Most firms have robust exterior safety, e.g. blocking all entry to manufacturing property utilizing a firewall, and requiring a VPN to get “inside” entry to manufacturing environments. Nonetheless, as soon as you might be related to the VPN, the interior methods are normally very poorly protected, and there’s little to no authentication and authorization for inner instruments and providers.
Two frequent threats to inner safety are compromised worker laptops and provide chain assaults. In these eventualities, the attacker operates behind the firewall, usually with unrestricted community entry.
Providers with an internet ui could be secured utilizing an software load balancer, e.g. an AWS ALB with OIDC, however how do you defend entry to command line interface (CLI) primarily based instruments? Requiring a username and password for each CLI invocation makes it painful to make use of and storing the credentials on the system leaves them large open in case the pc they reside on is compromised.
The Command Line
Most inner instruments have a CLI to handle the providers which are used inside the firm and lots of are poorly protected. What’s one of the best ways to authorize CLIs? And how are you going to tie authorization into the corporate’s SSO?
One possibility is to deploy Hashicorp Vault, however that’s numerous setup and upkeep, so except you’ve got a group to function it, Vault won’t be a superb match.
An alternative choice is the OAuth2 system authorization grant (RFC8628), which is what this weblog submit will present you use.
The OAuth 2.0 system authorization grant is designed for Web-connected units that both lack a browser to carry out a user-agent-based authorization or are enter constrained to the extent that requiring the person to enter textual content with the intention to authenticate in the course of the authorization stream is impractical. It allows OAuth shoppers on such units (like good TVs, media consoles, digital image frames, and printers) to acquire person authorization to entry protected sources by utilizing a person agent on a separate system.
In case you ever used the AWS CLI with Single SignOn, that is what it does.
OAuth2 Gadget Movement
The Gadget Authorization Movement comprises two totally different paths; one happens on the system requesting authorization (the CLI) and the opposite happens in a browser. The browser stream path, whereby a tool code is sure to the session within the browser, happens as a parallel path half within the system stream path.

Implementing the OAuth Gadget Movement
Now we’ll take a look at what the above sequence diagram seems to be like when it’s carried out.
The interior CLI software at Rockset known as rsctl and is written in go. Step one is to provoke the system stream to get a JWT entry token.
$ rsctl login
Trying to robotically open the SSO authorization web page in your default browser.
If the browser doesn't open otherwise you want to use a distinct system to authorize this request, open the next URL:
https://rockset.auth0.com/activate?user_code=BBLF-JCWB
Then enter the code:
BBLF-JCWB
Efficiently logged in!
