Journey companies have emerged because the goal of a hack-for-hire group dubbed Evilnum as a part of a broader marketing campaign aimed toward authorized and monetary funding establishments within the Center East and Europe.
The assaults concentrating on legislation companies all through 2020 and 2021 concerned a revamped variant of a malware referred to as Janicab that leverages a lot of public providers like YouTube as lifeless drop resolvers, Kaspersky stated in a technical report printed this week.
Janicab infections comprise a various set of victims situated in Egypt, Georgia, Saudi Arabia, the UAE, and the U.Ok. The event marks the primary time authorized organizations in Saudi Arabia have been focused by this group.
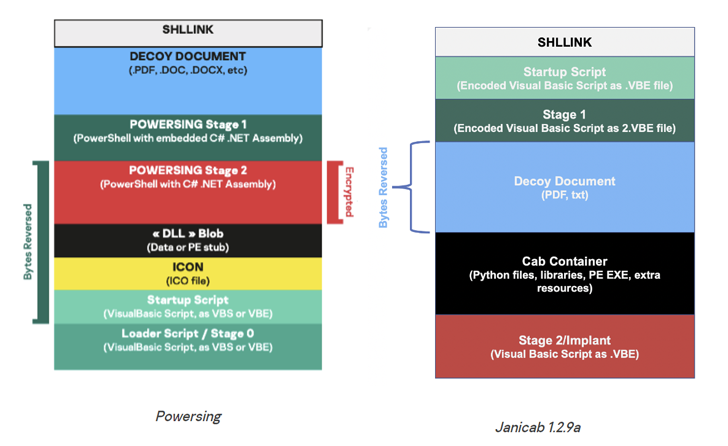
Additionally tracked as DeathStalker, the risk actor is thought to deploy backdoors like Janicab, Evilnum, Powersing, and PowerPepper to exfiltrate confidential company data.
“Their curiosity in gathering delicate enterprise data leads us to imagine that DeathStalker is a gaggle of mercenaries providing hacking-for-hire providers, or appearing as some form of data dealer in monetary circles,” the Russian cybersecurity firm famous in August 2020.
In line with ESET, the hacking crew has a sample of harvesting inner firm shows, software program licenses, e-mail credentials, and paperwork containing buyer lists, investments and buying and selling operations.
Earlier this yr, Zscaler and Proofpoint uncovered contemporary assaults orchestrated by Evilnum which were directed towards corporations within the crypto and fintech verticals since late 2021.
Kaspersky’s evaluation of the DeathStalker intrusions has revealed using an LNK-based dropper embedded inside a ZIP archive for preliminary entry by the use of a spear-phishing assault.
The lure attachment purports to be a company profile doc associated to energy hydraulics that, when opened, results in the deployment of the VBScript-based Janicab implant, which is able to command execution and deploying extra instruments.
Newer variations of the modular malware have concurrently eliminated audio recording options and added a keylogger module that shares overlaps with prior Powersing assaults. Different capabilities embody checking for put in antivirus merchandise and getting a listing of processes indicating malware evaluation.
The 2021 assaults are additionally notable for using unlisted previous YouTube hyperlinks which might be used to host an encoded string that is deciphered by Janicab to extract the command-and-control (C2) IP deal with for retrieving follow-on instructions and exfiltrating information.
“For the reason that risk actor makes use of unlisted previous YouTube hyperlinks, the probability of discovering the related hyperlinks on YouTube is nearly zero,” the researchers stated. “This additionally successfully permits the risk actor to reuse C2 infrastructure.”
The findings underscore that the risk actor has continued to replace its malware toolset to take care of stealthiness over prolonged intervals of time.
Moreover software allowlisting and working system hardening, organizations are really helpful to observe Web Explorer processes, for the reason that browser is utilized in hidden mode to speak with the C2 server.
As authorized and monetary sectors are a typical goal for the risk actor, the researchers additional theorized that DeathStalker’s clients and operators might be weaponizing the intrusions to maintain tabs on lawsuits, blackmail high-profile people, monitor monetary belongings, and harvest enterprise intelligence about potential mergers and acquisitions.