For greater than a decade, reminiscence security vulnerabilities have persistently represented greater than 65% of vulnerabilities throughout merchandise, and throughout the {industry}. On Android, we’re now seeing one thing completely different – a major drop in reminiscence security vulnerabilities and an related drop within the severity of our vulnerabilities.
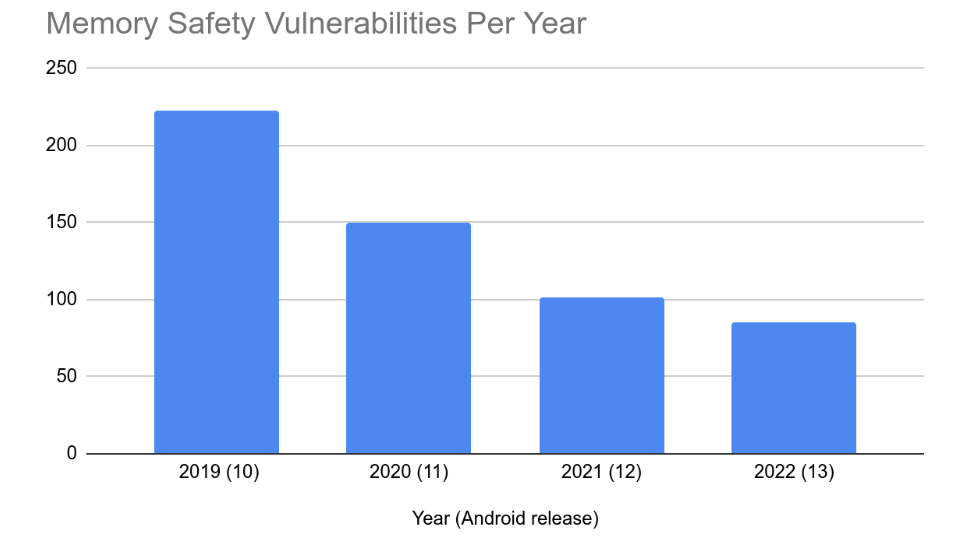
vulnerabilities reported within the Android safety bulletin, which incorporates important/excessive severity vulnerabilities reported by means of our vulnerability rewards program (VRP) and vulnerabilities reported internally, we see that the variety of reminiscence security vulnerabilities have dropped significantly over the previous few years/releases. From 2019 to 2022 the annual variety of reminiscence security vulnerabilities dropped from 223 right down to 85.
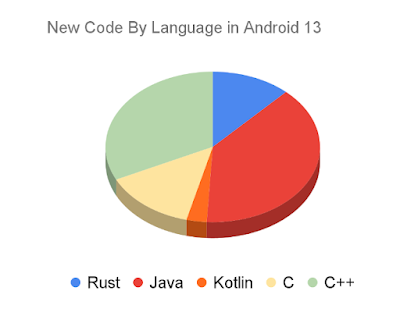
This drop coincides with a shift in programming language utilization away from reminiscence unsafe languages. Android 13 is the primary Android launch the place a majority of recent code added to the discharge is in a reminiscence secure language.
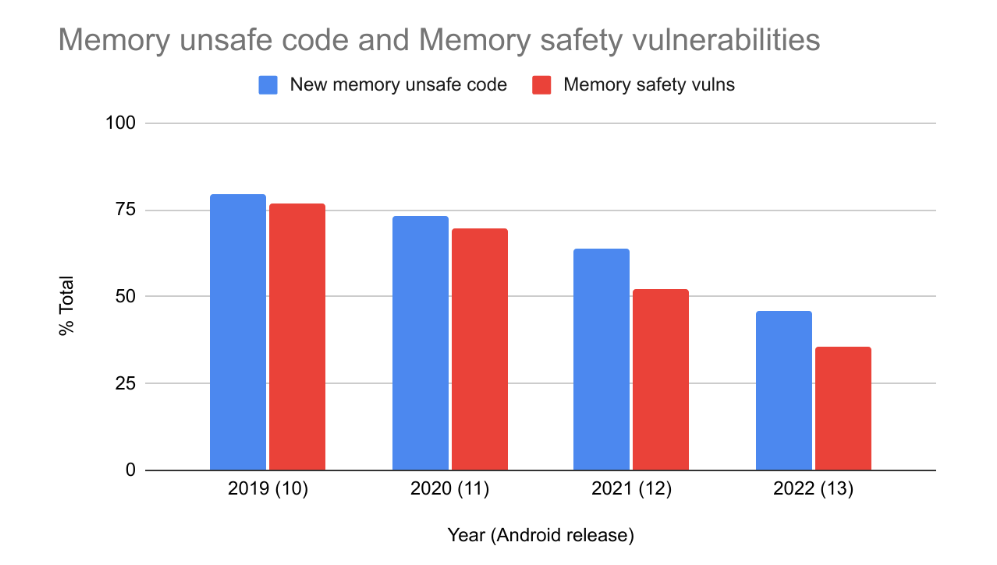
As the quantity of recent memory-unsafe code coming into Android has decreased, so too has the variety of reminiscence security vulnerabilities. From 2019 to 2022 it has dropped from 76% right down to 35% of Android’s complete vulnerabilities. 2022 is the primary 12 months the place reminiscence security vulnerabilities don’t characterize a majority of Android’s vulnerabilities.
Whereas correlation doesn’t essentially imply causation, it’s attention-grabbing to notice that the % of vulnerabilities brought on by reminiscence questions of safety appears to correlate reasonably intently with the event language that’s used for brand new code. This matches the expectations printed in our weblog put up 2 years in the past concerning the age of reminiscence security vulnerabilities and why our focus must be on new code, not rewriting current elements. After all there could also be different contributing elements or different explanations. Nevertheless, the shift is a significant departure from industry-wide tendencies which have persevered for greater than a decade (and sure longer) regardless of substantial investments in enhancements to reminiscence unsafe languages.
We proceed to spend money on instruments to enhance the protection of our C/C++. Over the previous few releases we’ve launched the Scudo hardened allocator, HWASAN, GWP-ASAN, and KFENCE on manufacturing Android gadgets. We’ve additionally elevated our fuzzing protection on our current code base. Vulnerabilities discovered utilizing these instruments contributed each to prevention of vulnerabilities in new code in addition to vulnerabilities present in outdated code which can be included within the above analysis. These are essential instruments, and critically essential for our C/C++ code. Nevertheless, these alone don’t account for the big shift in vulnerabilities that we’re seeing, and different tasks which have deployed these applied sciences haven’t seen a significant shift of their vulnerability composition. We consider Android’s ongoing shift from memory-unsafe to memory-safe languages is a significant component.
In Android 12 we introduced help for the Rust programming language within the Android platform as a memory-safe different to C/C++. Since then we’ve been scaling up our Rust expertise and utilization throughout the Android Open Supply Challenge (AOSP).
As we famous within the authentic announcement, our aim is to not convert current C/C++ to Rust, however reasonably to shift improvement of recent code to reminiscence secure languages over time.
In Android 13, about 21% of all new native code (C/C++/Rust) is in Rust. There are roughly 1.5 million complete traces of Rust code in AOSP throughout new performance and elements corresponding to Keystore2, the brand new Extremely-wideband (UWB) stack, DNS-over-HTTP3, Android’s Virtualization framework (AVF), and varied different elements and their open supply dependencies. These are low-level elements that require a techniques language which in any other case would have been applied in C++.
Safety influence
Up to now, there have been zero reminiscence security vulnerabilities found in Android’s Rust code.
We don’t anticipate that quantity to remain zero ceaselessly, however given the quantity of recent Rust code throughout two Android releases, and the security-sensitive elements the place it’s getting used, it’s a major end result. It demonstrates that Rust is fulfilling its meant objective of stopping Android’s most typical supply of vulnerabilities. Historic vulnerability density is bigger than 1/kLOC (1 vulnerability per thousand traces of code) in a lot of Android’s C/C++ elements (e.g. media, Bluetooth, NFC, and so forth). Based mostly on this historic vulnerability density, it’s possible that utilizing Rust has already prevented tons of of vulnerabilities from reaching manufacturing.
What about unsafe Rust?
Working system improvement requires accessing sources that the compiler can’t cause about. For memory-safe languages which means an escape hatch is required to do techniques programming. For Java, Android makes use of JNI to entry low-level sources. When utilizing JNI, care have to be taken to keep away from introducing unsafe conduct. Thankfully, it has confirmed considerably less complicated to assessment small snippets of C/C++ for security than whole applications. There are not any pure Java processes in Android. It’s all constructed on high of JNI. Regardless of that, reminiscence security vulnerabilities are exceptionally uncommon in our Java code.
Rust likewise has the unsafe{} escape hatch which permits interacting with system sources and non-Rust code. Very like with Java + JNI, utilizing this escape hatch comes with extra scrutiny. However like Java, our Rust code is proving to be considerably safer than pure C/C++ implementations. Let’s take a look at the brand new UWB stack for instance.
There are precisely two makes use of of unsafe within the UWB code: one to materialize a reference to a Rust object saved inside a Java object, and one other for the teardown of the identical. Unsafe was actively useful on this scenario as a result of the additional consideration on this code allowed us to find a potential race situation and guard towards it.
Normally, use of unsafe in Android’s Rust seems to be working as meant. It’s used not often, and when it’s used, it’s encapsulating conduct that’s simpler to cause about and assessment for security.
Security measures make memory-unsafe languages gradual
Cellular gadgets have restricted sources and we’re at all times attempting to make higher use of them to supply customers with a greater expertise (for instance, by optimizing efficiency, enhancing battery life, and decreasing lag). Utilizing reminiscence unsafe code usually implies that we have now to make tradeoffs between safety and efficiency, corresponding to including extra sandboxing, sanitizers, runtime mitigations, and {hardware} protections. Sadly, these all negatively influence code dimension, reminiscence, and efficiency.
Utilizing Rust in Android permits us to optimize each safety and system well being with fewer compromises. For instance, with the brand new UWB stack we had been capable of save a number of megabytes of reminiscence and keep away from some IPC latency by operating it inside an current course of. The brand new DNS-over-HTTP/3 implementation makes use of fewer threads to carry out the identical quantity of labor through the use of Rust’s async/await function to course of many duties on a single thread in a secure method.
The variety of vulnerabilities reported within the bulletin has stayed considerably regular over the previous 4 years at round 20 per thirty days, even because the variety of reminiscence security vulnerabilities has gone down considerably. So, what offers? A number of ideas on that.
A drop in severity
Reminiscence security vulnerabilities disproportionately characterize our most extreme vulnerabilities. In 2022, regardless of solely representing 36% of vulnerabilities within the safety bulletin, memory-safety vulnerabilities accounted for 86% of our important severity safety vulnerabilities, our highest score, and 89% of our remotely exploitable vulnerabilities. Over the previous few years, reminiscence security vulnerabilities have accounted for 78% of confirmed exploited “in-the-wild” vulnerabilities on Android gadgets.
Many vulnerabilities have a effectively outlined scope of influence. For instance, a permissions bypass vulnerability typically grants entry to a particular set of data or sources and is usually solely reachable if code is already operating on the gadget. Reminiscence security vulnerabilities are typically way more versatile. Getting code execution in a course of grants entry not simply to a particular useful resource, however every thing that that course of has entry to, together with assault floor to different processes. Reminiscence security vulnerabilities are sometimes versatile sufficient to permit chaining a number of vulnerabilities collectively. The excessive versatility is maybe one cause why the overwhelming majority of exploit chains that we have now seen use a number of reminiscence security vulnerabilities.
With the drop in reminiscence security vulnerabilities, we’re seeing a corresponding drop in vulnerability severity.
With the lower in our most extreme vulnerabilities, we’re seeing elevated experiences of much less extreme vulnerability sorts. For instance, about 15% of vulnerabilities in 2022 are DoS vulnerabilities (requiring a manufacturing unit reset of the gadget). This represents a drop in safety threat.
Android appreciates our safety analysis group and all contributions made to the Android VRP. We apply greater payouts for extra extreme vulnerabilities to make sure that incentives are aligned with vulnerability threat. As we make it tougher to seek out and exploit reminiscence security vulnerabilities, safety researchers are pivoting their focus in direction of different vulnerability sorts. Maybe the full variety of vulnerabilities discovered is primarily constrained by the full researcher time dedicated to discovering them. Or maybe there’s one other rationalization that we have now not thought-about. In any case, we hope that if our vulnerability researcher group is discovering fewer of those highly effective and versatile vulnerabilities, the identical applies to adversaries.
Assault floor
Regardless of many of the current code in Android being in C/C++, most of Android’s API floor is applied in Java. Which means Java is disproportionately represented within the OS’s assault floor that’s reachable by apps. This supplies an essential safety property: many of the assault floor that’s reachable by apps isn’t inclined to reminiscence corruption bugs. It additionally implies that we’d anticipate Java to be over-represented when taking a look at non-memory security vulnerabilities. It’s essential to notice nevertheless that varieties of vulnerabilities that we’re seeing in Java are largely logic bugs, and as talked about above, typically decrease in severity. Going ahead, we shall be exploring how Rust’s richer kind system can assist stop frequent varieties of logic bugs as effectively.
Google’s means to react
With the vulnerability sorts we’re seeing now, Google’s means to detect and stop misuse is significantly higher. Apps are scanned to assist detect misuse of APIs earlier than being printed on the Play retailer and Google Play Defend warns customers if they’ve abusive apps put in.
Migrating away from C/C++ is difficult, however we’re making progress. Rust use is rising within the Android platform, however that’s not the tip of the story. To satisfy the targets of enhancing safety, stability, and high quality Android-wide, we’d like to have the ability to use Rust anyplace within the codebase that native code is required. We’re implementing userspace HALs in Rust. We’re including help for Rust in Trusted Functions. We’ve migrated VM firmware within the Android Virtualization Framework to Rust. With help for Rust touchdown in Linux 6.1 we’re excited to carry memory-safety to the kernel, beginning with kernel drivers.
As Android migrates away from C/C++ to Java/Kotlin/Rust, we anticipate the variety of reminiscence security vulnerabilities to proceed to fall. Right here’s to a future the place reminiscence corruption bugs on Android are uncommon!