Open supply intelligence (OSINT) software program is turning into an more and more vital software for gathering public data. One of these software program permits customers to assemble simply accessible knowledge on people and organizations from a variety of sources — equivalent to engines like google, social media profiles, and authorities information — with the intention of making a complete image.
Superior OSINT software program can then cross-reference this knowledge to offer an correct supply of information and construct connections between completely different items of knowledge which will in any other case have gone unnoticed. In immediately’s data-driven world, OSINT software program offers an indispensable useful resource for anybody trying to achieve perception into themselves or these round them. It has additionally turn into more and more in style for cybersecurity professionals utilizing it for moral hacking, penetration testing and exterior risk identification.
OSINT is a key part of Open-Supply Enterprise Intelligence (OSBI), a meta development that’s quickly rising. OSINT eliminates the hefty related price which will be prohibitive for smaller companies, and it has emerged as a gorgeous mannequin of BI on account of its decrease price and scalability. At the moment, round 26% of corporations use open-source instruments as a part of their enterprise technique and this quantity is more likely to develop considerably sooner or later.
The OSINT market is predicted to expertise important development over the subsequent 5 years–offering ample alternative for startups trying to break into this area.
Listed below are some among the greatest open supply intelligence instruments available on the market:
Maltego is a flexible open supply intelligence platform that may simplify and expedite investigations. It offers entry to 58 knowledge sources and handbook add capabilities, in addition to databases of as much as 1 million entities that will help you conduct higher evaluation. Its highly effective visualization instruments additionally allow you to select from completely different layouts like blocks, hierarchical, or round graphs with weights and notes for additional refinement.
With Maltego, belief and security groups, regulation enforcement personnel and cybersecurity professionals get one-click investigation outcomes with easy-to-follow insights.
OSINT will be invaluable in a wide range of sectors, from regulation enforcement to monetary companies. That is why the corporate additionally invests closely in offering unbelievable sources on OSINT instruments and methods. Not solely are these different and complete, they’re additionally hand-picked by an professional crew to make sure prospects get the perfect out of their product. The corporate additionally affords a Maltego Basis course out there for buy on-line.
Spiderfoot is an open-source OSINT reconnaissance software with a wide range of options, together with the power to acquire and analyze IP addresses, CIDR ranges, domains and subdomains, ASNs, e mail addresses, cellphone numbers, names and usernames, BTC addresses, and extra.
Providing each a command-line interface in addition to an embedded web-server outfitted with a user-friendly GUI interface which is accessible on GitHub, Spiderfoot boasts over 200 modules which can be utilized to hold out essentially the most complete actions and uncover key particulars about any goal.
It can be used to evaluate whether or not or not organizations have knowledge uncovered that would probably trigger safety breaches. All in all, it’s a highly effective cyber intelligence software able to offering invaluable insights into probably dangerous on-line entities.
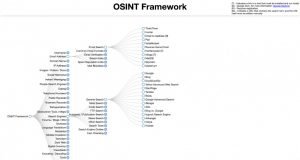
OSINT Framework is a superb useful resource for open-source intelligence gathering. It has all the pieces from knowledge sources to useful hyperlinks to efficient instruments, making it a lot simpler than attempting to individually analysis each program and gear on the market.
This listing additionally offers choices for working methods past Linux, offering options throughout the board. The one problem could also be growing an efficient search technique that narrows down outcomes equivalent to car registration or e mail addresses, however with such organized sources, this finally ends up being extra of an asset than ever.
The OSINT Framework is shortly turning into probably the most in style options for knowledge assortment, data discovery and sorting issues out.
In immediately’s digital economic system, verifying somebody’s identification utilizing numerous social media and on-line platform accounts as knowledge factors is turning into extra commonplace. SEON is on the forefront of this digital identification verification motion.
By tapping into its e mail and cellphone quantity methods, your corporation can entry over 50 completely different social alerts that produce a complete threat rating. These alerts not solely affirm the validity of a buyer’s e mail deal with or cellphone quantity but in addition gather deeper insights relating to their digital footprint.
Moreover, SEON offers companies with the flexibleness to implement queries manually, through API, and even via a Google Chrome extension; making it simpler to make use of and accessible.
Lampyre is a paid utility designed particularly for OSINT, offering an environment friendly answer for due diligence, cyber risk intelligence, crime evaluation, and monetary analytics. It’s an intuitive, one-click utility that may be put in in your PC or run on-line with ease.
Beginning with a single knowledge level equivalent to an organization registration quantity, full identify, or cellphone quantity, Lampyre routinely processes 100+ often up to date knowledge sources to disclose helpful data.
If wanted, you possibly can entry the information through PC software program or via API calls. For companies on the lookout for a complete platform to observe dangers and examine threats of assorted varieties, Lampyre’s SaaS product providing – often called Lighthouse – permits customers to pay per API name.

