNS queries.

The Exercise quantity view from Umbrella provides a top-level degree look of exercise by class, which we will drill into for deeper menace searching. On pattern with the earlier Black Hat Europe occasions, the highest Safety classes had been Dynamic DNS and Newly Seen Domains. Nonetheless, it’s value noting a proportionally bigger improve within the cryptomining and phishing classes from 9 to 17 and 28 to 73, respectively, in comparison with final yr.

These years, Black Hat noticed over 4,100 apps hook up with the community, which is almost double of what was seen final yr. Nonetheless, nonetheless not topping over 6,100 apps seen at Black Hat USA early this yr.

Ought to the necessity come up, we will block any software, akin to Mail.ru above.

Black Hat Europe 2022 was the perfect deliberate and executed NOC in my expertise, with probably the most integrations and visibility. This allowed us the time to cope with issues, which is able to at all times come up.
We’re very pleased with the collaboration of the crew and the NOC companions.
Black Hat Asia shall be in Might 2023, on the Marina Bay Sands, Singapore…hope to see you there!
Acknowledgments
Thanks to the Cisco NOC crew:
- Cisco Safe: Ian Redden, Christian Clasen, Aditya Sankar, Ryan MacLennan, Guillaume Buisson, Jerome Schneider, Robert Taylor, Piotr Jarzynka, Tim Wadhwa-Brown and Matthieu Sprunck
- Menace Hunter / Paris 2024 Olympics SOC: Jérémy Couture
- Meraki Community: Evan Basta, Sandro Fasser, Rossi Rosario Burgos, Otis Ioannou, Asmae Boutkhil, Jeffry Handal and Aleksandar Dimitrov Vladimirov
- Meraki Methods Supervisor: Paul Fidler
Additionally, to our NOC companions NetWitness (particularly David Glover, Iain Davidson, Alessandro Contini and Alessandro Zatti), Palo Alto Networks (particularly James Holland, Matt Ford, Matt Smith and Mathew Chase), Gigamon, IronNet, and the complete Black Hat / Informa Tech workers (particularly Grifter ‘Neil Wyler’, Bart Stump, Steve Fink, James Pope, Jess Stafford and Steve Oldenbourg).

About Black Hat
For 25 years, Black Hat has supplied attendees with the very newest in info safety analysis, improvement, and tendencies. These high-profile world occasions and trainings are pushed by the wants of the safety neighborhood, striving to convey collectively the perfect minds within the business. Black Hat evokes professionals in any respect profession ranges, encouraging progress and collaboration amongst academia, world-class researchers, and leaders in the private and non-private sectors. Black Hat Briefings and Trainings are held yearly in the US, Europe and USA. Extra info is on the market at: blackhat.com. Black Hat is dropped at you by Informa Tech.
We’d love to listen to what you suppose. Ask a Query, Remark Beneath, and Keep Related with Cisco Safe on social!
Cisco Safe Social Channels
Share:


