Items, providers, and other people merely can’t get to the place they’re wanted with out efficient logistics. Logistics are important to almost all elements of the economic system and nationwide safety. Regardless of this, quite a lot of challenges can disrupt logistics from extreme climate and international pandemics to distribution bottlenecks. On this weblog put up we’ll concentrate on cyber assaults to logistics resolution fashions.
Nationwide safety and navy organizations think about contested logistics as “the surroundings through which an adversary or competitor deliberately engages in actions or generates situations, throughout any area, to disclaim, disrupt, destroy, or defeat pleasant pressure logistics operations, amenities, and actions.” For instance, in World Struggle II, the Allied Transportation Plan included strategic bombing of main highway junctions, bridges, tunnels, rail traces, and airfields to hamper German actions to the Normandy space. This performed a decisive function within the success of the D-Day landings.
Whereas defending the bodily elements of logistics operations is essential, trendy logistic programs additionally embody in depth software-based resolution assist that’s important to logistics planning phases, and this software program additionally should be shielded from assault.
Past basic cybersecurity, there aren’t any customary strategies for monitoring, detecting, and stopping cyber assaults to logistics resolution fashions. Nonetheless, there are well-studied adjoining fields reminiscent of synthetic intelligence (AI) safety, machine studying operations (MLOps), and extra broadly AI engineering that may contribute to the securing of our logistics resolution fashions.
Hypothetical Assault to a Logistics Mannequin
Take into account a logistics mannequin that determines the right way to distribute provides to hurricane victims in Florida. We have to resolve the place to find provide storage amenities, in addition to how provides from every facility are to be distributed to surrounding populations.
Within the context of nationwide safety and navy operations, eventualities would possibly embody designing logistics programs to move gas, munitions, gear, and warfighting personnel from their originating areas to the entrance traces of a battle. One other navy use case could be figuring out the optimum routing of automobiles, ships, and airplanes in a manner that minimizes casualty threat and maximizes mission effectiveness.
Determine 1 illustrates utilizing a variation of the okay-center formulation to compute an optimum coverage for the Florida hurricane situation (left panel). If a cyber-attacker had entry to this mannequin and was in a position to modify its coefficients, then we’d find yourself with a plan reminiscent of depicted in the suitable panel. The advisable central facility location has modified, which may degrade the effectivity of our hypothetical system, or worse, forestall catastrophe victims from receiving wanted provides.
In a navy battle, even seemingly delicate modifications like a advisable facility location may very well be enormously damaging. For instance, if an adversary have been to have some functionality to assault or degrade a specific location unbeknownst to the defender, then manipulating the defender’s resolution mannequin may very well be a part of an effort to bodily injury the defender’s logistics system.
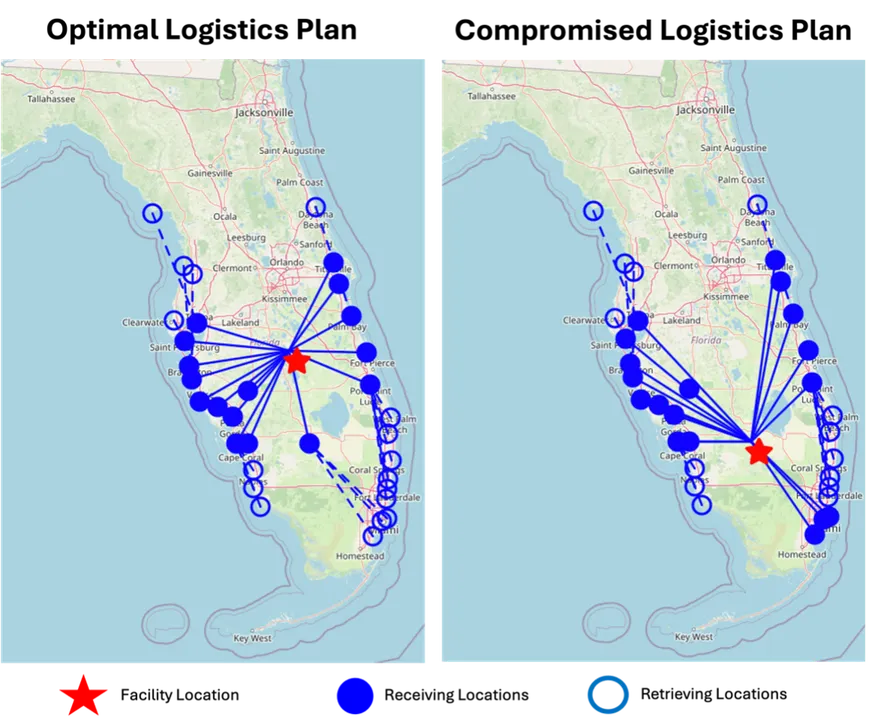
Determine 1: Hypothetical instance of how a cyber attacker would possibly subtly regulate mannequin parameters in such a manner that the mannequin recommends suboptimal or in any other case unfavorable insurance policies.
In observe, logistics resolution fashions could be extraordinarily massive. For instance, the small linear mannequin used for Determine 1 solves a system of 266 pages of linear equations, which Determine 2 depicts. If 100 areas must be lined, the mannequin would have about 20,000 resolution variables, about 40,000 constraints, and as much as about 800 million coefficients. Because of the downside of scale, practitioners usually use approximation algorithms that may generate moderately good insurance policies for his or her particular issues.
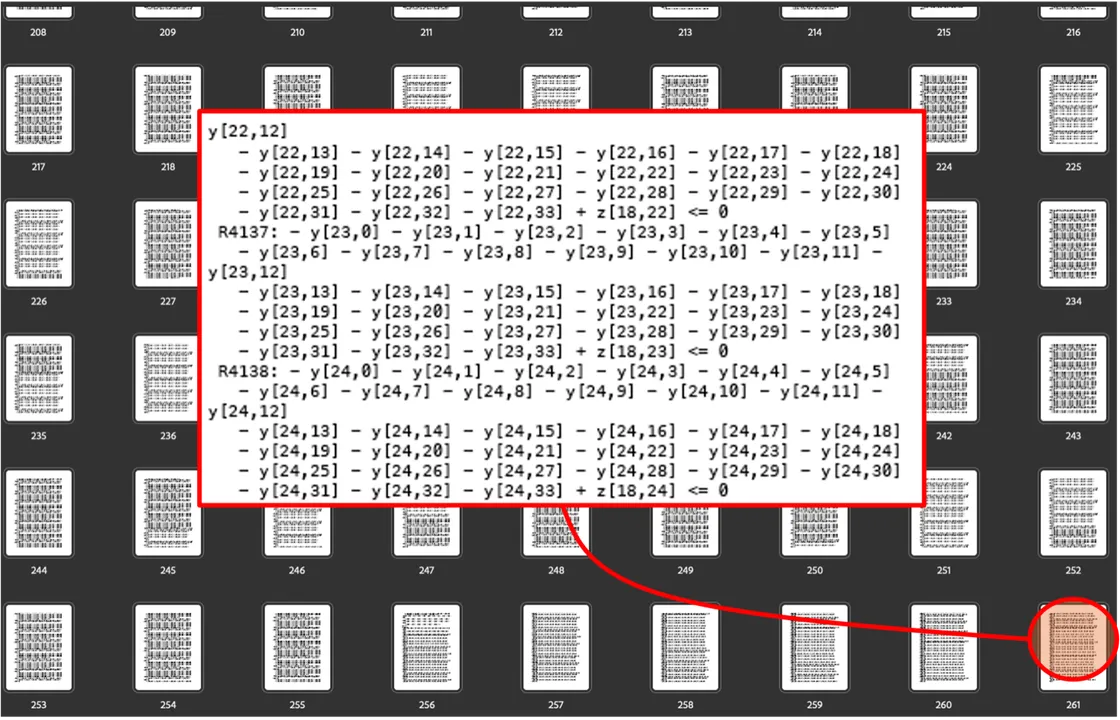
Determine 2: System of linear equations (266 pages) required to generate the optimum coverage in Determine 1. Realistically sized fashions are considerably bigger, and it might be straightforward for delicate mannequin manipulations to go undetected.
There are various varieties of logistics issues, together with facility location, automobile routing, scheduling, machine task, and bin packing. Logistics issues are sometimes formulated as linear applications. Determine 3 reveals the final type of a linear program, which (1) minimizes an goal operate (the vector of goal coefficients, c, multiplied by a vector of resolution variables, x); (2) topic to a set of constraints (the constraint coefficient matrix, A, multiplied by the vector of resolution variables, x, is the same as the constraint necessities vector, b); and (3) with the choice variables, x, taking up constructive values. Most logistics issues contain a variation of this mannequin referred to as a blended integer linear program, which permits a number of the resolution variables to be integer or binary. For instance, a binary resolution variable would possibly signify whether or not to open a provide depot (one) or not (zero) at a given location. Be aware that Determine 3 is a compact (small) mannequin illustration, and its use of vectors and matrices ( c, x , b , and A ) can mannequin any sized downside (for instance with hundreds of resolution variables, tens of hundreds of constraints, and hundreds of thousands of coefficients).

Determine 3: Common type of a linear program
George Dantzig invented the simplex methodology in 1947 to unravel linear applications, that are so pervasive that the simplex methodology is taken into account one of many nice algorithms of the twentieth century. Within the early 2010’s, it was estimated that 10-to-25 % of all scientific computation was dedicated to the simplex methodology. At present, even with computing developments, fixing linear applications at-scale stays an infinite problem.
In logistics observe, these fashions could be big. Not solely are they very troublesome to unravel, however they are often bodily unattainable to unravel with present computing expertise. At present, a lot of the operations analysis discipline is dedicated to growing approximation algorithms that yield prime quality (though not essentially optimum) options to real-world logistics issues. Latest analysis (see right here and right here) supplies examples of such approximation algorithms. As a result of these mathematical applications are sometimes NP-hard (i.e., the issue dimension grows exponentially, and optimum options can’t be generated in polynomial time), optimization is likely one of the promising use instances for quantum computing.
Discrete occasion simulation and system dynamics are additionally modeling types used to unravel logistics issues. Whereas we talk about linear programming as an exemplar mannequin type on this weblog, different mannequin kinds could be equally weak to cyber assaults.
Idea of Operations
There’s little printed analysis, and even working expertise, relating to cyber assaults on logistics resolution fashions. An assault would require undetected community intrusion; persistence to permit reconnaissance on the goal mannequin and assault planning; adopted by mannequin or knowledge manipulations which can be sufficiently subtle to be undetected whereas strategic sufficient to be damaging.
In observe, a profitable assault would require a classy mixture of abilities probably solely out there to motivated and skilled menace teams. Such menace teams do exist, as evidenced by intrusions into U.S. essential infrastructure and expertise enterprises like Google.
The Cyber Kill Chain developed by Lockheed Martin is a 7-step mannequin of how subtle cyber assaults are sometimes carried out. The seven steps are: reconnaissance, weaponization, supply, exploitation, set up, command and management, and eventually performing on the attacker’s targets. Attacking a call mannequin would equally require these steps to ascertain a persistent community intrusion, entry to the mannequin, and eventually manipulate the mannequin or its output.
As soon as attackers achieve entry to a logistics mannequin, the injury that they’ll inflict will depend on many elements. Like AI safety, a lot will depend on the kind of entry gained (e.g., mannequin read-only entry, mannequin write entry, coaching knowledge read-only entry, coaching knowledge write entry, capability to exfiltrate a duplicate of the mannequin or knowledge, and so on.). In contrast to many AI purposes, logistics usually introduces sprawling provide chains of contractors and subcontractors. If an higher echelon resolution mannequin will depend on knowledge from organizations at decrease echelons within the provide chain, then the mannequin may conceivably be attacked by poisoning knowledge in programs past the mannequin operator’s management.
Suggestions for Securing Logistics Determination Fashions
We name on the logistics, cybersecurity, and operations analysis communities to systematically examine the susceptibility of resolution fashions to cyber assault and to offer formal suggestions for a way greatest to guard these fashions.
Within the meantime, there are well-studied adjoining fields that supply present logistics mannequin operators alternatives to enhance safety. For instance, machine studying operations (MLOps) is a scientific framework for guaranteeing dependable deployments into manufacturing environments. Extra broadly, the SEI is main the Nationwide AI Engineering Initiative, which systematizes what is required to develop, deploy, and keep AI programs in unpredictable and chaotic real-world environments. Monitoring is a central tenet of MLOps and AI engineering, together with strategies to determine vital mannequin and knowledge modifications between revisions.
Lastly, we suggest that AI safety organizations think about logistics resolution fashions inside their purview. The linear programing that underpins logistics fashions shares many attributes with AI: each could be large scale, compute intensive, depend on knowledge, and be troublesome to interpret. Like AI, assaults to logistics resolution fashions can create vital, real-world injury.