Shodan is a sophisticated search engine that permits customers to shortly determine and entry data on the expertise utilized by any enterprise. By typing in an organization identify, one can obtain detailed insights into their IoT units – equivalent to location, configuration particulars and vulnerabilities – grouped in line with community or IP deal with.
Moreover, employers might use Shodan for additional evaluation of working methods getting used; open ports; internet server kind and design language employed with excessive accuracy achieved via its cutting-edge software program toolsets.

Recon-ng is a strong software used to search out data associated to web site domains. It initially began as a script, however now it has developed right into a full framework.
When utilizing Recon-ng, customers are capable of determine internet vulnerabilities together with GeoIP lookup, DNS lookup, and port scanning. This can be very helpful for finding delicate recordsdata equivalent to robots.txt, discovering hidden subdomains, on the lookout for SQL errors, and retrieving firm CMS or WHOIS data.
Regardless of being extra technical in nature in comparison with different instruments out there available on the market, there are numerous useful sources out there that you should utilize to discover ways to take full benefit of this high software program.

Aircrack-ng is a strong and complete safety penetration testing software utilized by digital safety professionals to check the security of wi-fi networks. The software permits customers to gather data associated to packet monitoring, together with capturing of frames and accumulating WEP IVs together with the place of entry factors if a GPS is added.
It could possibly additionally conduct penetration assessments on networks and analyze the efficiency by token injection assaults, faux entry factors and replay assaults. Lastly, it could possibly carry out password cracking for each WEP and WPA PSK (WPA 1 and a couple of). Aircrack-ng represents an indispensable software for assessing the potential vulnerabilities in a wi-fi community earlier than they are often probably exploited.
The flexibility of this software is a serious spotlight; it was developed primarily for Linux however will be tailored to different methods equivalent to Home windows, OS X and FreeBSD. Moreover, its functionality as a command line interface (CLI) provides it an edge in customization. Which means that extra superior customers can simply create customized scripts so as to additional modify the software and tailor it to their distinctive necessities.

BuiltWith is an extremely highly effective web site detective, permitting customers to search out out the tech stack, frameworks, plugins, and different data powering in style web sites. This may be helpful for these taken with utilizing related applied sciences for their very own websites.
Moreover, BuiltWith additionally lists JavaScript/CSS libraries {that a} web site could also be utilizing, offering additional granularity and perception into the structure of sure web sites. Because of this, BuiltWith just isn’t solely helpful for informal analysis however can be used to conduct reconnaissance on behalf of companies or organizations who have to know exactly how completely different webpages are put collectively.
For added safety assurance, you possibly can mix BuiltWith with web site safety scanners like WPScan specializing in figuring out widespread vulnerabilities impacting an internet site.

Metagoofil is a freely out there software on GitHub which makes a speciality of extracting metadata from a wide range of public paperwork, together with .pdf, .doc, .ppt and .xls. As an extremely highly effective search engine, it is ready to unearth helpful knowledge equivalent to usernames and actual names related to particular public paperwork, together with server data and the trail to those paperwork.
Whereas this data presents important dangers to organizations, the identical knowledge can be leveraged as a protection mechanism. Organizations can take proactive steps to make sure that the knowledge itself is hidden or obscured earlier than malicious actors have a possibility to make use of it for unwell means.