If you’re utilizing the CLI after logging in to a different pc, e.g. ssh:ing to a Linux server, and you utilize macOS, you possibly can configure iTerm to robotically open the hyperlink utilizing a “Run command” set off.
The web page that the hyperlink takes you to seems to be like this:
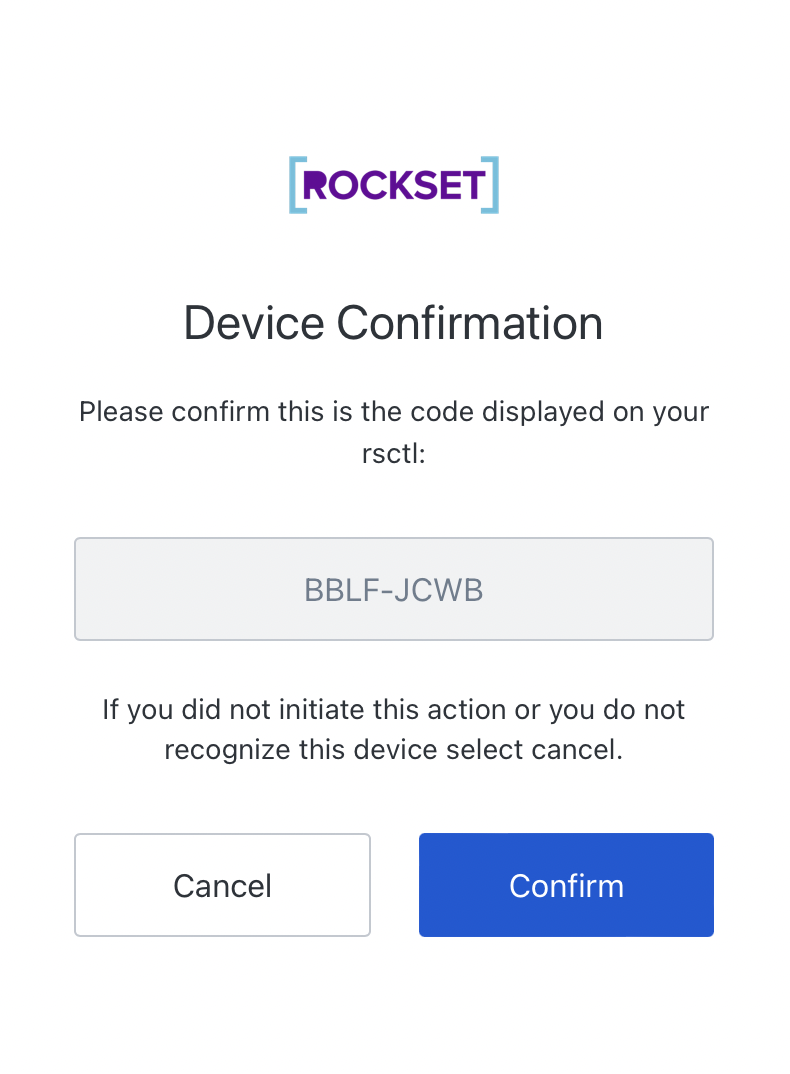
Upon getting confirmed that the “person code” is right (matches with what the CLI exhibits), and also you click on “Affirm”, it should take you thru the traditional OAuth2 login process (which in our case requires a username, password and {hardware} token).
As soon as the authentication is accomplished, you may be redirected and offered with a dialog just like the one under, and you may shut the browser window.
The CLI has now obtained a jwt entry token which is legitimate for plenty of hours and is used to authenticate through inner providers. The token could be cached on disk and reused between CLI invocations in the course of its lifetime.
If you difficulty a brand new rsctl command, it should learn the cached Entry Token from disk, and use it to authenticate with the interior APIs.
Underneath the Hood
We have now carried out and open sourced a go module to carry out the system authorization stream (github.com/rockset/device-authorization). It helps each Auth0 and Okta as OAuth suppliers.
Pattern Code
The next code is out there within the instance listing within the git repository.
Embedded content material: https://gist.github.com/pmenglund/5ed2708cdb88b6a6982258aed59a0899
We now have a JWT token, which can be utilized to authenticate REST calls by setting the Authorization header to Bearer: <jwt entry token>
Embedded content material: https://gist.github.com/pmenglund/b2ac7bb15ce25755a69573f5a063cb14
It’s now as much as the receiving finish to validate the bearer token, which could be executed utilizing an AWS ALB with OIDC authentication or a supplier particular API from the API server.
Offline Validation
An alternative choice for entry token validation is “offline validation”. In offline validation, the API server will get the general public key used to signal the JWT token from the supplier (and caches the general public key) and performs the validation within the API server, as an alternative of constructing a validation request to the supplier.
Residual Danger
One factor this doesn’t defend in opposition to is an attacker with a foothold on the pc that executes the CLI. They will simply wait till the person has accomplished the authentication, and they’re going to then have the ability to act because the person in the course of the entry token.
To mitigate this threat, you possibly can require a one time password (OTP), e.g. a Yubikey, each time the person performs a privileged motion.
$ rsctl delete useful resource foobar
please enter yubikey OTP: ccccccvfbbcddjtuehgnfrbtublkuufbgeebklrubkhf
useful resource foobar deleted
Closing Ideas
On this weblog, we’ve got proven how we constructed and open-sourced a go module to safe the Command Line Interface (CLI) utilizing an OAuth2 system authorization stream that helps each Auth0 and Okta SSO suppliers. You possibly can add this go module to your inner instruments and scale back inner safety threats.